Journey to cyber resilience
•
0 gefällt mir•953 views
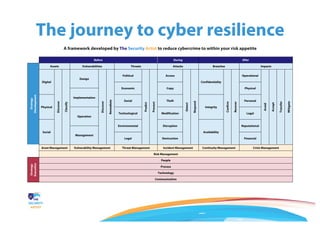
A framework developed by The Security Artist to reduce cybercrime to within your risk appetite. This was developed specifically to address the shortcomings of other frameworks such as ISO 27001; COBIT 5; and even the NIST cybersecurity framework.
Melden
Teilen
Melden
Teilen
Downloaden Sie, um offline zu lesen
Empfohlen
Empfohlen
Weitere ähnliche Inhalte
Was ist angesagt?
Was ist angesagt? (20)
Cybersecurity Frameworks | NIST Cybersecurity Framework | Cybersecurity Certi...

Cybersecurity Frameworks | NIST Cybersecurity Framework | Cybersecurity Certi...
How To Handle Cybersecurity Risk PowerPoint Presentation Slides

How To Handle Cybersecurity Risk PowerPoint Presentation Slides
Enterprise Security Architecture for Cyber Security

Enterprise Security Architecture for Cyber Security
Integrating ISO/IEC 27001 and ISO 31000 for Effective Information Security an...

Integrating ISO/IEC 27001 and ISO 31000 for Effective Information Security an...
Advanced Cybersecurity Risk Management: How to successfully address your Cybe...

Advanced Cybersecurity Risk Management: How to successfully address your Cybe...
Cybersecurity Incident Management Powerpoint Presentation Slides

Cybersecurity Incident Management Powerpoint Presentation Slides
The Journey to Cyber Resilience in a World of Fear, Uncertainty and Doubt

The Journey to Cyber Resilience in a World of Fear, Uncertainty and Doubt
Cyber Resilience – Strengthening Cybersecurity Posture & Preparedness by Phil...

Cyber Resilience – Strengthening Cybersecurity Posture & Preparedness by Phil...
The Next Generation of Security Operations Centre (SOC)

The Next Generation of Security Operations Centre (SOC)
Andere mochten auch
Sean McCloskey: How do we Strengthen the Public-Private Partnership to Mitiga...

Sean McCloskey: How do we Strengthen the Public-Private Partnership to Mitiga...Government Technology and Services Coalition
Andere mochten auch (17)
Sean McCloskey: How do we Strengthen the Public-Private Partnership to Mitiga...

Sean McCloskey: How do we Strengthen the Public-Private Partnership to Mitiga...
Science of Security: Cyber Ecosystem Attack Analysis Methodology

Science of Security: Cyber Ecosystem Attack Analysis Methodology
Cyber security resilience ESRM Conference Amsterdam 2016

Cyber security resilience ESRM Conference Amsterdam 2016
Balancing speed & agility with security & governance (July 2016)

Balancing speed & agility with security & governance (July 2016)
The Measure of Success: Security Metrics to Tell Your Story

The Measure of Success: Security Metrics to Tell Your Story
How to Steer Cyber Security with Only One KPI: The Cyber Risk Resilience

How to Steer Cyber Security with Only One KPI: The Cyber Risk Resilience
Ähnlich wie Journey to cyber resilience
Ähnlich wie Journey to cyber resilience (20)
The Role of Incident Response in Cybersecurity: Protecting Your Organization

The Role of Incident Response in Cybersecurity: Protecting Your Organization
The Role of Incident Response in Cybersecurity: Protecting Your Organization

The Role of Incident Response in Cybersecurity: Protecting Your Organization
Cisco Connect 2018 Malaysia - Risk less, achieve more with proactive security

Cisco Connect 2018 Malaysia - Risk less, achieve more with proactive security
ISACA UAE - Importance of Human-Centric Approaches to Cyber Security

ISACA UAE - Importance of Human-Centric Approaches to Cyber Security
Stay Ahead of Threats The Importance of Cyber Security Services.pdf

Stay Ahead of Threats The Importance of Cyber Security Services.pdf
2017 InfraGard Atlanta Conference - Matthew Rosenquist

2017 InfraGard Atlanta Conference - Matthew Rosenquist
Bolg Plus the-digital-immune-system-safeguarding-the-connected-world-20230821...

Bolg Plus the-digital-immune-system-safeguarding-the-connected-world-20230821...
Bolg Plus the-digital-immune-system-safeguarding-the-connected-world-20230821...

