Distance Vector vs Link State Routing Protocols Explained
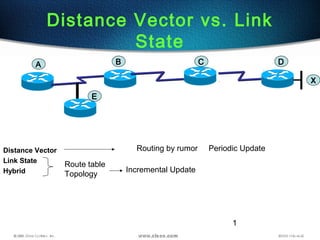
- 1. 1 Distance Vector Link State Hybrid Distance Vector vs. Link State Route table Topology Incremental Update Periodic UpdateRouting by rumor A B C D X E
- 2. 2 Distance Vector vs. Link State Distance VectorDistance Vector • Updates frequently • Each router is "aware" only of its immediate neighbors • Slow convergence • Prone to routing loops • Easy to configure Link State • Updates are event triggered • Each router is "aware" of all other routers in the "area" • Fast convergence • Less subject to routing loops • More difficult to configure
- 3. 3 Comparison Continued Distance VectorDistance Vector • Fewer router resources required • Updates require more bandwidth • Does not "understand" the topology of the network Link StateLink State • More router resource intensive • Updates require less bandwidth • Has detailed knowledge of distant networks and routers
- 4. 5 Link State Example OSPF IS-IS OSPF is used for corporate networks IS-IS is used for ISP’s
- 5. 6
- 6. 7 Open Shortest Path First (OSPF) OSPF is an open standards routing protocol This works by using the Dijkstra algorithm OSPF provides the following features: Minimizes routing update traffic Allows scalability (e.g. RIP is limited to 15 hops) Has unlimited hop count Supports VLSM/CIDR Allows multi-vendor deployment (open standard)
- 7. 8 Link State There are two types of Packets Hello LSA’s
- 8. 9 OSPF Hello • When router A starts it send Hello packet – uses 224.0.0.5 • Hello packets are received by all neighbors • B will write A’s name in its neighbor table • C also process the same way A B C
- 9. 10 "Hello" Packets • Small frequently issued packets • Discover neighbours and negotiate "adjacencies" • Verify continued availability of adjacent neighbours • Hello packets and Link State Advertisements (LSAs) build and maintain the topological database • Hello packets are addressed to 224.0.0.5.
- 10. 11 Link State Advertisement (LSA) An OSPF data packet containing link state and routing information that is shared among OSPF routers LSAs are shared only with routers with whom it has formed adjacencies LSA packets are used to update and maintain the topology database.
- 11. 12 Link State There are three type of tables Neighbor Topology Routing
- 12. 13 Tables Neighbor Contain information about the neighbors Neighbor is a router which shares a link on same network Another relationship is adjacency Not necessarily all neighbors LSA updates are only when adjacency is established
- 13. 14 Tables Topology Contain information about all network and path to reach any network All LSA’s are entered in to topology table When topology changes LSA’s are generated and send new LSA’s On topology table an algorithm is run to create a shortest path, this algorithm is known as SPF or dijkstra algorithm
- 14. 15 Tables Routing Table Also knows as forwarding database Generated when an algorithm is run on the topology database Routing table for each router is unique
- 15. 16 OSPF Terms Link Router ID Neighbours Adjacency OSPF Area Backbone area Internal routers Area Border Router (ABR) Autonomous System Boundary Router (ASBR)
- 16. 17 Link A network or router interface assigned to a given network Link (interface) will have "state" information associated with it Status (up or down) IP Address Network type (e.g. Fast Ethernet) Bandwidth Addresses of other routers attached to thisAddresses of other routers attached to this interfaceinterface
- 17. 18 OSPF Term: Link A link is a network or router interface assigned to any given network This link, or interface, will have state information associated with it (up or down) as well as one or more IP addresses
- 18. 19 OSPF Term: Link State Status of a link between two routers Information is shared between directly connected routers. This information propagates throughout the network unchanged and is also used to create a shortest path first (SPF) tree.
- 19. 20 Router ID The Router ID (RID) is an IP address used to identify the router Cisco chooses the Router ID by using the highest IP address of all configured loopback interfaces If no loopback interfaces are configured with addresses, OSPF will choose the highest IP address of all active physical interfaces. You can manually assign the router ID. The RID interface MUST always be up, therefore loopbacks are preferred
- 20. 21 Neighbours Neighbours are two or more routers that have an interface on a common network E.g. two routers connected on a serial link E.g. several routers connected on a common Ethernet or Frame relay network Communication takes place between / among neighbours neighbours form "adjacencies"
- 21. 22 Adjacency A relationship between two routers that permits the direct exchange of route updates Not all neighbours will form adjacencies This is done for reasons of efficiency – more later
- 22. 23 OSPF Design Each router connects to the backbone called area 0, or the backbone area. Routers that connect other areas to the backbone within an AS are called Area Border Routers (ABRs). One interface must be in area 0. OSPF runs inside an autonomous system, but can also connect multiple autonomous systems together. The router that connects these ASes together is called an Autonomous System Boundary Router (ASBR).
