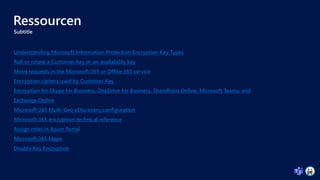
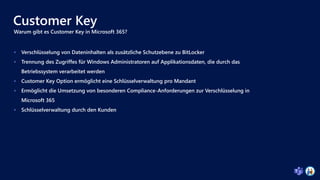
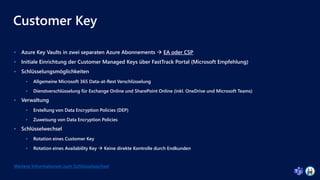
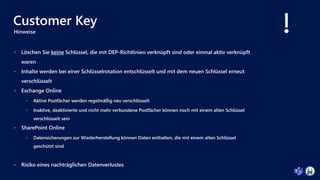
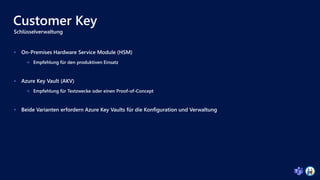
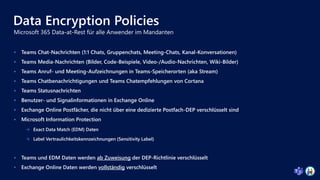
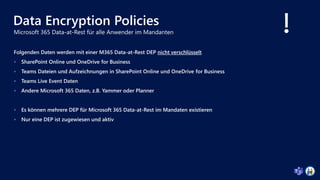
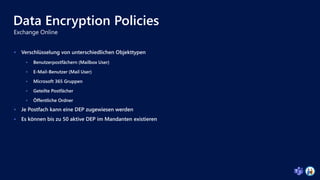
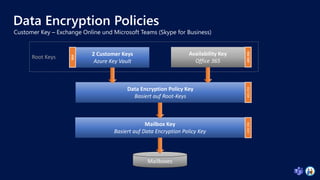
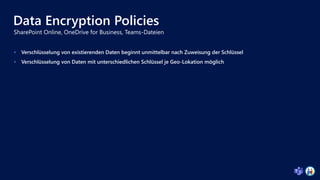
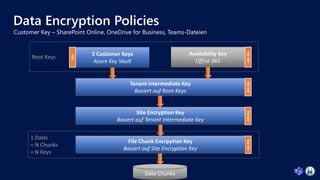
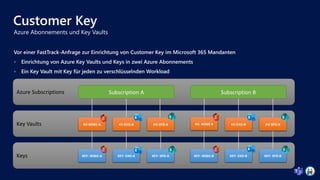
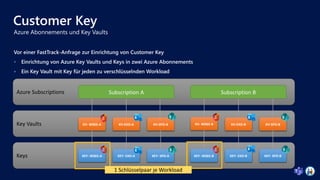
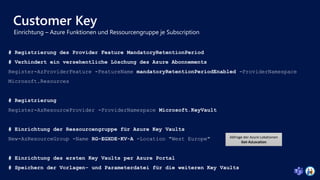
Das Dokument behandelt die Sicherung von Microsoft 365-Daten durch Service-Verschlüsselung, insbesondere durch die Implementierung von Kunden-Schlüsseln (Customer Key) zur zusätzlichen Absicherung und Verwaltung von Verschlüsselungsschlüsseln. Es beschreibt die verschiedenen Verschlüsselungsmethoden wie BitLocker, Azure-Disk- und Blob-Verschlüsselung sowie die Verwaltung von Data Encryption Policies für verschiedene Microsoft 365-Dienste wie Exchange Online und SharePoint Online. Weitere Themen sind die Anforderungen und Schritte zur Implementierung von Customer Key, einschließlich der Einrichtung von Azure Key Vaults und Zugriffsberechtigungen.




