The not-so-obvious skill that cyber security professionals must learn or else
•
0 gefällt mir•573 views
Melden
Teilen
Melden
Teilen
Downloaden Sie, um offline zu lesen
Empfohlen
Compliance in the framework of corporate governance (side panel 2) - Oliver O...

Compliance in the framework of corporate governance (side panel 2) - Oliver O...e-Democracy Conference
Empfohlen
Compliance in the framework of corporate governance (side panel 2) - Oliver O...

Compliance in the framework of corporate governance (side panel 2) - Oliver O...e-Democracy Conference
Inside Shanghai Tower - Exclusive interview with Chief Architect, Marshall St...

Inside Shanghai Tower - Exclusive interview with Chief Architect, Marshall St...Darwin Jayson Mariano
Saudi Arabia [ Abortion pills) Jeddah/riaydh/dammam/++918133066128☎️] cytotec tablets uses abortion pills 💊💊 How effective is the abortion pill? 💊💊 +918133066128) "Abortion pills in Jeddah" how to get cytotec tablets in Riyadh " Abortion pills in dammam*💊💊 The abortion pill is very effective. If you’re taking mifepristone and misoprostol, it depends on how far along the pregnancy is, and how many doses of medicine you take:💊💊 +918133066128) how to buy cytotec pills
At 8 weeks pregnant or less, it works about 94-98% of the time. +918133066128[ 💊💊💊 At 8-9 weeks pregnant, it works about 94-96% of the time. +918133066128) At 9-10 weeks pregnant, it works about 91-93% of the time. +918133066128)💊💊 If you take an extra dose of misoprostol, it works about 99% of the time. At 10-11 weeks pregnant, it works about 87% of the time. +918133066128) If you take an extra dose of misoprostol, it works about 98% of the time. In general, taking both mifepristone and+918133066128 misoprostol works a bit better than taking misoprostol only. +918133066128 Taking misoprostol alone works to end the+918133066128 pregnancy about 85-95% of the time — depending on how far along the+918133066128 pregnancy is and how you take the medicine. +918133066128 The abortion pill usually works, but if it doesn’t, you can take more medicine or have an in-clinic abortion. +918133066128 When can I take the abortion pill?+918133066128 In general, you can have a medication abortion up to 77 days (11 weeks)+918133066128 after the first day of your last period. If it’s been 78 days or more since the first day of your last+918133066128 period, you can have an in-clinic abortion to end your pregnancy.+918133066128
Why do people choose the abortion pill? Which kind of abortion you choose all depends on your personal+918133066128 preference and situation. With+918133066128 medication+918133066128 abortion, some people like that you don’t need to have a procedure in a doctor’s office. You can have your medication abortion on your own+918133066128 schedule, at home or in another comfortable place that you choose.+918133066128 You get to decide who you want to be with during your abortion, or you can go it alone. Because+918133066128 medication abortion is similar to a miscarriage, many people feel like it’s more “natural” and less invasive. And some+918133066128 people may not have an in-clinic abortion provider close by, so abortion pills are more available to+918133066128 them. +918133066128 Your doctor, nurse, or health center staff can help you decide which kind of abortion is best for you. +918133066128 More questions from patients: Saudi Arabia+918133066128 CYTOTEC Misoprostol Tablets. Misoprostol is a medication that can prevent stomach ulcers if you also take NSAID medications. It reduces the amount of acid in your stomach, which protects your stomach lining. The brand name of this medication is Cytotec®.+918133066128) Unwanted Kit Mifty kit IN Salmiya (+918133066128) Abortion pills IN Salmiyah Cytotec pills

Mifty kit IN Salmiya (+918133066128) Abortion pills IN Salmiyah Cytotec pillsAbortion pills in Kuwait Cytotec pills in Kuwait
Weitere ähnliche Inhalte
Mehr von Darwin Jayson Mariano
Inside Shanghai Tower - Exclusive interview with Chief Architect, Marshall St...

Inside Shanghai Tower - Exclusive interview with Chief Architect, Marshall St...Darwin Jayson Mariano
Mehr von Darwin Jayson Mariano (20)
Inside Shanghai Tower - Exclusive interview with Chief Architect, Marshall St...

