CNDSP Assessment Template
•
1 gefällt mir•1,212 views
Computer Network Defense (CND) Assessment Template to track progress since previous baseline assessment.
Melden
Teilen
Melden
Teilen
Downloaden Sie, um offline zu lesen
Empfohlen
Empfohlen
Weitere ähnliche Inhalte
Was ist angesagt?
Was ist angesagt? (20)
Guideline for the certification of wind turbine service technicians 2015 july

Guideline for the certification of wind turbine service technicians 2015 july
Matteo Meucci Software Security in practice - Aiea torino - 30-10-2015

Matteo Meucci Software Security in practice - Aiea torino - 30-10-2015
The Six Stages of Incident Response - Auscert 2016

The Six Stages of Incident Response - Auscert 2016
Prioritizing an audit program using the 20 critical controls

Prioritizing an audit program using the 20 critical controls
Why Static Analysis is mandatory for IoT device software

Why Static Analysis is mandatory for IoT device software
New USM v5.0 - Get Complete Security Visibility Faster & Easier Than Ever

New USM v5.0 - Get Complete Security Visibility Faster & Easier Than Ever
Enterprise Class Vulnerability Management Like A Boss

Enterprise Class Vulnerability Management Like A Boss
Key Strategies to Address Rising Application Risk in Your Enterprise

Key Strategies to Address Rising Application Risk in Your Enterprise
Vulnerability Management: What You Need to Know to Prioritize Risk

Vulnerability Management: What You Need to Know to Prioritize Risk
Importance Of Structured Incident Response Process

Importance Of Structured Incident Response Process
Andere mochten auch
Andere mochten auch (20)
NIST Policy Mapped to 800-53-800-53A-controls-and-objectives (Legal Size)

NIST Policy Mapped to 800-53-800-53A-controls-and-objectives (Legal Size)
Job aid framework-for-improving-critical-infrastructure-cybersecurity-core-jwd

Job aid framework-for-improving-critical-infrastructure-cybersecurity-core-jwd
Risk Management Framework (RMF) STEP 4- Access Security Controls - NIST SP 80...

Risk Management Framework (RMF) STEP 4- Access Security Controls - NIST SP 80...
Mike Bolger - Predict Webinar 2 - Contaminants in Food – Hazards and Risks

Mike Bolger - Predict Webinar 2 - Contaminants in Food – Hazards and Risks
(1a) map csc 5 to nist sp 800 53 rev 4 (security control table portrait) 2014...

(1a) map csc 5 to nist sp 800 53 rev 4 (security control table portrait) 2014...
(1b) Map CSC v5.0 to NIST SP 800 53 Revision 4 (security control table landsc...

(1b) Map CSC v5.0 to NIST SP 800 53 Revision 4 (security control table landsc...
Policy. FedRAMP Security Assessment Plan (SAP) Template, Policy and Procedure...

Policy. FedRAMP Security Assessment Plan (SAP) Template, Policy and Procedure...
Map Critical Security Controls (CSC) v5.0 to NIST SP 800-53 Revision 4 (Summa...

Map Critical Security Controls (CSC) v5.0 to NIST SP 800-53 Revision 4 (Summa...
Critical Security Controls v4 1 Mapped to NIST SP 800-53 Rev.4-final r6a

Critical Security Controls v4 1 Mapped to NIST SP 800-53 Rev.4-final r6a
RMF STEP 2: SELECT (NIST 800-53 Rev. 3 Controls, Enhancements and Supplementa...

RMF STEP 2: SELECT (NIST 800-53 Rev. 3 Controls, Enhancements and Supplementa...
Ähnlich wie CNDSP Assessment Template
Ähnlich wie CNDSP Assessment Template (20)
Edgescan vulnerability stats report 2019 - h-isac-2-2-2019

Edgescan vulnerability stats report 2019 - h-isac-2-2-2019
An evaluation of two host based intrusion prevention systems

An evaluation of two host based intrusion prevention systems
Research of Intrusion Preventio System based on Snort

Research of Intrusion Preventio System based on Snort
Security Testing Report Hitachi Application Q1 Sep 2015

Security Testing Report Hitachi Application Q1 Sep 2015
[cb22] "The Present and Future of Coordinated Vulnerability Disclosure" Inter...![[cb22] "The Present and Future of Coordinated Vulnerability Disclosure" Inter...](data:image/gif;base64,R0lGODlhAQABAIAAAAAAAP///yH5BAEAAAAALAAAAAABAAEAAAIBRAA7)
![[cb22] "The Present and Future of Coordinated Vulnerability Disclosure" Inter...](data:image/gif;base64,R0lGODlhAQABAIAAAAAAAP///yH5BAEAAAAALAAAAAABAAEAAAIBRAA7)
[cb22] "The Present and Future of Coordinated Vulnerability Disclosure" Inter...
Leveraging Vulnerability Management Beyond DPR (Discovery - Prioritization - ...

