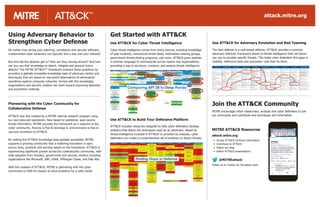
Use ATT&CK Framework for Cyber Threat Intelligence and Defense
- 1. Use ATT&CK for Cyber Threat Intelligence Cyber threat intelligence comes from many sources, including knowledge of past incidents, commercial threat feeds, information-sharing groups, government threat-sharing programs, and more. ATT&CK gives analysts a common language to communicate across reports and organizations, providing a way to structure, compare, and analyze threat intelligence. Use ATT&CK to Build Your Defensive Platform ATT&CK includes resources designed to help cyber defenders develop analytics that detect the techniques used by an adversary. Based on threat intelligence included in ATT&CK or provided by analysts, cyber defenders can create a comprehensive set of analytics to detect threats. Use ATT&CK for Adversary Emulation and Red Teaming The best defense is a well-tested defense. ATT&CK provides a common adversary behavior framework based on threat intelligence that red teams can use to emulate specific threats. This helps cyber defenders find gaps in visibility, defensive tools and processes—and then fix them. No matter how strong your patching, compliance and security software, a determined cyber adversary can typically find a way into your network. But how did the attacker get in? How are they moving around? And how can you use that knowledge to detect, mitigate and prevent future attacks? The MITRE ATT&CK™ framework answers those questions by providing a globally accessible knowledge base of adversary tactics and techniques that are based on real-world observations of adversaries’ operations against computer networks. Armed with this knowledge, organizations and security vendors can work toward improving detection and prevention methods. Pioneering with the Cyber Community for Collaborative Defense ATT&CK was first created by a MITRE internal research program using our own data and operations. Now based on published, open source threat information, MITRE provides the framework as a resource to the cyber community. Anyone is free to leverage it, and everyone is free to use and contribute to ATT&CK. By making the ATT&CK knowledge base globally accessible, MITRE supports a growing community that is fostering innovation in open source tools, products and services based on the framework. ATT&CK is experiencing significant growth across the cybersecurity community, with wide adoption from industry, government and security vendors including organizations like Microsoft, IBM, USAA, JPMorgan Chase, and Palo Alto. With the creation of ATT&CK, MITRE is partnering with the cyber community to fulfill its mission to solve problems for a safer world. Using Adversary Behavior to Strengthen Cyber Defense Get Started with ATT&CK Join the ATT&CK Community MITRE encourages other researchers, analysts and cyber defenders to join our community and contribute new techniques and information. Finding Gaps in Defense Comparing APT 28 to Deep Panda MITRE ATT&CK Resources attack.mitre.org • Access ATT&CK technical information • Contribute to ATT&CK • Follow our blog • Watch ATT&CK presentations @MITREattack Follow us on Twitter for the latest news. attack.mitre.org
- 2. The MITRE ATT&CK™ Enterprise Framework attack.mitre.org © 2019 The MITRE Corporation. All rights reserved. Approved for Public Release; Distribution Unlimited. Case Number 15-1288. Ini�al Access Execu�on Persistence Privilege Escala�on Defense Evasion Creden�alAccess Discovery Lateral Movement Collec�on Exfiltra�on Command and Control Valid Accounts Scheduled Task XSL Script Processing Network Sniffing Windows Remote Management Video Capture Scheduled Transfer Web Service Trusted Rela�onship Trap Process Injec�on Two-Factor Authen�ca�on Intercep�on System Time Discovery Screen Capture Exfiltra�on Over Physical Medium Uncommonly Used Port Supply Chain Compromise LSASS Driver Extra Window Memory Injec�on System Service Discovery Third-party So�ware Man in the Browser Standard Non-Applica�on Layer Protocol Spearphishing via Service Local Job Scheduling Bypass User Account Control Private Keys System Owner/User Discovery Taint Shared Content Input Capture Exfiltra�on Over Command and Control Channel Spearphishing Link Launchctl Access Token Manipula�on Password Filter DLL SSH Hijacking Email Collec�on Standard Applica�on Layer Protocol Spearphishing A�achment XSL Script Processing