Final year IEEE projects for 2013-14
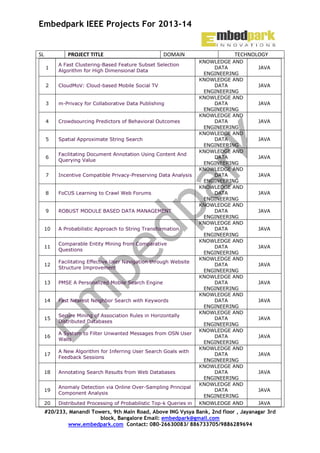
- 1. Embedpark IEEE Projects For 2013-14 PROJECT TITLE SL DOMAIN 1 A Fast Clustering-Based Feature Subset Selection Algorithm for High Dimensional Data 2 CloudMoV: Cloud-based Mobile Social TV 3 m-Privacy for Collaborative Data Publishing 4 Crowdsourcing Predictors of Behavioral Outcomes 5 Spatial Approximate String Search 6 Facilitating Document Annotation Using Content And Querying Value 7 Incentive Compatible Privacy-Preserving Data Analysis 8 FoCUS Learning to Crawl Web Forums 9 ROBUST MODULE BASED DATA MANAGEMENT 10 A Probabilistic Approach to String Transformation 11 Comparable Entity Mining from Comparative Questions 12 Facilitating Effective User Navigation through Website Structure Improvement 13 PMSE A Personalized Mobile Search Engine 14 Fast Nearest Neighbor Search with Keywords 15 Secure Mining of Association Rules in Horizontally Distributed Databases 16 A System to Filter Unwanted Messages from OSN User Walls 17 A New Algorithm for Inferring User Search Goals with Feedback Sessions 18 Annotating Search Results from Web Databases 19 Anomaly Detection via Online Over-Sampling Principal Component Analysis 20 Distributed Processing of Probabilistic Top-k Queries in TECHNOLOGY KNOWLEDGE AND DATA ENGINEERING KNOWLEDGE AND DATA ENGINEERING KNOWLEDGE AND DATA ENGINEERING KNOWLEDGE AND DATA ENGINEERING KNOWLEDGE AND DATA ENGINEERING KNOWLEDGE AND DATA ENGINEERING KNOWLEDGE AND DATA ENGINEERING KNOWLEDGE AND DATA ENGINEERING KNOWLEDGE AND DATA ENGINEERING KNOWLEDGE AND DATA ENGINEERING KNOWLEDGE AND DATA ENGINEERING KNOWLEDGE AND DATA ENGINEERING KNOWLEDGE AND DATA ENGINEERING KNOWLEDGE AND DATA ENGINEERING KNOWLEDGE AND DATA ENGINEERING KNOWLEDGE AND DATA ENGINEERING KNOWLEDGE AND DATA ENGINEERING KNOWLEDGE AND DATA ENGINEERING KNOWLEDGE AND DATA ENGINEERING KNOWLEDGE AND JAVA JAVA JAVA JAVA JAVA JAVA JAVA JAVA JAVA JAVA JAVA JAVA JAVA JAVA JAVA JAVA JAVA JAVA JAVA JAVA #20/233, Manandi Towers, 9th Main Road, Above ING Vysya Bank, 2nd floor , Jayanagar 3rd block, Bangalore Email: embedpark@gmail.com www.embedpark.com Contact: 080-26630083/ 886733705/9886289694
- 2. Embedpark IEEE Projects For 2013-14 Wireless Sensor Networks 21 Protecting Sensitive Labels in Social Network Data Anonymization 22 Tweet Analysis for Real-Time Event Detection and Earthquake Reporting System Development 23 Document Clustering for Forensic Analysis: An Approach for Improving Computer Inspection 24 A Method for Mining Infrequent Causal Associations and Its Application in Finding Adverse Drug Reaction Signal Pairs 25 Clustering Sentence-Level Text Using a Novel Fuzzy Relational Clustering Algorithm 26 A Generalized Flow-Based Method for Analysis of Implicit Relationships on Wikipedia 27 Anonymization of Centralized and Distributed Social Networks by Sequential Clustering 28 Preventing Private Information Inference Attacks on Social Networks 29 Multiparty Access Control for Online Social Networks Model and Mechanisms 30 Ranking on Data Manifold with Sink Points 31 A Methodology for Direct and Indirect Discrimination Prevention in Data Mining 