- 23. 24 OSPF Areas An OSPF area is a grouping of contiguous networks and routers Share a common area IDarea ID A router can be a member of more than one area (area border router) All routers in the same area have the same topology database When multiple areas exist, there must always be an area 0 (the backbone) to which other areas connect
- 24. 25 Why areas? Decreases routing overhead Compare to multiple smaller broadcast domains instead of one large one Speeds convergence Confines network instability (e.g. route "flapping") to single area of the network Adds considerably to the complexity of setting up OSPF CCNA certification deals only with single-area OSPF
- 26. 27 LSA’s in Area • LSAs communicate with adjacent routers in the same OSPF area • Subsequently, a change in a link state is "flooded" to all area routers via LSAs • In larger networks, multiple areas may be created – LSAs are sent only to adjacent routers in the same area – "Area border routers" connect areas, passing summarized route information between
- 27. 28 Path Calculation Changes to the topological database of a router trigger a recalculation to re-establish the best route(s) to known networks Uses the SPF (shortest path first) algorithm developed by a computer scientist named Dijkstra This is done by each individual router using its detailed "knowledge" of the whole network Leads to rapid and accurate convergence Based on detailed knowledge of every link in the area and the OSPF "cost" of each builds an OSPF treeOSPF tree with itself at the route
- 28. 29 Terminology: Cost • Various criteria can be selected by the administrator to determine the metric • Usually, OSPF cost=108 /bandwidth Do not forget to configure the bandwidth`bandwidth` command on serial links to ensure correct default OSPF cost
- 29. 30 Pros and Cons Note that OSPF is a more sophisticated routing protocol Converges rapidly and accurately Can use a metric calculation that effectively selects the "best" route(s) primarily based on bandwidth, although an OSPF cost can be administratively assigned Use of OSPF requires More powerful routing hardware More detailed knowledge by the administrator, especially when large multi-area networks are used
- 30. 31 Types of Neighbors • OSPF can be defined for three type of neighbors – Broadcast Multi Access (BMA) ex- Ethernet – Point to Point – Non-Broadcast Multi Access (NBMA)
- 32. 33 Adjacencies Point to Point all routers form adjacencies BMA & NBMA one router is elected as DR DR establish adjacency with every neighbor router LSA updates are exchanged only to DR DR is the router which has highest priority All CISCO routers has priority 1 If priority is same then router id is seen The RID is highest IP address of all interfaces
- 33. 34 Point-to-Point Links Usually a serial interface running either PPP or HDLC No DR or BDR election required OSPF autodetects this interface type OSPF packets are sent using multicast 224.0.0.5 All routers form adjacencies
- 34. 35 Multi-access Broadcast Network • Generally LAN technologies like Ethernet and Token Ring • DR and BDR selection required • All neighbor routers form full adjacencies with the DR and BDR only • Packets to the DR use 224.0.0.6 • Packets from DR to all other routers use 224.0.0.5
- 35. 36 Electing the DR and BDR Hello packets are exchanged via IP multicast. The router with the highest priority is selected as the DR. If Priority is same then Router ID is seen Use the OSPF router ID as the tie breaker.
- 36. 37 Terminology: DRs and BDRs The designateddesignated router (DR)router (DR) is responsible for generating LSAs on behalf of all routers connected to the same segment
- 37. 38 DR Responsibility When a router sees a new or changed link-state, it sends an LSA to its DR using a particular multicast address The DR then forwards the LSA to all the other routers with whom it is adjacent Minimizes the number of formal adjacencies that must be formed and therefore the amount of LSU (link state update) packet traffic in a multi-router network
- 38. 39 OSPF Summary AD -100 Hop count is unlimited Metric = Cost – 108 /BW Classless, VLSM Load balance up to SIX routers Require more processing power
- 39. 40 Basic OSPF Configuration Router(config)# router ospf 1Router(config)# router ospf 1 The number 1 in this example is a process-id #process-id # that begins an OSPF process in the router More than one process can be launched in a router, but this is rarely necessary Usually the same process-id is used throughout the entire network, but this is not required The process-id # can actually be any value from 1 to "very large integer“ The process-id # cannot be ZERO This is NOT the same as the AS# used in IGRP and EIGRP
- 40. 41 Configuring OSPF Areas After identifying the OSPF process, you need to identify the interfaces that you want to activate OSPF communications Lab_A#config t Lab_A(config)#router ospf 1 Lab_A(config-router)#network 10.0.0.0 0.255.255.255 area ? <0-4294967295> OSPF area ID as a decimal value A.B.C.D OSPF area ID in IP address format Lab_A(config-router)#network 10.0.0.0 0.255.255.255 area 0 • Every OSPF network must have an area 0 (the backbone area) to which other areas connect So in a multiple area network, there must be an area 0 The wildcard mask represents the set of hosts supported by the network and is really just the inverse of the subnet mask.
- 41. 42 OSPF Configuration • OSPF Process ID number is irrelevant. It can be the same on every router on the network • The arguments of the network command are the network number (10.0.0.0) and the wildcard mask (0.255.255.255) • Wildcards - A 0 octet in the wildcard mask indicates that the corresponding octet in the network must match exactly • A 255 indicates that you don’t care what the corresponding octet is in the network number • A network and wildcard mask combination of 1.1.1.1 0.0.0.0 would match 1.1.1.1 only, and nothing else. • The network and wildcard mask combination of 1.1.0.0 0.0.255.255 would match anything in the range 1.1.0.0–1.1.255.255
- 42. 43 OSPF Configuration -1 R2 R1 R3 S0 S1 E0 S0 E0 S0 10.0.0.1 20.0.0.1 20.0.0.2 30.0.0.1 30.0.0.2 40.0.0.1 10.0.0.2 40.0.0.2 A B
- 43. 44 OSPF Configuration -1 R2 R1 R3 S0 S1 E0 S0 E0 S0 10.0.0.1 20.0.0.1 20.0.0.2 30.0.0.1 30.0.0.2 40.0.0.1 10.0.0.2 40.0.0.2 R1#config t Enter configuration commands, one per line. End with CNTL/Z. R1(config)#router ospf 1 R1(config-router)#network 10.0.0.0 0.255.255.255 area 0 R1(config-router)#network 20.0.0.0 0.255.255.255 area 0 R1(config-router)#^Z A B
- 44. 45 OSPF Configuration -2 R2 R1 R3 S0 S1 E0 S0 E0 S0 200.0.0.16/28 200.0.0.8/30 200.0.0.12/30 200.0.0.32/27 A B
- 45. 46 OSPF Configuration -2 R2 R1 R3 S0 S1 E0 S0 E0 S0 200.0.0.17 200.0.0.9 200.0.0.10 200.0.0.13 200.0.0.14 200.0.0.33 200.0.0.18 200.0.0.34255.255.255.240 255.255.255.252 255.255.255.252 255.255.255.224 A B
