Tcp ack or syn+ack coming to fwsm running tp mode when session is not in the connection table
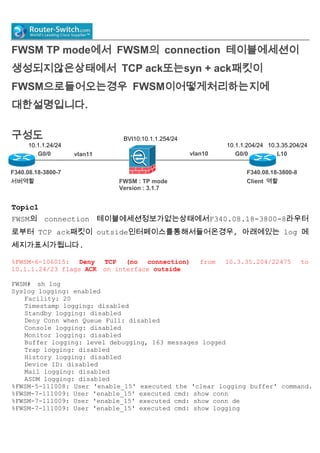
- 1. FWSM TP mode에서 FWSM의 connection 테이블에세션이 생성되지않은상태에서 TCP ack또는syn + ack패킷이 FWSM으로들어오는경우 FWSM이어떻게처리하는지에 대한설명입니다. 구성도 Topic1 FWSM의 connection 테이블에세션정보가없는상태에서F340.08.18-3800-8라우터 로부터 TCP ack패킷이 outside인터페이스를통해서들어온경우, 아래에있는 log 메 세지가표시가됩니다. %FWSM-6-106015: Deny TCP (no connection) from 10.3.35.204/22475 to 10.1.1.24/23 flags ACK on interface outside FWSM# sh log Syslog logging: enabled Facility: 20 Timestamp logging: disabled Standby logging: disabled Deny Conn when Queue Full: disabled Console logging: disabled Monitor logging: disabled Buffer logging: level debugging, 163 messages logged Trap logging: disabled History logging: disabled Device ID: disabled Mail logging: disabled ASDM logging: disabled %FWSM-5-111008: User 'enable_15' executed the 'clear logging buffer' command. %FWSM-7-111009: User 'enable_15' executed cmd: show conn %FWSM-7-111009: User 'enable_15' executed cmd: show conn de %FWSM-7-111009: User 'enable_15' executed cmd: show logging F340.08.18-3800-8 Client 역할 vlan11 F340.08.18-3800-7 서버역할 vlan10 10.1.1.24/24 10.1.1.204/24 10.3.35.204/24 FWSM : TP mode Version : 3.1.7 G0/0 G0/0 L10 BVI10:10.1.1.254/24
- 2. %FWSM-5-111007: Begin configuration: 127.0.0.51 reading from terminal %FWSM-5-111008: User 'enable_15' executed the 'configure terminal' command. %FWSM-5-111005: 127.0.0.51 end configuration: OK %FWSM-5-111007: Begin configuration: 127.0.0.51 reading from terminal %FWSM-5-111008: User 'enable_15' executed the 'configure terminal' command. %FWSM-5-111005: 127.0.0.51 end configuration: OK %FWSM-7-111009: User 'enable_15' executed cmd: show conn %FWSM-7-111009: User 'enable_15' executed cmd: show conn %FWSM-7-111009: User 'enable_15' executed cmd: show logging %FWSM-6-106015: Deny TCP (no connection) from 10.3.35.204/22475 to 10.1.1.24/23 flags ACK on interface outside %FWSM-6-302013: Built inbound TCP connection 145673024472747997 for outside:10.3.35.204/64591 (10.3.35.204/64591) to inside:10.1.1.24/23 (10.1.1.24/23) Topic2. FWSM의 connection 테이블에세션정보가없는상태에서F340.08.18-3800-7 라우터 로부터 TCP syn + ack패킷이 inside인터페이스를통해서들어온경우, 아래에있는 log 메세지가표시가됩니다. %FWSM-6-106015: Deny TCP (no connection) from 10.1.1.24/23 to 10.3.35.204/1500 flags SYN ACK on interface inside FWSM/admin# shlogg %FWSM-6-106015: Deny TCP (no connection) from 10.1.1.24/23 to 10.3.35.204/1500 flags SYN ACK on interface inside %FWSM-6-106015: Deny TCP (no connection)from 10.1.1.24/23 to 10.3.35.204/44069 flags SYN ACKon interface inside %FWSM-6-106015: Deny TCP (no connection) from 10.1.1.24/23 to 10.3.35.204/44070 flags SYN ACK on interface inside %FWSM-6-106015: Deny TCP (no connection) from 10.1.1.24/23 to 10.3.35.204/44071 flags SYN ACK on interface inside %FWSM-6-106015: Deny TCP (no connection) from 10.1.1.24/23 to 10.3.35.204/44072 flags SYN ACK on interface inside %FWSM-6-106015: Deny TCP (no connection) from 10.1.1.24/23 to 10.3.35.204/44073 flags SYN ACK on interface inside 시험에사용된설정 F340.08.18-3800-8설정 F340.08.18-3800-8#sh run Building configuration... Current configuration : 1039 bytes ! ! Last configuration change at 04:52:22 UTC Tue Nov 12 2013 version 15.1 service timestamps debug datetimemsec
- 3. service timestamps log datetimemsec no service password-encryption ! hostname F340.08.18-3800-8 ! boot-start-marker boot-end-marker ! ! ! noaaa new-model ! ! dot11 syslog ip source-route ! ! ! ipcef ! ! no ipv6 cef ! multilink bundle-name authenticated ! ! ! ! voice-card 0 ! ! ! ! ! ! ! cryptopki token default removal timeout 0 ! ! ! ! licenseudipid CISCO3825 sn FTX0951C0LK ! redundancy ! ! ! ! ! ! !
