Voice browser
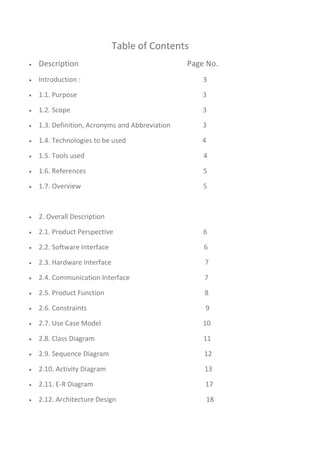
- 1. Table of Contents Description Page No. Introduction : 3 1.1. Purpose 3 1.2. Scope 3 1.3. Definition, Acronyms and Abbreviation 3 1.4. Technologies to be used 4 1.5. Tools used 4 1.6. References 5 1.7. Overview 5 2. Overall Description 2.1. Product Perspective 6 2.2. Software Interface 6 2.3. Hardware Interface 7 2.4. Communication Interface 7 2.5. Product Function 8 2.6. Constraints 9 2.7. Use Case Model 10 2.8. Class Diagram 11 2.9. Sequence Diagram 12 2.10. Activity Diagram 13 2.11. E-R Diagram 17 2.12. Architecture Design 18
- 2. 2.13. Assumptions and Dependencies 3. Specific Requirements 3.1.Supplementary Requirements 18 19
- 3. 1. Introduction 1.1 Purpose Voice Based Web Browser: Voice based web to make information accessible to users who may not be able to read or write, or who do not have access to the Internet. Users can access the voice-based web using a toll-free number, through a variety of ways including a voice recognition system or a tone phone. Unlike a computer interface, a voice interface needs no keyboard, no mouse, no screen, freeing users from these barriers to access and action. It requires no training. It is accessible to anyone with a telephone. Voice is mobile—information can be sent and retrieved from anywhere. Since customers can have access at anytime from anywhere, voice makes it possible to use time more effectively. Fast and efficient, voice frees users from not only the desktop, but even the laptop. 1.2 Scope : The user gives the request through the voice or text using phone ,personal computer or Touch tone. The request goes to the voice browser.If the request is voice, speech recognition converts voice into text. Checks the grammers and then using speech synthesis to convert text into pre-recorded audio. The pre-recored audio should be store in the administrator.it should display to the user. 1.3. Definitions, Acronyms and Abbreviations : • ADMIN-Administrator has the authority for convert the voice into text,text into voice and then displaying to the user. • ASR-Automatic Speech Recognition is to convert the speech into text. • HTML – Hypertext Markup Language is to create static websites.
- 4. • J2EE – Java 2 Enterprise Edition is a programming platform and it is the part of the java platform for developing and running distributed java applications. • EJB – Enterprise java bean, it is architecture for the development and deployment of transactional, distributed object applications-based, server- side software component. • RSA – Rational Software Architect is a designer toolkit which is designed for develop more complex projects by providing fully dynamic web service. • DB2 – Database 2 is the database management system that provides a flexible and efficient database platform to erect strong on demand business applications. • UML- Unified Modeling Language is a standard language for writing software blueprints. The UML may be used to visualize, specify, construct and document • XML - Extensive Markup Language used for data transfer and XML is stored naturally in DB2 • HTTP – Hypertext transfer protocol is a transaction oriented client/server protocol between web browser and a web server. • HTTPS – Secure hypertext transfer protocol is a hypertext transfer protocol over secure socket layer. 1.4 Technologies used: HTML – Hyper Text Markup Language JAVA – Application architecture XML – Extensive Mark Up Language Java Script – Script Language AJAX – Asynchronous Java script And XMLPage J2EE – Application architecture. 1.5. Tools used: • RSA – Rational Software Architect 7.0 • DB2 9 – Database • WAS – Websphere Application Server 6.0
- 5. • TSM – Tivoli Storage Manager 1.6 References : IBM TGMC Sample Synopsis. IBM – www.ibm.in/developerworks. Wikipedia - www.wikipedia.com. Database Management Systems - korth. 1.7 Overview : Existing System: Type the text search the content who may not be able to read or write people does not access it Drawbacks: WAP(Cellular phones, Palm Pilots)access to the web: Small screens: For web phones, theres an incredibly small viewing area; palmtops are barely better. Speed of access: All devices have slow access. Limited or fragmented availability: Wireless web access is sporadic in many areas and entirely unavailable in other areas. Awkward input: Palms Graffiti, touchtone pads, or even tiny QWERTY keyboards are awkward for any amount of writing, even a short email. Price: Many technology limitations are being addressed by higher-end devices and services. But the entry price for a good wireless web palmtop with decent display, keyboard, and speed is easily $700 to $900, not including monthly access. Lack of user habit: It takes some patience and overcoming the learning curve to get the hang of it -- connecting, putting in an address, typing. Users just arent used to the idea and protocol yet.
