Computer security risks
•Als PPTX, PDF herunterladen•
1 gefällt mir•326 views
Computer security risks
Melden
Teilen
Melden
Teilen
Empfohlen
Empfohlen
Weitere ähnliche Inhalte
Was ist angesagt?
Was ist angesagt? (20)
Andere mochten auch
Andere mochten auch (20)
Presentation Virus (salami attack and trojan horse)

Presentation Virus (salami attack and trojan horse)
MALICIOUS SOFTWARE VIRUS WORM TROJAN HORSE ANTI VIRUS 

MALICIOUS SOFTWARE VIRUS WORM TROJAN HORSE ANTI VIRUS
Mehr von Gilbert Pagapang
Mehr von Gilbert Pagapang (8)
Kürzlich hochgeladen
Dwarka Sector 26 Call Girls | Delhi | 9999965857 🫦 Vanshika Verma More Our Se...

Dwarka Sector 26 Call Girls | Delhi | 9999965857 🫦 Vanshika Verma More Our Se...Call Girls In Delhi Whatsup 9873940964 Enjoy Unlimited Pleasure
Call Girls In South Ex 📱 9999965857 🤩 Delhi 🫦 HOT AND SEXY VVIP 🍎 SERVICE

Call Girls In South Ex 📱 9999965857 🤩 Delhi 🫦 HOT AND SEXY VVIP 🍎 SERVICECall Girls In Delhi Whatsup 9873940964 Enjoy Unlimited Pleasure
Call Girls In Noida 📱 9999965857 🤩 Delhi 🫦 HOT AND SEXY VVIP 🍎 SERVICE

Call Girls In Noida 📱 9999965857 🤩 Delhi 🫦 HOT AND SEXY VVIP 🍎 SERVICECall Girls In Delhi Whatsup 9873940964 Enjoy Unlimited Pleasure
Rohini Sector 6 Call Girls Delhi 9999965857 @Sabina Saikh No Advance

Rohini Sector 6 Call Girls Delhi 9999965857 @Sabina Saikh No AdvanceCall Girls In Delhi Whatsup 9873940964 Enjoy Unlimited Pleasure
Top Rated Pune Call Girls Daund ⟟ 6297143586 ⟟ Call Me For Genuine Sex Servi...

Top Rated Pune Call Girls Daund ⟟ 6297143586 ⟟ Call Me For Genuine Sex Servi...Call Girls in Nagpur High Profile
Kürzlich hochgeladen (20)
Best VIP Call Girls Noida Sector 75 Call Me: 8448380779

Best VIP Call Girls Noida Sector 75 Call Me: 8448380779
Dwarka Sector 26 Call Girls | Delhi | 9999965857 🫦 Vanshika Verma More Our Se...

Dwarka Sector 26 Call Girls | Delhi | 9999965857 🫦 Vanshika Verma More Our Se...
Call Girls in Mayur Vihar ✔️ 9711199171 ✔️ Delhi ✔️ Enjoy Call Girls With Our...

Call Girls in Mayur Vihar ✔️ 9711199171 ✔️ Delhi ✔️ Enjoy Call Girls With Our...
Call Now ☎ 8264348440 !! Call Girls in Green Park Escort Service Delhi N.C.R.

Call Now ☎ 8264348440 !! Call Girls in Green Park Escort Service Delhi N.C.R.
Delhi Call Girls Rohini 9711199171 ☎✔👌✔ Whatsapp Hard And Sexy Vip Call

Delhi Call Girls Rohini 9711199171 ☎✔👌✔ Whatsapp Hard And Sexy Vip Call
FULL ENJOY Call Girls In Mayur Vihar Delhi Contact Us 8377087607

FULL ENJOY Call Girls In Mayur Vihar Delhi Contact Us 8377087607
On Starlink, presented by Geoff Huston at NZNOG 2024

On Starlink, presented by Geoff Huston at NZNOG 2024
Call Girls In South Ex 📱 9999965857 🤩 Delhi 🫦 HOT AND SEXY VVIP 🍎 SERVICE

Call Girls In South Ex 📱 9999965857 🤩 Delhi 🫦 HOT AND SEXY VVIP 🍎 SERVICE
Enjoy Night⚡Call Girls Dlf City Phase 3 Gurgaon >༒8448380779 Escort Service

Enjoy Night⚡Call Girls Dlf City Phase 3 Gurgaon >༒8448380779 Escort Service
Networking in the Penumbra presented by Geoff Huston at NZNOG

Networking in the Penumbra presented by Geoff Huston at NZNOG
Call Girls In Defence Colony Delhi 💯Call Us 🔝8264348440🔝

Call Girls In Defence Colony Delhi 💯Call Us 🔝8264348440🔝
AWS Community DAY Albertini-Ellan Cloud Security (1).pptx

AWS Community DAY Albertini-Ellan Cloud Security (1).pptx
GDG Cloud Southlake 32: Kyle Hettinger: Demystifying the Dark Web

GDG Cloud Southlake 32: Kyle Hettinger: Demystifying the Dark Web
𓀤Call On 7877925207 𓀤 Ahmedguda Call Girls Hot Model With Sexy Bhabi Ready Fo...

𓀤Call On 7877925207 𓀤 Ahmedguda Call Girls Hot Model With Sexy Bhabi Ready Fo...
'Future Evolution of the Internet' delivered by Geoff Huston at Everything Op...

'Future Evolution of the Internet' delivered by Geoff Huston at Everything Op...
SEO Growth Program-Digital optimization Specialist

SEO Growth Program-Digital optimization Specialist
Call Girls In Noida 📱 9999965857 🤩 Delhi 🫦 HOT AND SEXY VVIP 🍎 SERVICE

Call Girls In Noida 📱 9999965857 🤩 Delhi 🫦 HOT AND SEXY VVIP 🍎 SERVICE
Rohini Sector 6 Call Girls Delhi 9999965857 @Sabina Saikh No Advance

Rohini Sector 6 Call Girls Delhi 9999965857 @Sabina Saikh No Advance
Call Now ☎ 8264348440 !! Call Girls in Shahpur Jat Escort Service Delhi N.C.R.

Call Now ☎ 8264348440 !! Call Girls in Shahpur Jat Escort Service Delhi N.C.R.
Top Rated Pune Call Girls Daund ⟟ 6297143586 ⟟ Call Me For Genuine Sex Servi...

Top Rated Pune Call Girls Daund ⟟ 6297143586 ⟟ Call Me For Genuine Sex Servi...
Computer security risks
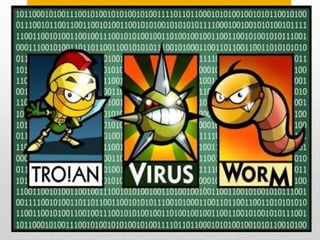
- 1. Computer Security Risks Viruses, Worms, and Trojan Horses
- 2. Potentially damaging. Negatively affect a computer and change the way it works. It spread and damage the computer’s files and software.
- 3. Copies itself repeatedly and spreads throughout a single computer or an entire network. Use up hard disk space or memory resources. Shutdown a computer or network.
- 4. A program that hides within or looks like a legitimate program. Triggered by certain condition or action. Does not replicate itself.
- 6. Protects your computer by identifying and removing viruses found in your computer’s memory, storage media, and incoming files. Needs to be updated regularly.