4.1.1 areas of computer ethics
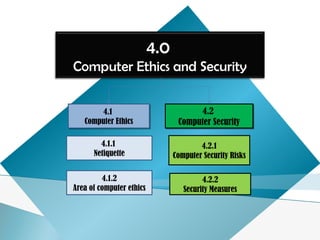
- 1. 4.0 Computer Ethics and Security 4.1 Computer Ethics 4.1 Computer Ethics 4.1.1 Netiquette 4.2 Computer Security 4.2 Computer Security 4.2.1 Computer Security Risks 4.2.2 Security Measures 4.1.2 Area of computer ethics
- 2. 4.1 Computer Ethics 4.1.1 Netiquette
- 3. At the end of this topic, students should be able to: ◦ Identify the rules of netiquette Learning Outcome
- 5. • Three areas where good netiquette is highly stressed are : 4.1.1 Netiquette
- 6. Rules of netiquette • Rules of netiquette on social interaction and communication electronically. 4.1.1 Netiquette
- 7. btw By the way imho In my humble opinion fyi For your information tyvm Thank You Very Much 4.1.1 Netiquette
- 8. :) smile :| Indifference :O Surprised :( Frown : Undecided 4.1.1 Netiquette
- 9. 6. Avoid forward chain letter. 8. Never access someone's private email. 9. Clearly identify a spoiler which is a message that reveals a solution to a game or ending to a movie or program. Rules of netiquette 4.1.1 Netiquette
- 10. Rules of netiquette 4.1.1 Netiquette
- 11. Summary What you have learned: • Definition of Netiquette. • Rules of Netiquette. 4.1.1 Netiquette
- 12. 1. Define netiquette. 2. What is the basic rule of netiquette? 3. Name two things you should remember about being online that are related to netiquette. 4. What is a flame war? 5. Why should you stay away from using all capital letters? 6. Why is it easy for there to be misunderstandings in online conversations? 7. What is an emoticon (smiley) and why would you use one? Give at least 2 examples and explain what they mean. 8. What should you do before forwarding personal emails to others? 9. List some items you think should be included in our college 's Internet Safety Tips. 10. List some items you think should be included in our college's Netiquette Rules. 4.1.1 Netiquette
- 13. 4.1 Computer Ethics 4.1.2 Area of Computer Ethics
- 14. At the end of this topic, students should be able to: ◦ Define computer ethics. ◦ Describe areas of computer ethics. Learning Outcome
- 15. Definition of computer ethicsDefinition of computer ethics • Moral guidelines that govern the use of computers and information systems Shelly Cashman • set of moral principles that regulate the use of computers http://www.techterms.com 4.1.2 Areas of computer Ethics
- 16. Areas of computer ethics:Areas of computer ethics: 1. Information accuracy 2. Green Computing 3. Codes of conduct 4. Intellectual Property Rights 5. Information Privacy 4.1.2 Areas of computer Ethics
- 17. 1. Information Accuracy1. Information Accuracy knowledge that is correct, or something that is true Information accuracy is a concern *** not all information on the web is correct 4.1.2 Areas of computer Ethics
- 18. 2. Green Computing:2. Green Computing: - Involving reducing the electricity and environmental waste while using a computer 4.1.2 Areas of computer Ethics
- 19. 3. Codes of conduct:3. Codes of conduct: - Written guideline that helps determine whether a specific computer action is ethical or unethical 4.1.2 Areas of computer Ethics
- 20. 4.1.2 Areas of computer Ethics
- 21. 4. Information Privacy:4. Information Privacy: • refer to the rights of individuals andrefer to the rights of individuals and companies to deny or restrict thecompanies to deny or restrict the collection and use of information aboutcollection and use of information about themthem 4.1.2 Areas of computer Ethics
- 22. 5. Intellectual Property5. Intellectual Property Unique and original works such as idea, inventions, art, writing, processes, company and product name, and logos. Refer to the creation of mind used in commerce 4.1.2 Areas of computer Ethics
- 23. Intellectual PropertyIntellectual Property PatentPatent TrademarkTrademark CopyrightCopyright Intellectual Property
- 24. is an exclusive right granted for an invention invention - a product or a process that provides a new way of doing something, or offers a new technical solution to a problem Example : the function and operation of Windows 7 Intellectual Property
- 25. • A distinctive sign which identifies certain goods or services Examples : LOGO SIGN SLOGAN Color DESIGN Connecting People Intellectual Property
- 26. A legal term describing rights given to creators for their literary and artistic works. literary works - novels, poems, plays, reference works, newspapers, computer programs, databases, films, musical compositions, and choreography artistic works - paintings, drawings, photographs, sculpture, architecture, advertisements, maps and technical drawings Intellectual Property Example : Licensed Windows 7
- 27. Importance of Intellectual Property To protect any original work that created by individual person/ company for example, image, drawing, lyric, publishing and so on. Preserve the features and processes that make things work. This lets inventors profit from their inventions. Intellectual Property
Hinweis der Redaktion
- Huge databases store data online It is important to safeguard your information
- Notes : Open Source is not a copyright because the software can be shared and develop together.