Ieee 2010 project titles
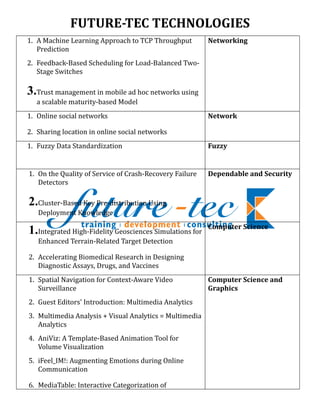
- 1. FUTURE-TEC TECHNOLOGIES 1. A Machine Learning Approach to TCP Throughput Networking Prediction 2. Feedback-Based Scheduling for Load-Balanced Two- Stage Switches 3.Trust management in mobile ad hoc networks using a scalable maturity-based Model 1. Online social networks Network 2. Sharing location in online social networks 1. Fuzzy Data Standardization Fuzzy 1. On the Quality of Service of Crash-Recovery Failure Dependable and Security Detectors 2.Cluster-Based Key Pre-distribution Using Deployment Knowledge Computer Science 1.Integrated High-Fidelity Geosciences Simulations for Enhanced Terrain-Related Target Detection 2. Accelerating Biomedical Research in Designing Diagnostic Assays, Drugs, and Vaccines 1. Spatial Navigation for Context-Aware Video Computer Science and Surveillance Graphics 2. Guest Editors' Introduction: Multimedia Analytics 3. Multimedia Analysis + Visual Analytics = Multimedia Analytics 4. AniViz: A Template-Based Animation Tool for Volume Visualization 5. iFeel_IM!: Augmenting Emotions during Online Communication 6. MediaTable: Interactive Categorization of
- 2. Multimedia Collections 1. Classification of Protein-Protein Interaction Full-Text Computational Biology Documents Using Text and Citation Network and Bioinformatics Features 2. Exploring Species-Based Strategies for Gene Normalization 1. Automatic Generation of Game Level Solutions as Computational Storyboards Intelligence and AI in Games 2. Game Bot Detection via Avatar Trajectory Analysis 3. The Parametrized Probabilistic Finite-State Transducer Probe Game Player Fingerprint Model 1. Full-Reference Video Quality Metric for Fully Broadcasting Scalable and Mobile SVC Content 1. Understanding Wi-Fi 2.0: from the economical Wireless Communications perspective of wireless service providers [Dynamic Spectrum Management] 2. Efficient routing for international mobile call setup [Accepted from Open Call] 3. IEEE 802.11E QoS and power saving features overview and analysis of combined performance [Accepted from Open Call] 4. Achieving Secret Communication for Fast Rayleigh Fading Channels 1. Using a web-based tool to define and implement Software software process improvement initiatives in a small industrial setting 2. Including both static and dynamic typing in the same programming language 3. Design principles of web-based distance education system and sample application in Afyon Kocatepe University 4. Component co-evolution and component
- 3. dependency: speculations and verifications 5. Technologies and Tools for Distributed Teams 1. End-to-End Service Support for Mashups Service Computing 1. Privacy-Preserving Sharing of Sensitive Information Security and privacy 2. Preserving Privacy Based on Semantic Policy Tools 3. The Phish-Market Protocol: Secure Sharing Between Competitors 4. Can Public-Cloud Security Meet Its Unique Challenges? 5. Internet Filtering Issues and Challenges 6. Encrypting Keys Securely 1. Joint synchronization and localization using TOAs: A Communications linearization based WLS solution 1. Auto-Context and Its Application to High-Level Pattern Analysis and Vision Tasks and 3D Brain Image Segmentation Machine Intelligence 2. Cost-Sensitive Face Recognition 3. Motion Segmentation in the Presence of Outlying, Incomplete, or Corrupted Trajectories 4. P&D 5. FS2You: Peer-Assisted Semipersistent Online Hosting at a Large Scale 1. Improved Speech Presence Probabilities Using Signal HMM-Based Inference, With Applications to Speech Enhancement and ASR 1. Affective Visualization and Retrieval for Music Video Multimedia 2. Speech Emotion Analysis: Exploring the Role of Context 3. Feature Analysis and Evaluation for Automatic Emotion Identification in Speech
