Ernst & Young visuals security survey 2012
•Als PPTX, PDF herunterladen•
0 gefällt mir•446 views
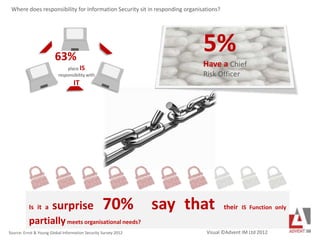
Risk and Security not always aligned. Not enough non IT focus on security. Hardly surprising that organisational Information Security needs are not being met in enough organisations.
Melden
Teilen
Melden
Teilen
Empfohlen
Weitere ähnliche Inhalte
Was ist angesagt?
Was ist angesagt? (20)
Sécurité Mobile : Votre Entreprise est-elle préparée pour 2020?

Sécurité Mobile : Votre Entreprise est-elle préparée pour 2020?
Understanding the Data & Analytics Specific Purchase Process [Infographic]![Understanding the Data & Analytics Specific Purchase Process [Infographic]](data:image/gif;base64,R0lGODlhAQABAIAAAAAAAP///yH5BAEAAAAALAAAAAABAAEAAAIBRAA7)
![Understanding the Data & Analytics Specific Purchase Process [Infographic]](data:image/gif;base64,R0lGODlhAQABAIAAAAAAAP///yH5BAEAAAAALAAAAAABAAEAAAIBRAA7)
Understanding the Data & Analytics Specific Purchase Process [Infographic]
The Cyber Security Readiness of Canadian Organizations

The Cyber Security Readiness of Canadian Organizations
Executive Summary of the 2016 Scalar Security Study

Executive Summary of the 2016 Scalar Security Study
SVB Cybersecurity Impact on Innovation Report - Overview

SVB Cybersecurity Impact on Innovation Report - Overview
2017 Role & Influence of the Technology Decision-Maker

2017 Role & Influence of the Technology Decision-Maker
How to Connect Your Server Room to the Board Room – Before a Data Breach Occurs

How to Connect Your Server Room to the Board Room – Before a Data Breach Occurs
Andere mochten auch
Andere mochten auch (18)
Ähnlich wie Ernst & Young visuals security survey 2012
Estudio de Russell Reynolds Associates sobre ciberseguridad que explora la importancia de la relación entre el Chief Information Security Officer y el Consejo de Administración. Cyber security: Five leadership issues worthy of board and executive attention

Cyber security: Five leadership issues worthy of board and executive attentionRamón Gómez de Olea y Bustinza
Russell Reynolds Associates aborda cinco cuestiones de liderazgo en materia de ciberseguridad que los Consejos de Administración y los ejecutivos deben preguntarse. Estas cuestiones abarcan diversos aspectos, desde el nivel de preparación del Consejo hasta la gestión del talento para proteger el negocio de una forma integral.Cyber security: five leadership issues worthy of Board and executive attention

Cyber security: five leadership issues worthy of Board and executive attentionRamón Gómez de Olea y Bustinza
Incident Response Management: How European Enterprises are Planning to Prepare for a Cyber Security BreachBreaches Are Bad for Business. How Will You Detect and Respond to Your Next C...

Breaches Are Bad for Business. How Will You Detect and Respond to Your Next C...Hewlett Packard Enterprise Business Value Exchange
According to the HP sponsored1 2014 Executive Breach Preparedness Research Report, more than 70 percent of executives think that their organization only partially understands the information risks they’re exposed to as a result of a breach. To add to that, less than half of c-suite and board-level executives are kept informed about the breach response process.
This report also found that business leadership knows that their involvement in data breach incident response is important – but they don’t believe, generally, that they are actually accountable for data breaches. In fact, only 45% stated that they think they are accountable for data breaches in their organization.
Read the full report for more insights.2014 Executive Breach Preparedness Research Report

2014 Executive Breach Preparedness Research ReportHewlett Packard Enterprise Business Value Exchange
Most Commonly Cited Area with a Problematic Shortage of IT Skills for 4th Consecutive Year: Information SecurityESG TechTruth: Advanced Persistent Threat: The Pervasive IT Security Skills S...

ESG TechTruth: Advanced Persistent Threat: The Pervasive IT Security Skills S...Enterprise Strategy Group
1. How often do you see non-sanctioned cloud services in use?
2. Are we protecting ourselves against insider threats?
3. Do we have a cyber security task force in place?
4. Is our BYOD policy secure?
5. Do you feel limited by your security budget or staff size?5 Questions Executives Should Be Asking Their Security Teams 

5 Questions Executives Should Be Asking Their Security Teams Arun Chinnaraju MBA, PMP, CSM, CSPO, SA
Ähnlich wie Ernst & Young visuals security survey 2012 (20)
Cyber security: Five leadership issues worthy of board and executive attention

Cyber security: Five leadership issues worthy of board and executive attention
Cyber security: five leadership issues worthy of Board and executive attention

Cyber security: five leadership issues worthy of Board and executive attention
Build a Business-Driven IT Risk Management Program

Build a Business-Driven IT Risk Management Program
Breaches Are Bad for Business. How Will You Detect and Respond to Your Next C...