- 4. ! ! ! interface Loopback10 ip address 10.3.35.204 255.255.255.0 ! interface GigabitEthernet0/0 ip address 10.1.1.204 255.255.255.0 duplex full speed auto media-type rj45 ! interface GigabitEthernet0/1 noip address shutdown duplex auto speed auto media-type rj45 ! ip forward-protocol nd ! ! noip http server noip http secure-server ! ! ! ! ! ! ! control-plane ! ! ! ! mgcp profile default ! ! ! ! ! ! line con 0 line aux 0 linevty 0 4 login transport input all ! scheduler allocate 20000 1000 end
- 5. F340.08.18-3800-8#sh ipintbr Interface IP-Address OK? Method Status Protocol GigabitEthernet0/0 10.1.1.204 YES manual up up GigabitEthernet0/1 unassigned YES NVRAM administratively down down Loopback10 10.3.35.204 YES manual up up FWSM 설정 FWSM/admin# shver FWSM Firewall Version 3.1(7) <context> FWSM# sh run : Saved : FWSM Version 3.1(7) ! firewall transparent hostname FWSM enable password 8Ry2YjIyt7RRXU24 encrypted names ! interface Vlan10 nameif outside bridge-group 10 security-level 0 ! interface Vlan11 nameif inside bridge-group 10 security-level 100 ! interface BVI10 ip address 10.1.1.254 255.255.255.0 ! passwd 2KFQnbNIdI.2KYOU encrypted ftp mode passive access-list all extended permit ip any any access-listhh extended permit ip host 10.1.1.204 host 10.1.1.24 access-listhh extended permit ip host 10.1.1.24 host 10.1.1.204 pager lines 24 logging enable logging buffer-size 1000000 logging buffered debugging mtu outside 1500 mtu inside 1500 no failover icmp permit any outside icmp permit any inside noasdm history enable
- 6. arp timeout 14400 access-group all in interface outside access-group all in interface inside timeoutxlate 3:00:00 timeout conn 0:05:00 half-closed 0:10:00 udp 0:02:00 icmp 0:00:02 timeoutsunrpc 0:10:00 h323 1:00:00 h225 1:00:00 mgcp 0:05:00 timeoutmgcp-pat 0:05:00 sip 0:30:00 sip_media 0:02:00 timeoutuauth 0:05:00 absolute nosnmp-server location nosnmp-server contact snmp-server enable traps snmp authentication linkup linkdowncoldstart telnet timeout 5 ssh timeout 5 console timeout 0 ! class-mapinspection_default match default-inspection-traffic ! ! policy-mapglobal_policy classinspection_default inspectdns maximum-length 512 inspect ftp inspect h323 h225 inspect h323 ras inspectrsh inspectsmtp inspectsqlnet inspect skinny inspectsunrpc inspectxdmcp inspect sip inspectnetbios inspecttftp ! service-policyglobal_policy global prompt hostname context Cryptochecksum:57da25c712fea479bcb6da8ec935423e : end FWSM# F340.11.09-6500-2#sh cdp ne Capability Codes: R - Router, T - Trans Bridge, B - Source Route Bridge S - Switch, H - Host, I - IGMP, r - Repeater, P - Phone, D - Remote, C - CVTA, M - Two-port Mac Relay Device ID Local IntrfceHoldtmeCapability Platform Port ID F340.08.18-3800-8 Gig 2/2 146 R S I 3825 Gig 0/0 F340.08.18-3800-7 Gig 2/1 146 R S I 3825 Gig 0/0
- 7. F340.08.18-3800-7설정 F340.08.18-3800-7#sh run Building configuration... Current configuration : 1259 bytes ! ! Last configuration change at 05:56:32 UTC Tue Nov 12 2013 version 15.1 service timestamps debug datetimemsec service timestamps log datetimemsec no service password-encryption ! hostname F340.08.18-3800-7 ! boot-start-marker boot system flash:c3825-advipservicesk9-mz.151-4.M7 boot-end-marker ! ! ! noaaa new-model ! ! dot11 syslog ip source-route ! ! ! ipcef ! ! ip host PAGENT-SECURITY-V3 55.11.39.5 36.72.0.0 no ipv6 cef ! multilink bundle-name authenticated ! ! ! ! voice-card 0 ! ! ! ! ! ! ! cryptopki token default removal timeout 0 !
- 8. ! ! ! licenseudipid CISCO3825 sn FTX1012A01W ! redundancy ! ! ! ! ! ! ! ! ! ! interface GigabitEthernet0/0 ip address 10.1.1.24 255.255.255.0 duplex full speed auto media-type rj45 ! interface GigabitEthernet0/1 noip address shutdown duplex auto speed auto media-type rj45 ! ip forward-protocol nd ! ! noip http server noip http secure-server ip route 0.0.0.0 0.0.0.0 10.1.1.204 ! ! ! ! ! ! ! control-plane ! ! ! ! mgcp profile default ! ! !
- 9. ! ! ! line con 0 exec-timeout 0 0 line aux 0 linevty 0 4 privilege level 15 no login transport input all ! scheduler allocate 20000 1000 end More Cisco Network Topics you can visit: http://blog.router-switch.com/