- 46. 47 OSPF Configuration -2 R2 R1 R3 S0 S1 E0 S0 E0 S0 200.0.0.17 200.0.0.9 200.0.0.10 200.0.0.13 200.0.0.14 200.0.0.33 200.0.0.18 200.0.0.34255.255.255.240 255.255.255.252 255.255.255.252 255.255.255.224 R1#config t Enter configuration commands, one per line. End with CNTL/Z. R1(config)#router ospf 1 R1(config-router)#network 200.0.0.16 0.0.0.15 area 0 R1(config-router)#network 200.0.0. 8 0.0.0.3 area 0 R1(config-router)#^Z A B R3#config t Enter configuration commands, one per line. End with CNTL/Z. R3(config)#router ospf 1 R3(config-router)#network 200.0.0. 32 0.0.0.31 area 0 R3(config-router)#network 200.0.0. 12 0.0.0.3 area 0 R3(config-router)#^Z
- 47. 48 OSPF and Loopback Interfaces Configuring loopback interfaces when using the OSPF routing protocol is important Cisco suggests using them whenever you configure OSPF on a router Loopback interfaces are logical interfaces, which are virtual, software-only interfaces; they are not real router interfaces Using loopback interfaces with your OSPF configuration ensures that an interface is always active for OSPF processes. The highest IP address on a router will become that router’s RID The RID is used to advertise the routes as well as elect the DR and BDR. If you configure serial interface of your router with highest IP Address this Address becomes RID of t is the RID of the router because e router If this interface goes down, then a re-election must occur It can have an big impact when the above link is flapping
- 48. 49 Configuring Loopback Interfaces R1#config t Enter configuration commands, one per line. End with CNTL/Z. R1(config)#int loopback 0 R1(config-if)#ip address 172.16.10.1 255.255.255.255 R1(config-if)#no shut R1(config-if)#^Z R1#
- 49. 50 show ip protocolsshow ip protocols Router# • Verifies the configured IP routing protocol processes, parameters and statistics Verifying OSPF Operation show ip route ospfshow ip route ospf Router# • Displays all OSPF routes learned by the router show ip ospf interfaceshow ip ospf interface Router# • Displays the OSPF router ID, area ID and adjacency information
- 50. 51 show ip ospfshow ip ospf Router# • Displays the OSPF router ID, timers, and statistics Verifying OSPF Operation (Cont.) show ip ospf neighbor [detail]show ip ospf neighbor [detail] Router# • Displays information about the OSPF neighbors, including Designated Router (DR) and Backup Designated Router (BDR) information on broadcast networks
- 51. 52 The show ip route ospf Command RouterA# show ip route ospf Codes: C - connected, S - static, I - IGRP, R - RIP, M - mobile, B - BGP, D - EIGRP, EX - EIGRP external, O - OSPF, IA - OSPF inter area, E1 - OSPF external type 1, E2 - OSPF external type 2, E - EGP, i - IS-IS, L1 - IS-IS level-1, L2 - IS-IS level-2, * - candidate default Gateway of last resort is not set 10.0.0.0 255.255.255.0 is subnetted, 2 subnets O 10.2.1.0 [110/10] via 10.64.0.2, 00:00:50, Ethernet0
- 52. 53 The show ip ospf interface Command RouterA# show ip ospf interface e0 Ethernet0 is up, line protocol is up Internet Address 10.64.0.1/24, Area 0 Process ID 1, Router ID 10.64.0.1, Network Type BROADCAST, Cost: 10 Transmit Delay is 1 sec, State DROTHER, Priority 1 Designated Router (ID) 10.64.0.2, Interface address 10.64.0.2 Backup Designated router (ID) 10.64.0.1, Interface address 10.64.0.1 Timer intervals configured, Hello 10, Dead 40, Wait 40, Retransmit 5 Hello due in 00:00:04 Neighbor Count is 1, Adjacent neighbor count is 1 Adjacent with neighbor 10.64.0.2 (Designated Router) Suppress hello for 0 neighbor(s)
- 53. 54 The show ip ospf neighbor Command RouterB# show ip ospf neighbor Neighbor ID Pri State Dead Time Address Interface 10.64.1.1 1 FULL/BDR 00:00:31 10.64.1.1 Ethernet0 10.2.1.1 1 FULL/- 00:00:38 10.2.1.1 Serial0
- 54. 55 show ip ospf neighbor detail show ip ospf database
- 55. 56 Setting Priority for DR Election ip ospf priority numberip ospf priority number This interface configuration command assigns the OSPF priority to an interface. Different interfaces on a router may be assigned different values. The default priority is 1. The range is from 0 to 255. 0 means the router is a DROTHER; it can’t be the DR or BDR. Router(config-if)#
- 56. 57
- 57. 58 EIGRP • IGRP – DV – Easy to configure – Neighbor – Advanced Metric – Periodic – Broadcast • OSPF – LS – Incremental Updates – Multicast – Open Standard • EIGRP – Hybrid – DUAL – Topology Database – Rapid Convergence – Reliable
- 58. 59 Overview Enhanced Interior Gateway Routing Protocol (EIGRP) is a Cisco- proprietary routing protocol based on Interior Gateway Routing Protocol (IGRP). Released in 1994, Unlike IGRP, which is a classful routing protocol, EIGRP supports CIDR and VLSM. it is probably one of the two most popular routing protocols in use today. Compared to IGRP, EIGRP boasts faster convergence times, improved scalability, and superior handling of routing loops. EIGRP is often described as a hybrid routing protocol, offering the best of distance vector and link-state algorithms.
- 59. 60 Comparing EIGRP with IGRP IGRP and EIGRP are compatible with each other. EIGRP offers multiprotocol support, but IGRP does not. Communication via Reliable Transport Protocol (RTP) Best path selection via Diffusing Update Algorithm (DUAL) Improved convergence time Reduced network overhead
- 60. Introducing EIGRP EIGRP supports: Rapid convergence Reduced bandwidth usage Multiple network-layer protocols
- 61. 62 EIGRP Tables • EIGRP maintains 3 tables – Neighbor table – Topology table – Routing table
- 62. 63 Neighbor Discovery There are three conditions that must be met for neighborship establishment Hello or ACK received AS numbers match Identical metrics (K values) Hello ? AS ? K K1 – BW K2- Delay K3-Load K3-Reliability K5-MTU
- 63. 64 The metrics used by EIGRP in making routing decisions are (lower the metric the better): bandwidth delay load Reliability MTU By default, EIGRP uses only: Bandwidth Delay Analogies: Think of bandwidth as the width of the pipe and delay as the length of the pipe. Bandwidth is the carrying capacity Delay is the end-to-end travel time. Metric Calculation
- 64. 65 Neighbor Table The neighbor table is the most important table in EIGRP Stores address and interface of neighbor
- 65. 66 Topology Table Give me information about all routes Network
- 66. 67 Topology Table The topology table is made up of all the EIGRP routing tables in the autonomous system. DUAL takes the information and calculates the lowest cost routes to each destination. By tracking this information, EIGRP routers can identify and switch to alternate routes quickly. The information that the router learns from the DUAL is used to determine the successor route, which is the term used to identify the primary or best route. Every EIGRP router maintains a topology table. All learned routes to a destination are maintained in the topology table.
