Melden
Teilen
Empfohlen
ICC Data and Device management

ICC"s icXchange IP data networking solution data (icXcloud) and device (icXmanager) management systems enable full view of the ICC solutions regardless of location, type, and size of network. Designed to decouple the cost of management and the devices, ICC's solution also enables the separation of the device from the management for clients with particularly sensitive cost structures.
Ejemplo

This document lists the educational background of Arturo Borja. It shows that he attended National High School from 8th through 10th level.
Seminar Ymchwil / Gwennan Elin Higham / Research Seminar

Canfyddiadau ymchwil ar ddysgu Cymraeg i Fewnfudwyr / PhD research findings on teaching Welsh to Immigrants
Front cover plan

The document provides details for a planned magazine cover shoot, including:
- The model, location, lighting, and her posing holding a guitar and smiling.
- The intended connotation of a happy pop star promoting her new album.
- Contingency plans if the primary model is unavailable, including an alternate model and pose.
- Notes on photography techniques like shutter speed and aperture that impact the shot.
- Analysis and rejection of some test photos that don't fully achieve the desired look and composition.
- An explanation for selecting the final chosen photo that best captures the vision of a casual yet stylish pop star look.
Deep Dive into OAuth for Connected Apps

The document discusses OAuth and its implementation for connected apps. It describes OAuth as a delegation protocol for conveying authorization across web apps and APIs. It then outlines the web server flow and user agent flow, including the different token types used. It demonstrates getting an access token via the web server flow and using it to query data. Finally, it provides information on refreshing access tokens before expired.
Gnav Presentation 2011 (Alimentaire)

GNAV Presenation 2011: Value ¨Proposition
Maroc, Détaillants, Besoins, Marques, Marketing, Mapping, CocaCola, Pepsi, Morocco, Mapping, Census, Audits, FMCG, Centrale Laitière, Koutoubia, Géomarketing
Empfohlen
ICC Data and Device management

ICC"s icXchange IP data networking solution data (icXcloud) and device (icXmanager) management systems enable full view of the ICC solutions regardless of location, type, and size of network. Designed to decouple the cost of management and the devices, ICC's solution also enables the separation of the device from the management for clients with particularly sensitive cost structures.
Ejemplo

This document lists the educational background of Arturo Borja. It shows that he attended National High School from 8th through 10th level.
Seminar Ymchwil / Gwennan Elin Higham / Research Seminar

Canfyddiadau ymchwil ar ddysgu Cymraeg i Fewnfudwyr / PhD research findings on teaching Welsh to Immigrants
Front cover plan

The document provides details for a planned magazine cover shoot, including:
- The model, location, lighting, and her posing holding a guitar and smiling.
- The intended connotation of a happy pop star promoting her new album.
- Contingency plans if the primary model is unavailable, including an alternate model and pose.
- Notes on photography techniques like shutter speed and aperture that impact the shot.
- Analysis and rejection of some test photos that don't fully achieve the desired look and composition.
- An explanation for selecting the final chosen photo that best captures the vision of a casual yet stylish pop star look.
Deep Dive into OAuth for Connected Apps

The document discusses OAuth and its implementation for connected apps. It describes OAuth as a delegation protocol for conveying authorization across web apps and APIs. It then outlines the web server flow and user agent flow, including the different token types used. It demonstrates getting an access token via the web server flow and using it to query data. Finally, it provides information on refreshing access tokens before expired.
Gnav Presentation 2011 (Alimentaire)

GNAV Presenation 2011: Value ¨Proposition
Maroc, Détaillants, Besoins, Marques, Marketing, Mapping, CocaCola, Pepsi, Morocco, Mapping, Census, Audits, FMCG, Centrale Laitière, Koutoubia, Géomarketing
Ontologia

La ontología estudia el ser y sus propiedades fundamentales. A través de la historia, ha habido diferentes visiones ontologicas, como la griega que veía al ser como cuerpo y alma, la medieval que consideraba a Dios como el ser supremo, y la contemporánea que analiza al ser desde la razón humana. La ontología se relaciona con la filosofía al ser la ciencia universal de las cosas, y con la psicología al estudiar el ser en general. También tiene aplicaciones en la educación y en campos como la ciencia, la tecnología y
Buurgerichte zorg als toekomstmodel - Herwig Teugels

Voka Health Community - kennissessie vermaatschappelijking van de zorg - 19 oktober 2015
2236 exantemas

