Meter sets
•Als PPT, PDF herunterladen•
1 gefällt mir•1,489 views
Melden
Teilen
Melden
Teilen
Empfohlen
Installation of services

The document discusses the components and installation process for natural gas services from the main distribution line to a customer's building. A typical service includes a service tee connecting to the main, a plastic or steel service line, a riser valve, regulator, meter, and connection to the customer's piping. The installation process involves planning based on the customer's gas needs, excavating a trench, installing the service components, pressure testing, and backfilling. Safety devices like excess flow valves may also be included to automatically shut off gas flow if the service line is damaged.
Regulator – inspection & testing

This document provides instructions for inspecting and testing a service regulator. Key steps include checking the regulator for leaks and proper lock-up pressure. The regulator must be set to deliver the correct pressure, typically 7 inches of water column or 2 pounds per square inch. Tests are done to ensure the regulator maintains pressure without flow and that connections are gas tight to prevent leaks. Inspection records must be completed after testing is finished.
PIPED LPG GAS SUPPLY 

Piped LPG gas supply is provided through an underground main pipe with lateral pipes installed to homes as an alternative to LPG gas cylinders. It has advantages over cylinders like not needing refilling so no handling or damage, providing continuous supply, being easy to access, paying based on consumption, increasing safety, saving space, and providing energy 24 hours. Safety measures for piped LPG pipelines include proper design and installation of the system, proper training to handle it, and regular inspection and maintenance.
IT Optimization & Risk Management

How to optimize IT and regulatory burdens while saving money and improving the overall security posture.
CISSPills #3.03

CISSPills are short-lasting presentations covering topics to study in order to prepare CISSP exam. CISSPills is a digest of my notes and doesn't want to replace a studybook, it wants to be only just another companion for self-paced students.
Every issue covers different topics of CISSP's CCBK and the goal is addressing all the 10 domains which compose CISSP.
IN THIS ISSUE:
Domain 3: Information Security Governance and Risk Management
- Enterprise Architectures
- Enterprise Security Architectures
- Capability Maturity Model Integration (CMMI)
Meter data

United Works manufactures gas meters under OEM in SINTTA's production facility. The gas meters adhere to United Works' high quality standards and are certified to ISO 9001 and OIML R31/EN1359 international standards. The company produces both normal and prepaid gas meters for domestic and commercial use in various capacities.
System Gas srl - distribution of natural gas, LPG and fluids

System Gas is an Italian firm founded in 1995 that specializes in the distribution of natural gas, LPG, and fluids. They offer industrial planning and installation of natural gas systems according to customer requirements. System Gas provides regulating installations, metering equipment, and after-sales service and spare parts for natural gas and LPG plants. They also offer software for remote monitoring of flow computers and correctors.
Empfohlen
Installation of services

The document discusses the components and installation process for natural gas services from the main distribution line to a customer's building. A typical service includes a service tee connecting to the main, a plastic or steel service line, a riser valve, regulator, meter, and connection to the customer's piping. The installation process involves planning based on the customer's gas needs, excavating a trench, installing the service components, pressure testing, and backfilling. Safety devices like excess flow valves may also be included to automatically shut off gas flow if the service line is damaged.
Regulator – inspection & testing

This document provides instructions for inspecting and testing a service regulator. Key steps include checking the regulator for leaks and proper lock-up pressure. The regulator must be set to deliver the correct pressure, typically 7 inches of water column or 2 pounds per square inch. Tests are done to ensure the regulator maintains pressure without flow and that connections are gas tight to prevent leaks. Inspection records must be completed after testing is finished.
PIPED LPG GAS SUPPLY 

Piped LPG gas supply is provided through an underground main pipe with lateral pipes installed to homes as an alternative to LPG gas cylinders. It has advantages over cylinders like not needing refilling so no handling or damage, providing continuous supply, being easy to access, paying based on consumption, increasing safety, saving space, and providing energy 24 hours. Safety measures for piped LPG pipelines include proper design and installation of the system, proper training to handle it, and regular inspection and maintenance.
IT Optimization & Risk Management