32 A New Algorithm for Inferring User Search Goals with Feedback Sessions 33 A Survey of XML Tree Patterns 34 Dynamic Personalized Recommendation on Sparse Data 35 Mining User Queries with Markov Chains: Application to Online Image Retrieval 36 TrustedDB: A Trusted Hardware based Database with Privacy and Data Confidentiality 37 A Proxy-Based Approach to Continuous LocationBased Spatial Queries in Mobile Environments 38 Supporting Search-As-You-Type Using SQL in Databases 39 Ginix Generalized Inverted Index for Keyword Search DATA ENGINEERING KNOWLEDGE AND DATA ENGINEERING KNOWLEDGE AND DATA ENGINEERING KNOWLEDGE AND DATA ENGINEERING KNOWLEDGE AND DATA ENGINEERING KNOWLEDGE AND DATA ENGINEERING KNOWLEDGE AND DATA ENGINEERING KNOWLEDGE AND DATA ENGINEERING KNOWLEDGE AND DATA ENGINEERING KNOWLEDGE AND DATA ENGINEERING KNOWLEDGE AND DATA ENGINEERING KNOWLEDGE AND DATA ENGINEERING KNOWLEDGE AND DATA ENGINEERING KNOWLEDGE AND DATA ENGINEERING KNOWLEDGE AND DATA ENGINEERING KNOWLEDGE AND DATA ENGINEERING KNOWLEDGE AND DATA ENGINEERING KNOWLEDGE AND DATA ENGINEERING KNOWLEDGE AND DATA ENGINEERING KNOWLEDGE AND DATA ENGINEERING JAVA JAVA JAVA JAVA JAVA JAVA JAVA JAVA JAVA JAVA JAVA DOTNET DOTNET DOTNET DOTNET DOTNET DOTNET DOTNET DOTNET #20/233, Manandi Towers, 9th Main Road, Above ING Vysya Bank, 2nd floor , Jayanagar 3rd block, Bangalore Email: embedpark@gmail.com www.embedpark.com Contact: 080-26630083/ 886733705/9886289694
- 3. Embedpark IEEE Projects For 2013-14 40 Secure Mining of Association Rules in Horizontally Distributed Databases 41 Evaluation for Keyword Search on Probabilistic XML Data 42 Dynamic Query Forms for Database Queries 43 Sampling Online Social Networks 44 Mining Order-Preserving Submatrices from Data with Repeated Measurements 45 46 47 48 49 50 51 52 53 54 55 56 57 58 59 60 61 62 63 64 A Load Balancing Model Based on Cloud Partitioning for the Public Cloud Privacy-Preserving Public Auditing for Secure Cloud Storage Winds of Change From Vendor Lock-In to the Meta Cloud Cloud computing for mobile users can offloading compution save energy AMES-Cloud: A Framework of Adaptive Mobile Video Streaming and Efficient Social Video Sharing in the Clouds Mining Contracts for Business Events and Temporal Constraints in Service Engagements Collaboration in Multicloud Computing Environments: Framework and Security Issues A Stochastic Model to Investigate Data Center Performance and QoS in IaaS Cloud Computing Systems Error-Tolerant Resource Allocation and Payment Minimization for Cloud System Harnessing the Cloud for Securely Outsourcing LargeScale Systems of Linear Equations Mona: Secure Multi-Owner Data Sharing for Dynamic Groups in the Cloud PACK: Prediction-Based Cloud Bandwidth and Cost Reduction System Enabling Dynamic Data and Indirect Mutual Trust for Cloud Computing Storage Systems Load Rebalancing for Distributed File Systems in Clouds Scalable and Secure Sharing of Personal Health Records in Cloud Computing Using Attribute-Based Encryption Privacy Preserving Delegated Access Control in Public Clouds Enabling Dynamic Data and Indirect Mutual Trust for Cloud Computing Storage Systems