Azure Sentinel Tips
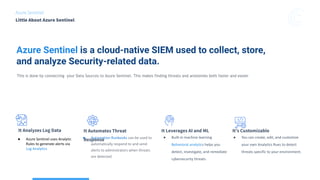
- 1. Little About Azure Sentinel Azure Sentinel It Analyzes Log Data It Automates Threat Response It Leverages AI and ML ● Built-in machine learning Behavioral analytics helps you detect, investigate, and remediate cybersecurity threats It’s Customizable Azure Sentinel is a cloud-native SIEM used to collect, store, and analyze Security-related data. This is done by connecting your Data Sources to Azure Sentinel. This makes finding threats and anolomies both faster and easier ● Azure Sentinel uses Analytic Rules to generate alerts via Log Analytics ● Automation Runbooks can be used to automatically respond to and send alerts to adminstrators when threats are detected. ● You can create, edit, and customize your own Analytics Rues to detect threats specific to your environment.
- 2. Azure Sentinel Data Sources Connect your data to Azure Sentinel. SC-200 Azure Sentinel AWS/GCP via Cloud-Trail Azure Active Directory audit logs and sign-in logs. Web App Firewall Firewall and connection logs.. SQL Database Logs database and audit logs . Kubernetes Service Office 365 audit logs and sign-in logs. You can see the full list of data sources HERE.
- 3. Azure Sentinel Workbooks SC-200 Azure Sentinel provides several ready-to-use templates that you can use to create your own Workbooks and then modify them as needed. Visit the Azure Sentinel Github Repository for out-of-the-box detections, exploration queries, hunting queries, workbooks, playbooks and more to improve the security of your environment. ● Most of the Data connectors in Azure Sentinel come with their own pre-built workbooks. ● You can get better insight into the data being ingested, by using Tables and Visualizations. They offer better insights into your data using bar and pie charts. ● You can also create your own workbooks from scratch, instead of using the predefined templates. From the Workbooks page in Sentinel, you can: ● Add a New workbook ● Review your saved workbooks ● Download workbook templates
- 4. SC-200 Defender For Endpoint Defender For Identity Defender For Office 365 Azure Sentinel Microsoft Cloud App Security. Azure Sentinel / M365 Defender Microsoft 365 Defender connects easily to Azure Sentinel and provides a purpose-driven user interface to mitigate threats detected by Microsoft 365 Defender. The Microsoft 365 Defender family of products include: ● Microsoft Defender for Endpoint ● Microsoft Defender for Identity ● Microsoft Defender for Office 365 ● Microsoft Cloud App Security Once connecting each of these services to Sentinel, any alerts will be sent to the SecurityAlerts table in Sentinel. From there, you can generate an Incident. Another connector - Microsoft 365 Defender - allows for the raw normalized data to be ingested by Azure Sentinel. Currently, only Microsoft Defender for Endpoint data is configurable in the Microsoft 365 Defender connector. You must decide if you want Microsoft 365 Defender products alerts in Azure Sentinel. Examples of Alerts include: ● A potentially malicious URL click was detected ● Email messages containing malware removed after delivery ● Email messages containing phish URLs removed after delivery ● Email reported by the user as malware or phish ● Suspicious email sending patterns detected ● User restricted from sending email The Microsoft 365 Defender connector lets you stream advanced hunting logs from Microsoft 365 Defender into Azure Sentinel. ● With the integration of Microsoft Defender for Endpoint into the Microsoft 365 Defender security umbrella, you can collect your Microsoft Defender for Endpoint advanced hunting events using the Use the Microsoft 365 Defender connector to stream your hunting events straight into your purpose-built tables in Azure Sentinel. The tables are built on the same schema that is used in the Microsoft 365 Defender portal, giving you complete access to the full set of advanced hunting logs and allowing you to do the following: ● Additionally, you can Easily copy your Microsoft Defender ATP advanced hunting queries into Azure Sentinel. ● ● Use the raw event logs to provide more insights for your alerts, hunting, and investigation, and correlate events with data from other data sources in Azure Sentinel. Microsoft 365 Defender
- 5. Azure Sentinel Threat Hunting SC-200 KQL Built-In Queries Custom Queries Live streams are based on Queries but are presented in real time. You can adjust the streaming options to display only the log info that you care about. Live Streams You can use KQL(Kustom Query Language) in Sentinel to hunt for security threats in your environment. You can filter through large amounts of data and security sources to identify potential threats or track down known and/or expected threats.You can find the Built-In Queries on the Sentinel “Hunting” page. Azure Sentinel uses the MITRE ATT&CK framework to categorize and order queries by tactics. ATT&CK is a knowledge base of tactics and techniques that are used and observed in the global threat landscape. You can use MITRE ATT&CK to develop your threat-hunting models. Refine your threat hunting by using Custom Queries. You can modify an existing Query and modify a query and display the results in real time. You can then save them for further use. Bookmarks Bookmarks help you to hunt for threats by saving the queries that you’ve run or identified as relevant. This saves administrative time and improves threat hunting efforts. You can also record your findings observations by adding notes and tags. Bookmarked data is visible and readily available for you and/or your Team.