How to optimize IT and regulatory burdens while saving money and improving the overall security posture.
CISSPills #3.03

CISSPills are short-lasting presentations covering topics to study in order to prepare CISSP exam. CISSPills is a digest of my notes and doesn't want to replace a studybook, it wants to be only just another companion for self-paced students.
Every issue covers different topics of CISSP's CCBK and the goal is addressing all the 10 domains which compose CISSP.
IN THIS ISSUE:
Domain 3: Information Security Governance and Risk Management
- Enterprise Architectures
- Enterprise Security Architectures
- Capability Maturity Model Integration (CMMI)
Meter data

United Works manufactures gas meters under OEM in SINTTA's production facility. The gas meters adhere to United Works' high quality standards and are certified to ISO 9001 and OIML R31/EN1359 international standards. The company produces both normal and prepaid gas meters for domestic and commercial use in various capacities.
System Gas srl - distribution of natural gas, LPG and fluids

System Gas is an Italian firm founded in 1995 that specializes in the distribution of natural gas, LPG, and fluids. They offer industrial planning and installation of natural gas systems according to customer requirements. System Gas provides regulating installations, metering equipment, and after-sales service and spare parts for natural gas and LPG plants. They also offer software for remote monitoring of flow computers and correctors.
Role of The Board In IT Governance & Cyber Security-Steve Howse

This document discusses I.T. strategy, risk management, and governance. It begins with an introduction of Steve Howse, the president of Millington & Associates, and his background. The document then discusses what I.T. strategy and governance entail and why they are important. It introduces the "20 questions" framework as a tool to assess I.T. strategy, risk, and governance. The questions are categorized into strategic issues, internal control issues, and risk issues. The document dives deeper into examples of risks and what organizations can do to address risks such as dedicating board members to I.T. committees and ensuring business continuity plans are tested.
India City Gas Distribution Market Forecast and Opportunities, 2030

Increasing government focus and favorable policy environment to boost city gas distribution market in India through 2030
Lpg reticulated gas system (cylinder bank) digital energy

The document discusses a reticulated LPG gas system, which is a centralized system that supplies liquefied petroleum gas (LPG) to homes and buildings through an underground pipeline network from a central storage bank of gas cylinders. Key benefits of the reticulated system include uninterrupted gas supply, increased safety since the gas enters homes at low pressure compared to individual cylinders, and reduced hassle since cylinders do not need to be replaced in each home. The system works by regulating the gas pressure through multiple stages to safely deliver gas to individual homes at low pressure. Safety features include automatic shut-off valves, leakage detection, and monitoring systems.
Prepayment Metering System

The document discusses Bangladesh's prepaid electricity metering system. It provides an overview of prepaid meter technologies, how the system works for purchasing electricity, objectives of the project including improved budgeting and convenience for customers. It also summarizes the results of implementing prepaid meters in several areas which led to reductions in losses and improvements in revenue collection and customer satisfaction.
City Gas Distribution

This document provides an overview of city gas distribution in India. It begins with acknowledgements and outlines the objectives of studying this topic. It then provides an executive summary that discusses key aspects of city gas distribution systems, including the network layout, pressure regimes, safety parameters, and examples from other countries like the US, Australia and China. The main focus is on the evolution, demand and supply scenario, challenges, players and regulatory framework for city gas distribution in India. Benefits and the future outlook for demand and supply in India are also summarized.
Anaesthesia gas cylinders & pipeline gas supply

The document discusses various aspects of medical gas cylinders and piped gas systems. It describes the parts of a cylinder including the body, valve, and pressure relief devices. It discusses safe handling practices like color coding, markings, and precautions during use. Hazards associated with cylinders are also summarized. The document then provides an overview of piped medical gas systems including the primary components, pressures, and terminal units where gases are delivered.
Cybersecurity - NSA Style