Valid Accounts LLMNR/NBT-NS Poisoning System Network Configura�on Discovery Shared Webroot Data Staged Data Transfer Size Limits Replica�on Through Removable Media Windows Remote Management Plist Modifica�on Keychain Replica�on Through Removable Media Data from Removable Media Data Encrypted Remote Access Tools Image File Execu�on Op�ons Injec�on Kerberoas�ng Security So�ware Discovery Data from Network Shared Drive Data Compressed Port Knocking Exploit Public-Facing Applica�on User Execu�on DLL Search Order Hijacking Input Prompt Remote System Discovery Remote File Copy Automated Exfiltra�on Mul�layer Encryp�on Trusted Developer U�li�es Web Shell Web Service Input Capture Query Registry Remote Desktop Protocol Data from Informa�on Repositories Exfiltra�on Over Other Network Medium Mul�band Communica�on Hardware Addi�ons Third-party So�ware Startup Items Trusted Developer U�li�es Hooking Process Discovery Pass the Ticket Mul�-Stage Channels Drive-by Compromise Space a�er Filename Setuid and Setgid Timestomp Forced Authen�ca�on Permission Groups Discovery Pass the Hash Automated Collec�on Exfiltra�on Over Alterna�ve Protocol Mul�-hop Proxy Source Service Registry Permissions Weakness Template Injec�on Exploita�on for Creden�al Access Peripheral Device Discovery Logon Scripts Audio Capture Fallback Channels Signed Script Proxy Execu�on Port Monitors Space a�er Filename Password Policy Discovery Exploita�on of Remote Services Data from Local System Domain Fron�ng Path Intercep�on So�ware Packing Creden�als in Files Network Share Discovery Clipboard Data Data Obfusca�on Service Execu�on New Service SIP and Trust Provider Hijacking Creden�al Dumping Network Service Scanning Applica�on Deployment So�ware Data Encoding Scrip�ng Launch Daemon Brute Force File and Directory Discovery Custom Cryptographic Protocol Rundll32 Hooking Signed Binary Proxy Execu�on Bash History Browser Bookmark Discovery Windows Admin Shares Regsvr32 File System Permissions Weakness Account Manipula�on Applica�on Window Discovery Remote Services Connec�on Proxy Regsvcs/Regasm Dylib Hijacking Rundll32 Securityd Memory Distributed Component Object Model Communica�on Through Removable Media PowerShell Applica�on Shimming Rootkit Creden�als in Registry System Network Connec�ons Discovery Mshta AppInit DLLs Regsvr32 AppleScript Standard Cryptographic Protocol InstallU�l AppCert DLLs Regsvcs/Regasm System Informa�on Discovery Graphical User Interface Accessibility Features Redundant Access Remote File Copy Exploita�on for Client Execu�on Winlogon Helper DLL Sudo Caching Process Hollowing Account Discovery Custom Command and Control Protocol Windows Management Instrumenta�on Event Subscrip�on Sudo Process Doppelganging Execu�on through API SID-History Injec�on Port Knocking Commonly Used Port Dynamic Data Exchange Exploita�on for Privilege Escala�on Obfuscated Files or Informa�on Control Panel Items SIP and Trust Provider Hijacking Compiled HTML File Network Share Connec�on Removal Command-Line Interface Security Support Provider CMSTP Screensaver Modify Registry AppleScript Registry Run Keys / Startup Folder Masquerading Windows Management Instrumenta�on LC_MAIN Hijacking Re-opened Applica�ons Launchctl Signed Binary Proxy Execu�on Rc.common InstallU�l Port Knocking Install Root Cer�ficate Execu�on through Module Load Office Applica�on Startup Indirect Command Execu�on Netsh Helper DLL Component Firmware Modify Exis�ng Service Indicator Removal from Tools Logon Scripts Indicator Blocking Login Item HISTCONTROL LC_LOAD_DYLIB Addi�on Hidden Window Launch Agent Hidden Users Kernel Modules and Extensions Hidden Files and Directories Gatekeeper Bypass Hidden Files and Directories File System Logical Offsets External Remote Services File Permissions Modifica�on Create Account File Dele�on Component Object Model Hijacking Exploita�on for Defense Evasion Change Default File Associa�on Disabling Security Tools Deobfuscate/Decode Files or Informa�on Bootkit BITS Jobs Control Panel Items Authen�ca�on Package Component Object Model Hijacking Account Manipula�on .bash_profile and .bashrc Compiled HTML File Time Providers Code Signing System Firmware CMSTP Shortcut Modifica�on Clear Command History Redundant Access BITS Jobs Hypervisor Signed Script Proxy Execu�on Component Firmware Scrip�ng Browser Extensions NTFS File A�ributes Mshta Indicator Removal on Host DLL Side-Loading DCShadow