Global tech project list
•Als DOC, PDF herunterladen•
0 gefällt mir•606 views
GlobaTech Solutions Call 09423222949 // 09823467071
Melden
Teilen
Melden
Teilen
Empfohlen
Empfohlen
Greencornertech,Ieee 2015-16 Projects,Nellore,AndhraPradeshCSE Java ieee titles 2015-16,Live Projects,Green Corner Tech,Nellore,Andhra ...

CSE Java ieee titles 2015-16,Live Projects,Green Corner Tech,Nellore,Andhra ...Green Corner Tech,Nellore
Weitere ähnliche Inhalte
Was ist angesagt?
Was ist angesagt? (13)
Cloud computing titles list dream web techno solutions

Cloud computing titles list dream web techno solutions
cse projects,Dot net ieee projects 2015,green corner tech,nellore

cse projects,Dot net ieee projects 2015,green corner tech,nellore
Ähnlich wie Global tech project list
Greencornertech,Ieee 2015-16 Projects,Nellore,AndhraPradeshCSE Java ieee titles 2015-16,Live Projects,Green Corner Tech,Nellore,Andhra ...

CSE Java ieee titles 2015-16,Live Projects,Green Corner Tech,Nellore,Andhra ...Green Corner Tech,Nellore
DOTNET/JAVA/MATLAB/VLSI/NS2/EMBEDDED IEEE 2014 PROJECTS FOR ME/BE/B.TECH STUDENTS. FINAL YEAR 2014 PROJECTS FOR CSE/IT/ECE/EEE/ STUDENTS IN CHENNAI (S3 INFOTECH : 09884848198).
Final year IEEE 2014 projects for BE, BTech, ME, MTech &PHD Students (09884848198 : S3 Infotech)
Dear Students,
Greetings from S3 INFOTECH (0988 48 48 198). We are doing Final year (IEEE & APPLICATION) projects in DOTNET, JAVA, MATLAB, ANDROID, VLSI, NS2, EMBEDDED SYSTEMS and POWER ELECTRONICS.
For B.E, M.E, B.Tech, M.Tech, MCA, M.Sc, & PHD Students.
We implement your own IEEE concepts also in ALL Technologies. We are giving support for Journal Arrangement & Publication also.
Send your IEEE base paper to yes3info@gmail.com (or) info@s3computers.com.
To Register your project: www.s3computers.com
We are providing Projects in
• DOT NET
• JAVA / J2EE / J2ME
• EMBEDDED & POWER ELECTRONICS
• MATLAB
• NS2
• VLSI
• NETWORKING
• HADOOP / Bigdata
• Android
• PHP
JAVA IEEE 2014 PROJECTS FOR ME/BE/B.TECH STUDENTS. FINAL YEAR 2014 PROJECTS F...

JAVA IEEE 2014 PROJECTS FOR ME/BE/B.TECH STUDENTS. FINAL YEAR 2014 PROJECTS F...S3 Infotech IEEE Projects
Ähnlich wie Global tech project list (20)
IEEE projects java and dotnet for BE BTECH ME MTECH MCA MCS Diploma

IEEE projects java and dotnet for BE BTECH ME MTECH MCA MCS Diploma
CSE Java ieee titles 2015-16,Live Projects,Green Corner Tech,Nellore,Andhra ...

CSE Java ieee titles 2015-16,Live Projects,Green Corner Tech,Nellore,Andhra ...
Ieee projects-in-pondicherry | 2015 ieee projects in pondicherry

Ieee projects-in-pondicherry | 2015 ieee projects in pondicherry
Bulk ieee projects | bulk ieee projects in pondicherry

Bulk ieee projects | bulk ieee projects in pondicherry
JAVA IEEE 2014 PROJECTS FOR ME/BE/B.TECH STUDENTS. FINAL YEAR 2014 PROJECTS F...

JAVA IEEE 2014 PROJECTS FOR ME/BE/B.TECH STUDENTS. FINAL YEAR 2014 PROJECTS F...
IEEE JAVA DOTNET ANDROID PROJECT TITLES 2014 - 2015 

IEEE JAVA DOTNET ANDROID PROJECT TITLES 2014 - 2015
Ieee 2020 21 java dotnet in pondicherry,final year projects in pondicherry,pr...