- 67. 68 Routing Tables A successor is a route selected as the primary route to use to reach a destination. DUAL calculates Successor (Primary Route) and places it in the routing table (and topology table) Can have up to 4 successors of equal or unequal value DUAL calculates Feasible Successor (Backup Route) and places it in the Topology Table. Promoted to successor if the route goes down if it has a lower cost than current successor If no FS in Table - Send query Multiple feasible successors for a destination can be retained in the topology table although it is not mandatory
- 68. 69 EIGRP Concepts & Terminology EIGRP routers that belong to different autonomous systems (ASes) don’t automatically share routing information The only time EIGRP advertises its entire routing table is when it discovers a new neighbor and forms an adjacency with it through the exchange of Hello packets When this happens, both neighbors advertise their entire routing tables to one another After each has learned its neighbor’s routes, only changes to the routing table are propagated
- 69. 70 172.16.100.0 1.544Mbps 56Kbp s 1.544Mbps Dist to 172.16.100.0 =100Dist to 172.16.100.0 =100 Dist to 172.16.100.0 =350 10Mbp s 10Mbps – 100 1,544Mbps – 250 56Kbps -1000 Chennai receives an update from Mumbai with a cost of 100, which is Mumbai's cost to reach 172.16.100.0, This cost is referred to as the reported distance (RD) Bangalore will report its cost to reach 172.16.100.0. Bangalore's RD is 350 Chennai will compute its cost to reach 172.16.100.0 via Mumbai and Bangalore and compare the metrics for the two paths Chennai's cost via Mumbai is 1100. Chennai's cost via Bangalore is 600. The lowest cost to reach a destination is referred to as the feasible distance (FD) for that destination Chennai's FD to 172.16.100.0 is 600. The next-hop router in the lowest-cost path to the destination is referred to as the successor. A feasible successor is a path whose reported distance is less than the feasible distance, and it is considered a backup route.
- 70. 71 EIGRP Terms Feasible distance (FD) - This is the lowest calculated metric to reach destination. This is the route that you will find in the routing table, because it is considered the best path Reported distance (RD) - The distance reported by an adjacent neighbor to a specific destination. Interface information - The interface through which the destination can be reached. Route status - The status of a route. Routes are identified as being either passive, which means that the route is stable and ready for use, or active, which means that the route is in the process of being recomputed by DUAL
- 71. 72 Successor – Current Route A successor is a route selected as the primary route to use to reach a destination. Successors are the entries kept in the routing table. Feasible Successor - A backup route A feasible successor is a backup route. These routes are selected at the same time the successors are identified, but they are kept in the topology table. Multiple feasible successors for a destination can be retained in the topology table. EIGRP Terminology and Operations
- 72. 73 Reliable Transport Protocol (RTP) Used by EIGRP for its routing updates in place of TCP EIGRP can call on RTP to provide reliable or unreliable service EIGRP uses reliable service for route updates Unreliable for Hellos Reliable Transport Protocol (RTP) is a transport layer protocol that guarantees ordered delivery of EIGRP packets to all neighbors. On an IP network, hosts use TCP to sequence packets and ensure their timely delivery. RIP uses UDP However, EIGRP is protocol-independent and does not rely on TCP/IP to exchange routing information the way that RIP, IGRP, and OSPF do. EIGRP uses RTP as its own proprietary transport layer protocol to guarantee delivery of routing information. With RTP, EIGRP can multicast and unicast to different peers simultaneously.
- 73. 74 Diffusing Update Algorithm (DUAL) All route computations in EIGRP are handled by DUAL One of DUAL's tasks is maintaining a table of loop-free paths to every destination. This table is referred to as the topology table DUAL saves all paths in the topology table The least-cost path(s) is copied from the topology table to the routing table In the event of a failure, the topology table allows for very quick convergence if another loop-free path is available If a loop-free path is not found in the topology table, a route recomputation must occur DUAL queries its neighbors, who, in turn, may query their neighbors, and so on... Hence the name "Diffusing" Update Algorithm
- 74. 75 VLSM Support • EIGRP supports the use of Variable- Length Subnet Masks • Can use 30-bit subnet masks for point-to-point networks • Because the subnet mask is propagated with every route update, EIGRP also supports the use of discontiguous subnets • Discontiguous network is the one that has two or more subnetworks of a classful network connected together by different classful networks
- 76. Configuring EIGRP outer(config-router)#network network-number • Selects participating attached networks Router(config)#router eigrp autonomous-system • Defines EIGRP as the IP routing protocol
- 78. 80 EIGRP Configuration R2 R1 R3 S0 S1 E0 S0 E0 S0 200.0.0.17 200.0.0.9 200.0.0.10 200.0.0.13 200.0.0.14 200.0.0.33 200.0.0.18 200.0.0.34255.255.255.240 255.255.255.252 255.255.255.252 255.255.255.224 R1#config t Enter configuration commands, one per line. End with CNTL/Z. R1(config)#router eigrp 10 R1(config-router)#network 200.0.0.16 R1(config-router)#network 200.0.0. 8 R1(config-router)#^Z A B R3#config t Enter configuration commands, one per line. End with CNTL/Z. R3(config)#router eigrp 10 R3(config-router)#network 200.0.0. 32 R3(config-router)#network 200.0.0. 12 R3(config-router)#^Z
- 79. 81 Verifying the EIGRP Configuration To verify the EIGRP configuration a number of show and debug commands are available. These commands are shown on the next few slides.
