Practical Verification of TKIP Vulnerabilities
•
0 gefällt mir•2,282 views
Presentation given at Asia CCS on the paper "Practicular Verification of WPA-TKIP Vulnerabilities".
Melden
Teilen
Melden
Teilen
Downloaden Sie, um offline zu lesen
Empfohlen
Empfohlen
Weitere ähnliche Inhalte
Was ist angesagt?
Was ist angesagt? (20)
DDoS Open Threat Signaling (DOTS) Working Group Presentation on draft-ietf-do...

DDoS Open Threat Signaling (DOTS) Working Group Presentation on draft-ietf-do...
Ähnlich wie Practical Verification of TKIP Vulnerabilities
Ähnlich wie Practical Verification of TKIP Vulnerabilities (20)
M08 protecting your message data in IBM MQ with encryption

M08 protecting your message data in IBM MQ with encryption
Fragattacks-Breaking-Wi-Fi-Through-Fragmentation-And-Aggregation.pdf

Fragattacks-Breaking-Wi-Fi-Through-Fragmentation-And-Aggregation.pdf
[BlackHat USA 2016] Nonce-Disrespecting Adversaries: Practical Forgery Attack...![[BlackHat USA 2016] Nonce-Disrespecting Adversaries: Practical Forgery Attack...](data:image/gif;base64,R0lGODlhAQABAIAAAAAAAP///yH5BAEAAAAALAAAAAABAAEAAAIBRAA7)
![[BlackHat USA 2016] Nonce-Disrespecting Adversaries: Practical Forgery Attack...](data:image/gif;base64,R0lGODlhAQABAIAAAAAAAP///yH5BAEAAAAALAAAAAABAAEAAAIBRAA7)
[BlackHat USA 2016] Nonce-Disrespecting Adversaries: Practical Forgery Attack...
Do-it-Yourself Spy Program: Abusing Apple’s Call Relay Protocol

Do-it-Yourself Spy Program: Abusing Apple’s Call Relay Protocol
Preventing Autonomous System against IP Source Address Spoofing: (PASIPS) A N...

Preventing Autonomous System against IP Source Address Spoofing: (PASIPS) A N...
DTS Solution - Wireless Security Protocols / PenTesting 

DTS Solution - Wireless Security Protocols / PenTesting
Kürzlich hochgeladen
Kürzlich hochgeladen (20)
Automating Google Workspace (GWS) & more with Apps Script

Automating Google Workspace (GWS) & more with Apps Script
Apidays New York 2024 - The value of a flexible API Management solution for O...

Apidays New York 2024 - The value of a flexible API Management solution for O...
[2024]Digital Global Overview Report 2024 Meltwater.pdf![[2024]Digital Global Overview Report 2024 Meltwater.pdf](data:image/gif;base64,R0lGODlhAQABAIAAAAAAAP///yH5BAEAAAAALAAAAAABAAEAAAIBRAA7)
![[2024]Digital Global Overview Report 2024 Meltwater.pdf](data:image/gif;base64,R0lGODlhAQABAIAAAAAAAP///yH5BAEAAAAALAAAAAABAAEAAAIBRAA7)
[2024]Digital Global Overview Report 2024 Meltwater.pdf
Strategize a Smooth Tenant-to-tenant Migration and Copilot Takeoff

Strategize a Smooth Tenant-to-tenant Migration and Copilot Takeoff
2024: Domino Containers - The Next Step. News from the Domino Container commu...

2024: Domino Containers - The Next Step. News from the Domino Container commu...
Connector Corner: Accelerate revenue generation using UiPath API-centric busi...

Connector Corner: Accelerate revenue generation using UiPath API-centric busi...
How to Troubleshoot Apps for the Modern Connected Worker

How to Troubleshoot Apps for the Modern Connected Worker
Exploring the Future Potential of AI-Enabled Smartphone Processors

Exploring the Future Potential of AI-Enabled Smartphone Processors
Strategies for Unlocking Knowledge Management in Microsoft 365 in the Copilot...

Strategies for Unlocking Knowledge Management in Microsoft 365 in the Copilot...
Workshop - Best of Both Worlds_ Combine KG and Vector search for enhanced R...