Leveraging Vulnerability Management Beyond DPR (Discovery - Prioritization - ...
FREQUENTLY ASKED QUESTION IN A TESTER INTERVIEW PENETRATION AND VULNERABILITY

FREQUENTLY ASKED QUESTION IN A TESTER INTERVIEW PENETRATION AND VULNERABILITY
A Comparative Study between Vulnerability Assessment and Penetration Testing

A Comparative Study between Vulnerability Assessment and Penetration Testing
RADAR - Le nouveau scanner de vulnérabilité par F-Secure

RADAR - Le nouveau scanner de vulnérabilité par F-Secure
Demonstrating Information Security Program Effectiveness

Demonstrating Information Security Program Effectiveness
Disrupting the Malware Kill Chain - What's New from Palo Alto Networks.

Disrupting the Malware Kill Chain - What's New from Palo Alto Networks.
Mehr von James W. De Rienzo
Mehr von James W. De Rienzo (11)
FedRAMP 2.0 Control-Implementation-Summary (CIS) v2 1 cross-matrixed with Fed...

FedRAMP 2.0 Control-Implementation-Summary (CIS) v2 1 cross-matrixed with Fed...
NIST NVD REV 4 Security Controls Online Database Analysis

NIST NVD REV 4 Security Controls Online Database Analysis
(4) NIST SP 800-53 Revision 4 (security control enhancements omitted) 20140804

(4) NIST SP 800-53 Revision 4 (security control enhancements omitted) 20140804
(3) Map Council on CyberSecurity's Critical Security Controls (CSC) Version 5...

(3) Map Council on CyberSecurity's Critical Security Controls (CSC) Version 5...
(2) map csc 5 to nist sp 800 53 rev 4 (controls & enhancements) 20140804

(2) map csc 5 to nist sp 800 53 rev 4 (controls & enhancements) 20140804
Information Assurance, A DISA CCRI Conceptual Framework

Information Assurance, A DISA CCRI Conceptual Framework
Information System Sensitivity Level Impact Assessment (NIST SP 800-60v2r1)

Information System Sensitivity Level Impact Assessment (NIST SP 800-60v2r1)
Kürzlich hochgeladen
Kürzlich hochgeladen (20)
What Are The Drone Anti-jamming Systems Technology?

What Are The Drone Anti-jamming Systems Technology?
2024: Domino Containers - The Next Step. News from the Domino Container commu...

2024: Domino Containers - The Next Step. News from the Domino Container commu...
TrustArc Webinar - Stay Ahead of US State Data Privacy Law Developments

TrustArc Webinar - Stay Ahead of US State Data Privacy Law Developments
Advantages of Hiring UIUX Design Service Providers for Your Business

Advantages of Hiring UIUX Design Service Providers for Your Business
08448380779 Call Girls In Civil Lines Women Seeking Men

08448380779 Call Girls In Civil Lines Women Seeking Men
Raspberry Pi 5: Challenges and Solutions in Bringing up an OpenGL/Vulkan Driv...

Raspberry Pi 5: Challenges and Solutions in Bringing up an OpenGL/Vulkan Driv...
Presentation on how to chat with PDF using ChatGPT code interpreter

Presentation on how to chat with PDF using ChatGPT code interpreter
Bajaj Allianz Life Insurance Company - Insurer Innovation Award 2024

Bajaj Allianz Life Insurance Company - Insurer Innovation Award 2024
Scaling API-first – The story of a global engineering organization

Scaling API-first – The story of a global engineering organization
The 7 Things I Know About Cyber Security After 25 Years | April 2024

The 7 Things I Know About Cyber Security After 25 Years | April 2024
The Role of Taxonomy and Ontology in Semantic Layers - Heather Hedden.pdf

The Role of Taxonomy and Ontology in Semantic Layers - Heather Hedden.pdf
Factors to Consider When Choosing Accounts Payable Services Providers.pptx

Factors to Consider When Choosing Accounts Payable Services Providers.pptx
08448380779 Call Girls In Diplomatic Enclave Women Seeking Men