- 80. 82 show ip eigrp topology show ip eigrp topology [active | pending | successors]
- 81. 83 show ip eigrp topology all-links show ip eigrp traffic
- 83. 85 TELNET Getting information about remote device Can connect to remote device and configure a device Password must be set R1(config)# line vty 0 4 Password cisco login
- 84. 86 © 2002, Cisco Systems, Inc. All rights reserved. 86 Discovering Neighbors on the Network
- 85. Cisco Discovery Protocol CDP is a proprietary utility that gives you a summary of directly connected switches, routers, and other Cisco devices. CDP discovers neighboring devices regardless of which protocol suite they are running. Runs on the Data link layer Physical media must support the Subnetwork Access Protocol (SNAP) encapsulation. Only give directly connected device By default enabled, you can enable or disable
- 86. Discovering Neighbors with CDP CDP runs on routers with Cisco IOS® software Release 10.3 or later and on Cisco switches. Show CDP ? Summary information includes: Device ID Local Interface Port ID Capabilities list Platform
- 87. 89 CDP CDP timer is how often CDP packets are transmitted to all active interfaces. Router(config)#cdp timer 90 CDP holdtime is the amount of time that the device will hold packets received from neighbor devices. Router(config)#cdp holdtime 240
- 88. 90 Using CDP
- 89. 91 Using the show cdp neighbors Command The show cdp neighbor command (sh cdp nei for short) delivers information about directly connected devices.
- 90. 92 CDP show cdp neighbor detail This command can be run on both routers and switches, and it displays detailed information about each device connected to the device
- 91. 93 Using the show cdp entry Command The show cdp entry * command displays the same information as the show cdp neighbor details command.
- 92. 94 Additional CDP Commands The show cdp traffic command displays information about interface traffic, including the number of CDP packets sent and received and the errors with CDP.
- 93. 95 CDP Commands To disable the CDP on particular interface use the "no cdp enable" command To disable CDP on the entire router use the "no cdp run" in global configuration mode.
- 94. 96 Summary Cisco Discovery Protocol is an information-gathering tool used by network administrators to get information about directly connected devices. CDP exchanges hardware and software device information with its directly connected CDP neighbors. You can enable or disable CDP on a router as a whole or on a port-by-port basis. The show cdp neighbors command displays information about a router’s CDP neighbors. The show cdp entry, show cdp traffic, and show cdp interface commands display detailed CDP information on a Cisco device.
- 95. 97
- 96. Manage IP traffic as network access grows Filter packets as they pass through the router Why Use Access Lists?
- 97. 99 What are ACLs? ACLs are lists of conditions that are applied to traffic traveling across a router's interface. These lists tell the router what types of packets to accept or deny. Acceptance and denial can be based on specified conditions. ACLs can be configured at the router to control access to a network or subnet. Some ACL decision points are source and destination addresses, protocols, and upper-layer port numbers.
- 98. 100 Reasons to Create ACLs The following are some of the primary reasons to create ACLs: Limit network traffic and increase network performance. Provide traffic flow control. Provide a basic level of security for network access. Decide which types of traffic are forwarded or blocked at the router interfaces For example: Permit e-mail traffic to be routed, but block all telnet traffic. If ACLs are not configured on the router, all packets passing through the router will be allowed onto all parts of the network.
- 99. 101 ACL’s Different access list for Telnet When configuring ISDN you need to use access list Implicit deny at bottom All restricted statements should be on first There are two types Standard Extended
- 100. 102 Network N1 N2 N3 N4 N5 N6 192.168.12.0 A B C 192.168.34.0 192.168.56.0 192.168.12.2 192.168.12.3
- 101. 103 IP Packet SRC IP Address DEST IP Address Protocol type SRC Port DEST Port The first 2 bytes in the TCP/UDP header are the source port number The next 2 bytes in the TCP/UDP header are the Destination port number
- 102. 104 Standard Checks source address Permits or denies entire protocol suite Extended Checks source and destination address Generally permits or denies specific protocols Types of Access Lists
- 103. How to Identify Access Lists Standard IP lists (1-99) test conditions of all IP packets from source addresses. Extended IP lists (100-199) test conditions of source and destination addresses, specific TCP/IP protocols, and destination ports. Standard IP lists (1300-1999) (expanded range). Extended IP lists (2000-2699) (expanded range).
- 104. 106 Standard ACLs The full syntax of the standard ACL command is: Router(config)#access-list access-list-number {deny | permit} source [source-wildcard ] The no form of this command is used to remove a standard ACL. This is the syntax: Router(config)#no access-list access-list-number Config# Access-list 1 deny 192.168.1.0 0.0.0.255 Config# access-list 1 permit any
- 105. 107 Wildcard Mask Access-list 99 permit 192.168.1.1 wildcard mask All 32 bits of an IP Address can be filtered Wildcard inverse mask 0=must match 1= ignore MASK (192.168.1.1) Matching IP 0.0.0.0 (host) 192.168.1.1 0.0.0.255 192.168.1.0-255 0.0.255.255 192.168.0-255.0-255 0.255.255.255 192.0-255.0-255.0-255 255.255.255.255 0-255.0-255.0-255.0-255 (any)
- 106. 108 The ANY and HOST keyword Access-list 1 permit 200.0.0.9 0.0.0.0 Or permit host 200.0.0.9 Access-list 1 permit 0.0.0.0 255.255.255.255 Or permit any
- 107. Testing Packets with Standard Access Lists
- 108. Outbound ACL Operation • If no access list statement matches, then discard the packet.
