Databse & Technology 2 _ Francisco Munoz Alvarez _ Oracle Security Tips - Some easyways to make your DB more secure.pdf
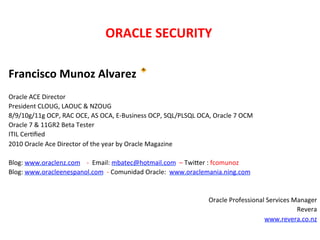
- 1. ORACLE SECURITY Francisco Munoz Alvarez Oracle ACE Director President CLOUG, LAOUC & NZOUG 8/9/10g/11g OCP, RAC OCE, AS OCA, E-‐Business OCP, SQL/PLSQL OCA, Oracle 7 OCM Oracle 7 & 11GR2 Beta Tester ITIL CerKfied 2010 Oracle Ace Director of the year by Oracle Magazine Blog: www.oraclenz.com -‐ Email: mbatec@hotmail.com – TwiXer : fcomunoz Blog: www.oracleenespanol.com -‐ Comunidad Oracle: www.oraclemania.ning.com Oracle Professional Services Manager Revera www.revera.co.nz
- 2. ORACLE SECURITY TIPS Insync 2011 Sydney, Australia By: Francisco Munoz Alvarez
- 3. Mature Born here Grow up Got Married Here Now Living here here here DBIS - Copyright 2010 3
- 4. The Rule: “The most important rule with respect to data is to never put yourself into an unrecoverable situaKon.” The importance of this guideline cannot be stressed enough, but it does not mean that you can never use time saving or performance enhancing options.
- 5. Always Try it Before! When it comes to theory, “NEVER” believe anything you hear or read unKl you have tried it yourself. 5
- 6. 6
- 7. Backup, Backup & Backup Why? Because bad stuff happens… 7
- 8. InformaBon Security Has Changed
- 10. OFFICIAL STATISTICS from Secret Service Germany
- 11. SOME SHORT FACTS
- 12. HIGH SCORE LIST
- 14. CRISIS SHOPPING LIST 2009
- 15. CONCLUSION
- 19. DB ENVIRONMENT
- 20. Security Data in Rest/Access Control
- 21. WHAT IS ASO?
- 22. What Security Problems does ASO solve?
- 23. ASO BENEFITS
- 24. TDE – Transparent Data EncrypBon
- 25. TDE – Transparent Data EncrypBon
- 26. TDE – Transparent Data EncrypBon
- 27. SECURING DATA IN MOTION
- 29. SECURING BACKUP
- 30. SECURING BACKUP Examples
- 31. DATAMASKING
- 33. PREVENT MODIFICATIONS BY UNAUTHORIZED USERS
- 34. WHAT IS DATA VAULT?
- 35. DATA VAULT HELP TO SOLVE:
- 36. DATA VAULT Vs VPD and OLS
- 37. DATABASE VAULT Realms and Rule
- 40. HIGHLY SECURED ENVIROMENTS AUDIT VALT
- 42. AUDIT VAULT REPORTS Who, What, When, Where
- 45. 26 Security Tips
- 46. Some Oracle Security Tips 1) Grant privileges only to a user or applicaKon which requires the privilege to accomplish necessary work. Excessive granKng of unnecessary privileges can compromise security.
- 47. Some Oracle Security Tips 2)No administraKve funcKons are to be performed by an applicaKon. For example create user, delete user, grant role, grant object privileges, etc.
- 48. Some Oracle Security Tips 3) Privileges for schema or database owner objects should be granted via a role and not explicitly. Do not use the “ALL” opKon when granKng object privileges, instead specify the exact privilege needed, such as select, update, insert, delete.
- 49. Some Oracle Security Tips 4 ) P a s s w o r d p r o t e c t e d r o l e s m a y b e implemented to allow an applicaKon to control access to its data. Thereby, end users may not access the applicaKon’s data from outside the applicaKon.
- 50. Some Oracle Security Tips 5)Access to AdministraKve or System user accounts should be restricted to authorized DBAs.
- 51. Some Oracle Security Tips 6) Do not grant system supplied database roles. These roles may have administraKve privileges and the role privileges may change with new releases of the database.
- 52. Some Oracle Security Tips 7) Database catalog access should be restricted. Example: Use “USER_VIEWS” instead of “DBA_VIEWS” for an Oracle database.
- 53. Some Oracle Security Tips 8) Privileges granted to PUBLIC are accessible to every user and should be granted only when necessary.
