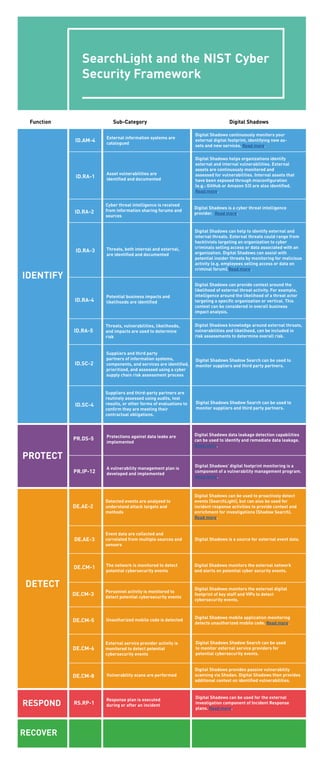
Digital Shadows and the NIST Cyber Security Framework
- 1. SearchLight and the NIST Cyber Security Framework IDENTIFY PROTECT DETECT RESPOND RECOVER ID.AM-4 Function Sub-Category Digital Shadows ID.RA-1 ID.RA-2 ID.RA-3 ID.RA-4 ID.RA-5 ID.SC-2 ID.SC-4 PR.DS-5 PR.IP-12 DE.CM-1 DE.AE-2 DE.AE-3 DE.CM-3 DE.CM-5 DE.CM-6 DE.CM-8 RS.RP-1 External information systems are catalogued Asset vulnerabilities are identified and documented Cyber threat intelligence is received from information sharing forums and sources Threats, both internal and external, are identified and documented Potential business impacts and likelihoods are identified Threats, vulnerabilities, likelihoods, and impacts are used to determine risk Suppliers and third party partners of information systems, components, and services are identified, prioritized, and assessed using a cyber supply chain risk assessment process Suppliers and third-party partners are routinely assessed using audits, test results, or other forms of evaluations to confirm they are meeting their contractual obligations. Protections against data leaks are implemented Event data are collected and correlated from multiple sources and sensors Digital Shadows is a source for external event data. A vulnerability management plan is developed and implemented The network is monitored to detect potential cybersecurity events Detected events are analyzed to understand attack targets and methods Digital Shadows can be used to proactively detect events (SearchLight), but can also be used for incident response activities to provide context and enrichment for investigations (Shadow Search). Read more. Personnel activity is monitored to detect potential cybersecurity events Unauthorized mobile code is detected External service provider activity is monitored to detect potential cybersecurity events Vulnerability scans are performed Response plan is executed during or after an incident Digital Shadows continuously monitors your external digital footprint, identifying new as- sets and new services. Read more. Digital Shadows helps organizations identify external and internal vulnerabilities. External assets are continuously monitored and assessed for vulnerabilities. Internal assets that have been exposed through misconfiguration (e.g.: GitHub or Amazon S3) are also identified. Read more. Digital Shadows is a cyber threat intelligence provider. Read more. Digital Shadows can help to identify external and internal threats. External threats could range from hacktivists targeting an organization to cyber criminals selling access or data associated with an organization. Digital Shadows can assist with potential insider threats by monitoring for malicious activity (e.g. employees selling access or data on criminal forum).Read more. Digital Shadows can provide context around the likelihood of external threat activity. For example, intelligence around the likelihood of a threat actor targeting a specific organization or vertical. This context can be considered in overall business impact analysis. Digital Shadows knowledge around external threats, vulnerabilities and likelihood, can be included in risk assessments to determine overall risk. Digital Shadows Shadow Search can be used to monitor suppliers and third party partners. Digital Shadows Shadow Search can be used to monitor suppliers and third party partners. Digital Shadows data leakage detection capabilities can be used to identify and remediate data leakage. Read more. Digital Shadows’ digital footprint monitoring is a component of a vulnerability management program. Read more. Digital Shadows monitors the external network and alerts on potential cyber security events. Digital Shadows monitors the external digital footprint of key staff and VIPs to detect cybersecurity events. Digital Shadows mobile application monitoring detects unauthorized mobile code. Read more. Digital Shadows Shadow Search can be used to monitor external service providers for potential cybersecurity events. Digital Shadows provides passive vulnerability scanning via Shodan. Digital Shadows then provides additional context on identified vulnerabilities. Digital Shadows can be used for the external investigation component of Incident Response plans. Read more.
