Melden
Teilen
Weitere ähnliche Inhalte
Was ist angesagt?
Was ist angesagt? (19)
Topic 2.1 network communication using osi model part1

Topic 2.1 network communication using osi model part1
Tracing An IP Address or Domain Name by Raghu Khimani

Tracing An IP Address or Domain Name by Raghu Khimani
Andere mochten auch
Andere mochten auch (12)
Ähnlich wie Lesson 4 maya 4
Ähnlich wie Lesson 4 maya 4 (20)
A Deep Dive in the World of IT Networking (part 1)

A Deep Dive in the World of IT Networking (part 1)
Networkprotocolstructurescope 130719081246-phpapp01

Networkprotocolstructurescope 130719081246-phpapp01
Modue 1 part 1 of computer networks for your university exams

Modue 1 part 1 of computer networks for your university exams
09 Systems Software Programming-Network Programming.pptx

09 Systems Software Programming-Network Programming.pptx
Mehr von Max Friel
Mehr von Max Friel (20)
Kürzlich hochgeladen
Driving Behavioral Change for Information Management through Data-Driven Gree...

Driving Behavioral Change for Information Management through Data-Driven Gree...Enterprise Knowledge
Kürzlich hochgeladen (20)
The 7 Things I Know About Cyber Security After 25 Years | April 2024

The 7 Things I Know About Cyber Security After 25 Years | April 2024
Scaling API-first – The story of a global engineering organization

Scaling API-first – The story of a global engineering organization
What Are The Drone Anti-jamming Systems Technology?

What Are The Drone Anti-jamming Systems Technology?
08448380779 Call Girls In Greater Kailash - I Women Seeking Men

08448380779 Call Girls In Greater Kailash - I Women Seeking Men
08448380779 Call Girls In Civil Lines Women Seeking Men

08448380779 Call Girls In Civil Lines Women Seeking Men
TrustArc Webinar - Stay Ahead of US State Data Privacy Law Developments

TrustArc Webinar - Stay Ahead of US State Data Privacy Law Developments
Exploring the Future Potential of AI-Enabled Smartphone Processors

Exploring the Future Potential of AI-Enabled Smartphone Processors
[2024]Digital Global Overview Report 2024 Meltwater.pdf![[2024]Digital Global Overview Report 2024 Meltwater.pdf](data:image/gif;base64,R0lGODlhAQABAIAAAAAAAP///yH5BAEAAAAALAAAAAABAAEAAAIBRAA7)
![[2024]Digital Global Overview Report 2024 Meltwater.pdf](data:image/gif;base64,R0lGODlhAQABAIAAAAAAAP///yH5BAEAAAAALAAAAAABAAEAAAIBRAA7)
[2024]Digital Global Overview Report 2024 Meltwater.pdf
Handwritten Text Recognition for manuscripts and early printed texts

Handwritten Text Recognition for manuscripts and early printed texts
Powerful Google developer tools for immediate impact! (2023-24 C)

Powerful Google developer tools for immediate impact! (2023-24 C)
Advantages of Hiring UIUX Design Service Providers for Your Business

Advantages of Hiring UIUX Design Service Providers for Your Business
Driving Behavioral Change for Information Management through Data-Driven Gree...

Driving Behavioral Change for Information Management through Data-Driven Gree...
Factors to Consider When Choosing Accounts Payable Services Providers.pptx

Factors to Consider When Choosing Accounts Payable Services Providers.pptx
08448380779 Call Girls In Friends Colony Women Seeking Men

08448380779 Call Girls In Friends Colony Women Seeking Men
Tata AIG General Insurance Company - Insurer Innovation Award 2024

Tata AIG General Insurance Company - Insurer Innovation Award 2024
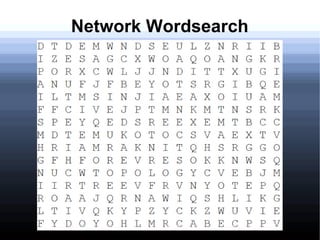
Lesson 4 maya 4
- 2. Characteristics of a network Topology Protocol Architecture
- 3. Network Protocols Ethernet • Most widely used for LAN networks, in particular S___ and b__ topologies. • The computer checks if the network cable is clear and has no d___ and then will send data.
- 4. Network Protocols Ethernet • Most widely used for LAN networks, in particular star and bus topologies. • The computer checks if the network cable is clear and has no data and then will send data.
- 5. Network Protocols IBM token-ring This protocol works in the form of a ring and is made up of a controlling computer and other computers.
- 6. Network Protocols IBM token-ring The _______ computer sends a token in the ring which travels from one computer to another. When a computer wants to send a message, it waits for an empty token.
- 7. Network Protocols IBM token-ring -The controlling computer sends a token in the ring which travels from one computer to another. -When a computer wants to send a message, it waits for an empty token.
- 8. Network Protocols IBM token-ring -The controlling computer sends a token in the ring which travels from one computer to another. -When a computer wants to send a message, it waits for an empty token.
- 9. Network Protocols IBM token-ring -When a computer finds an E_____ token, it fills it with the address of the destination station along with a message. -The token then goes around the ring until it reaches the C________ that the message came from.
- 10. Network Protocols IBM token-ring When a computer finds an empty token, it fills it with the address of the destination station along with a message. The token then goes around the ring until it reaches the Computer that the message came from.
- 11. Network Architecture Peer to Peer Architecture -tasks are distributed evenly amongst peers, no central infrastruture. -computers connect with each other in a workgroup to share files, printers and internet. Client/Server Architecture -tasks are distributed between the server and clients. The server provides the resource for clients on request. This is commonly used by companies.