Este documento describe el diagnóstico diferencial de los exantemas en pediatría. La mayoría de las enfermedades exantemáticas se manifiestan durante la edad pediátrica y constituyen consultas frecuentes. El diagnóstico se basa en la integración de datos clínicos como las características del exantema, los antecedentes, los síntomas y los hallazgos de la exploración. Los exantemas se clasifican según su morfología (máculo-papulosos, eritrodérmicos,
Dendistry best calligraphy

Creating a font by hand requires higher order thinking skills than selecting a font from a menu. Calligraphy is taught in schools not because students will use calligraphy scripts as adults, but because learning calligraphy requires skills like concentration, observation, intellectual stamina, and discipline. These skills are important for success in academic endeavors. Learning calligraphy is also an artistic creative process that builds pride. The brain is also strengthened through the calligraphy writing process.
Test v1

This 3 page test file contains brief placeholder text on each page to serve as a sample document. The test file consists of 3 pages that provide minimal placeholder content for testing summarization purposes.
Instructions MINOX MD 7x42 C | Optics Trade

Instructions MINOX MD 7x42 C | Optics Trade
http://www.optics-trade.eu/shop/en/shopby/manufacturer-minox.html
Kapitel 12:
Trading-Plattform & Trading-Typen

DIE PROFITLINIE
“PROFIT NEHMEN“-Funktion
“ANGEBOT EINHOLEN“-FUNKTION
ROLL FORWARD FUNKTION
INDIKATOR ZUR BÖRSENSTIMMUNG
MOBILE TRADING
Coagulación 4

Este documento resume los conceptos clave de la coagulación sanguínea, incluyendo el papel de las plaquetas, los factores de coagulación, la vitamina K, la warfarina y la heparina. Explica cómo las pruebas de laboratorio como el TPT, TP e INR ayudan a determinar si existe un problema en la vía intrínseca o extrínseca de la coagulación. Finalmente, destaca la importancia de monitorear estas pruebas para ajustar de manera adecuada los niveles de anticoagulantes como la
Boletim200 iac

O documento fornece informações sobre o abacaxizeiro, incluindo cultivares, clima e solo adequados, práticas de propagação, plantio e manejo da cultura. É descrita a importância econômica e nutricional do abacaxi, bem como seus usos na indústria de alimentos e na obtenção de subprodutos.
Presentacion de herpes zoster

El documento describe la varicela y el herpes zóster, causados por el virus varicela zóster. El herpes zóster ocurre cuando el virus se reactiva después de haber tenido varicela, causando una erupción dolorosa en un dermatoma. Los síntomas incluyen erupciones cutáneas, vesículas y dolor neural. El riesgo aumenta con la edad y en personas inmunocomprometidas. No existe cura, pero los antivirales y la vacuna pueden prevenir brotes.
New Symfony Tips & Tricks (SymfonyCon Paris 2015)

This talk included tens of tips and tricks, new features and rarely used options for Symfony and its ecosystem. Besides the full-stack Symfony framework, other related technologies were mentioned, like Doctrine, Composer, Twig, PHPUnit and Monolog.
Shape the Future

Hier finden Sie eine Auswahl der in Österreich verfügbaren Shape the Future Endgeräte.
Information Security @ AVL

H. Czamai presented on information security at AVL, an automotive engineering company. AVL has implemented an Information Security Management System (ISMS) based on ISO 27001 to ensure information security through organizational and technical measures. This includes an ISO 27001 certification, security awareness training, global policies, audits, and technical controls like firewalls, access management, and encryption. AVL also manages risks through threat detection and vulnerability management processes. The presentation discussed AVL's global operations, top security threats, and cloud security strategy using Microsoft services like Azure and Intune.
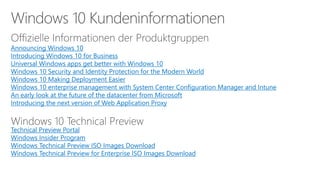
Secure the modern Enterprise

The document discusses cybersecurity and protecting information. It provides statistics on why organizations want to protect information, such as to reduce data leakage, meet compliance requirements, and partition sensitive data from unauthorized users. It then lists some of Microsoft's security capabilities for protecting devices, customer data in the cloud, on-premises environments, and customer data both in the cloud and on-premises.
Microsoft Digital Crimes Unit

Big data, cybersecurity threats, and cybercrime are growing issues according to the document. Microsoft takes a layered approach to security across its many products and services to help protect customers. Key aspects of Microsoft's security approach include detection of threats using signals and machine learning, responding quickly to issues, and protecting endpoints. The Microsoft Digital Crimes Unit works with law enforcement and through public-private partnerships to disrupt malware and fight technical support scams and other technology-facilitated crimes.
Microsoft: #DigitaleHelden Symposium - Graphic Recording