Bolg Plus the-digital-immune-system-safeguarding-the-connected-world-20230821...
Kürzlich hochgeladen
unwanted pregnancy Kit [+918133066128] Abortion Pills IN Dubai UAE Abudhabi![unwanted pregnancy Kit [+918133066128] Abortion Pills IN Dubai UAE Abudhabi](data:image/gif;base64,R0lGODlhAQABAIAAAAAAAP///yH5BAEAAAAALAAAAAABAAEAAAIBRAA7)
![unwanted pregnancy Kit [+918133066128] Abortion Pills IN Dubai UAE Abudhabi](data:image/gif;base64,R0lGODlhAQABAIAAAAAAAP///yH5BAEAAAAALAAAAAABAAEAAAIBRAA7)
unwanted pregnancy Kit [+918133066128] Abortion Pills IN Dubai UAE AbudhabiAbortion pills in Kuwait Cytotec pills in Kuwait
VVVIP Call Girls In Greater Kailash ➡️ Delhi ➡️ 9999965857 🚀 No Advance 24HRS...

VVVIP Call Girls In Greater Kailash ➡️ Delhi ➡️ 9999965857 🚀 No Advance 24HRS...Call Girls In Delhi Whatsup 9873940964 Enjoy Unlimited Pleasure
Kürzlich hochgeladen (20)
Uneak White's Personal Brand Exploration Presentation

Uneak White's Personal Brand Exploration Presentation
Enhancing and Restoring Safety & Quality Cultures - Dave Litwiller - May 2024...

Enhancing and Restoring Safety & Quality Cultures - Dave Litwiller - May 2024...
Call Girls From Pari Chowk Greater Noida ❤️8448577510 ⊹Best Escorts Service I...

Call Girls From Pari Chowk Greater Noida ❤️8448577510 ⊹Best Escorts Service I...
unwanted pregnancy Kit [+918133066128] Abortion Pills IN Dubai UAE Abudhabi![unwanted pregnancy Kit [+918133066128] Abortion Pills IN Dubai UAE Abudhabi](data:image/gif;base64,R0lGODlhAQABAIAAAAAAAP///yH5BAEAAAAALAAAAAABAAEAAAIBRAA7)
![unwanted pregnancy Kit [+918133066128] Abortion Pills IN Dubai UAE Abudhabi](data:image/gif;base64,R0lGODlhAQABAIAAAAAAAP///yH5BAEAAAAALAAAAAABAAEAAAIBRAA7)
unwanted pregnancy Kit [+918133066128] Abortion Pills IN Dubai UAE Abudhabi
Call Girls Pune Just Call 9907093804 Top Class Call Girl Service Available

Call Girls Pune Just Call 9907093804 Top Class Call Girl Service Available
Falcon's Invoice Discounting: Your Path to Prosperity

Falcon's Invoice Discounting: Your Path to Prosperity
MONA 98765-12871 CALL GIRLS IN LUDHIANA LUDHIANA CALL GIRL

MONA 98765-12871 CALL GIRLS IN LUDHIANA LUDHIANA CALL GIRL
VVVIP Call Girls In Greater Kailash ➡️ Delhi ➡️ 9999965857 🚀 No Advance 24HRS...

VVVIP Call Girls In Greater Kailash ➡️ Delhi ➡️ 9999965857 🚀 No Advance 24HRS...
👉Chandigarh Call Girls 👉9878799926👉Just Call👉Chandigarh Call Girl In Chandiga...

👉Chandigarh Call Girls 👉9878799926👉Just Call👉Chandigarh Call Girl In Chandiga...
Ensure the security of your HCL environment by applying the Zero Trust princi...

Ensure the security of your HCL environment by applying the Zero Trust princi...
Call Girls Navi Mumbai Just Call 9907093804 Top Class Call Girl Service Avail...

Call Girls Navi Mumbai Just Call 9907093804 Top Class Call Girl Service Avail...
Call Girls Service In Old Town Dubai ((0551707352)) Old Town Dubai Call Girl ...

Call Girls Service In Old Town Dubai ((0551707352)) Old Town Dubai Call Girl ...
0183760ssssssssssssssssssssssssssss00101011 (27).pdf

0183760ssssssssssssssssssssssssssss00101011 (27).pdf
Call Girls Ludhiana Just Call 98765-12871 Top Class Call Girl Service Available

Call Girls Ludhiana Just Call 98765-12871 Top Class Call Girl Service Available
Journey to cyber resilience
- 1. The journey to cyber resilience A framework developed by The Security Artist to reduce cybercrime to within your risk appetite Before During After Strategy Development Assets Vulnerabilities Threats Attacks Breaches Impacts Digital Discover Classify Design Discover Remediate Political Predict Prevent Access Detect Respond Confidentiality Confirm Recover Operational Avoid Accept Transfer Mitigate Economic Copy Physical Implementation Physical Social Theft Integrity Personal Operation Technological Modification Legal Social Environmental Disruption Availability Reputational Management Legal Destruction Financial Asset Management Vulnerability Management Threat Management Incident Management Continuity Management Crisis Management Risk Management Strategy Execution People Process Technology Communication