- 109. 111 Reading an ACL First Hit or Best Fit? 1. Access-list 99 deny host 192.168.1.1 0.0.0.0 access-list 99 permit any 255.255.255.255 2. Access-list 99 permit 192.168.1.0 0.0.0.255 Access-list 99 deny host 192.168.1.1 access-list 99 permit any 3. Access-list 99 deny host 192.168.1.1 Implicit deny at the end of every ACL
- 110. 112 Creating ACLs ACLs are created in the global configuration mode. There are many different types of ACLs including standard, extended, IPX, AppleTalk, and others. When configuring ACLs on a router, each ACL must be uniquely identified by assigning a number to it. This number identifies the type of access list created and must fall within the specific range of numbers that is valid for that type of list. Since IP is by far the most popular routed protocol, addition ACL numbers have been added to newer router IOSs. Standard IP: 1300-1999 Extended IP: 2000- 2699
- 111. 113 The ip access-group command { in | out }
- 112. 114 Exercise – Standard Access List A B Account should be denied access to Sales To steps to configure •Create a standard Access list •Apply ACL to proper interface inbound or outbound S0 S0 E0 E0 192.168.0.18 255.255.255.248 S0 S1192.168.0.17 255.255.255.248 192.168.0.5 255.255.255.252 192.168.0.6 255.255.255.252 192.168.0.9 255.255.255.252 192.168.0.10 255.255.255.252 192.168.0.33 255.255.255.240 192.168.0.34 255.255.255.240
- 113. 115 Exercise – Standard Access List A B S0 S0 E0 E0 192.168.0.18 255.255.255.248 S0 S1192.168.0.17 255.255.255.248 192.168.0.5 255.255.255.252 192.168.0.6 255.255.255.252 192.168.0.9 255.255.255.252 192.168.0.10 255.255.255.252 192.168.0.33 255.255.255.240 192.168.0.34 255.255.255.240 Config# Access-list 1 deny 192.168.0.18 0.0.0.7 Config# access-list 1 permit any Config#int e 0 Config-if# ip access-group 1 out
- 114. 116 Extended ACLs Extended ACLs are used more often than standard ACLs because they provide a greater range of control. Extended ACLs check the source and destination packet addresses as well as being able to check for protocols and port numbers. At the end of the extended ACL statement, additional precision is gained from a field that specifies the optional Transmission Control Protocol (TCP) or User Datagram Protocol (UDP) port number. Logical operations may be specified such as, equal (eq), not equal (neq), greater than (gt), and less than (lt), that the extended ACL will perform on specific protocols. Extended ACLs use an access-list-number in the range 100 to 199 (also from 2000 to 2699 in recent IOS).
- 115. 117 Configuration • Access-list acl# {permit/Deny} • Protocol • Src IP src WCM • Dst IP dst WCM • Opetrator port • Protocol – OSPF – EIGRP – ICMP – TCP – UDP RP If you need to Block a routing protocol IP • Operator – eq – gt – lt – neq
- 116. Testing Packets with Extended Access Lists
- 118. 121 Extended ACL LAB -2 S0 S0 E0 E0 A B 192.168.0.34 should be denied FTP of 192.168.0.18 On Router R1 Config# Access-list 100 deny tcp 192.168.0.34 0.0.0.0 192.168.0.18 0.0.0.0 eq 21 Config# access-list 100 permit IP any any Config#int s0 Config-if# ip access-group 100 IN 192.168.0.18 should be denied website of 192.168.0.34 On Router R3 Config# Access-list 100 deny tcp 192.168. 0.18 0.0.0.0 192.168.0.34 0.0.0.0 eq 80 Config# access-list 100 permit IP any any Config#int s0 Config-if# ip access-group 100 IN S1 S0 192.168.0.18 255.255.255.248 192.168.0.17 255.255.255.248 192.168.0.5 255.255.255.252 192.168.0.6 255.255.255.252 192.168.0.9 255.255.255.252 192.168.0.10 255.255.255.252 192.168.0.33 255.255.255.240 192.168.0.34 255.255.255.240
- 119. 122 Deny FTP access-list 101 deny tcp any any eq 21 access-list 101 permit ip any any or access-list 101 deny tcp any any eq ftp access-list 101 permit ip any any
- 120. 123 Rules For extended access list apply near to the source For standard access list apply near to the destination
- 121. 124 Named ACLs IP named ACLs were introduced in Cisco IOS Software Release 11.2, allowing standard and extended ACLs to be given names instead of numbers. The characteristics of named accesslist: Identify an ACL using an alphanumeric name. You can delete individual statements in a named access list Named access lists must be specified as standard or extended You can use the ip access-list command to create named access lists. Named ACLs are not compatible with Cisco IOS releases prior to Release 11.2. The same name may not be used for multiple ACLs.
- 122. 125 Named ACL’s Numbered Access list did not give you any hint, What is filtered Named ACL’s are both basic and advanced filtering tool Name cannot start with a number or ! Cannot have space in the name Should not have ? Character anywhere in the name Name is case sensitive
- 123. 126 Named ACL Example R1(config)#ip access-list standard blocksales • R1(config-std-nacl)#deny 172.16.40.0 0.0.0.255 • R1(config-std-nacl)#permit any • R1(config-std-nacl)#exit • R1(config)#^Z • R1# #Int e 0 #Ip access-group blocksales out
- 125. 128 Basic Rules for ACLs Standard IP access lists should be applied closest to the destination. Extended IP access lists should be applied closest to the source. Use the inbound or outbound interface reference as if looking at the port from inside the router. Statements are processed sequentially from the top of list to the bottom until a match is found, if no match is found then the packet is denied. There is an implicit deny at the end of all access lists. This will not appear in the configuration listing. Access list entries should filter in the order from specific to general. Specific hosts should be denied first, and groups or general filters should come last. Never work with an access list that is actively applied. New lines are always added to the end of the access list. A no access-list x command will remove the whole list. It is not possible to selectively add and remove lines with numbered ACLs. Outbound filters do not affect traffic originating from the local router.
Hinweis der Redaktion
- DV- the router D will tell C that I know network X, and C will tell B that I know network X and so on, route A does not know anything beyond its neighbor, so its routing by tumor. This also uses periodic update, it also sends the entire routing table, these protocls are based in the early days of internet and some of them are class based. Link state gives much more information, here the link is defined with its interface, IP address, Mask, the type of network its on and its neighbors SO Router A will tell My IP…. This information is passed to router to router and maintain two databases. The topology table is important and its because of topology table the robustness comes. The topology table contains Link state advertisements and the router knows the network topology, any network fails the convergence is faster.
- DV will send entire routing table will waste the bandwidth. Link states exchange updates about only Link states Suitable for very large networks
- Draw diagram to explain router ID
- If the two routers are the only routers on the network, an adjacency should form. If there are more than two routers on the network, adjacencies only form with the designated router (DR) and backup designated router (BDR). If the two routers have already formed adjacencies with the DR and the BDR, they cannot form adjacencies with each other
- Backbone Router: Has an interface connected to the backbone (Area 0). Area Border Router (ABR): Has interfaces in multiple areas with at lest one interface in area 0. Connects other areas to the backbone and maintains routing information for each connected area. Autonomous System Boundary Router (ASBR): Router located between OSPF autonomous system and a non-OSPF network. Used to redistribute routing information between networks. Must reside in a non-stub area.
