Bl cybersecurity z_dooly
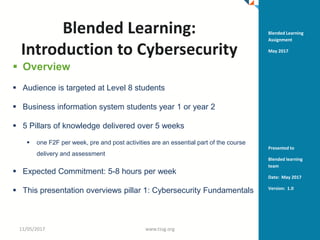
- 1. Blended Learning: Introduction to Cybersecurity Overview Audience is targeted at Level 8 students Business information system students year 1 or year 2 5 Pillars of knowledge delivered over 5 weeks one F2F per week, pre and post activities are an essential part of the course delivery and assessment Expected Commitment: 5-8 hours per week This presentation overviews pillar 1: Cybersecurity Fundamentals 11/05/2017 www.tssg.org 1 Blended Learning Assignment May 2017 Presented to Blended learning team Date: May 2017 Version: 1.0
- 2. - My teaching philosophy - Aim of the module 11/05/2017 www.tssg.org 2
- 3. My teaching philosophy • Social constructivist • Participatory learning leads to greater understanding • My experience – researcher workshops – peer /reciprocated learning – Little experience in learning outcomes and assessment rather workshop and working group ToR/objectives and evaluation reports 11/05/2017 www.tssg.org 3
- 4. Pre-workshop tasks • Read papers • Review reports • Watch TED • Go to TES/Padlet and follow instructions to complete tasks 11/05/2017 www.tssg.org 4
- 5. F2F overview • Slides delivered to students @F2F • Discussion of forum items • In class poll on importance of cybersecurity fundamentals for each domain/class of society 11/05/2017 www.tssg.org 5
- 6. Post-workshop tasks • Pick a task and complete it • Watch the jigsaw 8-10 years old and reflect on it and any cultural • Watch TED • Read a paper about your online presence post-death and reflect on this – share in forum • Go to TES/Padlet and follow instructions to complete tasks 11/05/2017 www.tssg.org 6
- 7. Relevant tools & mechanisms 1. PESTLE Analysis of Key PACs Domain Trends 11/05/2017 www.tssg.org 7
- 8. Introduction to Cybersecurity CYBERSECURITY FUNDAMENTALS EXPERTISE PARTNERS SCIENCE Concepts include privacy, identity, access control, threats/vulnerbilities, authentication Fraunhofer, CNRS, HP Labs, Deutsch Telecom, Intel, IBM, Cisco Leading software R&D Centre with particular expertise in networks, mobile and communications services. Connected globally with other Research centres, this is reflected in the Post Doc’s and PhD Students with a total of 40 in NetLabs SOTA MARKET AWARENESS is one of Ireland’s leaders in the EU collaborative R&D programmes (FP7 / Horizon 2020) and has worked with over 450 companies on these programmes. INDUSTRY Completed over 110 direct industry projects in Ireland over the past 3 years and has spun out a number of leading international start-ups such as FeedHenry Ltd. 11-May-17
- 9. Concepts • in computer security, a vulnerability is a weakness which allows an attacker to reduce a system's information assurance. Vulnerability is the intersection of three elements: a system susceptibility or flaw, attacker access to the flaw, and attacker capability to exploit the flaw. 11/05/2017 www.tssg.org 9
- 10. privacy-oriented solutions in marketplace 11/05/2017 www.tssg.org 10
- 11. Market Analysis Science and Technology Policy Framework and Legislation Market OverviewTrends and Challenges Market Analysis Module- week 3 Economics Cyber-security Privacy Basics and introduction Basics and introduction Research Field Research Field Decision models Indicators and metrics Preference measurement … Economic Incentive Schemes
- 12. SOTA/Landscape • Audit and Monitoring • Authentication, Authorisation and Access Control (AAA) • Cryptology • Forensics and Incident Response • Privacy and Security Metrics • Malware and Offensive Technologies • Mobile Security • Network Security and Management • Security Information Sharing • Secure Software Development and Assurance • Security Management Support 11/05/2017 12
- 13. INNOVATION MODEL TSSG What we can offer 11-May-17 13