Mona: Secure Multi-Owner Data Sharing for Dynamic Groups in the Cloud A Privacy Leakage Upper Bound Constraint-Based Approach for Cost-Effective Privacy Preserving of Intermediate Data Sets in Cloud An Adaptive Cloud Downloading Service KNOWLEDGE AND DATA ENGINEERING KNOWLEDGE AND DATA ENGINEERING KNOWLEDGE AND DATA ENGINEERING KNOWLEDGE AND DATA ENGINEERING KNOWLEDGE AND DATA ENGINEERING CLOUD COMPUTING CLOUD COMPUTING CLOUD COMPUTING CLOUD COMPUTING CLOUD COMPUTING CLOUD COMPUTING CLOUD COMPUTING CLOUD COMPUTING CLOUD COMPUTING CLOUD COMPUTING CLOUD COMPUTING CLOUD COMPUTING CLOUD COMPUTING CLOUD COMPUTING CLOUD COMPUTING DOTNET DOTNET DOTNET DOTNET DOTNET JAVA JAVA JAVA JAVA JAVA JAVA JAVA JAVA JAVA JAVA JAVA JAVA JAVA JAVA JAVA CLOUD COMPUTING CLOUD COMPUTING CLOUD COMPUTING DOTNET CLOUD COMPUTING DOTNET CLOUD COMPUTING DOTNET JAVA DOTNET #20/233, Manandi Towers, 9th Main Road, Above ING Vysya Bank, 2nd floor , Jayanagar 3rd block, Bangalore Email: embedpark@gmail.com www.embedpark.com Contact: 080-26630083/ 886733705/9886289694
- 4. Embedpark IEEE Projects For 2013-14 65 Optimal Multiserver Configuration for Profit Maximization in Cloud Computing 66 QoS Ranking Prediction for Cloud Services 67 68 69 70 71 72 73 74 75 76 77 Toward Fine-Grained, Unsupervised, Scalable Performance Diagnosis for Production Cloud Computing Systems Towards Secure Multi-Keyword Top-k Retrieval over Encrypted Cloud Data Dynamic Audit Services for Outsourced Storages in Clouds Attribute-based Access to Scalable Media in Cloudassisted Content Sharing Networks Privacy-Preserving Public Auditing for Secure Cloud Storage Scalable and Secure Sharing of Personal Health Records in Cloud Computing Using Attribute-Based Encryption Privacy Preserving Delegated Access Control in Public Clouds Super-Resolution-based Inpainting Beyond Text QA: Multimedia Answer Generation by Harvesting Web Information Scalable Face Image Retrieval using AttributeEnhanced Sparse Codewords Understanding the External Links of Video Sharing Sites: Measurement and Analysis 78 Query-Adaptive Image Search With Hash Codes 79 Reversible Data Hiding With Optimal Value Transfer 80 81 82 83 84 85 86 87 88 89 90 91 92 93 Reversible Watermarking Based on Invariant Image Classification and Dynamic Histogram Shifting Noise Reduction Based on Partial-Reference, DualTree Complex Wavelet Transform Shrinkage Local Directional Number Pattern for Face Analysis: Face and Expression Recognition Perceptual Video Coding Based on SSIM-Inspired Divisive Normalization Local Linear SURE-Based Edge-Preserving Image Filtering Beyond Text QA: Multimedia Answer Generation by Harvesting Web Information CAM: Cloud-Assisted Privacy Preserving Mobile Health Monitoring Secure Encounter-based Mobile Social Networks Requirements Designs and Tradeoffs Two tales of privacy in online social networks Extracting Spread-Spectrum Hidden Data from Digital Media Utility-Privacy Tradeoff in Databases An Informationtheoretic Approach EAACK—A Secure Intrusion-Detection System for MANETs Identity-Based Secure Distributed Data Storage Schemes Modeling the Pairwise Key Predistribution Scheme in CLOUD COMPUTING