The National Security Agency offers up free cyber security tips on their website www.nsa.gov/ia. This slideshare is a consolidation of those tips for easy reading and understanding.
GSM BASED PREPAID ENERGY METER BILLING VIA SMS

The project is designed for reading electrical energy consumed in units and in rupees to display on an LCD screen to the user. This data is also provided to the electrical department using GSM technology for billing purposes. Owing to high electricity cost these days it becomes necessary for the consumer to know as to how much electricity is consumed to control electricity bill within his budget by recharging the energy meter units via S.M.S .
Finally when the energy meter coming to zero user can again recharge according to the purpose used. In this proposed system, the consumer will get his energy consumption data on real time basis on a LCD display. The same data is sent through GSM modem to the electricity department via SMS. A microcontroller of 8051 family is interfaced to the energy meter to get the Watt Hour pulses.
Further this project can be enhanced by to control the electrical appliances remotely via SMS. Also, the electricity department can send the monthly bill amount over SMS to the receiving unit for consumer information.
7 cyber security questions for boards

The cyber security job is everyone's business including the Board of Directors, even without a cyber security degree. Recent cyber security news proves that. According to several studies, Boards are getting it wrong and are leaving cyber awareness and risk management in the hands of the CEO, CISO, CTOs and cyber security companies. In a sense they are abdicating their responsibility to the shareholders. This slideshare proposes 7 questions every board should be asking their company executives abour IT security. They're not necessarily all encompassing and don't take the place of real cybersecurity training, but will drive the discussion to better and more complete understanding of strategic risk. Questions cover the basics of cyber security training, cyber policies, who briefs and when at board meetings. Thanks.
Cyber security presentation

Cyber security involves protecting computers, networks, programs and data from unauthorized access and cyber attacks. It includes communication security, network security and information security to safeguard organizational assets. Cyber crimes are illegal activities that use digital technologies and networks, and include hacking, data and system interference, fraud, and illegal device usage. Some early forms of cyber crime date back to the 1970s. Maintaining antivirus software, firewalls, backups and strong passwords can help protect against cyber threats while being mindful of privacy and security settings online. The document provides an overview of cyber security, cyber crimes, their history and basic safety recommendations.
Cybercrime.ppt

Cyber crime involves unlawful activities using computers and the internet. The document categorizes cyber crimes as those using computers to attack other computers or as tools to enable real-world crimes. It provides examples of various cyber crimes like hacking, child pornography, viruses, and cyber terrorism. It stresses the importance of cyber security to defend against attacks through prevention, detection and response. The document advises safety tips like using antivirus software, firewalls, and strong passwords. India's cyber laws address both traditional crimes committed online and new crimes defined in the Information Technology Act.
Cyber security

This document discusses cyber security and the need for it. It begins by defining cyber security as the security offered through online services to protect information. It then discusses how security threats are increasing as more people go online. The document covers the meaning of the term "cyber," major security problems like viruses and hackers, and ways to implement and maintain cyber security, such as using strong passwords and firewalls. It concludes by emphasizing that cyber security is everyone's responsibility.
Cyber crime ppt

Cyber crime is a growing problem in India. Some common cyber crimes reported in India include phishing, hacking of government websites, and identity theft. India ranks 11th globally for reported cyber crimes, which are increasing due to factors like rapid growth of internet users. Common cyber crimes involve unauthorized access to systems, data theft and alteration, and using computers to enable other illicit activities. While laws like the IT Act 2000 have been enacted to tackle cyber crimes, enforcement remains a challenge as only a small percentage of crimes are reported. Techniques like antivirus software, firewalls, and educating users can help address the problem.
Cyber crime and security ppt

This document provides an overview of cyber crime and security. It defines cyber crime as illegal activity committed on the internet, such as stealing data or importing malware. The document then covers the history and evolution of cyber threats. It categorizes cyber crimes as those using the computer as a target or weapon. Specific types of cyber crimes discussed include hacking, denial of service attacks, virus dissemination, computer vandalism, cyber terrorism, and software piracy. The document concludes by emphasizing the importance of cyber security.
Weitere ähnliche Inhalte
Andere mochten auch
Role of The Board In IT Governance & Cyber Security-Steve Howse