Ieee 2020 21 java dotnet in pondicherry,final year projects in pondicherry,pr...
Kürzlich hochgeladen
💉💊+971581248768>> SAFE AND ORIGINAL ABORTION PILLS FOR SALE IN DUBAI AND ABUDHABI}}+971581248768
+971581248768 Mtp-Kit (500MG) Prices » Dubai [(+971581248768**)] Abortion Pills For Sale In Dubai, UAE, Mifepristone and Misoprostol Tablets Available In Dubai, UAE CONTACT DR.Maya Whatsapp +971581248768 We Have Abortion Pills / Cytotec Tablets /Mifegest Kit Available in Dubai, Sharjah, Abudhabi, Ajman, Alain, Fujairah, Ras Al Khaimah, Umm Al Quwain, UAE, Buy cytotec in Dubai +971581248768''''Abortion Pills near me DUBAI | ABU DHABI|UAE. Price of Misoprostol, Cytotec” +971581248768' Dr.DEEM ''BUY ABORTION PILLS MIFEGEST KIT, MISOPROTONE, CYTOTEC PILLS IN DUBAI, ABU DHABI,UAE'' Contact me now via What's App…… abortion Pills Cytotec also available Oman Qatar Doha Saudi Arabia Bahrain Above all, Cytotec Abortion Pills are Available In Dubai / UAE, you will be very happy to do abortion in Dubai we are providing cytotec 200mg abortion pill in Dubai, UAE. Medication abortion offers an alternative to Surgical Abortion for women in the early weeks of pregnancy. We only offer abortion pills from 1 week-6 Months. We then advise you to use surgery if its beyond 6 months. Our Abu Dhabi, Ajman, Al Ain, Dubai, Fujairah, Ras Al Khaimah (RAK), Sharjah, Umm Al Quwain (UAQ) United Arab Emirates Abortion Clinic provides the safest and most advanced techniques for providing non-surgical, medical and surgical abortion methods for early through late second trimester, including the Abortion By Pill Procedure (RU 486, Mifeprex, Mifepristone, early options French Abortion Pill), Tamoxifen, Methotrexate and Cytotec (Misoprostol). The Abu Dhabi, United Arab Emirates Abortion Clinic performs Same Day Abortion Procedure using medications that are taken on the first day of the office visit and will cause the abortion to occur generally within 4 to 6 hours (as early as 30 minutes) for patients who are 3 to 12 weeks pregnant. When Mifepristone and Misoprostol are used, 50% of patients complete in 4 to 6 hours; 75% to 80% in 12 hours; and 90% in 24 hours. We use a regimen that allows for completion without the need for surgery 99% of the time. All advanced second trimester and late term pregnancies at our Tampa clinic (17 to 24 weeks or greater) can be completed within 24 hours or less 99% of the time without the need surgery. The procedure is completed with minimal to no complications. Our Women's Health Center located in Abu Dhabi, United Arab Emirates, uses the latest medications for medical abortions (RU-486, Mifeprex, Mifegyne, Mifepristone, early options French abortion pill), Methotrexate and Cytotec (Misoprostol). The safety standards of our Abu Dhabi, United Arab Emirates Abortion Doctors remain unparalleled. They consistently maintain the lowest complication rates throughout the nation. Our Physicians and staff are always available to answer questions and care for women in one of the most difficult times in their lives. The decision to have an abortion at the Abortion Cl+971581248768>> SAFE AND ORIGINAL ABORTION PILLS FOR SALE IN DUBAI AND ABUDHA...

+971581248768>> SAFE AND ORIGINAL ABORTION PILLS FOR SALE IN DUBAI AND ABUDHA...?#DUbAI#??##{{(☎️+971_581248768%)**%*]'#abortion pills for sale in dubai@
Kürzlich hochgeladen (20)
Bajaj Allianz Life Insurance Company - Insurer Innovation Award 2024

Bajaj Allianz Life Insurance Company - Insurer Innovation Award 2024
Automating Google Workspace (GWS) & more with Apps Script

Automating Google Workspace (GWS) & more with Apps Script
Strategize a Smooth Tenant-to-tenant Migration and Copilot Takeoff

Strategize a Smooth Tenant-to-tenant Migration and Copilot Takeoff
Apidays New York 2024 - The Good, the Bad and the Governed by David O'Neill, ...

Apidays New York 2024 - The Good, the Bad and the Governed by David O'Neill, ...
+971581248768>> SAFE AND ORIGINAL ABORTION PILLS FOR SALE IN DUBAI AND ABUDHA...

+971581248768>> SAFE AND ORIGINAL ABORTION PILLS FOR SALE IN DUBAI AND ABUDHA...
Cloud Frontiers: A Deep Dive into Serverless Spatial Data and FME

Cloud Frontiers: A Deep Dive into Serverless Spatial Data and FME
Understanding Discord NSFW Servers A Guide for Responsible Users.pdf

Understanding Discord NSFW Servers A Guide for Responsible Users.pdf
Repurposing LNG terminals for Hydrogen Ammonia: Feasibility and Cost Saving

Repurposing LNG terminals for Hydrogen Ammonia: Feasibility and Cost Saving
TrustArc Webinar - Stay Ahead of US State Data Privacy Law Developments

TrustArc Webinar - Stay Ahead of US State Data Privacy Law Developments
HTML Injection Attacks: Impact and Mitigation Strategies

HTML Injection Attacks: Impact and Mitigation Strategies
Why Teams call analytics are critical to your entire business

Why Teams call analytics are critical to your entire business
Apidays New York 2024 - The value of a flexible API Management solution for O...