Breaches Are Bad for Business. How Will You Detect and Respond to Your Next C...
2014 Executive Breach Preparedness Research Report

2014 Executive Breach Preparedness Research Report
Insights from the IBM Chief Information Security Officer Assessment

Insights from the IBM Chief Information Security Officer Assessment
Government and Education Webinar: Public Sector Cybersecurity Survey - What I...

Government and Education Webinar: Public Sector Cybersecurity Survey - What I...
01-Build-an-IT-Risk-Management-Program--Phases-1-3.pptx

01-Build-an-IT-Risk-Management-Program--Phases-1-3.pptx
ESG TechTruth: Advanced Persistent Threat: The Pervasive IT Security Skills S...

ESG TechTruth: Advanced Persistent Threat: The Pervasive IT Security Skills S...
Cyber Security in the Digital Age: A Survey and its Analysis

Cyber Security in the Digital Age: A Survey and its Analysis
5 Questions Executives Should Be Asking Their Security Teams 

5 Questions Executives Should Be Asking Their Security Teams
Accenture 2015 Global Risk Management Study: Insurance Report Key Findings an...

Accenture 2015 Global Risk Management Study: Insurance Report Key Findings an...
Kürzlich hochgeladen
Kürzlich hochgeladen (20)
Cloud Frontiers: A Deep Dive into Serverless Spatial Data and FME

Cloud Frontiers: A Deep Dive into Serverless Spatial Data and FME
Modular Monolith - a Practical Alternative to Microservices @ Devoxx UK 2024

Modular Monolith - a Practical Alternative to Microservices @ Devoxx UK 2024
AWS Community Day CPH - Three problems of Terraform

AWS Community Day CPH - Three problems of Terraform
WSO2's API Vision: Unifying Control, Empowering Developers

WSO2's API Vision: Unifying Control, Empowering Developers
Vector Search -An Introduction in Oracle Database 23ai.pptx

Vector Search -An Introduction in Oracle Database 23ai.pptx
Why Teams call analytics are critical to your entire business

Why Teams call analytics are critical to your entire business
Connector Corner: Accelerate revenue generation using UiPath API-centric busi...

Connector Corner: Accelerate revenue generation using UiPath API-centric busi...
Web Form Automation for Bonterra Impact Management (fka Social Solutions Apri...

Web Form Automation for Bonterra Impact Management (fka Social Solutions Apri...
ICT role in 21st century education and its challenges

ICT role in 21st century education and its challenges
ProductAnonymous-April2024-WinProductDiscovery-MelissaKlemke

ProductAnonymous-April2024-WinProductDiscovery-MelissaKlemke
EMPOWERMENT TECHNOLOGY GRADE 11 QUARTER 2 REVIEWER

EMPOWERMENT TECHNOLOGY GRADE 11 QUARTER 2 REVIEWER
Apidays New York 2024 - Passkeys: Developing APIs to enable passwordless auth...

Apidays New York 2024 - Passkeys: Developing APIs to enable passwordless auth...
How to Troubleshoot Apps for the Modern Connected Worker

How to Troubleshoot Apps for the Modern Connected Worker
Ernst & Young visuals security survey 2012
- 1. 63% place IS responsibility with IT 5% Have a Chief Risk Officer Source: Ernst & Young Global Information Security Survey 2012 Where does responsibility for Information Security sit in responding organisations? Is it a surprise 70% say that their IS Function only partiallymeets organisational needs? Visual ©Advent IM Ltd 2012
- 2. 46% neveror almost never discuss Information Security at top governing structure of their organisation 56% 42% 38% aligned to IT Strategyaligned to Business Strategyaligned to Risk Appetit how is Information Security aligned in your organisation?
- 3. planned spend increase of 5-15% planned spend increase of 25% or more With so little boardroom involvement and so little specialist security resourcing, how will any additional spending be effectively appropriately controlled?
- 4. 63% place IS responsibility with IT 5% Have a Chief Risk Officer Source: Ernst & Young Global Information Security Survey 2012 Where does responsibility for Information Security sit in responding organisations? Is it a surprise 70% say that their IS Function only partiallymeets organisational needs?
