Cloud Identity
•
0 gefällt mir•543 views
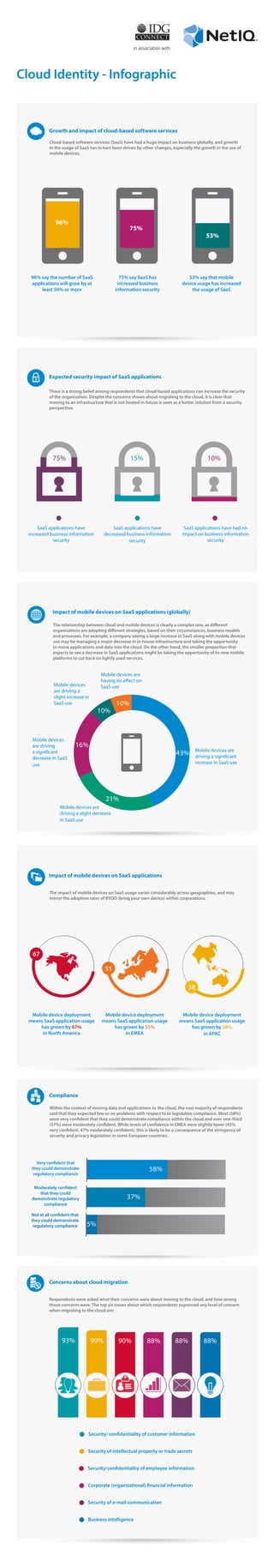
The findings of a recent survey, commissioned by NetIQ through IDG Connect, found that increased cloud-based software-as-a-service (SaaS) application use by businesses has led to more confidence amongIT decision-makers that corporate data is better secured now than it has been in the past.
Melden
Teilen
Melden
Teilen
Downloaden Sie, um offline zu lesen
Empfohlen
Empfohlen
Weitere ähnliche Inhalte
Was ist angesagt?
Was ist angesagt? (20)
Smarter Security - A Practical Guide to Doing More with Less

Smarter Security - A Practical Guide to Doing More with Less
Why Zero Trust Architecture Will Become the New Normal in 2021

Why Zero Trust Architecture Will Become the New Normal in 2021
Scale vp wisegate-investing-in_security_innovation_aug2014-gartner_catalyst

Scale vp wisegate-investing-in_security_innovation_aug2014-gartner_catalyst
Cybersercurity Resource Allocation & Efficacy Index: 2020 - 2021 Trends

Cybersercurity Resource Allocation & Efficacy Index: 2020 - 2021 Trends
Leveraging Identity to Manage Change and Complexity

Leveraging Identity to Manage Change and Complexity
What affects security program confidence? - may2014 - bill burns

What affects security program confidence? - may2014 - bill burns
Government and Education Webinar: Public Sector Cybersecurity Survey - What I...

Government and Education Webinar: Public Sector Cybersecurity Survey - What I...
Top 5 Information Security Lessons Learned from Transitioning to the Cloud

Top 5 Information Security Lessons Learned from Transitioning to the Cloud
Symantec 2011 Encryption Flash Poll Global Results

Symantec 2011 Encryption Flash Poll Global Results
Symantec - The Importance of Building Your Zero Trust Program on a Solid Plat...

Symantec - The Importance of Building Your Zero Trust Program on a Solid Plat...
Direct Edge and BATS Global Markets Trusts Intralinks Dealspace™

Direct Edge and BATS Global Markets Trusts Intralinks Dealspace™
Manage Risk by Protecting the Apps and Data That Drive Business Productivity

Manage Risk by Protecting the Apps and Data That Drive Business Productivity
Ähnlich wie Cloud Identity
Author : Tomslin Samme-Nlar
Presented at EOCON 2022
Video of the presentation : https://youtu.be/UC-8HteCxPkReport: Digital Transformation and Application Security Posture in West and C...

Report: Digital Transformation and Application Security Posture in West and C...EyesOpen Association
Ähnlich wie Cloud Identity (20)
Perception Gaps in Cyber Resilience: What Are Your Blind Spots?

