Resiliency in the cloud myths versus facts
•
0 gefällt mir•204 views
Analisis comparativo de las soluciones en la Nube
Melden
Teilen
Melden
Teilen
Downloaden Sie, um offline zu lesen
Empfohlen
Big data analysis concepts and references by Cloud Security Alliance

Big data analysis concepts and references by Cloud Security AllianceInformation Security Awareness Group
Navigating through the Cloud - 7 feb 2012 at Institute for Information Manage...

Navigating through the Cloud - 7 feb 2012 at Institute for Information Manage...Livingstone Advisory
Weitere ähnliche Inhalte
Ähnlich wie Resiliency in the cloud myths versus facts
Big data analysis concepts and references by Cloud Security Alliance

Big data analysis concepts and references by Cloud Security AllianceInformation Security Awareness Group
Navigating through the Cloud - 7 feb 2012 at Institute for Information Manage...

Navigating through the Cloud - 7 feb 2012 at Institute for Information Manage...Livingstone Advisory
Ähnlich wie Resiliency in the cloud myths versus facts (20)
Will You Be Prepared When The Next Disaster Strikes - Whitepaper

Will You Be Prepared When The Next Disaster Strikes - Whitepaper
Big data analysis concepts and references by Cloud Security Alliance

Big data analysis concepts and references by Cloud Security Alliance
Symantec Disaster Recovery Orchestrator: One Click Disaster Recovery to the C...

Symantec Disaster Recovery Orchestrator: One Click Disaster Recovery to the C...
[Report] Five Trends Reveal The Emergence of Cloud-First Enterprises![[Report] Five Trends Reveal The Emergence of Cloud-First Enterprises](data:image/gif;base64,R0lGODlhAQABAIAAAAAAAP///yH5BAEAAAAALAAAAAABAAEAAAIBRAA7)
![[Report] Five Trends Reveal The Emergence of Cloud-First Enterprises](data:image/gif;base64,R0lGODlhAQABAIAAAAAAAP///yH5BAEAAAAALAAAAAABAAEAAAIBRAA7)
[Report] Five Trends Reveal The Emergence of Cloud-First Enterprises
What makes the large enterprise network management, large

What makes the large enterprise network management, large
V mware business trend brief - crash insurance - protect your business with...

V mware business trend brief - crash insurance - protect your business with...
Navigating through the Cloud - 7 feb 2012 at Institute for Information Manage...

Navigating through the Cloud - 7 feb 2012 at Institute for Information Manage...
Rob Livingstone Advisory - The risks of a fractured cloud strategy within th...

Rob Livingstone Advisory - The risks of a fractured cloud strategy within th...
Disaster Recovery & Business Resilience Trends - CloudSmartz | Smarter Transf...

Disaster Recovery & Business Resilience Trends - CloudSmartz | Smarter Transf...
Disaster Recovery: Understanding Trend, Methodology, Solution, and Standard

Disaster Recovery: Understanding Trend, Methodology, Solution, and Standard
Mastering Backup and Disaster Recovery: Ensuring Data Continuity and Resilience

Mastering Backup and Disaster Recovery: Ensuring Data Continuity and Resilience
Kürzlich hochgeladen
Kürzlich hochgeladen (20)
Transforming Data Streams with Kafka Connect: An Introduction to Single Messa...

Transforming Data Streams with Kafka Connect: An Introduction to Single Messa...
How to Remove Document Management Hurdles with X-Docs?

How to Remove Document Management Hurdles with X-Docs?
The Codex of Business Writing Software for Real-World Solutions 2.pptx

The Codex of Business Writing Software for Real-World Solutions 2.pptx
The 7 Things I Know About Cyber Security After 25 Years | April 2024

The 7 Things I Know About Cyber Security After 25 Years | April 2024
Unblocking The Main Thread Solving ANRs and Frozen Frames

Unblocking The Main Thread Solving ANRs and Frozen Frames
08448380779 Call Girls In Diplomatic Enclave Women Seeking Men

08448380779 Call Girls In Diplomatic Enclave Women Seeking Men
Human Factors of XR: Using Human Factors to Design XR Systems

Human Factors of XR: Using Human Factors to Design XR Systems
08448380779 Call Girls In Friends Colony Women Seeking Men

08448380779 Call Girls In Friends Colony Women Seeking Men
Neo4j - How KGs are shaping the future of Generative AI at AWS Summit London ...

Neo4j - How KGs are shaping the future of Generative AI at AWS Summit London ...
Scaling API-first – The story of a global engineering organization

Scaling API-first – The story of a global engineering organization
How to Troubleshoot Apps for the Modern Connected Worker

How to Troubleshoot Apps for the Modern Connected Worker
Tech-Forward - Achieving Business Readiness For Copilot in Microsoft 365

Tech-Forward - Achieving Business Readiness For Copilot in Microsoft 365
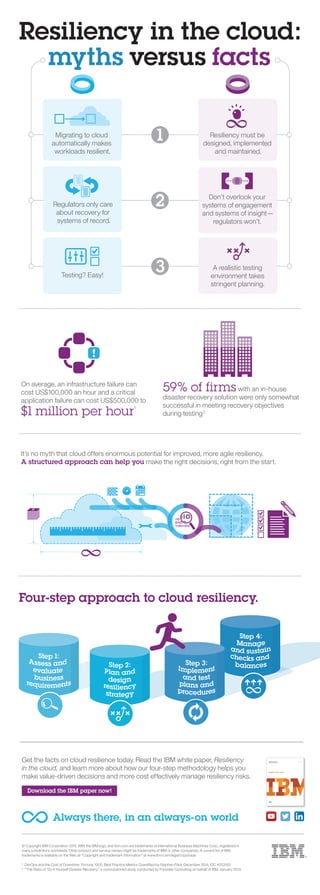
Resiliency in the cloud myths versus facts
- 1. Resiliency in the cloud: myths versus facts On average, an infrastructure failure can cost US$100,000 an hour and a critical application failure can cost US$500,000 to $1 million per hour1 Regulators only care about recovery for systems of record. Don’t overlook your systems of engagement and systems of insight— regulators won’t. 59% of firms with an in-house disaster recovery solution were only somewhat successful in meeting recovery objectives during testing2 Testing? Easy! A realistic testing environment takes stringent planning. Migrating to cloud automatically makes workloads resilient. Resiliency must be designed, implemented and maintained. 1 3 2 It’s no myth that cloud offers enormous potential for improved, more agile resiliency. A structured approach can help you make the right decisions, right from the start. Four-step approach to cloud resiliency. © Copyright IBM Corporation 2015. IBM, the IBM logo, and ibm.com are trademarks of International Business Machines Corp., registered in many jurisdictions worldwide. Other product and service names might be trademarks of IBM or other companies. A current list of IBM trademarks is available on the Web at “Copyright and trademark information” at www.ibm.com/legal/copytrade. 1 DevOps and the Cost of Downtime: Fortune 1000, Best Practice Metrics Quantified by Stephen Elliot, December 2014, IDC #253155 2 ”The Risks of ‘Do It Yourself Disaster Recovery,” a commissioned study conducted by Forrester Consulting on behalf of IBM, January 2013. Get the facts on cloud resilience today. Read the IBM white paper, Resiliency in the cloud, and learn more about how our four-step methodology helps you make value-driven decisions and more cost effectively manage resiliency risks. Download the IBM paper now! Always there, in an always-on world