- OSPF routers and links are grouped logically into areas that are identified by assigned numbers. All OSPF networks have at least one area with the default being area 0. If more than one area exists, area 0 is defined as the backbone area and is used to connect all other areas. Each area has its own link state databases.
- Area 0 should not have more than 30 routers
- In order to ensure that a router will become the OSPF DR for any given segment, there are a number of options. One way is to manually configure the interface priority as described in option A above using the "ip ospf priority" interface configuration command. The second method is described in option C. OSPF routers will always use the loopback interface IP address as the router ID, when configured, and the router with the highest IP address will be chosen as the DR when the priorities are the same. The final method is to change the priority of the other routers in the segment to zero. When the OSPF priority is set to 0, the router is ineligible to become the DR or the BDR. Important Note: The OSPF DR/BDR election process is not pre-emptive, so any changes to the network regarding the DR/BDR election process will only occur when the routers are restarted.
- When the OSPF process starts, the Cisco IOS uses the highest local active IP address as its OSPF router ID. If there is no active interface, the OSPF process will not start. If the active interface goes down, the OSPF process has no router ID and therefore ceases to function until the interface comes up again.
- EIGRP scales the metric of IGRP by a factor of 256. That is because EIGRP uses a metric that is 32 bits long, and IGRP uses a 24-bit metric. EIGRP can multiply or divide by 256 to easily exchange information with IGRP
- Purpose : The figure introduces the IGRP routing protocol. IGRP is a sophisticated distance vector routing protocol. Emphasize: The Interior Gateway Routing Protocol (IGRP) is a dynamic distance-vector routing protocol designed by Cisco in the mid-1980s for routing in an autonomous system that contains large, arbitrarily complex networks with diverse bandwidth and delay characteristics. Historically, IGRP became one of the success factors for the early Cisco IOS software capabilities because of its superiority to RIP version 1. The important IGRP characteristics are as follows: More scalability than RIP Fast response to network changes Sophisticated metric Multiple-path support
- EIGRP Metrics Another really sweet thing about EIGRP is that unlike many other protocols that use a single factor to compare routes and select the best possible path, EIGRP can use a combination of four: Bandwidth Delay Load Reliability
- EIGRP routers that belong to different autonomous systems (ASes) don’t automatically share routing information and they don’t become neighbors. This behavior can be a real benefit when used in larger networks to reduce the amount of route information propagated through a specific AS. The only catch is that you might have to take care of redistribution between the different ASes manually. The only time EIGRP advertises its entire routing table is when it discovers a new neighbor and forms an adjacency with it through the exchange of Hello packets. When this happens, both neighbors advertise their entire routing tables to one another. After each has learned its neighbor’s routes, only changes to the routing table are propagated from then on. When EIGRP routers receive their neighbors’ updates, they store them in a local topology table. This table contains all known routes from all known neighbors, and serves as the raw material from which the best routes are selected and placed into the routing table. EIGRP routers keep route and topology information readily available in RAM, so they can react quickly to changes. Like OSPF, EIGRP saves this information in several tables and databases.
- Route source - The identification number of the router that originally advertised that route. This field is populated only for routes learned externally from the EIGRP network.
- Reliable Transport Protocol The EIGRP transport mechanism uses a mix of multicast and unicast packets, using reliable delivery when necessary. All transmissions use IP with the protocol type field set to 88. The IP multicast address used is 224.0.0.10. DUAL requires guaranteed and sequenced delivery for some transmissions. This is achieved using acknowledgments and sequence numbers. So, for example, update packets (containing routing table data) are delivered reliably (with sequence numbers) to all neighbors using multicast. Acknowledgment packets-- with the correct sequence number--are expected from every neighbor. If the correct acknowledgment number is not received from a neighbor, the update is retransmitted as a unicast. The sequence number (seq num) in the last packet from the neighbor is recorded to ensure that packets are received in sequence. The number of packets in the queue that might need retransmission is shown as a queue count (QCnt), and the smoothed round trip time (SRTT) is used to estimate how long to wait before retransmitting to the neighbor. The retransmission timeout (RTO) is the time the router will wait for an acknowledgment before retransmitting the packet in the queue. Some transmissions do not require reliable delivery. For example, hello packets are multicast to all neighbors on an Ethernet segment, whereas acknowledgments are unicast. Neither hellos nor acknowledgments are sent reliably. EIGRP also uses queries and replies as part of DUAL. Queries are multicast or unicast using reliable delivery, whereas replies are always reliably unicast. Query and reply packets are discussed in more detail in the next section.
- All route computations in EIGRP are handled by DUAL. One of DUAL's tasks is maintaining a table of loop-free paths to every destination. This table is referred to as the topology table . Unlike traditional DV protocols that save only the best (least-cost) path for every destination, DUAL saves all paths in the topology table. The least-cost path(s) is copied from the topology table to the routing table. In the event of a failure, the topology table allows for very quick convergence if another loop-free path is available. If a loop-free path is not found in the topology table, a route recomputation must occur, during which DUAL queries its neighbors, who, in turn, may query their neighbors, and so on... hence the name "Diffusing" Update Algorithm.
- Slide 1 of 2 Purpose: This figure explains how to use the router igrp and network commands to configure an IGRP process. Emphasize: Note that the AS keyword is required for IGRP. You can use multiple network commands to specify all networks that are to participate in the IGRP process. Only those networks specified will be published to other routers.
- Purpose: The figure shows how the IGRP commands operate on the example network. Emphasize : An administrator only specifies directly connected networks that should be published to other routers. Without the network command, nothing is advertised. With a network command, the router will advertise every subnet within the Class A, B, or C network specified in the configuration.