CLOUD COMPUTING CLOUD COMPUTING CLOUD COMPUTING CLOUD COMPUTING CLOUD COMPUTING CLOUD COMPUTING CLOUD COMPUTING CLOUD COMPUTING IMAGE PROCESSING IMAGE PROCESSING IMAGE PROCESSING IMAGE PROCESSING IMAGE PROCESSING IMAGE PROCESSING IMAGE PROCESSING IMAGE PROCESSING IMAGE PROCESSING IMAGE PROCESSING IMAGE PROCESSING MULTIMEDIA SECURE COMPUTING SECURE COMPUTING SECURE COMPUTING SECURE COMPUTING SECURE COMPUTING SECURE COMPUTING SECURE COMPUTING SECURE DOTNET DOTNET DOTNET DOTNET DOTNET DOTNET DOTNET DOTNET DOTNET JAVA JAVA JAVA JAVA DOTNET DOTNET DOTNET DOTNET DOTNET DOTNET DOTNET DOTNET JAVA JAVA JAVA JAVA JAVA JAVA JAVA JAVA #20/233, Manandi Towers, 9th Main Road, Above ING Vysya Bank, 2nd floor , Jayanagar 3rd block, Bangalore Email: embedpark@gmail.com www.embedpark.com Contact: 080-26630083/ 886733705/9886289694
- 5. Embedpark IEEE Projects For 2013-14 the Presence of Unreliable Links 94 NICE: Network Intrusion Detection and Countermeasure Selection in Virtual Network Systems 95 Securing Class Initialization in Java-like Languages 96 97 98 99 100 101 102 103 104 105 106 107 108 109 110 Security Analysis of a Single Sign-On Mechanism for Distributed Computer Networks SORT: A Self-ORganizing Trust Model for Peer-to-Peer Systems WARNINGBIRD: A Near Real-time Detection System for Suspicious URLs in Twitter Stream Secure Encounter-based Mobile Social Networks: Requirements, Designs, and Tradeoffs Twitsper: Tweeting Privately Cross-Domain Privacy-Preserving Cooperative Firewall Optimization Privacy Preserving Data Sharing With Anonymous ID Assignment SORT: A Self-ORganizing Trust Model for Peer-to-Peer Systems Privacy Preserving Data Sharing With Anonymous ID Assignment Modeling the Pairwise Key Predistribution Scheme in the Presence of Unreliable Links Non-Cooperative Location Privacy Enforcing Secure and Privacy-Preserving Information Brokering in Distributed Information Sharing Reversible Data Hiding in Encrypted Images by Reserving Room Before Encryption EAACK—A Secure Intrusion-Detection System for MANETs CAM: Cloud-Assisted Privacy Preserving Mobile Health Monitoring 111 Enabling Data Dynamic and Indirect Mutual Trust for Cloud Computing Storage Systems 112 A Privacy Leakage Upper-bound Constraint based Approach for Cost-effective Privacy Preserving of Intermediate Datasets in Cloud 113 Dynamic Resource Allocation using Virtual Machines for Cloud Computing Environment 114 Towards Differential Query Services in Cost-Efficient Clouds 115 Geo-Community-Based Broadcasting for Data Dissemination in Mobile Social Networks 116 A Secure Protocol for Spontaneous Wireless Ad Hoc Networks Creation 117 IP-Geolocation Mapping for Moderately Connected Internet Regions 118 SocialTube P2P-assisted Video Sharing in Online Social Networks COMPUTING SECURE COMPUTING SECURE COMPUTING SECURE COMPUTING SECURE COMPUTING SECURE COMPUTING SECURE COMPUTING SECURE COMPUTING SECURE COMPUTING SECURE COMPUTING SECURE COMPUTING SECURE COMPUTING SECURE COMPUTING SECURE COMPUTING SECURE COMPUTING SECURE COMPUTING SECURE COMPUTING SECURE COMPUTING PARALLEL AND DISTRIBUTED SYSTEMS PARALLEL AND DISTRIBUTED SYSTEMS PARALLEL AND