- 6. Proposed System: Voice Browsers offer the promise of allowing everyone to access Web based services from any phone, making it practical to access the Web any time and anywhere, whether at home, on the move, or at work. Users will able to choose whether to respond by a key press or a spoken command. Voice browsers allow people to access the Web using speech synthesis, pre-recorded audio, and speech recognition. Our plan: Accept the voice commands Output should be converted into speech 2. Overall Description 2.1. Product Perspective: 2.2. Software Interface Client on Internet Web Browser, Operating System (any)
- 7. Web Server WASCE, Operating System (any) Data Base Server DB2, Operating System (any) Development End RAD (J2EE, Java, Java Bean, Servlets, HTML, XML, AJAX), DB2, OS (Windows), WebSphere(Web Server) 2.3. Hardware Interface Minimum Requirements: 2.4. Communication Interface: • Voice based web browser will be connected to the World Wide Web. • The HTTP protocol will be used to facilitate communication between the client and server.
- 8. 2.5 Product Function: Voice based web browser- Easy to use - for people with no knowledge or fear of computers. Voice interaction can escape the physical limitations on keypads and displays as mobile devices become ever smaller. Many companies to offer services over the phone via menus traversed using the phones keypad. Voice Browsers arethe next generation of call centers, which will become Voice Web portals to the companies services and related websites, whether accessed via the telephone networks via the Internet. Some of the features of the product are as follow: Accessing business information: The corporate "front desk" which asks callers who or what they want • Automated telephone ordering services • Support desks • Order tracking • Airline arrival and departure information Accessing public information: • Community information such as weather, traffic conditions, school closures, directions and events • Local, national and international news • National and international stock market information • Business and e-commerce transactions Accessing personal information: • Voice mail
- 9. • Calendars, address and telephone lists • Personal horoscope • Personal newsletter • To-do lists, shopping lists, and calorie counters 2.6. Constraints : • The information of all the users must be stored in a database that is accessible by the Administrator. • Voice based web browser system is connected to the computer and is running all 24 hours a day. • The users can access Online Book Sales with mobile SMS System from any computer that has Internet browsing capabilities and an Internet connection.
- 10. 2.7 Use Case Model :
- 12. 2.9.Squence Diagram : 2.9.1.User Interaction via Browser :
- 13. 2.9.2. Uploading and downloading Resources:
- 15. 2.10.1.User Interation via Browser
- 18. 2.12.Architecture Diagram: 2.13. Assumption and Dependencies : • The Computer should have Internet connection and Internet server capabilities. • The users know the English language, as the user interface will be provided in English.
- 19. 3.3Supplementary Requirement : Safety Requirements: Highly recommend Kaspersky 2010 internet security to been Installed in users Pc to prevent the harm that may occurs by unwanted malicious software’s, phishing URLs and all the types of virus attacks during using this application.. Security Requirements : All users should be properly authenticated before allowed entry into the system authentication will be based on an E-mail address, and a password. All activities on the system must be logged. Non-Functional Requirements : • Secure access of confidential data (user’s details). SSL can be used. • 24 X 7 availability. • Better component design to get better performance at peak time. • Flexible service based architecture will be highly desirable for future extension. Other Requirements: The user must be agreed with all the term and conditions that have provided by the System Administrator, local authority and Should Obey to the all International standards and Protocols.