- # Show users – will show connected users # Clear line 1 – will disconnect the session on line 1
- Purpose: This chapter introduces the Cisco IOS™ CLI on the Catalyst® 1900 switch and router. Timing: This chapter should take about 2 hours to present. Note: The Catalyst 1900 switch only has a subset of the router Cisco IOS commands available. Contents: Introduction to Cisco IOS. Explain to the student what is IOS? Cisco Device startup procedures in general. IOS configuration source. General introduction to the IOS CLI . Cat 1900 switch startup procedures. Intro to Cat 1900 CLI. This part covers the basic configuration on the switch, like setting the IP address and hostname. More details about the various Cat 1900 switch configuration commands are explained in Chapter 6 and 7. Router startup procedures. More details on the router startup process is discussed in chapter 5. Router IOS CLI.
- Note: CDP is sent using multicast frames with the MAC address 0100.0ccc.cccc. CDP is a Cisco proprietary data link layer protocol that operates over any medium that supports the Subnetwork Access Protocol (SNAP) encapsulation (LANs, most WANs, and ATM). It is important to understand that because CDP operates at Layer 2 (data link layer of the OSI model), it functions independently of the Layer 3 (network) protocol (IP or IPX). CDP is on by default, but it can be disabled. In many cases, CDP is disabled on dial backup links, such as ISDN, so as to not keep the link up constantly. CDP – One dependency, the media type at the physical layer must support SNAP. SNAP was created because all protocols does not work well for 802.3 Ethernet frame as 802.3 had no type filed any longer. The original Ethernet had type filed, But the 802.3 had replaced this with length field, so When we bring SNAP at layer 2 it brings back type field. Frame relay, Ethernet, ATM, Token ring all support SNAP
- Device ID. The hostname of the neighboring device Local Interface. The interface on which this router received information about the neighboring device. Holdtime. The amount of time the router will store this information before dropping it from memory, if additional CDP packets are not received. Capability. The type of device that announced itself using CDP. Platform. The hardware platform of the neighboring equipment. Port ID. The port from which the CDP packet was sent on the neighboring device. Emphasize: CDP is media- and protocol-independent and runs on all Cisco-manufactured equipment including routers, access servers, switches, and some managed hubs. With CDP, network management applications can retrieve the device type and SNMP agent address of neighboring devices. This capability enables applications to send SNMP queries to neighboring devices. CDP allows network management applications to dynamically discover Cisco devices that are neighbors. CDP runs on all media that support the Subnetwork Access Protocol, including LAN and Frame Relay. CDP runs over the data link layer only, not the network layer. Therefore, two systems that support different network-layer protocols can learn about each other. Cached CDP information is available to network management applications. Cisco devices never forward a CDP packet. When new information is received, old information is discarded. The holdtime determines how long to keep existing information from a neighbor.
- Note: Some of the CDP commands are not available on the Catalyst 1900 switch, like cdp run , show cdp traffic , and show cdp entry . It’s important to remember that CDP packets aren’t passed through a Ciscoswitch, and that you see only what’s directly attached. So this means that if your router is connected to a switch, you won’t see any of the devices hooked up to that switch.
- Emphasize: This graphic shows the show cdp neighbors command initiated from a router, which displays a summary of the capabilities and access details for the CDP neighbors. The show cdp neighbors detail command shows detailed information about the same devices. Note: If the neighbor is a Catalyst 1900 switch, the switch MAC address is also displayed. If the switch is a 2900xl, its MAC address is not displayed. Device ID. The hostname of the neighboring device Local Interface. The interface on which this router received information about the neighboring device. Holdtime. The amount of time the router will store this information before dropping it from memory, if additional CDP packets are not received. Capability. The neighbor’s capability, such as router, switch, or repeater. The capability codes are listed at the top of the command output. Platform. The hardware platform of the neighboring equipment.( Cisco 2509, Cisco 2511, and Catalyst 5000) Port ID. The port from which the CDP packet was sent on the neighboring device.
- Emphasize: The example shows what information can be obtained about RouterA’s neighbor. CDP is one way to learn about other Cisco devices on the network.
- Note: The holdtime indicates how long the neighbor information will be kept in the local CDP table.
- 181-37
- Purpose: This slide discuss the initial configurations on the routers and switches. Note: There is no setup mode on the Catalyst 1900 switch.
- Layer 2 of 2 Emphasize: An access list is a mechanism for identifying particular traffic. One application of an access list is for filtering traffic into or out of a router interface.
- Permission for router Manage IP Traffic Filter packet which pas thru Either can permit or Deny
- If u want to permit only one from a network then permit shud be first
- Layer 3 of 3 Purpose: Describe an inbound versus outbound access list on an interface.
- Layer 3 of 3 Emphasize: Layer 3—Adds the Novell IPX access lists covered in Chapter 11, “Configuring Novell IPX,” and the number ranges for these types of access lists. As of Release 11.2.4(F), IPX also supports named access lists. Point out that number ranges generally allow 100 different access lists per type of protocol. When a given hundred-number range designates a standard access list, the rule is that the next hundred-number range is for extended access lists for that protocol. Exceptions to the numbering classification scheme include AppleTalk and DECnet, where the same number range can identify various access list types. For the most part, number ranges do not overlap between different protocols. Note: With Cisco IOS 12.0, the IP access-lists range has been expanded to also include: <1300-1999> IP standard access list (expanded range) <2000-2699> IP extended access list (expanded range)
- Purpose: This graphic gives an overview of the type of TCP/IP packet tests that standard access lists can filter. It uses the encapsulation graphic and diamond decision graphic to remind students of material presented earlier in this course.
- Layer 3 of 3 Purpose: Shows a deny result of the access list test. Emphasize: Now the packet is discarded into the packet discard bucket. The unwanted packet has been denied access to the outbound interface. The Notify Sender message shows a process like ICMP, returning an “administratively prohibited” message back to the sender.
- Explain how the access list process, here there are three ACLS. Can give the example with a host IP address 192.168.1.1 and host 192.168.1.2 what happens on all the three ACLS
- Purpose: This graphic gives an overview of the type of TCP/IP packet tests that extended access lists can filter. It uses the encapsulation graphic and diamond decision graphic to remind students of material presented earlier in this course.
- Named access lists allow you to use names to both create and apply either standard or extended access lists. There is nothing new or different about these access lists aside from being able to refer to them in a way that makes sense to humans.