Inside Shanghai Tower - Exclusive interview with Chief Architect, Marshall St...
Aiming for Alpha - Opportunities and Challenges for ETF Investors in Asia

Aiming for Alpha - Opportunities and Challenges for ETF Investors in Asia
6 Game-Changing Tips to Deal with Risk Management and Drug Safety Audit

6 Game-Changing Tips to Deal with Risk Management and Drug Safety Audit
How effective is double skin façade in preventing building heat loss

How effective is double skin façade in preventing building heat loss
Nagging Dilemmas in Airport Expansion (and how to deal with them)

Nagging Dilemmas in Airport Expansion (and how to deal with them)
The 3-Tier Process to Keep Pavements and Runways in Top Form 

The 3-Tier Process to Keep Pavements and Runways in Top Form
Latin America vs Southeast Asia: The Race for Private Equity Supremacy

Latin America vs Southeast Asia: The Race for Private Equity Supremacy
7 Most Significant Underground Projects in Asia Today [Infograph]![7 Most Significant Underground Projects in Asia Today [Infograph]](data:image/gif;base64,R0lGODlhAQABAIAAAAAAAP///yH5BAEAAAAALAAAAAABAAEAAAIBRAA7)
![7 Most Significant Underground Projects in Asia Today [Infograph]](data:image/gif;base64,R0lGODlhAQABAIAAAAAAAP///yH5BAEAAAAALAAAAAABAAEAAAIBRAA7)
7 Most Significant Underground Projects in Asia Today [Infograph]
SKY HIGH - The 7 Most Remarkable Tall Building Projects in the World

SKY HIGH - The 7 Most Remarkable Tall Building Projects in the World
The Changing Face of Asia's Geospatial Intelligence 

The Changing Face of Asia's Geospatial Intelligence
Battle of Mega Bridges - The 7 Highly Notable Mega Bridge Projects 

Battle of Mega Bridges - The 7 Highly Notable Mega Bridge Projects
TRAILBLAZING: Shared Services and Outsourcing Trends in Asia 2013 

TRAILBLAZING: Shared Services and Outsourcing Trends in Asia 2013
Kürzlich hochgeladen
Saudi Arabia [ Abortion pills) Jeddah/riaydh/dammam/++918133066128☎️] cytotec tablets uses abortion pills 💊💊 How effective is the abortion pill? 💊💊 +918133066128) "Abortion pills in Jeddah" how to get cytotec tablets in Riyadh " Abortion pills in dammam*💊💊 The abortion pill is very effective. If you’re taking mifepristone and misoprostol, it depends on how far along the pregnancy is, and how many doses of medicine you take:💊💊 +918133066128) how to buy cytotec pills
At 8 weeks pregnant or less, it works about 94-98% of the time. +918133066128[ 💊💊💊 At 8-9 weeks pregnant, it works about 94-96% of the time. +918133066128) At 9-10 weeks pregnant, it works about 91-93% of the time. +918133066128)💊💊 If you take an extra dose of misoprostol, it works about 99% of the time. At 10-11 weeks pregnant, it works about 87% of the time. +918133066128) If you take an extra dose of misoprostol, it works about 98% of the time. In general, taking both mifepristone and+918133066128 misoprostol works a bit better than taking misoprostol only. +918133066128 Taking misoprostol alone works to end the+918133066128 pregnancy about 85-95% of the time — depending on how far along the+918133066128 pregnancy is and how you take the medicine. +918133066128 The abortion pill usually works, but if it doesn’t, you can take more medicine or have an in-clinic abortion. +918133066128 When can I take the abortion pill?+918133066128 In general, you can have a medication abortion up to 77 days (11 weeks)+918133066128 after the first day of your last period. If it’s been 78 days or more since the first day of your last+918133066128 period, you can have an in-clinic abortion to end your pregnancy.+918133066128
Why do people choose the abortion pill? Which kind of abortion you choose all depends on your personal+918133066128 preference and situation. With+918133066128 medication+918133066128 abortion, some people like that you don’t need to have a procedure in a doctor’s office. You can have your medication abortion on your own+918133066128 schedule, at home or in another comfortable place that you choose.+918133066128 You get to decide who you want to be with during your abortion, or you can go it alone. Because+918133066128 medication abortion is similar to a miscarriage, many people feel like it’s more “natural” and less invasive. And some+918133066128 people may not have an in-clinic abortion provider close by, so abortion pills are more available to+918133066128 them. +918133066128 Your doctor, nurse, or health center staff can help you decide which kind of abortion is best for you. +918133066128 More questions from patients: Saudi Arabia+918133066128 CYTOTEC Misoprostol Tablets. Misoprostol is a medication that can prevent stomach ulcers if you also take NSAID medications. It reduces the amount of acid in your stomach, which protects your stomach lining. The brand name of this medication is Cytotec®.+918133066128) Unwanted Kit Mifty kit IN Salmiya (+918133066128) Abortion pills IN Salmiyah Cytotec pills

