Keys To Better Data Security In the Cloud
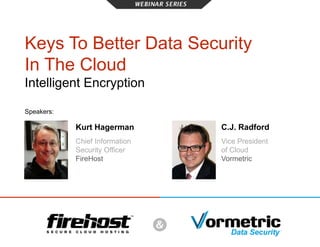
- 1. Keys To Better Data Security In The Cloud Intelligent Encryption Speakers: C.J. Radford Vice President of Cloud Vormetric Kurt Hagerman Chief Information Security Officer FireHost
- 2. Keys To Better Data Security In The Cloud INTELLIGENT ENCRYPTION Today’s Agenda • Cloud Industry Trends • Data Security Myths & Realities • Compliance & Legal Considerations • Encryption as Part of a Broader Security Approach • An Intelligent Security Model: Multilayered Security • Incorporating Data Security Sensibly • Recent Breaches and Encryption’s Role • Questions & Answers Submit your questions throughout the webinar via chat. We’ll address them live at the end or follow up offline
- 3. Diversification Impact of that on provider decision Keys To Better Data Security In The Cloud INTELLIGENT ENCRYPTION Specialists vs. Generalists Diversification of providers
- 4. Keys To Better Data Security In The Cloud INTELLIGENT ENCRYPTION Cloud Security Pain Points Top Security Concerns with Cloud Computing Data Privacy & Security Access & Control Auditing & Compliance Control of Data Security Models/Toolsets Contractual/Legal Issues Internal Issues Network Connection Security Geographical Coverage 37% Believe security is the biggest pain point 73% Considered Security to be extremely important 41% 35% 32% 26% 18% 15% 11% 10% 4%
- 5. Keys To Better Data Security In The Cloud INTELLIGENT ENCRYPTION SECURE DATA
- 6. Types of Encryption Data in Motion Keys To Better Data Security In The Cloud INTELLIGENT ENCRYPTION Data at Rest
- 7. Keys To Better Data Security In The Cloud You’re not secure with Full Disk Encryption I’m secure with Full Disk Encryption INTELLIGENT ENCRYPTION VS Myth Reality
- 8. Myth Keys To Better Data Security In The Cloud Encryption is vital and required for most organizations Encryption is optional for my organization Reality VS INTELLIGENT ENCRYPTION
- 9. Keys To Better Data Security In The Cloud A well-designed solution can avoid performance degradation Encryption slows down my performance INTELLIGENT ENCRYPTION VS Myth Reality
- 10. Keys To Better Data Security In The Cloud A best practice is having an encryption strategy from the beginning Encryption is a final touch on a security program INTELLIGENT ENCRYPTION VS Myth Reality
- 11. Keys To Better Data Security In The Cloud Encryption & key management can be simple with the right solution Encryption & key management is hard INTELLIGENT ENCRYPTION VS Myth Reality
- 12. Keys To Better Data Security In The Cloud Encryption protects It depends! my data from privileged user access INTELLIGENT ENCRYPTION VS Myth Reality
- 13. Keys To Better Data Security In The Cloud INTELLIGENT ENCRYPTION The Legal Side of Encryption
- 14. Keys To Better Data Security In The Cloud INTELLIGENT ENCRYPTION How FireHost approaches encryption • Enforce separation of DSM from other VMs • Customer is always the custodian of policies and keys
- 15. Keys To Better Data Security In The Cloud INTELLIGENT ENCRYPTION The FireHost Difference
- 16. Keys To Better Data Security In The Cloud INTELLIGENT ENCRYPTION In the News December 2013 January 2014 110 million customers’ credit card and personal data stolen 1.1 million customers’ credit and debit card data stolen April 2014 3 million customers’ credit and debit card data stolen May 2014 June 2014 145 million users’ passwords affected (Forensics under way) Credit and debit cards Who’s Next? ? It happened this week…
- 17. Keys To Better Data Security In The Cloud INTELLIGENT ENCRYPTION The Last Week Monday, August 18 4.5 million patient records stolen Names, addresses, birth dates, phone numbers, and Social Security numbers Publicity could have been avoided with Encryption. Don’t Be Next 206 Hospitals in 29 States HIPAA, and most state breach notification laws, don't consider the loss of encrypted data without the keys as a reportable event. August 15 August 20
- 18. Thank You Questions? @kurthagerman @cjrad C.J. Radford Vice President of Cloud Vormetric Kurt Hagerman Chief Information Security Officer FireHost
Hinweis der Redaktion
- -- Canned Q/Tie in with PPT flow as well: Hybrid cloud trends, sharing across lines; Vormetric well-suited for hybrid cloud environments
- Cloud Industry’s Diversification & Its Impact on Customer Decisions – -- Cloud industry convergence (SPs, product vendors, SaaS/PaaS, startups, SI, cloud providers) -- Generalist vs. specialist and rise of specialization, security as an example.