DISTRIBUTED SYSTEMS PARALLEL AND DISTRIBUTED SYSTEMS PARALLEL AND DISTRIBUTED SYSTEMS PARALLEL AND DISTRIBUTED SYSTEMS PARALLEL AND DISTRIBUTED SYSTEMS PARALLEL AND DISTRIBUTED SYSTEMS JAVA JAVA JAVA JAVA JAVA JAVA JAVA JAVA JAVA DOTNET DOTNET DOTNET DOTNET DOTNET DOTNET DOTNET DOTNET JAVA JAVA JAVA JAVA JAVA JAVA JAVA JAVA #20/233, Manandi Towers, 9th Main Road, Above ING Vysya Bank, 2nd floor , Jayanagar 3rd block, Bangalore Email: embedpark@gmail.com www.embedpark.com Contact: 080-26630083/ 886733705/9886289694
- 6. Embedpark IEEE Projects For 2013-14 119 A System for Denial-of-Service Attack Detection Based on Multivariate Correlation Analysis 120 Security Analysis of a Privacy-Preserving Decentralized Key-Policy Attribute-Based Encryption Scheme 121 SybilDefender Defend Against Sybil Attacks in Large Social Networks 122 A Secure Payment Scheme with Low Communication and Processing Overhead for Multihop Wireless Networks 123 Multicast Capacity in MANET with Infrastructure Support 124 Detection and Localization of Multiple Spoofing Attackers in Wireless Networks 125 A Probabilistic Misbehavior Detection Scheme towards Efficient Trust Establishment in Delay-tolerant Networks 126 Attribute-Aware Data Aggregation Using PotentialBased Dynamic Routing n Wireless Sensor Networks 127 Privacy Preserving Back-Propagation Neural Network Learning Over Arbitrarily Partitioned Data 128 SPOC: A Secure and Privacy-preserving Opportunistic Computing Framework for Mobile-Healthcare Emergency 129 Secure and Efficient Data Transmission for Clusterbased Wireless Sensor Networks 130 Mobi-Sync: Efficient Time Synchronization for Mobile Underwater Sensor Networks 131 A Highly Scalable Key Pre-Distribution Scheme for Wireless Sensor Networks 132 Privacy-Preserving Distributed Profile Matching in Proximity-based Mobile Social Networks 133 A Highly Scalable Key Pre-Distribution Scheme for Wireless Sensor Networks 134 135 136 137 138 139 140 Mobile Relay Configuration in Data-intensive Wireless Sensor Networks Vampire attacks:Draining life from wireless ad-hoc sensor networks Towards a Statistical Framework for Source Anonymity in Sensor Networks A Scalable Server Architecture for Mobile Presence Services in Social Network Applications Distributed Cooperative Caching in Social Wireless Networks Community-Aware Opportunistic Routing in Mobile Social Networks Content Sharing over Smartphone-Based DelayTolerant Networks PARALLEL AND DISTRIBUTED SYSTEMS PARALLEL AND DISTRIBUTED SYSTEMS PARALLEL AND DISTRIBUTED SYSTEMS PARALLEL AND DISTRIBUTED SYSTEMS PARALLEL AND DISTRIBUTED SYSTEMS PARALLEL AND DISTRIBUTED SYSTEMS PARALLEL AND DISTRIBUTED SYSTEMS PARALLEL AND DISTRIBUTED SYSTEMS PARALLEL AND DISTRIBUTED SYSTEMS PARALLEL AND DISTRIBUTED SYSTEMS PARALLEL AND DISTRIBUTED SYSTEMS PARALLEL AND DISTRIBUTED SYSTEMS PARALLEL AND DISTRIBUTED SYSTEMS WIRELESS COMMUNICATION S WIRELESS COMMUNICATION S MOBILE COMPUTING MOBILE COMPUTING MOBILE COMPUTING MOBILE COMPUTING MOBILE COMPUTING MOBILE COMPUTING MOBILE COMPUTING JAVA JAVA JAVA DOTNET DOTNET DOTNET DOTNET DOTNET DOTNET DOTNET DOTNET DOTNET DOTNET JAVA JAVA JAVA JAVA JAVA JAVA JAVA JAVA JAVA #20/233, Manandi Towers, 9th Main Road, Above ING Vysya Bank, 2nd floor , Jayanagar 3rd block, Bangalore Email: embedpark@gmail.com www.embedpark.com Contact: 080-26630083/ 886733705/9886289694