- 14. RESEARCH TECHNIQUES AT TSSG Virtualisation of network resources and functions to support highly customisable service deployment environments. Network Architectures Techniques for the federation of networks and services to deliver end-to-end service Quality of Experience. End-to-end QoS New algorithms, protocols and tools to manage programmable networks in a scalable and controllable manner. Management Techniques Services Personalisation to meets users and service providers needs. Information Security 14 New design patterns, tools and methodologies, harness programmable networks. Engineering Services Development of data analytics that is distributed, fine grained and scalable to support mass population. Data Analysis 11-May-17
- 15. Why? • Our lives depend on online services. Gain essential cyber security knowledge and skills, to help protect your digital life. • ybersecurity concepts, issues, and tools that are critical in solving problems in the computing security domain. • Human centric focus – citizen • IoT • nowledge gained for analysis and management of international cyber incidents and conflicts including for activities such as development of policy related to cybercrime and cyberwarfare • Safety online • Privacy awareness • Protection mechanisms for vulnerable (young/old/technophobes 11/05/2017 www.tssg.org 15
- 17. Aim of the module • Introduces the students to Cybersecurity theory and practical applications • This involves a basic contextual introduction to the domain and its related domains, state of the art (SOTA) and to scaffold student theoretical learning with practical knowledge and utilisation. • Cybersecurity fundamentals 11/05/2017 www.tssg.org 17
- 18. Aim of the module 11/05/2017 www.tssg.org 18 Course Content Summary Objective Activity/Assessment Week 1 Cybersecurity Fundamentals Week 2 Societal considerations Privacy, inter-cultural considerations Week 3 SOTA Market awareness Week 4 Business opportunities and innovation Week 5
- 19. Tips to get started • Content curation tools • Music – use it – try it – focus attention – distract – calm • Find a schedule that suits you, your learning style and meets partnership agreement 11/05/2017 www.tssg.org 19
- 20. Dynamic flexibility • Switch modules • Add /delete content – prioritise depending on student requirements – build the curriculum (parts that are not assessed?>) 11/05/2017 www.tssg.org 20
- 22. Research Networks Discuss what is Network theory • network theory is related to graph theory and looks at asymmetric relations between discrete objects. The first proof of network theory is the Seven Bridges of Königsberg (Newman et al., 2006). • Edges and nodes . 11/05/2017 www.tssg.org 22
- 23. Course content • software vulnerabilities and attacks that exploit them -- such as buffer overflows, SQL injection, and session hijacking -- and we will consider defenses that prevent or mitigate these attacks, including advanced testing and program analysis techniques. Importantly, we take a "build security in" mentality, considering techniques at each phase of the development cycle that can be used to strengthen the security of software systems. • Cryptopgraphy • Legislation – GDPR – global look 11/05/2017 www.tssg.org 23
- 24. Course overview • working collaboratively toward research innovation • Network analysis focuses on these relationships and explains the attitudes and behaviours of these actors and organisational members. 11/05/2017 www.tssg.org 24
- 25. • https://www.savvius.com/resources/ondemand_webinars for webinars on security 11/05/2017 www.tssg.org 25
- 26. Class exercise • Take X minutes to put yourself in middle of your network and map it out • Out of class assignment: • Record and write your reflections drawing from your readings, experiences, and in- class activities, on-line forum and other discussions (20 mins) 11/05/2017 www.tssg.org 26
- 27. Further resources • Linkedin Groups – Cyber intelligence network – Information Systems Security Association (ISSA) Discussion Forum – Information Security Community – Cloud Security Alliance – CyberSecurity Law, Policy, and Technology • Websites – http://www.ecs-org.eu • Innovation Union Website, http://ec.europa.eu/research/innovation-union/index_en.cfm • Europe2020, http://ec.europa.eu/europe2020/index_en.htm • Secure Societies website, http://ec.europa.eu/programmes/horizon2020/en/h2020-section/secure-societies-%E2%80%93-protecting- freedom-and-security-europe-and-its-citizens • LEIT website, http://ec.europa.eu/programmes/horizon2020/en/h2020-section/leadership-enabling-and-industrial-technologies • EU Cyber Security Strategy, http://ec.europa.eu/dgs/connect/en/content/cybersecurity-strategy-european-union 11/05/2017 www.tssg.org 27