Graphic recording is a visual documentation technique used at events like conferences and meetings. A graphic recorder listens to the event and draws illustrations, diagrams, and icons that depict the key topics, discussions, and takeaways in visual form. These graphic recordings provide a unique visual summary of the event in a concise and engaging format that is easy for participants and observers to understand.
Digitale Transformation: Technologie und Mensch - die nächsten 5 Jahre

Speaker: Gerd Leonhard
Microsoft #DigitaleHelden Symposium
Digital Transformation "Book of Dreams"

Digital transformation can help organizations engage customers, empower employees, optimize operations, and transform products. To engage customers, organizations can deliver personalized experiences for customers across any device or location. They can also gain insights from customer data to improve marketing effectiveness and customer satisfaction. Transforming products involves managing the full product lifecycle and collaborating with customers on design. Optimizing operations focuses on digitizing processes, automating customer service, and using data-driven supply chain management. Empowering employees involves tools for productivity, collaboration, and talent development to meet changing customer needs.
Smart Buildings & IoT

This document discusses how smart buildings and the Internet of Things (IoT) can empower organizations by providing insights, increasing agility, and improving customer care. It describes how connecting devices and analyzing data can optimize building utilization, productivity, and costs. The document outlines Microsoft's vision for a smart buildings platform that uses IoT, cloud services, and analytics to gain visibility, manage key performance indicators, and anticipate and address issues. It also discusses how Microsoft technologies can support building management systems, integrate sensor data from various sources, and apply machine learning to enhance predictive capabilities.
Weitere ähnliche Inhalte
Andere mochten auch
Ontologia

La ontología estudia el ser y sus propiedades fundamentales. A través de la historia, ha habido diferentes visiones ontologicas, como la griega que veía al ser como cuerpo y alma, la medieval que consideraba a Dios como el ser supremo, y la contemporánea que analiza al ser desde la razón humana. La ontología se relaciona con la filosofía al ser la ciencia universal de las cosas, y con la psicología al estudiar el ser en general. También tiene aplicaciones en la educación y en campos como la ciencia, la tecnología y
Buurgerichte zorg als toekomstmodel - Herwig Teugels

Voka Health Community - kennissessie vermaatschappelijking van de zorg - 19 oktober 2015
2236 exantemas

Este documento describe el diagnóstico diferencial de los exantemas en pediatría. La mayoría de las enfermedades exantemáticas se manifiestan durante la edad pediátrica y constituyen consultas frecuentes. El diagnóstico se basa en la integración de datos clínicos como las características del exantema, los antecedentes, los síntomas y los hallazgos de la exploración. Los exantemas se clasifican según su morfología (máculo-papulosos, eritrodérmicos,
Dendistry best calligraphy

Creating a font by hand requires higher order thinking skills than selecting a font from a menu. Calligraphy is taught in schools not because students will use calligraphy scripts as adults, but because learning calligraphy requires skills like concentration, observation, intellectual stamina, and discipline. These skills are important for success in academic endeavors. Learning calligraphy is also an artistic creative process that builds pride. The brain is also strengthened through the calligraphy writing process.
Test v1

This 3 page test file contains brief placeholder text on each page to serve as a sample document. The test file consists of 3 pages that provide minimal placeholder content for testing summarization purposes.
Instructions MINOX MD 7x42 C | Optics Trade

Instructions MINOX MD 7x42 C | Optics Trade
http://www.optics-trade.eu/shop/en/shopby/manufacturer-minox.html
Kapitel 12:
Trading-Plattform & Trading-Typen

DIE PROFITLINIE
“PROFIT NEHMEN“-Funktion
“ANGEBOT EINHOLEN“-FUNKTION
ROLL FORWARD FUNKTION
INDIKATOR ZUR BÖRSENSTIMMUNG
MOBILE TRADING
Coagulación 4

Este documento resume los conceptos clave de la coagulación sanguínea, incluyendo el papel de las plaquetas, los factores de coagulación, la vitamina K, la warfarina y la heparina. Explica cómo las pruebas de laboratorio como el TPT, TP e INR ayudan a determinar si existe un problema en la vía intrínseca o extrínseca de la coagulación. Finalmente, destaca la importancia de monitorear estas pruebas para ajustar de manera adecuada los niveles de anticoagulantes como la
Boletim200 iac