Mifty kit IN Salmiya (+918133066128) Abortion pills IN Salmiyah Cytotec pillsAbortion pills in Kuwait Cytotec pills in Kuwait
Kürzlich hochgeladen (20)
Mifty kit IN Salmiya (+918133066128) Abortion pills IN Salmiyah Cytotec pills

Mifty kit IN Salmiya (+918133066128) Abortion pills IN Salmiyah Cytotec pills
FULL ENJOY Call Girls In Mahipalpur Delhi Contact Us 8377877756

FULL ENJOY Call Girls In Mahipalpur Delhi Contact Us 8377877756
KYC-Verified Accounts: Helping Companies Handle Challenging Regulatory Enviro...

KYC-Verified Accounts: Helping Companies Handle Challenging Regulatory Enviro...
FULL ENJOY Call Girls In Majnu Ka Tilla, Delhi Contact Us 8377877756

FULL ENJOY Call Girls In Majnu Ka Tilla, Delhi Contact Us 8377877756
The Coffee Bean & Tea Leaf(CBTL), Business strategy case study

The Coffee Bean & Tea Leaf(CBTL), Business strategy case study
B.COM Unit – 4 ( CORPORATE SOCIAL RESPONSIBILITY ( CSR ).pptx

B.COM Unit – 4 ( CORPORATE SOCIAL RESPONSIBILITY ( CSR ).pptx
The Path to Product Excellence: Avoiding Common Pitfalls and Enhancing Commun...

The Path to Product Excellence: Avoiding Common Pitfalls and Enhancing Commun...
How to Get Started in Social Media for Art League City

How to Get Started in Social Media for Art League City
Call Girls Hebbal Just Call 👗 7737669865 👗 Top Class Call Girl Service Bangalore

Call Girls Hebbal Just Call 👗 7737669865 👗 Top Class Call Girl Service Bangalore
Call Girls Jp Nagar Just Call 👗 7737669865 👗 Top Class Call Girl Service Bang...

Call Girls Jp Nagar Just Call 👗 7737669865 👗 Top Class Call Girl Service Bang...
Yaroslav Rozhankivskyy: Три складові і три передумови максимальної продуктивн...

Yaroslav Rozhankivskyy: Три складові і три передумови максимальної продуктивн...
Lucknow 💋 Escorts in Lucknow - 450+ Call Girl Cash Payment 8923113531 Neha Th...

Lucknow 💋 Escorts in Lucknow - 450+ Call Girl Cash Payment 8923113531 Neha Th...
Ensure the security of your HCL environment by applying the Zero Trust princi...

Ensure the security of your HCL environment by applying the Zero Trust princi...
Russian Call Girls In Gurgaon ❤️8448577510 ⊹Best Escorts Service In 24/7 Delh...

Russian Call Girls In Gurgaon ❤️8448577510 ⊹Best Escorts Service In 24/7 Delh...
Grateful 7 speech thanking everyone that has helped.pdf

