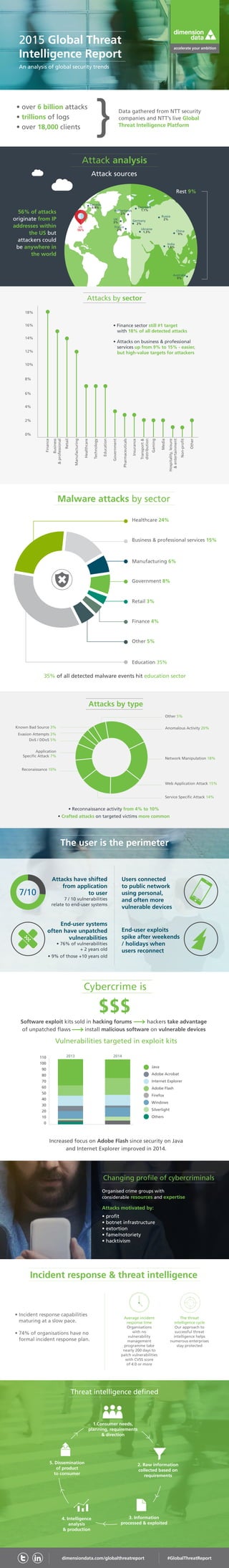
2015 Global Threat Intelligence Report - an analysis of global security trends
•
0 gefällt mir•720 views
The 2015 Global Threat Intelligence Report is an annual report which gives an overview of the biggest threats, and most prominent trends in the cyber security landscape.
Melden
Teilen
Melden
Teilen
Downloaden Sie, um offline zu lesen
Empfohlen
Empfohlen
Weitere ähnliche Inhalte
Was ist angesagt?
Was ist angesagt? (20)
Cybersecurity for Board of Directors - CIO Perspectives Atlanta 2015

Cybersecurity for Board of Directors - CIO Perspectives Atlanta 2015
What CIOs Need To Tell Their Boards About Cyber Security

What CIOs Need To Tell Their Boards About Cyber Security
Sia Partners - Insurance emerging risks infographic_v1

Sia Partners - Insurance emerging risks infographic_v1
The Journey to Cyber Resilience in a World of Fear, Uncertainty and Doubt

The Journey to Cyber Resilience in a World of Fear, Uncertainty and Doubt
Cyber Security in the Digital Age: A Survey and its Analysis

Cyber Security in the Digital Age: A Survey and its Analysis
Cyber Security Transformation - A New Approach for 2015 & Beyond - Daryl Pereira

Cyber Security Transformation - A New Approach for 2015 & Beyond - Daryl Pereira
Hide and seek - Attack Surface Management and continuous assessment.

Hide and seek - Attack Surface Management and continuous assessment.
Security Crossroads of Healthcare reforms and IoT enabled E-health

Security Crossroads of Healthcare reforms and IoT enabled E-health
Cybersecurity Priorities and Roadmap: Recommendations to DHS

Cybersecurity Priorities and Roadmap: Recommendations to DHS
Ähnlich wie 2015 Global Threat Intelligence Report - an analysis of global security trends
Data Breaches and Security: Ditching Data Disasters-Michael McNeil, Philips H...

Data Breaches and Security: Ditching Data Disasters-Michael McNeil, Philips H...IT Network marcus evans
CHIME LEAD San Francisco 2015 - Opening Keynote "What is Cyber Security and W...

CHIME LEAD San Francisco 2015 - Opening Keynote "What is Cyber Security and W...Health IT Conference – iHT2
Ähnlich wie 2015 Global Threat Intelligence Report - an analysis of global security trends (20)
Data Breaches and Security: Ditching Data Disasters-Michael McNeil, Philips H...

Data Breaches and Security: Ditching Data Disasters-Michael McNeil, Philips H...
SVB Cybersecurity Impact on Innovation Report - Overview

SVB Cybersecurity Impact on Innovation Report - Overview
Threat Detection as presented at the 2016 DGI Cyber security Conference

Threat Detection as presented at the 2016 DGI Cyber security Conference
5 Ways Technology Vendors Put Their Healthcare Customer's PHI at Risk

5 Ways Technology Vendors Put Their Healthcare Customer's PHI at Risk
CHIME LEAD San Francisco 2015 - Opening Keynote "What is Cyber Security and W...

CHIME LEAD San Francisco 2015 - Opening Keynote "What is Cyber Security and W...
Executive Summary of the 2016 Scalar Security Study

Executive Summary of the 2016 Scalar Security Study
7 Best Practices to Protect Critical Business Information [Infographic]![7 Best Practices to Protect Critical Business Information [Infographic]](data:image/gif;base64,R0lGODlhAQABAIAAAAAAAP///yH5BAEAAAAALAAAAAABAAEAAAIBRAA7)
![7 Best Practices to Protect Critical Business Information [Infographic]](data:image/gif;base64,R0lGODlhAQABAIAAAAAAAP///yH5BAEAAAAALAAAAAABAAEAAAIBRAA7)
7 Best Practices to Protect Critical Business Information [Infographic]
Mehr von DImension Data
Mehr von DImension Data (20)
End-User Computing Insights: A study of digital maturity

End-User Computing Insights: A study of digital maturity
Digital technology revolutionised the viewing experience of the tour de france

Digital technology revolutionised the viewing experience of the tour de france
Creating workspaces for tomorrow at the greatest cycling event in the world

Creating workspaces for tomorrow at the greatest cycling event in the world
Zurich case study how to move a data centre in 8 days

Zurich case study how to move a data centre in 8 days
Zurich case study: Reducing risk for insurance customers

Zurich case study: Reducing risk for insurance customers
High-performance solutions for an international university

High-performance solutions for an international university
How we helped Fujifilm keep its customers' special memories safe

How we helped Fujifilm keep its customers' special memories safe
Dimension Data Department Prime Minister and cabinet G20 case study

Dimension Data Department Prime Minister and cabinet G20 case study
2015 Global Contact Centre Benchmarking Report key findings

2015 Global Contact Centre Benchmarking Report key findings
Kürzlich hochgeladen
Kürzlich hochgeladen (20)
Presentation on how to chat with PDF using ChatGPT code interpreter

Presentation on how to chat with PDF using ChatGPT code interpreter
Axa Assurance Maroc - Insurer Innovation Award 2024

Axa Assurance Maroc - Insurer Innovation Award 2024
How to Troubleshoot Apps for the Modern Connected Worker

How to Troubleshoot Apps for the Modern Connected Worker
Neo4j - How KGs are shaping the future of Generative AI at AWS Summit London ...