- 4. 4. Emotion Recognition in Text for 3-D Facial Expression Rendering 5. A 3-D Audio-Visual Corpus of Affective Communication 6. Accelerating the Media Business with MPEG Extensible Middleware 1. Classroom Wiki: A Collaborative Wiki for Learning Technologies Instructional Use with Multiagent Group Formation 2. An Interactive Table for Supporting Participation Balance in Face-to-Face Collaborative Learning 3. Automatic Detection of Off-Task Behaviors in Intelligent Tutoring Systems with Machine Learning Techniques 4. Improving Teaching and Learning through Automated Short-Answer Marking 1. Efficient Lazy Evaluation of Rule-Based Programs KDD 2. A Novel Combination of Answer Set Programming with Description Logics for the Semantic Web 3. Unsupervised Semantic Similarity Computation between Terms Using Web Documents 1. Web-Application Security: From Reactive to IT Proactive 2. Introduction: Cyber security 1. Trust and Reputation Management INTERNET COMPUTING 2. Trusted Cloud Computing with Secure Resources and Data Coloring 3. Advanced Feedback Management for Internet Auction Reputation Systems 4. A Survey of First-Person Shooter Gaming Traffic on the Internet 5. Incentive Mechanisms in P2P Media Streaming Systems
- 5. 6. Cloud Computing: The New Frontier of Internet Computing 7. Secure/Multipurpose Internet Mail Extensions 8. Trust and the Internet 1. Intrusion Detection for Grid and Cloud Computing IT PROFESSIONAL 2. A Framework for RFID Deployment in Supply Chains 1. Special Section on Distributed Camera Networks: Image Processing Sensing, Processing, Communication, and Implementation 2. 3-D Target-Based Distributed Smart Camera Network Localization 3. Activity Based Matching in Distributed Camera Networks 1. A managerial community of Web Services for WEB SERVICES management of communities of Web Services 2. Automatic Composition of Semantic Web Services An Enhanced State Space Search Approach 3. Knowledge-first web services an E-Government example 4. Using the iPhone and iPod Touch for remote sensor control and data acquisition 1. The Applied Research of Cloud Computing Platform Cloud Computing Architecture in the E-Learning Area. 2. Cloud Computing System Based on Trusted Computing Platform. 3. IT Auditing to Assure a Secure Cloud Computing. 4. Performance Evaluation of Cloud Computing Offerings 5. Providing Privacy Preserving in cloud computing 6. Toward a Unified Ontology of Cloud Computing.
- 6. Bayesian classifier programmed in SQL Secured Data Collection Gene ontology with word computing with SOM MILD Edge Adaptive image stenography by MSB Multibody Structure-and-Motion Segmentation by Branch- and-Bound Model Selection Satellite Image Contrast Enhancement Using Discrete Wavelet Transform and Singular Value Decomposition Skew Estimation of Document Images Using Bagging Fast-Mesh: A Low-Delay High-Bandwidth Mesh for Peer- to-Peer Live Streaming A Stochastic Approach to Image Retrieval Using Relevance Feedback and Particle Swarm Optimization A Virtual Cloud Computing LAB Predictive Network Anomaly detection and visualization Active Re-ranking for Web Image Search Facial detection and recognition in mimetic algorithm Accurate image search using contextual dissimilarity measures Light:A query efficient yet low maintenance indexing scheme over dth's Anonymous query processing in road networks The applied research of cloud computing arch in area of e- learning Routing Understanding online interruption based advertising impact Aging Bloom Filter with Two Active Buffers for Dynamic Sets
- 7. Layered Approach Using Conditional Random Fields for Intrusion Detection For details: ASHADAS.P.K / SARANYA Mob: 9566216611 / 33 asha@future-tec.co.in / sharanya@future-tec.co.in www.future-tec.co.in Old 52,New 62,Floor 3,Espee Complex Brindavan Street,West Mambalam,Chennai 33