- 7. Embedpark IEEE Projects For 2013-14 141 142 143 144 145 146 147 148 149 150 151 152 153 154 155 156 157 158 159 160 161 162 163 164 165 166 167 168 169 DCIM: Distributed Cache Invalidation Method for Maintaining Cache Consistency in Wireless Mobile Networks Discovery and Verification of Neighbor Positions in Mobile Ad Hoc Networks Efficient Rekeying Framework for Secure Multicast with Diverse-Subscription-Period Mobile Users Toward Privacy Preserving and Collusion Resistance in a Location Proof Updating System Optimal Content Downloading in Vehicular Networks Network-Assisted Mobile Computing with Optimal Uplink Query Processing Adaptive Position Update for Geographic Routing in Mobile Ad Hoc Networks Cooperative Packet Delivery in Hybrid Wireless Mobile Networks: A Coalitional Game Approach Relay Selection for Geographical Forwarding in SleepWake Cycling Wireless Sensor Networks A Neighbor Coverage-Based Probabilistic Rebroadcast for Reducing Routing Overhead in Mobile Ad Hoc Networks Target Tracking and Mobile Sensor Navigation in Wireless Sensor Networks Toward Accurate Mobile Sensor Network Localization in Noisy Environments Optimal Multicast Capacity and Delay Tradeoffs in MANETs On Quality of Monitoring for Multi-channel Wireless Infrastructure Networks EMAP : Expedite Message Authentication Protocol for Vehicular Ad Hoc Networks Price Differentiation for Communication Networks Participatory Privacy Enabling Privacy in Participatory Sensing Optimizing Cloud Resources for Delivering IPTV Services through Virtualization Access Policy Consolidation for Event Processing Systems SinkTrail: A Proactive Data Reporting Protocol for Wireless Sensor Networks Delay-Based Network Utility Maximization Dynamic Control of Coding for Progressive Packet Arrivals in DTNs Minimum Cost Blocking Problem in Multi-path Wireless Routing Protocols On the Node Clone Detection in Wireless Sensor Networks Opportunistic MANETs: Mobility Can Make Up for Low Transmission Power Back-Pressure-Based Packet-by-Packet Adaptive Routing in Communication Networks Fast Transmission to Remote Cooperative Groups: A New Key Management Paradigm Using Fuzzy Logic Control to Provide Intelligent Traffic Management Service for High-Speed Networks Optimum Relay Selection for Energy-Efficient Cooperative Ad Hoc Network MOBILE COMPUTING MOBILE COMPUTING MOBILE COMPUTING MOBILE COMPUTING MOBILE COMPUTING MOBILE COMPUTING MOBILE COMPUTING MOBILE COMPUTING MOBILE COMPUTING MOBILE COMPUTING MOBILE COMPUTING MOBILE COMPUTING MOBILE COMPUTING MOBILE COMPUTING MOBILE COMPUTING NETWORKING JAVA JAVA JAVA JAVA DOTNET DOTNET DOTNET DOTNET DOTNET DOTNET DOTNET DOTNET DOTNET DOTNET DOTNET JAVA NETWORKING JAVA NETWORKING JAVA NETWORKING JAVA NETWORKING JAVA NETWORKING JAVA NETWORKING JAVA NETWORKING JAVA NETWORKING JAVA NETWORKING JAVA NETWORKING JAVA NETWORKING JAVA NETWORKING JAVA NETWORKING JAVA #20/233, Manandi Towers, 9th Main Road, Above ING Vysya Bank, 2nd floor , Jayanagar 3rd block, Bangalore Email: embedpark@gmail.com www.embedpark.com Contact: 080-26630083/ 886733705/9886289694