Grateful 7 speech thanking everyone that has helped.pdf
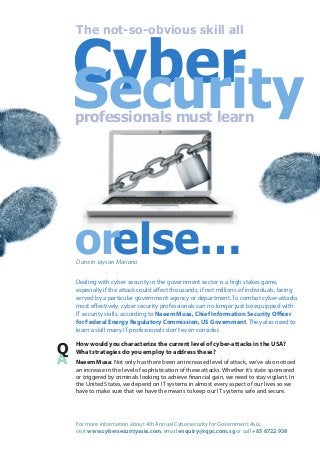
The not-so-obvious skill that cyber security professionals must learn or else
- 1. Cyber Security The not-so-obvious skill all professionals must learn orelse… Darwin Jayson Mariano Dealing with cyber security in the government sector is a high stakes game, especially if the attack could affect thousands, if not millions of individuals, being served by a particular government agency or department. To combat cyber-attacks most effectively, cyber security professionals can no longer just be equipped with IT security skills, according to Naeem Musa, Chief Information Security Officer for Federal Energy Regulatory Commission, US Government. They also need to learn a skill many IT professionals don’t even consider. Q A How would you characterize the current level of cyber-attacks in the USA? What strategies do you employ to address these? Naeem Musa: Not only has there been an increased level of attack, we’ve also noticed an increase in the level of sophistication of these attacks. Whether it’s state sponsored or triggered by criminals looking to achieve financial gain, we need to stay vigilant. In the United States, we depend on IT systems in almost every aspect of our lives so we have to make sure that we have the means to keep our IT systems safe and secure. For more information about 4th Annual Cybersecurity for Government Asia, visit www.cybersecurityasia.com, email enquiry@iqpc.com.sg or call +65 6722 938
- 2. My role obviously involves protecting our infrastructure to ensure that our data remains confidential. However, lately, we see a heightened level of attacks on our financial institutions, mostly driven by organised crime whose objective is to commit financial fraud and identity theft. There are state sponsored attacks that our government is also obviously addressing but that is not something I’m directly involved in. In addressing these issues, one of the most effective strategies is to educate the user community. But in dealing with the larger issue of cyber security, it is important to be aware of this “three-legged stool” strategy, which is: 1) technology, 2) process and 3) people. You really have to focus on each of those areas. You have to have a streamlined process and procedures in place to respond to an incident. You have to have the right level of technology in terms of the right firewalls and Trojan infection mechanisms. However, all of that would be futile if you’re not educating your user community. In our case, we’re doing a lot of education to the user level to ensure that when those people are targeted by phishing attacks, whether by unscrupulous individuals targeting them or them visiting different websites, potentially getting infected, they know how to respond and act in a way that will not compromise our IT security. We’re also trying to create mechanisms to prevent people from going to the wrong sites so the chance of getting infected is minimised. We have this whitelisting and blacklisting of sites, we deploy all kinds of technologies to prevent unauthorised executables on the entire network. At the same time, we monitor and scan our network regularly to see if there is any anomaly and then we try to detect, analyse and figure out if those anomalies can pose a threat or if they are within the tolerance level. So, really, a combination of the three: focus on the technology, focus on the processes and creating awareness in the user community. Q A From your perspective, how can governments in Asia, given the relative uniqueness of this region, address issues related to cyber security? Q A Given the nature of these attacks, should special emphasis be put on public sector as opposed to private sector? Naeem Musa: I think the cyber world is borderless. Organised crime does not discriminate and will always go after the gain. They could launch targeted attacks in Malaysia, Southeast Asia, Canada, Australia or the USA. As long as there’s a gain to be had, they’re going to go after it. So in that regard, everybody is facing the same set of challenges, especially from organised crime and state-sponsored espionage. We’ve also heard in the news how specific countries are even targeting telecommunications companies within the European continent. Bottom line is: the same potential for attacks exists for everybody regardless of the region and physical geography. Naeem Musa: Yes, certainly. Because the public sector is engaged in services to citizens, any time there are attacks or disruptions; it impacts the level of services you give to the public. In addition, you need to deal with whether it’s critical infrastructure that is at risk or national security information that is at stake, which could potentially harm the country. So you definitely have to have more focus on the public sector to ensure that the information’s confidentiality, integrity and availability are protected. For more information about 4th Annual Cybersecurity for Government Asia, visit www.cybersecurityasia.com, email enquiry@iqpc.com.sg or call +65 6722 938
- 3. Q A What are the best practices that you use to implement a robust cyber security program for government agencies? Naeem Musa: I think every security professional has to understand that security is a journey, not a destination. That means you could never do enough as the level of sophistication of attacks increases at a very rapid pace. The bad guys are always one step ahead. So the best strategy is to understand that it’s a continuous process, a journey. You have to continuously implement measures and put mitigating procedures in place. You need to emphasise awareness among your employees and staff and get them the right training. You have to practise incident response and be able to understand where your data is in order to protect and assess the damage in case that data is compromised. I think data leak prevention technology is maturing with time and if put in place, it will help aid security professionals discover attacks. In the end, it all boils down to combination of people, process and technology. The other important thing that you need to ensure is buy-in from management. Educate your management, don’t scare them. Educating and convincing your management to be on your side is a lot better than using fear tactics. Cyber security professionals are no longer just IT professionals, they are politicians. You have got to be smart, be able to sell your ideas, lobby and be able to get support for what you’re trying to implement. It is important to be able to get the funding that you need for your programs because just like anybody else, you need budget. And it’s not going to come easy unless you have the sophistication to lobby and sell your ideas to the CFO or the agency that will fund you. Naeem Musa, Chief Information Security Officer, Federal Energy Regulatory Commission, USA , will be speaking about “Preventing Government Data Leaks in an Increasingly Connected World” at the 4th Annual Cybersecurity for Government Asia happening on 5-6 March 2014 in Malaysia. For more information, visit www.cybersecurityasia.com For more information about 4th Annual Cybersecurity for Government Asia, visit www.cybersecurityasia.com, email enquiry@iqpc.com.sg or call +65 6722 938