This document discusses I.T. strategy, risk management, and governance. It begins with an introduction of Steve Howse, the president of Millington & Associates, and his background. The document then discusses what I.T. strategy and governance entail and why they are important. It introduces the "20 questions" framework as a tool to assess I.T. strategy, risk, and governance. The questions are categorized into strategic issues, internal control issues, and risk issues. The document dives deeper into examples of risks and what organizations can do to address risks such as dedicating board members to I.T. committees and ensuring business continuity plans are tested.
India City Gas Distribution Market Forecast and Opportunities, 2030

Increasing government focus and favorable policy environment to boost city gas distribution market in India through 2030
Lpg reticulated gas system (cylinder bank) digital energy

The document discusses a reticulated LPG gas system, which is a centralized system that supplies liquefied petroleum gas (LPG) to homes and buildings through an underground pipeline network from a central storage bank of gas cylinders. Key benefits of the reticulated system include uninterrupted gas supply, increased safety since the gas enters homes at low pressure compared to individual cylinders, and reduced hassle since cylinders do not need to be replaced in each home. The system works by regulating the gas pressure through multiple stages to safely deliver gas to individual homes at low pressure. Safety features include automatic shut-off valves, leakage detection, and monitoring systems.
Prepayment Metering System

The document discusses Bangladesh's prepaid electricity metering system. It provides an overview of prepaid meter technologies, how the system works for purchasing electricity, objectives of the project including improved budgeting and convenience for customers. It also summarizes the results of implementing prepaid meters in several areas which led to reductions in losses and improvements in revenue collection and customer satisfaction.
City Gas Distribution

This document provides an overview of city gas distribution in India. It begins with acknowledgements and outlines the objectives of studying this topic. It then provides an executive summary that discusses key aspects of city gas distribution systems, including the network layout, pressure regimes, safety parameters, and examples from other countries like the US, Australia and China. The main focus is on the evolution, demand and supply scenario, challenges, players and regulatory framework for city gas distribution in India. Benefits and the future outlook for demand and supply in India are also summarized.
Anaesthesia gas cylinders & pipeline gas supply

The document discusses various aspects of medical gas cylinders and piped gas systems. It describes the parts of a cylinder including the body, valve, and pressure relief devices. It discusses safe handling practices like color coding, markings, and precautions during use. Hazards associated with cylinders are also summarized. The document then provides an overview of piped medical gas systems including the primary components, pressures, and terminal units where gases are delivered.
Cybersecurity - NSA Style

The National Security Agency offers up free cyber security tips on their website www.nsa.gov/ia. This slideshare is a consolidation of those tips for easy reading and understanding.
GSM BASED PREPAID ENERGY METER BILLING VIA SMS

The project is designed for reading electrical energy consumed in units and in rupees to display on an LCD screen to the user. This data is also provided to the electrical department using GSM technology for billing purposes. Owing to high electricity cost these days it becomes necessary for the consumer to know as to how much electricity is consumed to control electricity bill within his budget by recharging the energy meter units via S.M.S .
Finally when the energy meter coming to zero user can again recharge according to the purpose used. In this proposed system, the consumer will get his energy consumption data on real time basis on a LCD display. The same data is sent through GSM modem to the electricity department via SMS. A microcontroller of 8051 family is interfaced to the energy meter to get the Watt Hour pulses.
Further this project can be enhanced by to control the electrical appliances remotely via SMS. Also, the electricity department can send the monthly bill amount over SMS to the receiving unit for consumer information.
7 cyber security questions for boards