O documento fornece informações sobre o abacaxizeiro, incluindo cultivares, clima e solo adequados, práticas de propagação, plantio e manejo da cultura. É descrita a importância econômica e nutricional do abacaxi, bem como seus usos na indústria de alimentos e na obtenção de subprodutos.
Presentacion de herpes zoster

El documento describe la varicela y el herpes zóster, causados por el virus varicela zóster. El herpes zóster ocurre cuando el virus se reactiva después de haber tenido varicela, causando una erupción dolorosa en un dermatoma. Los síntomas incluyen erupciones cutáneas, vesículas y dolor neural. El riesgo aumenta con la edad y en personas inmunocomprometidas. No existe cura, pero los antivirales y la vacuna pueden prevenir brotes.
New Symfony Tips & Tricks (SymfonyCon Paris 2015)

This talk included tens of tips and tricks, new features and rarely used options for Symfony and its ecosystem. Besides the full-stack Symfony framework, other related technologies were mentioned, like Doctrine, Composer, Twig, PHPUnit and Monolog.
Andere mochten auch (14)
Buurgerichte zorg als toekomstmodel - Herwig Teugels

Buurgerichte zorg als toekomstmodel - Herwig Teugels
Mehr von Microsoft Österreich
Shape the Future

Hier finden Sie eine Auswahl der in Österreich verfügbaren Shape the Future Endgeräte.
Information Security @ AVL

H. Czamai presented on information security at AVL, an automotive engineering company. AVL has implemented an Information Security Management System (ISMS) based on ISO 27001 to ensure information security through organizational and technical measures. This includes an ISO 27001 certification, security awareness training, global policies, audits, and technical controls like firewalls, access management, and encryption. AVL also manages risks through threat detection and vulnerability management processes. The presentation discussed AVL's global operations, top security threats, and cloud security strategy using Microsoft services like Azure and Intune.
Secure the modern Enterprise

The document discusses cybersecurity and protecting information. It provides statistics on why organizations want to protect information, such as to reduce data leakage, meet compliance requirements, and partition sensitive data from unauthorized users. It then lists some of Microsoft's security capabilities for protecting devices, customer data in the cloud, on-premises environments, and customer data both in the cloud and on-premises.
Microsoft Digital Crimes Unit

Big data, cybersecurity threats, and cybercrime are growing issues according to the document. Microsoft takes a layered approach to security across its many products and services to help protect customers. Key aspects of Microsoft's security approach include detection of threats using signals and machine learning, responding quickly to issues, and protecting endpoints. The Microsoft Digital Crimes Unit works with law enforcement and through public-private partnerships to disrupt malware and fight technical support scams and other technology-facilitated crimes.
Microsoft: #DigitaleHelden Symposium - Graphic Recording

Graphic recording is a visual documentation technique used at events like conferences and meetings. A graphic recorder listens to the event and draws illustrations, diagrams, and icons that depict the key topics, discussions, and takeaways in visual form. These graphic recordings provide a unique visual summary of the event in a concise and engaging format that is easy for participants and observers to understand.
Digitale Transformation: Technologie und Mensch - die nächsten 5 Jahre

Speaker: Gerd Leonhard
Microsoft #DigitaleHelden Symposium
Digital Transformation "Book of Dreams"

Digital transformation can help organizations engage customers, empower employees, optimize operations, and transform products. To engage customers, organizations can deliver personalized experiences for customers across any device or location. They can also gain insights from customer data to improve marketing effectiveness and customer satisfaction. Transforming products involves managing the full product lifecycle and collaborating with customers on design. Optimizing operations focuses on digitizing processes, automating customer service, and using data-driven supply chain management. Empowering employees involves tools for productivity, collaboration, and talent development to meet changing customer needs.
Smart Buildings & IoT

This document discusses how smart buildings and the Internet of Things (IoT) can empower organizations by providing insights, increasing agility, and improving customer care. It describes how connecting devices and analyzing data can optimize building utilization, productivity, and costs. The document outlines Microsoft's vision for a smart buildings platform that uses IoT, cloud services, and analytics to gain visibility, manage key performance indicators, and anticipate and address issues. It also discusses how Microsoft technologies can support building management systems, integrate sensor data from various sources, and apply machine learning to enhance predictive capabilities.
Mit Simplicity und Storytelling zum „Warum“: Motivation und Führung einer neu...

Mit Simplicity und Storytelling zum „Warum“: Motivation und Führung einer neu...Microsoft Österreich
Mit Simplicity und Storytelling zum „Warum“: Motivation und Führung einer neuen Generation.
Speaker: Ali Mahlodji, CEO whatchadoEnable Mobility and Improve Cost Efficiency within a Secure Ecosystem - Futur...