![Customer Key
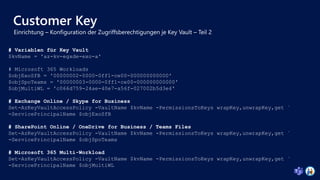
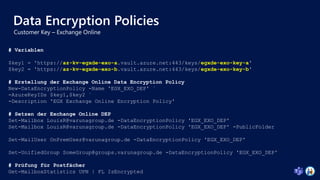
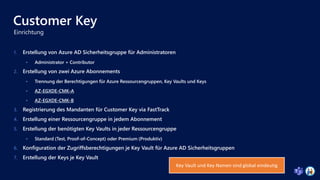
# Vorbereitung der Parameterdatei
"parameters": {
"name": {
"value": "az-kv-egxde-exo-a"
{…}
"accessPolicies": {
"value": [
{
"objectId": "754e1dbe-1bcf-4789-bbee-22410877fdb0",
"tenantId": "d320e379-89d3-4566-b834-6ca78a2f6399",
# Template-Datei laden und in Json konvertieren
$TemplateFile = [System.IO.File]::ReadAllText("C:CMKkeyvault-template.json")
$TemplateJson = ConvertFrom-Json $TemplateFile –AsHashtable
# Neue Ressourcengruppe erstellen
New-AzResourceGroupDeployment -ResourceGroupName "RG-EGXDE-KV-A" -TemplateObject `
$TemplateJson -TemplateParameterFile "C:CMKkeyvault-parameters-exo-a.json"
Key Vault Namen sind global eindeutig](https://image.slidesharecdn.com/securingmicrosoft365datawithserviceencryption-220324100804/85/Teams-Nation-2022-Securing-Microsoft-365-data-with-service-encryption-30-320.jpg)
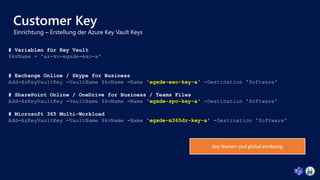
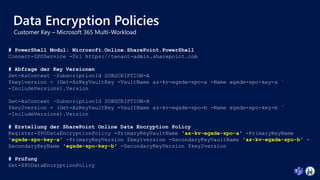
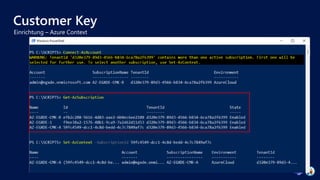
![Customer Key
# Variablen für Key Vault und Admin Sicherheitsgruppe
$kvName = 'az-kv-egxde-exo-a'
$kvAdminGroup = 'kv-Admins'
# Setzen der Zugriffsrichtlinie für Admininstratoren
Set-AzKeyVaultAccessPolicy -VaultName $kvName `
-ObjectId (Get-AzADGroup -SearchString $kvAdminGroup)[0].Id `
-PermissionsToKeys create,import,list,get,backup,restore
# Konfiguration der Contributor-Gruppe via Azure Portal für die Ressourcengruppe](https://image.slidesharecdn.com/securingmicrosoft365datawithserviceencryption-220324100804/85/Teams-Nation-2022-Securing-Microsoft-365-data-with-service-encryption-31-320.jpg)
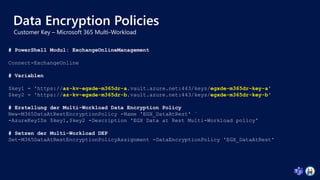
![Customer Key
# Variablen für Key Vault und Admin Sicherheitsgruppe
$kvName = 'az-kv-egxde-exo-a'
$kvAdminGroup = 'kv-Admins'
Set-AzKeyVaultAccessPolicy -VaultName $kvName `
-ObjectId (Get-AzADGroup -SearchString $kvAdminGroup)[0].Id `
-PermissionsToKeys create,import,list,get,backup,restore
# Konfiguration der Contributor-Gruppe via Azure Portal für die Ressourcengruppe](https://image.slidesharecdn.com/securingmicrosoft365datawithserviceencryption-220324100804/85/Teams-Nation-2022-Securing-Microsoft-365-data-with-service-encryption-32-320.jpg)