- 28. • References and Bibliography • [APF12] Report on Annual Privacy Forum 2012, ENISA • [ARD13] Jorge L. Hernandez-Ardieta, Juan E. Tapiador and Guillermo Suarez-Tangil. Information Sharing Models for Cooperative Cyber Defence. 2013, 5th International Conference on Cyber Conflict (CyCon'13). K. Podins, J. Stinissen, M. Maybaum (Eds.) 2013 © NATO CCD COE Publications, Tallinn • [ARS14] "Apple expands data encryption under iOS 8, making handover to cops moot", arstechnica.com, Sept 18th 2014. • [CAS07] Casper, S. (2007). How do technology clusters emerge and become sustainable?: Social network formation and inter-firm mobility within the San Diego biotechnology cluster. Research Policy, 36(4), 438-455. • [DWO11] Dwork, C. (2011). A firm foundation for private data analysis. Communications of the ACM, 54(1), 86-95. • [DTI00] DTI, A practical guide to Cluster Development, England’s Regional Development Agencies, UK, 2000. • [EFF11] EFFECTS+ D2.2 - THE INNOVATION POTENTIAL OF FP7 SECURITY AND TRUST PROJECTS, 10th July 2011, www.effectsplus.eu • [EFF2_11] EFFECTS+, D2.1 - Results and Impacts of FP7 Projects (includes Draft Clusters Analysis) –28th February 2011, www.effectsplus.eu • [ENISA13] Recommended cryptographic measures - Securing personal data, ENISA report, https://www.enisa.europa.eu/activities/identity-and- trust/library/deliverables/recommended-cryptographic-measures-securing-personal-data • [EUC08] The Concept of Clusters and Cluster Policies and Their Role For Competitiveness and Innovation: Main Statistical Results and Lessons Learned, EU Commission Staff Working Document, SEC (2008) 2637, 2008 • [FIR13] FIRE FP7 Project – D5.3, Recommendations to improve pull-through and hence industrial competitiveness for clusters and stakeholders, 31 August 2014, www.trustworthyictonfire.com • [FIR2_13] FIRE D6.1 - D6.1, Addressing societal concerns on legal and privacy issues in ICT-related projects, www.trustworthyictonfire.com • [FOR14] Contextual Privacy: Making Trust A Market Differentiator, Forrester webinar January 28th 2014, https://www.forrester.com/The+New+Privacy+Is+All+About+Context/-/E-WEB16543 • [GAR14] Gartner, Information Security Is Becoming a Big Data Analytics Problem, 23 March 2012. • [HEF11] He, J., & Fallah, M. H. (2011). The typology of technology clusters and its evolution—Evidence from the hi-tech industries. Technological Forecasting and Social Change, 78(6), 945-952. 11/05/2017 www.tssg.org 28
- 29. • [ITU11] ITU National Cybersecurity Strategy Guide (Annex 2) Technical Solutions, published September 2011, http://www.itu.int/ITU-D/cyb/cybersecurity/docs/ITUNationalCybersecurityStrategyGuide.pdf • [JIA11] He, Jiang, and M. Hosein Fallah. "The typology of technology clusters and its evolution—Evidence from the hi-tech industries." Technological Forecasting and Social Change 78.6 (2011): 945-952. • [LAN12] Landwehr, C., Boneh, D., Mitchell, J. C., Bellovin, S. M., Landau, S., & Lesk, M. E. (2012). Privacy and cybersecurity: The next 100 years. Proceedings of the IEEE, 100(Special Centennial Issue), 1659-1673. • [MAR20] A. Marshall, Principles of Economics, 8th Ed.Macmillan, London 1920. • [NAR10] Narayanan, A., & Shmatikov, V. (2010). Myths and fallacies of personally identifiable information. Communications of the ACM, 53(6), 24-26. • [NIS14] State of the Art of Secure ICT Landscape, NIS Platform WG3, submitted July 2014. • [NIT15] NITRD - ‘The Networking and Information Technology Research and Development Program - Supplement to the President’s Budget (FY2015)’ http://www.whitehouse.gov/sites/default/files/microsites/ostp/NITRD_FY15_Final.pdf - 28th March 2014 • [NSF14] NSF – ‘Frequently Asked Questions (FAQ) for the Secure and Trustworthy Cyberspace (SaTC) Program’ http://www.nsf.gov/pubs/2013/nsf13130/nsf13130.jsp - 4th April 2014 • [NYT14] "White House Tech Advisers: Online Privacy Is a ‘Market Failure’", Steve Lohr, New York Times Online, May 5th 2014.http://bits.blogs.nytimes.com/2014/05/05/white-house-tech-advisers-online-privacy-is-a-market- failure/?