- 54. Some Oracle Security Tips 9) Any password stored by applicaKons in the database should be encrypted.
- 55. Some Oracle Security Tips 10) ApplicaKons should not “DROP”, “CREATE” or “ALTER” objects within the applicaKon.
- 56. Some Oracle Security Tips 11) UKlize the shared database infrastructure to share cost whenever possible.
- 57. Some Oracle Security Tips 12) ApplicaKons should not access the database with the same security as the owner of the database objects. For example on SQL Server do not grant the “dbowner” role and on Oracle do not use the Schema userid to connect to the database. Setup another userid with the necessary privileges to run the applicaKon.
- 58. Some Oracle Security Tips 13) Database integrity should be enforced on the database using foreign keys not in the applicaKon code. This helps prevent code outside the applicaKon from creaKng orphan records and/or invalid data.
- 59. Some Oracle Security Tips 14) Do not hard code username and passwords in the applicaKon source code. • Sqlplus /nolog @myscript – Create a password file (.password) fmunoz evelyn scoX Kger – Create a shell script getpwd.sh fgrep $1 $HOME/tools/.password | cut –d “ “ –f2 – Use the script and the password file Getpwd.sh fmunoz | sqlplus –s fmunoz @script • RMAN rman target / connect catalog user/pwd@catdb
- 60. Some Oracle Security Tips 15) Protect your Listener (Cont.): – LSNRCTL> Set Current Listener <ip_address> – LSNRCTL> Set rawmode on – LSNRCTL> Services – LSNRCTL> Stop – LSNRCTL> Set startup_waitme 20 – LSNRCTL> Set logfile redo01a – LSNRCTL> Set log_directory ‘/u01/app/oracle/redo’
- 61. Some Oracle Security Tips 15) Protect your Listener: – Disable online modificaKons • LSNRCTL> Admin_restricKons _<listener_name>=ON • LSNRCTL> Change_password • LSNRCTL> Save_config
- 62. Some Oracle Security Tips 16) Ensure external users have the least privilege possible.
- 63. Some Oracle Security Tips 17) Have a clear and well documented Backup and Recovery Strategy
- 64. Some Oracle Security Tips 18) Implement an strong password policy (user profile) and force all users to change their passwords constantly .
- 65. Some Oracle Security Tips 19) All important passwords need to be saved in a safe and replaced when changed.
- 66. Some Oracle Security Tips 20) Install only what’s really required.
- 67. Some Oracle Security Tips 21) Implement Audit, soon or later you will be ask to tell who changed that. Please, implement a purge strategy.
- 68. Some Oracle Security Tips 22) Create promoKon procedures (DEV-‐>TEST-‐ >PROD), lock your producKon environment and test environment. Don’t forget to implement and document a change register.
- 69. Some Oracle Security Tips 23) Implement an Indirect Login Policy – Each user have their own login account – Allow connecKons to oracle account (OS) only thru sudo – This will leaves an audit trail of acKons
- 70. Some Oracle Security Tips 24) Prevent SYSDBA connecKon – Sqlplus / as sysdba • Change SQLNET.ORA SQLNET.AUTHENTICATION_SERVICES=(NONE)
- 71. Some Oracle Security Tips 25) Avoid Risk ConnecKons (Ext. Procedures) – Listener.ora • (ADDRESS_LIST = (ADDRESS = (PROTOCOL = IPC) (KEY = EXTPROC)) Remove this lines, or move to a different listener
- 72. Some Oracle Security Tips 26) Enable Data DicKonary ProtecKon Oracle Recommends that customers implement data dicKonary protecKon to prevent users who have the “ANY” system privileges to modify or harm the Oracle data dicKonary. Set 07_DICTIONARY_ACCESSIBILITY parameter to FALSE.
- 73. PROGRAM The Oracle ACE Program is designed to recognize and reward members of the Oracle Technology and Applications communities for their contributions to those communities. These individuals are technically proficient (when applicable) and willingly share their knowledge and experiences. The program comprises two levels: Oracle ACE and Oracle ACE Director. The former designation is Oracle's way of saying "thank you" to community contributors for their efforts; we (and the community) appreciate their enthusiasm. The latter designation is for community enthusiasts who not only share their knowledge (usually in extraordinary ways), but also want to increase their community advocacy and work more proactively with Oracle to find opportunities for the same. In this sense, Oracle ACE is "backward looking" and Oracle ACE Director is "forward looking."
- 77. QuesBons?
- 78. Thank you !