Cyber Security - Flier
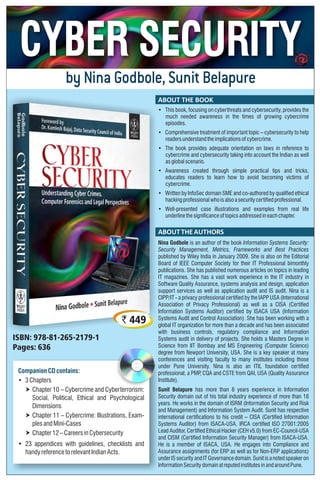
- 1. CompanionCDcontains: • 3Chapters † Chapter 10 – Cybercrime and Cyberterrorism: Social, Political, Ethical and Psychological Dimensions † Chapter 11 – Cybercrime: Illustrations, Exam- plesandMini-Cases † Chapter12–Careersin Cybersecurity • 23 appendices with guidelines, checklists and handyreferencetorelevantIndianActs. by Nina Godbole, Sunit Belapure ABOUT THE BOOK ABOUTTHEAUTHORS • This book, focusing on cyberthreats and cybersecurity, provides the much needed awareness in the times of growing cybercrime episodes. • Comprehensive treatment of important topic – cybersecurity to help readersunderstandtheimplicationsofcybercrime. • The book provides adequate orientation on laws in reference to cybercrime and cybersecurity taking into account the Indian as well asglobalscenario. • Awareness created through simple practical tips and tricks, educates readers to learn how to avoid becoming victims of cybercrime. • Written by InfoSec domain SME and co-authored by qualified ethical hackingprofessionalwhoisalsoasecuritycertifiedprofessional. • Well-presented case illustrations and examples from real life underlinethesignificanceoftopicsaddressedineachchapter. Nina Godbole is an author of the book Information Systems Security: Security Management, Metrics, Frameworks and Best Practices published by Wiley India in January 2009. She is also on the Editorial Board of IEEE Computer Society for their IT Professional bimonthly publications. She has published numerous articles on topics in leading IT magazines. She has a vast work experience in the IT industry in Software Quality Assurance, systems analysis and design, application support services as well as application audit and IS audit. Nina is a CIPP/IT - a privacy professional certified by the IAPP USA (International Association of Privacy Professional) as well as a CISA (Certified Information Systems Auditor) certified by ISACA USA (Information Systems Audit and Control Association). She has been working with a global IT organization for more than a decade and has been associated with business controls, regulatory compliance and Information Systems audit in delivery of projects. She holds a Masters Degree in Science from IIT Bombay and MS Engineering (Computer Science) degree from Newport University, USA. She is a key speaker at many conferences and visiting faculty to many institutes including those under Pune University. Nina is also an ITIL foundation certified professional, a PMP, CQA and CSTE from QAI, USA (Quality Assurance Institute). Sunit Belapure has more than 8 years experience in Information Security domain out of his total industry experience of more than 18 years. He works in the domain of ISRM (Information Security and Risk and Management) and Information System Audit. Sunit has respective international certifications to his credit – CISA (Certified Information Systems Auditor) from ISACA-USA, IRCA certified ISO 27001:2005 Lead Auditor, Certified Ethical Hacker (CEH v5.0) from EC-Council-USA and CISM (Certified Information Security Manager) from ISACA-USA. He is a member of ISACA, USA. He engages into Compliance and Assurance assignments (for ERP as well as for Non-ERP applications) underISsecurityand ITGovernancedomain.Sunit isanotedspeakeron InformationSecuritydomainatreputedinstitutesinandaroundPune. ISBN: 978-81-265-2179-1 Pages: 636 ` 449
- 2. HEAD OFFICE: 4435-36/7, Ansari Road, Daryaganj, New Delhi-110002. Tel: 91-11-43630000 Fax: 91-11-23275895. Email: csupport@wiley.com BANGALORE: Tel: 080-23132383. Telefax: 080-23124319. Email: blrsales@wiley.com MUMBAI: Tel: 022-27889263, 27889272. Telefax: 022-27889263. Email: mumsales@wiley.com www.wileyindia.com Wiley India Pvt. Ltd. KEY FEATURES TABLE OF CONTENTS Appendix Appendix Appendix Appendix Appendix Appendix Appendix Appendix Appendix Appendix Appendix Appendix Appendix K : L : M : N : O : P : Q : R : S : T : U : V : W : Virtual Crime Cybercrimes Worldwide – Trends and Patterns Data Privacy, Data Protection and Cybercrime Digital Rights Management The Indian Information Technology Act The Indian Penal Code The Indian Evidence Act The Indian Patents Act The Indian Trademarks Act The Indian Copyright Act DSCI Security Framework (DSF) from Data Security Council of India DSCI Privacy Framework (DPF) from Data Security Council of India Chapterwise List of All References B : C : E-Mail Security and Etiquettes and Policy Template for Computer and Network Usage D : Protection Checklist for Individuals and Organizations Template E : F : Guidelines for Computer Forensics Laboratory Set-up and Guidance on Forensic Readiness Activities in Organizations G : Preservation of Digital Crime Scene Related Photographs and Checklist for Processing Computer Forensic Data and Evidence H : I J : Appendix Appendix Appendix Appendix Appendix Appendix Appendix Appendix Appendix List of useful Software Utilities and Websites List of Tools : Vulnerability Scanning and Penetration Testing Guidance on Structuring the Incidence Response Handling Team : List of Forensic Equipment and Forensic Software Tools Cybercafe Due Diligence Questionnaire • AuthorsareindustryprofessionalswithextensiveexperienceinthedomainofInformation Security andDataPrivacy. • The book is aimed at individuals, students (including those doing law courses), IT professionals and legal professionals forbuildingawarenessaboutcybercrimeandcybersecurity. • Useful for candidates aspiring to appear for international certification exams in the domain of Information Security/IT Securityandotherrelateddomains. • Detailed discussion about multiple dimensions of cybersecurity – presents current scenario on cybercrime, serves as referencebookwithrichdiscussiononallrelevantaspectsofthedomain,including cyberforensics. • ProvidesinanutshellIndianaswellasglobalperspectiveoncyberlaws. • Bringstoreadersusefulappendiceswithrichcontentsthatserveassupplementarymaterialtothe chapters. • Understandingofkeyconceptsfacilitatedthroughwell-illustrateddiagrams,tablesandvignettes inside the chapters. • Real-lifecaseillustrationsandexamplesprovidedtohelpconsolidateunderstanding oftopicspresented in eachchapter. • Reviewquestionsandreferencematerialpointersaftereachchapter. Inside the Book Inside the CD Appendices 1 Introduction to Cybercrime 2 Cyberoffences: How Criminals Plan Them 3 Cybercrime: Mobile and Wireless Devices 4 Tools and Methods Used in Cybercrime 5 Phishing and Identity Theft 6 Cybercrime and Cybersecurity: The Legal Perspectives 7 Understanding Computer Forensics 8 Forensics of Hand-Held Devices 9 Cybersecurity: Organizational Implications 10 Cybercrime and Cyberterrorism: Social, Political, Ethical and Psychological Dimensions 11 Cybercrime: Illustrations, Examples and Mini-Cases 12 Careers in Cybersecurity A : Glossary of Cybersecurity Terms and Acronyms Appendix