- 8. Embedpark IEEE Projects For 2013-14 170 171 172 173 174 175 176 177 178 179 180 181 182 A Distributed Control Law for Load Balancing in Content Delivery Networks An Efficient and Robust Addressing Protocol for Node Auto configuration in Ad Hoc Networks BAHG: Back-Bone-Assisted Hop Greedy Routing for VANET’s City Environments Efficient Algorithms for Neighbor Discovery in Wireless Networks Localization of Wireless Sensor Networks in the Wild: Pursuit of Ranging Quality Resource Allocation for QoS Support in Wireless Mesh Networks A Low-Complexity Congestion Control and Scheduling Algorithm for Multihop Wireless Networks With OrderOptimal Per-Flow Delay Transfer Reliability and Congestion Control Strategies in Opportunistic Networks A Survey The Target Tracking in Mobile Sensor Networks Redundancy Management of Multipath Routing for Intrusion Tolerance in Heterogeneous Wireless Sensor Networks Exploiting Cooperative Relay for High Performance Communications in MIMO Ad Hoc Networks A Decentralized Service Discovery Approach on Peerto-Peer Networks Personalized QoS-Aware Web Service Recommendation and Visualization 183 Privacy-Enhanced Web Service Composition 184 Cost-Based Optimization of Service Compositions 185 Evolution of Social Networks Based on Tagging Practices 186 Whole Test Suite Generation 187 A Framework for Mining Signatures from Event Sequences and Its Applications in Healthcare Data 188 A Data-Mining Model for Protection of FACTS-Based Transmission Line 189 TrPF A Trajectory Privacy-Preserving Framework for Participatory Sensing 190 Attribute-Based Encryption With Verifiable Outsourced Decryption 191 A Decentralized Privacy Preserving Reputation Protocol for the Malicious Adversarial Model. 192 Fully Anonymous Profile Matching in Mobile Social Networks 193 Optimal Client-Server Assignment for Internet Distributed Systems NETWORKING DOTNET NETWORKING DOTNET NETWORKING DOTNET NETWORKING DOTNET NETWORKING DOTNET NETWORKING DOTNET NETWORKING DOTNET NETWORKING DOTNET NETWORKING DOTNET NETWORKING DOTNET NETWORKING DOTNET SERVICE COMPUTING SERVICE COMPUTING SERVICE COMPUTING SERVICE COMPUTING SERVICE COMPUTING SOFTWARE ENGINEERING PATTERN ANALYSIS AND MACHINE INTELLIGENCE POWER DELIVERY INFORMATION FORENSICS AND SECURITY INFORMATION FORENSICS AND SECURITY INFORMATION FORENSICS AND SECURITY SELECTED AREAS IN COMMUNICATION CONFERENCE JAVA JAVA JAVA DOTNET DOTNET JAVA JAVA JAVA JAVA JAVA DOTNET JAVA JAVA #20/233, Manandi Towers, 9th Main Road, Above ING Vysya Bank, 2nd floor , Jayanagar 3rd block, Bangalore Email: embedpark@gmail.com www.embedpark.com Contact: 080-26630083/ 886733705/9886289694