- 6. Azure Sentinel Notebooks SC-200 Visualization/Graphic s Data Processing/Analysis Stats & Numerical Computing Machine/Deep Learning Notebooks come packaged with Azure Sentinel. Some of these notebooks are built for a specific scenario and can be used as-is. Others are samples that are meant to illustrate the techniques and features of Sentinel Notebooks. You can also import/deploy Notebooks from the Azure Sentinel Community GitHub. Notebooks have two components: 1. The browser-based interface where you enter and run queries and code and where the execution results are displayed. 2. The kernel, which is responsible for parsing and executing the code itself. The Azure Sentinel notebooks make use of many security-focused Python libraries, Including:
- 7. Azure Sentinel Playbooks 1 2 3 4 5 ● You can create security playbooks in Sentinel to automatically respond to alerts. ● You create them by using Logic Apps, which run in response to a pre-configured alert. ● You can run these security playbooks manually in response to your investigation of an incident or you can configure an alert to run them automatically(automation playbook). A trigger is an event that occurs when a specific set of conditions is satisfied. Triggers activate automatically when conditions are met. For example, a security incident occurs in Azure Sentinel, which is a trigger for an automated action. Playbooks need to be attached to an analytics rule to automate incedent responses. You can use the Automated Response section in the analytics rule to select a playbook to run automatically when the alert is generated. For more information on how to create analytics rule, see the "Threat detection with Azure Sentinel analytics" module. Check out a list of sample Azure Sentinel Playbooks HERE. An action is an operation that performs a task in the Logic Apps workflow. Actions run when a trigger activates, another action completes, or a condition is met. SC-200
- 8. Azure Sentinel Incident Management SC-200 Find and Remediate Security Threats For Example: You recently noticed that a significant number of VMs were deleted from your Azure subscription. Due to a recent alert, you decide to implement an analytics rule to create an incident when someone deletes an existing VM. You can then investigate the incident to determine the details, and close the incident when you're finished. -Incident Management is the process of incident investigation. -This includes creation, in-depth investigation, and then resolution. -You can use Sentinel to review detailed incident information, assign an incident owner, set and maintain incident severity, and manage incident status. Most incidents are generated because of an analytics rule ALERT. Examples of Alerts include: ● Detection of suspicious files. ● Detection of suspicious user activities. ● Attempted elevation of privilege. ● Analytics rules generate alerts, based on either KQL queries or direct connection to Microsoft Security solutions such as Azure Security Center or Microsoft Defender 365. If you enable alert grouping, Azure Sentinel includes any related alert evidence for the incident.riv
- 9. Azure Sentinel Logs Collect the right data for Analysis Use Azure Sentinel Connectors to connect your data sources and collect log data. The Data Connectors page displays a growing list of connectors provided by Azure Sentinel. Examples include: ● Microsoft/Azure Services - The connectors for Microsoft and Azure-related services include (but are not limited to): ● Azure Active Directory - audit logs and sign-in logs - See who is signing in, when, from where, and how by analyzing your sign-in data. ● Azure AD Identity Protection - Further auditing and investigation of privileged accounts and what they’re being used for. ● Azure Security Center - Alerts from Azure Defender solutions ● Cloud App Security - See what risks and vulnerabilities are present in your cloud/web apps. ● Office 365 You can use the Log Analytics Data Collector API to send log data to the Azure Sentinel Log Analytics workspace.
