Passwords & corresponding accounts
•Als PPT, PDF herunterladen•
1 gefällt mir•743 views
Are you able to remember and recall the relations between accounts and the corresponding passwords? The Expanded Password System that accepts images provides a solution to this hard problem. When unique matrices of images are allocated to different accounts with the EPS, those unique matrices of images will be telling you what images you could pick up as your passwords.
Melden
Teilen
Melden
Teilen
Empfohlen
Empfohlen
Weitere ähnliche Inhalte
Andere mochten auch
Andere mochten auch (7)
NCC achieves transparency via IBX Spend Analytics enabling a complete procure...

NCC achieves transparency via IBX Spend Analytics enabling a complete procure...
Personalising Customer Experience in the Hospitality Industry June 2016

Personalising Customer Experience in the Hospitality Industry June 2016
Mehr von Hitoshi Kokumai
Mehr von Hitoshi Kokumai (16)
Fend Off Cyberattack with Episodic Memory (24Feb2023)

Fend Off Cyberattack with Episodic Memory (24Feb2023)
Slide Share (Updated) - Fend Off Cybercrime with Episodic Memory 29Aug2022

Slide Share (Updated) - Fend Off Cybercrime with Episodic Memory 29Aug2022
Bring healthy second life to legacy password system

Bring healthy second life to legacy password system
Intriguing Evlolution from One to Two and Back to One

Intriguing Evlolution from One to Two and Back to One
Updated: Identity Assurance by Our Own Volition and Memory

Updated: Identity Assurance by Our Own Volition and Memory
Clues to Unravelling Conundrums - Biometrics deployed 'in parallel' as again...

Clues to Unravelling Conundrums - Biometrics deployed 'in parallel' as again...
Help unravel the conundrum over NIST authentication guideline

Help unravel the conundrum over NIST authentication guideline
Expanded password system - Reliable Identity Assurance

Expanded password system - Reliable Identity Assurance
Kürzlich hochgeladen
Enterprise Knowledge’s Urmi Majumder, Principal Data Architecture Consultant, and Fernando Aguilar Islas, Senior Data Science Consultant, presented "Driving Behavioral Change for Information Management through Data-Driven Green Strategy" on March 27, 2024 at Enterprise Data World (EDW) in Orlando, Florida.
In this presentation, Urmi and Fernando discussed a case study describing how the information management division in a large supply chain organization drove user behavior change through awareness of the carbon footprint of their duplicated and near-duplicated content, identified via advanced data analytics. Check out their presentation to gain valuable perspectives on utilizing data-driven strategies to influence positive behavioral shifts and support sustainability initiatives within your organization.
In this session, participants gained answers to the following questions:
- What is a Green Information Management (IM) Strategy, and why should you have one?
- How can Artificial Intelligence (AI) and Machine Learning (ML) support your Green IM Strategy through content deduplication?
- How can an organization use insights into their data to influence employee behavior for IM?
- How can you reap additional benefits from content reduction that go beyond Green IM?
Driving Behavioral Change for Information Management through Data-Driven Gree...

Driving Behavioral Change for Information Management through Data-Driven Gree...Enterprise Knowledge
Kürzlich hochgeladen (20)
Understanding Discord NSFW Servers A Guide for Responsible Users.pdf

Understanding Discord NSFW Servers A Guide for Responsible Users.pdf
[2024]Digital Global Overview Report 2024 Meltwater.pdf![[2024]Digital Global Overview Report 2024 Meltwater.pdf](data:image/gif;base64,R0lGODlhAQABAIAAAAAAAP///yH5BAEAAAAALAAAAAABAAEAAAIBRAA7)
![[2024]Digital Global Overview Report 2024 Meltwater.pdf](data:image/gif;base64,R0lGODlhAQABAIAAAAAAAP///yH5BAEAAAAALAAAAAABAAEAAAIBRAA7)
[2024]Digital Global Overview Report 2024 Meltwater.pdf
2024: Domino Containers - The Next Step. News from the Domino Container commu...

2024: Domino Containers - The Next Step. News from the Domino Container commu...
How to Troubleshoot Apps for the Modern Connected Worker

How to Troubleshoot Apps for the Modern Connected Worker
Powerful Google developer tools for immediate impact! (2023-24 C)

Powerful Google developer tools for immediate impact! (2023-24 C)
Exploring the Future Potential of AI-Enabled Smartphone Processors

Exploring the Future Potential of AI-Enabled Smartphone Processors
Apidays Singapore 2024 - Building Digital Trust in a Digital Economy by Veron...

Apidays Singapore 2024 - Building Digital Trust in a Digital Economy by Veron...
08448380779 Call Girls In Friends Colony Women Seeking Men

08448380779 Call Girls In Friends Colony Women Seeking Men
Boost PC performance: How more available memory can improve productivity

Boost PC performance: How more available memory can improve productivity
The 7 Things I Know About Cyber Security After 25 Years | April 2024

The 7 Things I Know About Cyber Security After 25 Years | April 2024
08448380779 Call Girls In Civil Lines Women Seeking Men

08448380779 Call Girls In Civil Lines Women Seeking Men
The Role of Taxonomy and Ontology in Semantic Layers - Heather Hedden.pdf

The Role of Taxonomy and Ontology in Semantic Layers - Heather Hedden.pdf
08448380779 Call Girls In Greater Kailash - I Women Seeking Men

08448380779 Call Girls In Greater Kailash - I Women Seeking Men
Strategies for Landing an Oracle DBA Job as a Fresher

Strategies for Landing an Oracle DBA Job as a Fresher
What Are The Drone Anti-jamming Systems Technology?

What Are The Drone Anti-jamming Systems Technology?
Driving Behavioral Change for Information Management through Data-Driven Gree...

Driving Behavioral Change for Information Management through Data-Driven Gree...
Passwords & corresponding accounts
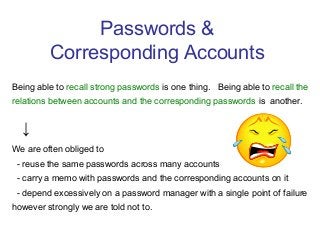
- 1. Passwords & Corresponding Accounts Being able to recall strong passwords is one thing. Being able to recall the relations between accounts and the corresponding passwords is another. ↓ We are often obliged to - reuse the same passwords across many accounts - carry a memo with passwords and the corresponding accounts on it - depend excessively on a password manager with a single point of failure however strongly we are told not to.
- 2. Biometric products do not help for this problem because biometric solutions require a password to be registered in case of false rejection. No Help from Password-Dependent Solutions Neither do the multi-factor authentications which require a password as one of the factors.
- 3. Expanded Password System that accepts images provides a solution to this hard problem. When unique matrices of images are allocated to different accounts with the EPS, those unique matrices of images will be telling you what images you could pick up as your passwords. Here is The Solution The EPS will free us from the burden of managing the relations between accounts and the corresponding passwords. Account A Account B Account C Account D Account E, F, G, H, I, J, K, L-----------
- 4. At the root of the password headache is the cognitive phenomena called “interference of memory”, by which we cannot firmly remember more than 5 text passwords on average. What worries us is not the password, but the textual password. The textual memory is only a small part of what we remember. We could think of making use of the larger part of our memory that is less subject to interference of memory. More attention could be paid to the efforts of expanding the password system to include images, particularly KNOWN images, in addition to characters. The outline of Expanded Password System is available at http://www.slideshare.net/HitoshiKokumai/expanded-password-system Interference of Memory 19 April, 2015 Mnemonic Security, Inc. Japan/UK