The cyber security job is everyone's business including the Board of Directors, even without a cyber security degree. Recent cyber security news proves that. According to several studies, Boards are getting it wrong and are leaving cyber awareness and risk management in the hands of the CEO, CISO, CTOs and cyber security companies. In a sense they are abdicating their responsibility to the shareholders. This slideshare proposes 7 questions every board should be asking their company executives abour IT security. They're not necessarily all encompassing and don't take the place of real cybersecurity training, but will drive the discussion to better and more complete understanding of strategic risk. Questions cover the basics of cyber security training, cyber policies, who briefs and when at board meetings. Thanks.
Cyber security presentation

Cyber security involves protecting computers, networks, programs and data from unauthorized access and cyber attacks. It includes communication security, network security and information security to safeguard organizational assets. Cyber crimes are illegal activities that use digital technologies and networks, and include hacking, data and system interference, fraud, and illegal device usage. Some early forms of cyber crime date back to the 1970s. Maintaining antivirus software, firewalls, backups and strong passwords can help protect against cyber threats while being mindful of privacy and security settings online. The document provides an overview of cyber security, cyber crimes, their history and basic safety recommendations.
Cybercrime.ppt

Cyber crime involves unlawful activities using computers and the internet. The document categorizes cyber crimes as those using computers to attack other computers or as tools to enable real-world crimes. It provides examples of various cyber crimes like hacking, child pornography, viruses, and cyber terrorism. It stresses the importance of cyber security to defend against attacks through prevention, detection and response. The document advises safety tips like using antivirus software, firewalls, and strong passwords. India's cyber laws address both traditional crimes committed online and new crimes defined in the Information Technology Act.
Cyber security

This document discusses cyber security and the need for it. It begins by defining cyber security as the security offered through online services to protect information. It then discusses how security threats are increasing as more people go online. The document covers the meaning of the term "cyber," major security problems like viruses and hackers, and ways to implement and maintain cyber security, such as using strong passwords and firewalls. It concludes by emphasizing that cyber security is everyone's responsibility.
Cyber crime ppt

Cyber crime is a growing problem in India. Some common cyber crimes reported in India include phishing, hacking of government websites, and identity theft. India ranks 11th globally for reported cyber crimes, which are increasing due to factors like rapid growth of internet users. Common cyber crimes involve unauthorized access to systems, data theft and alteration, and using computers to enable other illicit activities. While laws like the IT Act 2000 have been enacted to tackle cyber crimes, enforcement remains a challenge as only a small percentage of crimes are reported. Techniques like antivirus software, firewalls, and educating users can help address the problem.
Cyber crime and security ppt

This document provides an overview of cyber crime and security. It defines cyber crime as illegal activity committed on the internet, such as stealing data or importing malware. The document then covers the history and evolution of cyber threats. It categorizes cyber crimes as those using the computer as a target or weapon. Specific types of cyber crimes discussed include hacking, denial of service attacks, virus dissemination, computer vandalism, cyber terrorism, and software piracy. The document concludes by emphasizing the importance of cyber security.
Andere mochten auch (14)
Role of The Board In IT Governance & Cyber Security-Steve Howse

Role of The Board In IT Governance & Cyber Security-Steve Howse
India City Gas Distribution Market Forecast and Opportunities, 2030

India City Gas Distribution Market Forecast and Opportunities, 2030
Lpg reticulated gas system (cylinder bank) digital energy

Lpg reticulated gas system (cylinder bank) digital energy
Meter sets
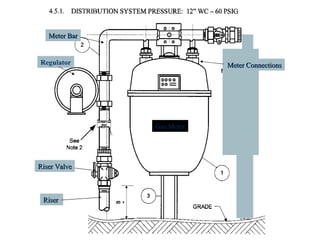
- 1. Regulator Gas Meter Riser Valve Meter Bar Meter Connections Riser
- 2. Meter Sets
- 3. Meter Sets
- 4. Meter Sets
- 5. Meter Sets
- 6. Meter Sets
- 7. Meter Sets
- 8. Meter Sets
- 9. Meter Sets
- 10. Meter Sets
- 11. Meter Sets
- 12. Meter Sets
- 13. Meter Sets
- 14. Meter Sets
- 15. Meter Sets
- 16. Meter Sets