08448380779 Call Girls In Diplomatic Enclave Women Seeking Men
CNDSP Assessment Template
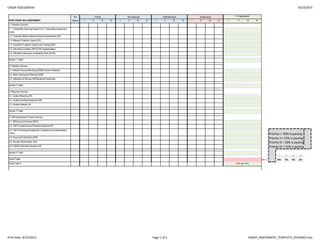
- 1. CNDSP ASSESSMENT 8/23/2014 Not Priority Not Observed Potential Score Actual Score % Implemented POST-CNDSP SAV ASSESSMENT Obsrvd I II III IV I II III IV I II III IV I II III IV I II III IV 1. Protection Services 1.1. Vulnerability Scanning Support (VS) / Vulnerability Assessment (VAA) 1.2. Computer Network Defense External Assessments (EA) 1.3. Malware Protection Support (AV) 1.4. Subscriber Protection Support and Training (S&T) 1.5. Information Condition (INFOCON) Implementation 1.6. Information Assurance Vulnerability Alerts (IAVM) Section 1 Totals 2. Detection Services 2.1. Network Security Monitoring (NSM)/ Intrusion Detection 2.2. Attack Sensing and Warning (ASW) 2.3. Indications & Warning (IW)/Situational Awareness Section 2 Totals 3. Response Services 3.1. Incident Reporting (IR) 3.2. Incident Handling Response (IHR) 3.3. Incident Analysis (IA) Section 3 Totals 4. CND Sustainment Function Services 4.1. MOU(s) and Contracts (MOU) 4.2. CND Functional Level Policies/Procedures (FP) 4.3. CND Technology Development, Evaluation and Implementation (TDEI) Priority I = 90% is passing 4.4. Personnel & Workforce (PW) Priority II = 75% is passing 4.5. Security Administration (SA) Priority III = 50% is passing 4.6. CNDSP Information Systems (IS) Priority IV = 25% is passing Section 4 Totals I II III IV Grand Totals <---- 90% 75% 50% 25% Grand Total % FAIL or PASS Print Date: 8/23/2014 Page 1 of 3 CNDSP_ASSESSMENT_TEMPLATE_20140823.xlsx
- 2. CNDSP ASSESSMENT 8/23/2014 Not Priority Not Observed Potential Score Actual Score % Implemented BASELINE C&A CNDSP Obsrvd I II III IV I II III IV I II III IV I II III IV I II III IV 1. Protection Services 1.1. Vulnerability Scanning Support (VS) / Vulnerability Assessment (VAA) 1.2. Computer Network Defense External Assessments (EA) 1.3. Malware Protection Support (AV) 1.4. Subscriber Protection Support and Training (S&T) 1.5. Information Condition (INFOCON) Implementation 1.6. Information Assurance Vulnerability Alerts (IAVM) Section 1 Totals 2. Detection Services 2.1. Network Security Monitoring (NSM)/ Intrusion Detection 2.2. Attack Sensing and Warning (ASW) 2.3. Indications & Warning (IW)/Situational Awareness Section 2 Totals 3. Response Services 3.1. Incident Reporting (IR) 3.2. Incident Handling Response (IHR) 3.3. Incident Analysis (IA) Section 3 Totals 4. CND Sustainment Function Services 4.1. MOU(s) and Contracts (MOU) 4.2. CND Functional Level Policies/Procedures (FP) 4.3. CND Technology Development, Evaluation and Implementation (TDEI) Priority I = 90% is passing 4.4. Personnel & Workforce (PW) Priority II = 75% is passing 4.5. Security Administration (SA) Priority III = 50% is passing 4.6. CNDSP Information Systems (IS) Priority IV = 25% is passing Section 4 Totals I II III IV Grand Totals <---- 90% 75% 50% 25% Grand Total % #DIV/0! #DIV/0! #DIV/0! #DIV/0! #DIV/0! #DIV/0! #DIV/0! #DIV/0! #DIV/0! #DIV/0! #DIV/0! #DIV/0! FAIL or PASS Print Date: 8/23/2014 Page 2 of 3 CNDSP_ASSESSMENT_TEMPLATE_20140823.xlsx
- 3. CNDSP ASSESSMENT 8/23/2014 Not Priority Not Observed Potential Score Actual Score Variance CNDSP Services Obsrvd I II III IV I II III IV I II III IV I II III IV 1. Protection Services 1.1. Vulnerability Scanning Support (VS) / Vulnerability Assessment (VAA) 1.2. Computer Network Defense External Assessments (EA) 1.3. Malware Protection Support (AV) 1.4. Subscriber Protection Support and Training (S&T) 1.5. Information Condition (INFOCON) Implementation 1.6. Information Assurance Vulnerability Alerts (IAVM) Section 1 Totals 2. Detection Services 2.1. Network Security Monitoring (NSM)/ Intrusion Detection 2.2. Attack Sensing and Warning (ASW) 2.3. Indications & Warning (IW)/Situational Awareness Section 2 Totals 3. Response Services 3.1. Incident Reporting (IR) 3.2. Incident Handling Response (IHR) 3.3. Incident Analysis (IA) Section 3 Totals 4. CND Sustainment Function Services 4.1. MOU(s) and Contracts (MOU) 4.2. CND Functional Level Policies/Procedures (FP) 4.3. CND Technology Development, Evaluation and Implementation (TDEI) 4.4. Personnel & Workforce (PW) 4.5. Security Administration (SA) 4.6. CNDSP Information Systems (IS) Section 4 Totals Grand Totals Grand Total % Print Date: 8/23/2014 Page 3 of 3 CNDSP_ASSESSMENT_TEMPLATE_20140823.xlsx