Enable Mobility and Improve Cost Efficiency within a Secure Ecosystem - Futur...Microsoft Österreich
Enable Mobility and Improve Cost Efficiency within a Secure Ecosystem - Future Decoded
Speaker: Rudolf Roschitz & Bernahrd EdelbacherModernes Rechenzentrum - Future Decoded

Modernes Rechenzentrum - Future Decoded
Speaker: Christian Decker, Cloud Architect - Base IT
Microsoft Trusted Cloud - Security Privacy & Control, Compliance, Transparency

Microsoft Trusted Cloud - Security Privacy & Control, Compliance, Transparency
Speaker: DI. Harald Leitenmüller & Stephan Winklbauer
Microsoft Trusted Cloud - Harald Leitenmüller (Microsoft)

The document discusses security, privacy, and control of customer data in Microsoft's trusted cloud. It addresses questions about whether customer data is safe, whether it belongs to customers, and whether customers have control. It outlines Microsoft's technical and process controls to encrypt customer data, ensure only authorized access, and give customers choice over and deletion of their data. These controls are aimed to address issues raised by the invalidation of the EU's Safe Harbor framework and ensure compliance with European data protection laws.
Enable Mobility and Improve Cost Efficiency within a Secure Ecosystem - S&T

Mobile Efficiency:
Wie man IT als mobiles Service zur Verfügung stellen kann, ohne die Datensicherheit im Unternehmen zu gefährden.
In Kooperation mit S&T
IMMERSIVE AND HYPER-INTELLIGENT WORLD 2025 - TrendOne

IMMERSIVE AND HYPER-INTELLIGENT WORLD 2025 - TrendOne
ÖBB - Bahnstrombedarfsprognose- mit Advanced Analytics 

ÖBB - Bahnstrombedarfsprognose- mit Advanced Analytics mehrere hunderttausend Euro Energiekosten einsparen.
In Kooperation mit ÖBB-Produktions GmbH und Cubido
New World of Work - Solvion

Wie flexible Arbeitsweisen für mehr Produktivität und Innovationskraft in ihrem Unternehmen sorgen.
In Kooperation mit Semperit, CASAG und Solvion
Der Hund an der digitalen Leine - tractive

Der Hund an der digitalen Leine oder: Wie Sie aus ihrem Wissen neue Produkte und Services entwickeln.
In Kooperation mit tractive.
Aufbau einer erfolgreichen Vertriebsabteilung – Neue Erkenntnisse aus der Ver...

Aufbau einer erfolgreichen Vertriebsabteilung – Neue Erkenntnisse aus der Ver...Microsoft Österreich
Aufbau einer erfolgreichen Vertriebsabteilung – Neue Erkenntnisse aus der Vertriebsforschung 2015Mehr von Microsoft Österreich (20)
Microsoft: #DigitaleHelden Symposium - Graphic Recording

Microsoft: #DigitaleHelden Symposium - Graphic Recording
Digitale Transformation: Technologie und Mensch - die nächsten 5 Jahre

Digitale Transformation: Technologie und Mensch - die nächsten 5 Jahre
Mit Simplicity und Storytelling zum „Warum“: Motivation und Führung einer neu...

Mit Simplicity und Storytelling zum „Warum“: Motivation und Führung einer neu...
Enable Mobility and Improve Cost Efficiency within a Secure Ecosystem - Futur...

Enable Mobility and Improve Cost Efficiency within a Secure Ecosystem - Futur...
Microsoft Trusted Cloud - Security Privacy & Control, Compliance, Transparency

Microsoft Trusted Cloud - Security Privacy & Control, Compliance, Transparency
Microsoft Trusted Cloud - Harald Leitenmüller (Microsoft)

Microsoft Trusted Cloud - Harald Leitenmüller (Microsoft)
Enable Mobility and Improve Cost Efficiency within a Secure Ecosystem - S&T

Enable Mobility and Improve Cost Efficiency within a Secure Ecosystem - S&T
IMMERSIVE AND HYPER-INTELLIGENT WORLD 2025 - TrendOne

IMMERSIVE AND HYPER-INTELLIGENT WORLD 2025 - TrendOne
ÖBB - Bahnstrombedarfsprognose- mit Advanced Analytics 

ÖBB - Bahnstrombedarfsprognose- mit Advanced Analytics
Aufbau einer erfolgreichen Vertriebsabteilung – Neue Erkenntnisse aus der Ver...

Aufbau einer erfolgreichen Vertriebsabteilung – Neue Erkenntnisse aus der Ver...
