Android pen test Checklist
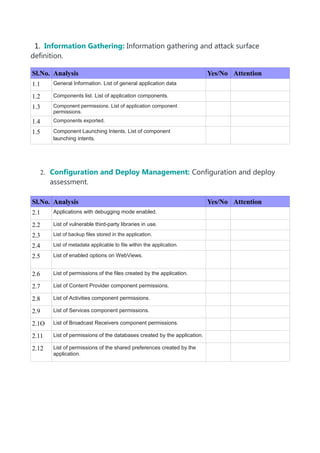
- 1. 1. Information Gathering: Information gathering and attack surface definition. Sl.No. Analysis Yes/No Attention 1.1 General Information. List of general application data 1.2 Components list. List of application components. 1.3 Component permissions. List of application component permissions. 1.4 Components exported. 1.5 Component Launching Intents. List of component launching intents. 2. Configuration and Deploy Management: Configuration and deploy assessment. Sl.No. Analysis Yes/No Attention 2.1 Applications with debugging mode enabled. 2.2 List of vulnerable third-party libraries in use. 2.3 List of backup files stored in the application. 2.4 List of metadata applicable to file within the application. 2.5 List of enabled options on WebViews. 2.6 List of permissions of the files created by the application. 2.7 List of Content Provider component permissions. 2.8 List of Activities component permissions. 2.9 List of Services component permissions. 2.1O List of Broadcast Receivers component permissions. 2.11 List of permissions of the databases created by the application. 2.12 List of permissions of the shared preferences created by the application.
- 2. 3. Authentication: Authentication assessment. Sl.No. Analysis Yes/No Attention 3.1 Login methods 3.2 Default Users and Passwords.List of default users and passwords stored by the application. 3.3 Weak Password Policy. Weaknesses related with the password robust policies. 3.4 Remember Credentials Functionality. Weaknesses related with credential storage through the remember functions. 4. Cryptography: Cryptography use assessment. Sl.No. Analysis Yes/No Attention 4.1 Hard-coded credentials.Passwords stored within the source code. 4.2 Insecure Data Storage.Weaknesses related with confidential information storage. 4.3 Insecure use of Transport Protocol. Weaknesses related with unsecure information flow. 4.4 Certificate Pinning. Weaknesses related with trusted chains of digital certifications. 5. Information Leak: Confidential information leak assessment. Sl.No. Analysis Yes/No Attention 3.1 Information Leak to log files. 3.2 Information Leak to SDCard. 3.3 Information Leak to Network 3.4 Information Leak to Android’s IPC
- 3. 6. Data Validation:User entry management assessment. Sl.No. Analysis Yes/No Attention 6.1 HTML code injection. 6.2 Buffer overflow. 6.3 Command injection in databases. 6.4 Path injection in file access. 6.5 Null parameter checking. 6.6 Log injection. 6.7 Injection Process Control via intent data. 7. Intent Spoofing: Intent reception management assessment. Sl.No. Analysis Yes/No Attention 7.1 Intent Spoofing on Broadcast components. 7.2 Arbitrary launch of Activities 7.3 Arbitrary launch of Services. 7.4 Weaknesses related with the insecure use of Pending Intents. 8. Unauthorized Intent Receipt: Intent resolution assessment. Sl.No. Analysis Yes/No Attention 8.1 Intent interception on Broadcast components. 8.2 Intent interception on Activity components. 8.3 Intent interception on Service components. 8.4 Pending Intent interception.