- 9. Embedpark IEEE Projects For 2013-14 194 195 196 197 198 199 200 201 202 203 Intrusion Detection Technique by using K-means, Fuzzy Neural Network and SVM classifiers. Combining Cryptographic Primitives to Prevent Jamming Attacks in Wireless Networks Outsourcing Privacy-Preserving Social Networks to a Cloud Search Me If You Can Privacy-preserving Location Query Service Privacy against Aggregate Knowledge Attacks SUSIE Search using services and information extraction Gmatch Secure and Privacy-Preserving Group Matching in Social Networks A Log-based Approach to Make Digital Forensics Easier on Cloud Computing CloudFTP: A Case Study of Migrating Traditional Applications to the Cloud Performance Analysis of OSPF and EIGRP Routing Protocols for Greener Internetworking 204 On the Role of Mobility for Multi-message Gossip 205 A Fast Re-Route Method 206 207 A Rank Correlation Based Detection against Distributed Reflection DoS Attacks SeDas A Self-Destructing Data System Based on Active Storage Framework 208 Topological Conditions for In-Network Stabilization of Dynamical Systems 209 Secure Logging As a Service—Delegating Log Management to the Cloud 210 T-Drive: Enhancing Driving Directions with Taxi Driver Intelligence 211 Dynamic Personalized Recommendation on Sparse Data 212 Spatial Query Integrity with Voronoi Neighbors 213 MeetYou -- Social Networking on Android 214 A Proxy-Based Approach to Continuous LocationBased Spatial Queries in Mobile Environments 215 PMSE: A Personalized Mobile Search Engine 216 Crowdsourced Trace Similarity with Smartphones 217 Twitsper: Tweeting Privately CONFERENCE JAVA CONFERENCE JAVA CONFERENCE JAVA CONFERENCE JAVA CONFERENCE JAVA CONFERENCE DOTNET CONFERENCE DOTNET CONFERENCE DOTNET CONFERENCE DOTNET CONFERENCE DOTNET INFORMATION THEORY COMMUNICATION S LETTER JAVA JAVA COMMUNICATION S LETTER DOTNET MAGNETICS DOTNET SELECTED AREAS IN COMMUNICATION S SYSTEMS JOURNAL KNOWLEDGE AND DATA ENGINEERING KNOWLEDGE AND DATA ENGINEERING KNOWLEDGE AND DATA ENGINEERING KNOWLEDGE AND DATA ENGINEERING (CONF) KNOWLEDGE AND DATA ENGINEERING KNOWLEDGE AND DATA ENGINEERING KNOWLEDGE AND DATA ENGINEERING SECURE COMPUTING JAVA JAVA ANDROID ANDROID ANDROID ANDROID ANDROID ANDROID ANDROID ANDROID #20/233, Manandi Towers, 9th Main Road, Above ING Vysya Bank, 2nd floor , Jayanagar 3rd block, Bangalore Email: embedpark@gmail.com www.embedpark.com Contact: 080-26630083/ 886733705/9886289694
- 10. Embedpark IEEE Projects For 2013-14 218 219 220 221 222 223 224 225 Review of Behavior Malware Analysis for Android Research in Progress - Defending Android Smartphones from Malware Attacks Secure Encounter-based Mobile Social Networks: Requirements, Designs, and Tradeoffs CloudFTP: A Case Study of Migrating Traditional Applications to the Cloud Collaborative Policy Administration SPOC: A Secure and Privacy-Preserving Opportunistic Computing Framework for Mobile-Healthcare Emergency Scalable and Secure Sharing of Personal Health Records in Cloud Computing Using Attribute-Based Encryption Collaborative Learning Assistant for Android SECURE COMPUTING SECURE COMPUTING SECURE COMPUTING CLOUD COMPUTING PARALLEL AND DISTRIBUTED SYSTEMS PARALLEL AND DISTRIBUTED SYSTEMS PARALLEL AND DISTRIBUTED SYSTEMS E LEARNING (CONF) ANDROID ANDROID ANDROID ANDROID ANDROID ANDROID ANDROID ANDROID #20/233, Manandi Towers, 9th Main Road, Above ING Vysya Bank, 2nd floor , Jayanagar 3rd block, Bangalore Email: embedpark@gmail.com www.embedpark.com Contact: 080-26630083/ 886733705/9886289694