Neo4j - How KGs are shaping the future of Generative AI at AWS Summit London ...
Raspberry Pi 5: Challenges and Solutions in Bringing up an OpenGL/Vulkan Driv...

Raspberry Pi 5: Challenges and Solutions in Bringing up an OpenGL/Vulkan Driv...
08448380779 Call Girls In Friends Colony Women Seeking Men

08448380779 Call Girls In Friends Colony Women Seeking Men
Breaking the Kubernetes Kill Chain: Host Path Mount

Breaking the Kubernetes Kill Chain: Host Path Mount
08448380779 Call Girls In Greater Kailash - I Women Seeking Men

08448380779 Call Girls In Greater Kailash - I Women Seeking Men
Scaling API-first – The story of a global engineering organization

Scaling API-first – The story of a global engineering organization
Exploring the Future Potential of AI-Enabled Smartphone Processors

Exploring the Future Potential of AI-Enabled Smartphone Processors
Top 5 Benefits OF Using Muvi Live Paywall For Live Streams

Top 5 Benefits OF Using Muvi Live Paywall For Live Streams
Automating Google Workspace (GWS) & more with Apps Script

Automating Google Workspace (GWS) & more with Apps Script
Apidays Singapore 2024 - Building Digital Trust in a Digital Economy by Veron...

Apidays Singapore 2024 - Building Digital Trust in a Digital Economy by Veron...
Factors to Consider When Choosing Accounts Payable Services Providers.pptx

Factors to Consider When Choosing Accounts Payable Services Providers.pptx
Unblocking The Main Thread Solving ANRs and Frozen Frames

Unblocking The Main Thread Solving ANRs and Frozen Frames
The 7 Things I Know About Cyber Security After 25 Years | April 2024

The 7 Things I Know About Cyber Security After 25 Years | April 2024
2015 Global Threat Intelligence Report - an analysis of global security trends
- 1. Vulnerabilities targeted in exploit kits Healthcare 24% Business & professional services 15% Manufacturing 6% Government 8% Retail 3% Finance 4% Other 5% Education 35% 2015 Global Threat Intelligence Report An analysis of global security trends • over 6 billion attacks • trillions of logs • over 18,000 clients 56% of attacks originate from IP addresses within the US but attackers could be anywhere in the world • Finance sector still #1 target with 18% of all detected attacks Attacks have shifted from application to user 7 / 10 vulnerabilities relate to end-user systems Users connected to public network using personal, and often more vulnerable devices End-user exploits spike after weekends / holidays when users reconnect End-user systems often have unpatched vulnerabilities • 76% of vulnerabilities + 2 years old • 9% of those +10 years old Data gathered from NTT security companies and NTT’s live Global Threat Intelligence Platform Attack analysis Attack sources Attacks by sector Malware attacks by sector 35% of all detected malware events hit education sector The user is the perimeter 7/10 Software exploit kits sold in hacking forums hackers take advantage of unpatched flaws install malicious software on vulnerable devices Cybercrime is Changing profile of cybercriminals Organised crime groups with considerable resources and expertise Attacks motivated by: • profit • botnet infrastructure • extortion • fame/notoriety • hacktivism Incident response & threat intelligence Threat intelligence defined • Incident response capabilities maturing at a slow pace. • 74% of organisations have no formal incident response plan. Average incident response time Organisations with no vulnerability management programme take nearly 200 days to patch vulnerabilities with CVSS score of 4.0 or more The threat intelligence cycle Our approach to successful threat intelligence helps numerous enterprises stay protected 2. Raw information collected based on requirements 3. Information processed exploited 4. Intelligence analysis production 1.Consumer needs, planning, requirements direction 5. Dissemination of product to consumer Finance 0% 2% 4% 8% 10% 12% 14% 16% 18% 6% Business professional Manufacturing Retail Healthcare Technology Education Government Pharmaceuticals Insurance Transport distribution Gaming Media Hospitality,leisure entertainment Non-profit Other • Reconnaissance activity from 4% to 10% • Crafted attacks on targeted victims more common Java Adobe Acrobat Internet Explorer Adobe Flash Firefox Windows Silverlight Others Increased focus on Adobe Flash since security on Java and Internet Explorer improved in 2014. 2013 2014110 100 90 80 70 60 50 40 30 20 10 0 dimensiondata.com/globalthreatreport #GlobalThreatReport US 56% China 9% France 2% India 1.5% Germany 2% Netherlands 2% Denmark 1.1% Russia 2% Ukraine 1.3% Canada 0.9% Australia 9% Rest 9% • Attacks on business professional services up from 9% to 15% - easier, but high-value targets for attackers $$ $ Other 5% Known Bad Source 3% Evasion Attempts 3% DoS / DDoS 5% Application Specific Attack 7% Reconaissance 10% Anomalous Activity 20% Network Manipulation 18% Web Application Attack 15% Service Specific Attack 14% Attacks by type UK 3%