Perception Gaps in Cyber Resilience: What Are Your Blind Spots?
How You can Leverage Cloud Platforms to Transform Digital Experience

How You can Leverage Cloud Platforms to Transform Digital Experience
Cloud for Busieness Managers: the Good, the Bad and de Ugly

Cloud for Busieness Managers: the Good, the Bad and de Ugly
Infographic: Bringing Your Cloud Visibility Back Into Focus

Infographic: Bringing Your Cloud Visibility Back Into Focus
Identity and Access Management as a Service Gets Boost with SailPoint's Ident...

Identity and Access Management as a Service Gets Boost with SailPoint's Ident...
application-security-fallacies-and-realities-veracode

application-security-fallacies-and-realities-veracode
AbstractCloud computing technology has become the new fron.docx

AbstractCloud computing technology has become the new fron.docx
Report: Digital Transformation and Application Security Posture in West and C...

Report: Digital Transformation and Application Security Posture in West and C...
Mehr von NetIQ
Mehr von NetIQ (20)
Advanced Persistent Threat - Evaluating Effective Responses

Advanced Persistent Threat - Evaluating Effective Responses
The University of Westminster Saves Time and Money with Identity Manager

The University of Westminster Saves Time and Money with Identity Manager
The London School of Hygiene & Tropical Medicine Accelerates and Streamlines ...

The London School of Hygiene & Tropical Medicine Accelerates and Streamlines ...
Swisscard Saves Time and Effort in Managing User Access

Swisscard Saves Time and Effort in Managing User Access
Vodacom Tightens Security with Identity Manager from NetIQ

Vodacom Tightens Security with Identity Manager from NetIQ
University of Dayton Ensures Compliance with Sentinel Log Manager

University of Dayton Ensures Compliance with Sentinel Log Manager
Nippon Light Metal Forges a Disaster Recovery Solution with NetIQ

Nippon Light Metal Forges a Disaster Recovery Solution with NetIQ
Nexus Differentiates Itself and Grows Its Capabilities with Operations Center

Nexus Differentiates Itself and Grows Its Capabilities with Operations Center
Professional Services Company Boosts Security, Facilitates Compliance, Automa...

Professional Services Company Boosts Security, Facilitates Compliance, Automa...
NetIQ Identity Manager Unites Hanshan Normal University

NetIQ Identity Manager Unites Hanshan Normal University
Handelsbanken Takes Control of Identity Management with NetIQ

Handelsbanken Takes Control of Identity Management with NetIQ
Millions of People Depend on Datang Xianyi Technology and NetIQ

Millions of People Depend on Datang Xianyi Technology and NetIQ
bluesource Uses NetIQ AppManager to Offer Standout Managed Service

bluesource Uses NetIQ AppManager to Offer Standout Managed Service
Central Denmark Region Strengthens Administrative Security with Identity Mana...

Central Denmark Region Strengthens Administrative Security with Identity Mana...
Kürzlich hochgeladen
Kürzlich hochgeladen (20)
ProductAnonymous-April2024-WinProductDiscovery-MelissaKlemke

ProductAnonymous-April2024-WinProductDiscovery-MelissaKlemke
Boost Fertility New Invention Ups Success Rates.pdf

Boost Fertility New Invention Ups Success Rates.pdf
Automating Google Workspace (GWS) & more with Apps Script

Automating Google Workspace (GWS) & more with Apps Script
Top 5 Benefits OF Using Muvi Live Paywall For Live Streams

Top 5 Benefits OF Using Muvi Live Paywall For Live Streams
TrustArc Webinar - Unlock the Power of AI-Driven Data Discovery

TrustArc Webinar - Unlock the Power of AI-Driven Data Discovery
Mastering MySQL Database Architecture: Deep Dive into MySQL Shell and MySQL R...

Mastering MySQL Database Architecture: Deep Dive into MySQL Shell and MySQL R...
HTML Injection Attacks: Impact and Mitigation Strategies

HTML Injection Attacks: Impact and Mitigation Strategies
Cloud Frontiers: A Deep Dive into Serverless Spatial Data and FME

Cloud Frontiers: A Deep Dive into Serverless Spatial Data and FME
Workshop - Best of Both Worlds_ Combine KG and Vector search for enhanced R...