- Industry Trends: Cloud, Data, Internet Just think what these projections could be if security was not a barrier and contingencies were addressed.
- Role Data security’s role in IofT, mobility, app-centricity, etc. as it all manifests in cloud – last line of defense? All grabbing data from a server – ultimately data is the atomic unit; It’s about the data… Following it and securing where it lives and goes is critical
- In motion is IPsec/SSL VPN/P2P encryption Data-at-Rest, e.g. Application-Layer Encryption / Table-level encryption/TDE, Vormetric is the #1 File System Encryption solution, Disk is Self Encryption Drives like NetApp NSE drives. Today’s presentation is about Data-at-Rest. Note, Application-layer and sometimes File System (like with backup) also handle data in motion.
- It only protects your data if the hardware is physically stolen. Once powered up and unlocked all drive data is in the clear to privileged users and miscreants Encryption is the lock, keys activate that encryption/lock. Hide keys in the house, under a rock, under the mat? Bad guys hunt for keys. Too laborious to crack encryption/lock itself. Storing the keys and protecting them is key…
- Vital for compliance with many regulations, like PCI, HIPAA, Breach Notification laws, etc. Vormetric has a paper….
- Look for solutions optimized for performance. Things to look for include: Deep file system integration, strong multi-threading and queuing capabilities and ability to leverage AES acceleration hardware like Intel AES-NI capabilities.
- It is always easier to start with encryption so that you don’t have to identify and encrypt large amounts of information further down a data life cycle. Think of all the back ups, snap shots, and other copies that may have been made before the encryption was put in place! In addition, all too often single purpose solutions are deployed b/c an encryption strategy isn’t in place… this has high capex and opex costs…. Better to have a strategy in place that is consistent, repeatable and centrally managed for many environments and data types….
- Encryption key management is very hard Encryption is the lock, keys activate that encryption/lock. Hide keys in the house, under a rock, under the mat? Bad guys hunt for keys. Too laborious to crack encryption/lock itself. Storing the keys and protecting them is key…
- Some File System-level solutions and Application-layer solutions can foil privileged users. Once booted, FDE and Volume-level solutions can’t stop the privileged user. Encryption is the lock, keys activate that encryption/lock. Hide keys in the house, under a rock, under the mat? Bad guys hunt for keys. Too laborious to crack encryption/lock itself. Storing the keys and protecting them is key…
- Compliance and regulatory requirements Protection against fine and penalties. Even if you lose the data, it’s remains encrypted and consequences are reduced.
- Vormetric Data Security solution can be implemented in two different configurations in CSP. Customer can host Data Security Manager(s) on-site and protect data both on server in their data center as well as servers in CSP cloud. The customer will manage and have ownership of encryption keys and data access policies. They can dictate who can access protected data. CSP Team can manage customer data (e.g. backup/restore, DR capability) but will not be able to see the contents of data as it will remain encrypted. HOW IT WORKS Encryption, enterprise key management & access control Encryption is only as strong as the keys are protected You own your keys to keep your data private Provider has no data access Other solutions don’t offer this option
- The FireHost Difference Our clouds are born secure Encryption is an ingredient – not the entire program It is built in, not bolted on Our security enables compliance - not a checkbox mentality
- Industry Trends: Cloud, Data, Internet Just think what these projections could be if security was not a barrier and contingencies were addressed.
- Industry Trends: Cloud, Data, Internet Just think what these projections could be if security was not a barrier and contingencies were addressed.