_php=true&_type=blogs&_php=true&_type=blogs&_r=1 • [PCW11] How to Stop Hack Attacks In One Easy Step: Whitelisting, June 2011 • http://www.pcworld.com/article/230980/how_to_stop_hack_attacks_in_one_easy_step_whitelisting.html • [SEC13] SecCord Research and Innovation Yearbook, January 2014, http://www.cspforum.eu/Yearbook2013-V1.41.pdf • [TEC14] How Israel is rewriting the future of cybersecurity and creating the next Silicon Valley, http://www.techrepublic.com/article/how-israel-is-rewriting-the-future-of-cybersecurity-and-creating-the-next-silicon-valley/#. • [YOU08] Youtie, J., & Shapira, P. (2008). Building an innovation hub: A case study of the transformation of university roles in regional technological and economic development. Research policy, 37(8), 1188-1204. • • • 11/05/2017 www.tssg.org 29
- 30. European Research focus • Secure Services – increasing trustworthiness of service infrastructures, particularly security properties of composed services with Service Oriented Architectures, secure online collaboration, improved service certification schemes, and improvements around data sharing and information protection • Enabling Technology and Tools – improving the ability to define robust T+S policies, supporting next generation cryptography enhancements, and improving overall software and hardware development lifecycles from security, privacy and trust perspectives • Secure Networks – improving wireless and sensor security (particularly around emerging IoT challenges, improving resilience against offensive threats, improving network management approaches • Cloud Security – enhancing user “chain of trust” in cloud solutions, improving capabilities around secure and privacy- preserving remote data processing • Secure Devices – improving security properties of emerging devices, particularly around mobile and emerging Internet of Things • Privacy Technologies – improvements around privacy-preserving identity management, increased empowerment of users and self-management of data, increased transparency between data controllers and processors regarding data use 11/05/2017 www.tssg.org 30
- 31. European clusters • AEI Ciberseguridad (Spain) • www.aeiciberseguridad.es • Bavarian IT Security Cluster (Germany) • http://bit.ly/1wuWfl0 • CenSec (Denmark) • http://www.censec.dk/ • Centre for Secure Information Technologies (UK – Northern Ireland) • http://www.csit.qub.ac.uk/ • Cybernetica (Estonia) • http://cyber.ee/en/ • Digital Trust & Security Working Group, Paris (France) • http://www.systematic-paris-region.org/en/get-info- topics/digital-trust-and-security • Finnish Information Security Cluster (Finland) • http://fisc.fi/ • Hague Security Delta (Netherlands) • https://www.thehaguesecuritydelta.com/ • Leaders in Security (LSEC) (Belgium) • http://www.leadersinsecurity.org/ • http://www.madridnetwork.org/ • National Technology Platform on Secure and Dependable ICT (eSEC) (Spain) • Network Security Monitoring Cluster (Czech Republic) • http://www.nsmcluster.com/ • Members: http://www.nsmcluster.com/en/our-members/ • TeleTrust (TTT) IT Security Association (Germany) • https://www.it-sicherheit.de/ • UK Cyber Security Forum (UK) • http://www.ukcybersecurityforum.com/ 11/05/2017 www.tssg.org 31
- 32. Global context • On a global level, mainly US, Israel and EU – Wirh London, Ottawa, and Canberra emerging players 11/05/2017 www.tssg.org 32
- 34. Any questions?
Hinweis der Redaktion
- The city of Königsberg in Prussia (now Kaliningrad, Russia) was set on both sides of the Pregel River, and included two large islands which were connected to each other and the mainland by seven bridges. The problem was to devise a walk through the city that would cross each bridge once and only once, with the provisos that: the islands could only be reached by the bridges and every bridge once accessed must be crossed to its other end. The starting and ending points of the walk need not be the same.