Workshop - Best of Both Worlds_ Combine KG and Vector search for enhanced R...
Repurposing LNG terminals for Hydrogen Ammonia: Feasibility and Cost Saving

Repurposing LNG terminals for Hydrogen Ammonia: Feasibility and Cost Saving
Strategies for Landing an Oracle DBA Job as a Fresher

Strategies for Landing an Oracle DBA Job as a Fresher
AWS Community Day CPH - Three problems of Terraform

AWS Community Day CPH - Three problems of Terraform
Strategize a Smooth Tenant-to-tenant Migration and Copilot Takeoff

Strategize a Smooth Tenant-to-tenant Migration and Copilot Takeoff
Strategies for Unlocking Knowledge Management in Microsoft 365 in the Copilot...

Strategies for Unlocking Knowledge Management in Microsoft 365 in the Copilot...
Boost PC performance: How more available memory can improve productivity

Boost PC performance: How more available memory can improve productivity
Apidays New York 2024 - The value of a flexible API Management solution for O...

Apidays New York 2024 - The value of a flexible API Management solution for O...
How to Troubleshoot Apps for the Modern Connected Worker

How to Troubleshoot Apps for the Modern Connected Worker
Cloud Identity
- 1. Cloud Identity - Infographic Compliance Within the context of moving data and applications to the cloud, the vast majority of respondents said that they expected few or no problems with respect to to legislative compliance. Most (58%) were very confident that they could demonstrate compliance within the cloud and over one-third (37%) were moderately confident. While levels of confidence in EMEA were slightly lower (45% very confident, 47% moderately confident), this is likely to be a consequence of the stringency of security and privacy legislation in some European countries. in association with Impact of mobile devices on SaaS applications The impact of mobile devices on SaaS usage varies considerably across geographies, and may mirror the adoption rates of BYOD (bring your own device) within corporations. Impact of mobile devices on SaaS applications (globally) The relationship between cloud and mobile devices is clearly a complex one, as different organisations are adopting different strategies, based on their circumstances, business models and processes. For example, a company seeing a large increase in SaaS along with mobile devices use may be managing a major decrease in in-house infrastructure and taking the opportunity to move applications and data into the cloud. On the other hand, the smaller proportion that expects to see a decrease in SaaS applications might be taking the opportunity of its new mobile platforms to cut back on lightly used services. There is a strong belief among respondents that cloud-based applications can increase the security of the organisation. Despite the concerns shown about migrating to the cloud, it is clear that moving to an infrastructure that is not hosted in-house is seen as a better solution from a security perspective. 15%75% 10% Expected security impact of SaaS applications SaaS applications have increased business information security SaaS applications have decreased business information security SaaS applications have had no impact on business information security Cloud-based software services (SaaS) have had a huge impact on business globally, and growth in the usage of SaaS has in turn been driven by other changes, especially the growth in the use of mobile devices. Growth and impact of cloud-based software services 96% say the number of SaaS applications will grow by at least 50% or more 75% say SaaS has increased business information security 53% say that mobile device usage has increased the usage of SaaS 53% 43% 21% 16% 10% 10% Mobile devices are driving a significant increase in SaaS use Mobile devices are driving a slight decrease in SaaS use Mobile devices are driving a significant decrease in SaaS use Mobile devices are driving a slight increase in SaaS use Mobile devices are having no effect on SaaS use Mobile device deployment means SaaS application usage has grown by 67% in North America Mobile device deployment means SaaS application usage has grown by 51% in EMEA Mobile device deployment means SaaS application usage has grown by 38% in APAC Very confident that they could demonstrate regulatory compliance Moderately confident that they could demonstrate regulatory compliance Not at all confident that they could demonstrate regulatory compliance Concerns about cloud migration Respondents were asked what their concerns were about moving to the cloud, and how strong those concerns were. The top six issues about which respondents expressed any level of concern when migrating to the cloud are: Security/ confidentiality of customer information Security of intellectual property or trade secrets Security/confidentiality of employee information Corporate (organizational) financial information Security of e-mail communication Business intelligence 93% 90% 90% 88% 88% 88% 75% 96% 58% 37% 5% 67 51 38