Workshop - Best of Both Worlds_ Combine KG and Vector search for enhanced R...
The 7 Things I Know About Cyber Security After 25 Years | April 2024

The 7 Things I Know About Cyber Security After 25 Years | April 2024
Axa Assurance Maroc - Insurer Innovation Award 2024

Axa Assurance Maroc - Insurer Innovation Award 2024
Understanding Discord NSFW Servers A Guide for Responsible Users.pdf

Understanding Discord NSFW Servers A Guide for Responsible Users.pdf
Bajaj Allianz Life Insurance Company - Insurer Innovation Award 2024

Bajaj Allianz Life Insurance Company - Insurer Innovation Award 2024
Practical Verification of TKIP Vulnerabilities
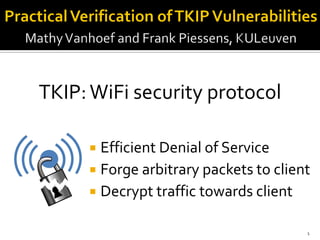
- 1. Efficient Denial of Service Forge arbitrary packets to client Decrypt traffic towards client 1 TKIP:WiFi security protocol
- 2. Why studyTKIP if a replacement already exist? 2 1999 2002 2004 WEP Broken WPA-TKIP Acceptable WPA-CCMP (AES) Secure
- 3. Detected 6803 networks 66% supportTKIP 19% support onlyTKIP 3 Need more arguments to killTKIP!
- 4. 4 Beck &Tews Attack >8 mins Key to calculate integrity check Forge 3 small packets to client
- 5. NewAttack: Efficient Denial of Service Improve & implement existing ideas to: Forge arbitrary packets Decrypt packets towards client [M. Beck. EnhancedTKIP michael attacks.] 5
- 6. 1. Add Message Integrity Check (MIC) 2. Encrypt using XOR stream cipher 3. Add Packet ID (#ID) to avoid replays #ID MICData Encrypted How are packets sent/received? 6
- 7. 1. Add Message Integrity Check (MIC) 2. Encrypt using XOR stream cipher 3. Add Packet ID (#ID) to avoid replays #ID MICData Encrypted How are packets sent/received? 7 MIC key Encryption key
- 8. 8 #ID MICData If decrypted, reveals MIC key. If ( two MIC failures within a minute ) halt all traffic for 1 minute
- 9. Attack: Capture packet, change priority, replay. 9 #ID / prior. MICData Encrypted
- 10. Avoids replay detection Doesn’t affect decryption Changes expected MIC value Attack: Capture packet, change priority, replay. 10 #ID / prior. MICData Encrypted Change priority
- 11. Avoids replay detection Doesn’t affect decryption Changes expected MIC value Attack: Capture packet, change priority, replay. 11 #ID / prior. MICData Encrypted Change priority MIC Failure(s) Traffic halted for 1 minute
- 12. Beck &Tews attack can forge 3 packets. Injecting more requires new keystreams: 12 Ciphertext PlaintextKeystream All packets start with LLC header We predict these with very high accuracy Capture packets with new #ID’s.
- 13. LLC Header is only 12 bytes …. Combine them using fragmentation! #ID1 Data1 #ID16 Data16 MIC Data MIC Data1 Data16 MICData2 12 bytes/fragment: inject 120 bytes of data
- 14. Port Scanner: 1. Get MIC key using Beck &Tews attack 2. InjectTCP SYN packets 3. Detect SYN/ACK based on length Remarks: High amount of packet injection proven! Also: DNS poisoning, DHCP spoofing, … 14
- 15. AP Client 1. Sniff packet 2. 15 Attacker Data MICPing req. Sniffed packet
- 16. AP Client 1. Sniff packet 2. 16 Attacker Data MICPing req. Sniffed packet Magic
- 17. AP Client 1. Sniff packet 2. 3. Reply incl. packet External IP 17 Attacker Data MICPing req. Sniffed packet Magic
- 18. State1: initial state of every packet State2: state after processing prefix State3: equal to state1 due to magic bytes State4: equal to MIC of sniffed packet! Data MICMagicPrefix Sniffed packet 18 State4State3State2State1
- 19. Possible applications? Decrypt web responses: Web mail Bank details … DecryptTCP sequence number, hijack connection and inject malware? 19
- 20. Integrity (MIC) not verified when fragmented: AlfaAWUS036h Belkin F5D7053 Ralink U150BB 20 Attack time reduced from >8 min to zero.
- 21. No replay protection: AlfaAWUS036h Belkin F5D7053 Tomato 1.28 (AP firmware) 21 No need to generate new keystreams!
- 22. Always accepts unencrypted packets: AlfaAWUS036h Belkin F7D1102 ScarletVDSL (AP of ISP in BE) 22 Game over, you lose!
- 24. TKIP is insecure! Efficient Denial of Service Forge any packet towards client Decrypt traffic towards client 24
- 25. 25