Apidays New York 2024 - The value of a flexible API Management solution for O...
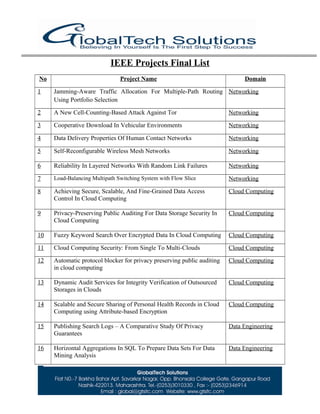
Global tech project list
- 1. IEEE Projects Final List No Project Name Domain 1 Jamming-Aware Traffic Allocation For Multiple-Path Routing Using Portfolio Selection Networking 2 A New Cell-Counting-Based Attack Against Tor Networking 3 Cooperative Download In Vehicular Environments Networking 4 Data Delivery Properties Of Human Contact Networks Networking 5 Self-Reconfigurable Wireless Mesh Networks Networking 6 Reliability In Layered Networks With Random Link Failures Networking 7 Load-Balancing Multipath Switching System with Flow Slice Networking 8 Achieving Secure, Scalable, And Fine-Grained Data Access Control In Cloud Computing Cloud Computing 9 Privacy-Preserving Public Auditing For Data Storage Security In Cloud Computing Cloud Computing 10 Fuzzy Keyword Search Over Encrypted Data In Cloud Computing Cloud Computing 11 Cloud Computing Security: From Single To Multi-Clouds Cloud Computing 12 Automatic protocol blocker for privacy preserving public auditing in cloud computing Cloud Computing 13 Dynamic Audit Services for Integrity Verification of Outsourced Storages in Clouds Cloud Computing 14 Scalable and Secure Sharing of Personal Health Records in Cloud Computing using Attribute-based Encryption Cloud Computing 15 Publishing Search Logs – A Comparative Study Of Privacy Guarantees Data Engineering 16 Horizontal Aggregations In SQL To Prepare Data Sets For Data Mining Analysis Data Engineering
- 2. 17 Closing The Loop In Webpage Understanding Data Engineering 18 Automatic Discovery Of Personal Name Aliases From The Web Data Engineering 19 A Personalized Ontology Model For Web Information Gathering Data Engineering 20 Scalable And Secure Sharing Of Personal Health Records In Cloud Computing Using Attribute-Based Encryption Data Engineering 21 Efficient Computation of Range Aggregates against Uncertain Location Based Queries Data Engineering 22 Hiding Sensitive Association Rule For Privacy Preservation Security 23 Authentication Schemes For Session Passwords Using Color And Images Security 24 Separable Reversible Data Hiding In Encrypted Image Security 25 Implicit Password Authentication System Security 26 Data Hiding In Motion Vectors Of Compressed Video Based On Their Associated Prediction Error Security 27 Defenses Against Large Scale Online Password Guessing Attacks By Using Persuasive Click Points Security 28 A Probabilistic Model Of (T, N) Visual Cryptography Scheme With Dynamic Group Security
- 5. 29 Robust Correlation Of Encrypted Attack Traffic Through Stepping Stones By Flow Watermarking Image Processing 30 On the Selection of Optimal Feature Region Set for Robust Digital Image Watermarking Image Processing 31 Semi supervised Biased Maximum Margin Analysis For Interactive Image Retrieval Image Processing 32 Three-Dimensional Password For More Secure Authentication Image Processing 33 Optimal Stochastic Location Updates In Mobile Ad Hoc Networks Mobile Computing 34 Mabs: Multicast Authentication Based On Batch Signature Mobile Computing 35 Random Cast: An Energy Efficient Communication Scheme For Mobile Ad Hoc Networks Mobile Computing 36 Monitoring Service Systems From A Language-Action Perspective Service Computing 37 Online Intrusion Alert Aggregation With Generative Data Stream Modeling Service Computing 38 Dynamic Authentication For Cross-Realm SOA-Based Business Processes Service Computing 39 Identifying Content For Planned Events Across Social Media Sites Service Computing 40 Bridging Socially-Enhanced Virtual Communities Service Computing 41 Automated Certification For Compliant Cloud-Based Business Processes Data Mining 42 Slow Adaptive OFDMA Systems Through Chance Constrained Programming Signal Processing 43 Exploiting Dynamic Resource Allocation For Efficient Parallel Data Processing In The Cloud Parallel & Distributed 44 Anonymous Query Processing In Road Network Parallel & Distributed 45 Throughput Optimization In High Speed Downlink Packet Access (HSDPA) Wireless Communications 46 Analysis of P2P File Sharing Network Wireless Communications 47 Digital Image Watermarking Image Processing 48 Load-Balancing Multipath Switching System with Flow Slice Data Mining 49 Vulnerability Analysis in SOA-based Business Processes Data Mining 50 A Fast Clustering-Based Feature Subset 51 A Load Balancing Model Based on Cloud Partitioningfor the Public Cloud
