Symantec Endpoint Protection
•
0 gefällt mir•2,826 views
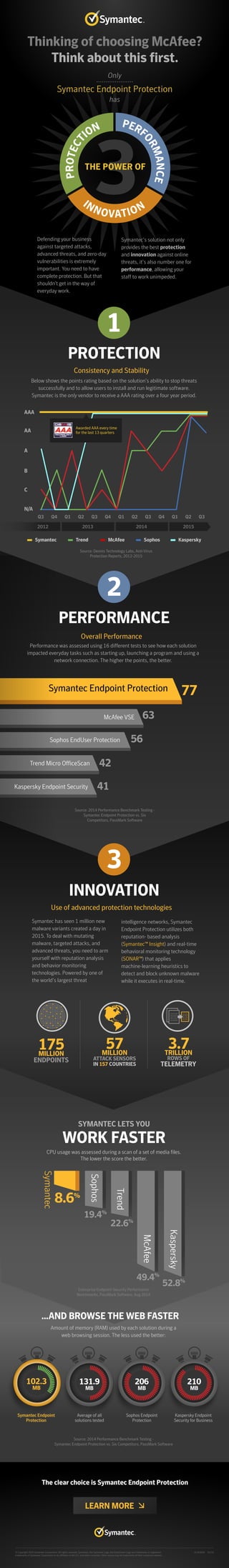
Considering endpoint protection? Only Symantec has the power of three: protection, performance and innovation.
Melden
Teilen
Melden
Teilen
Downloaden Sie, um offline zu lesen
Empfohlen
Empfohlen
Weitere ähnliche Inhalte
Was ist angesagt?
Was ist angesagt? (20)
TECHNICAL BRIEF: Using Symantec Endpoint Protection 12.1 to Protect Against A...

TECHNICAL BRIEF: Using Symantec Endpoint Protection 12.1 to Protect Against A...
The Importance of Endpoint Protection - Featuring SEP 14

The Importance of Endpoint Protection - Featuring SEP 14
Cyber Tech Israel 2016: Advanced Threat Protection Technical Overview

Cyber Tech Israel 2016: Advanced Threat Protection Technical Overview
Symantec Endpoint Protection Enterprise Edition Best Practices Guidelines

Symantec Endpoint Protection Enterprise Edition Best Practices Guidelines
Avoid Meltdown from the Spectre - How to measure impact and track remediation

Avoid Meltdown from the Spectre - How to measure impact and track remediation
A Buyers Guide to Investing in Endpoint Detection and Response for Enterprise...

A Buyers Guide to Investing in Endpoint Detection and Response for Enterprise...
So You Got That SIEM. NOW What Do You Do? by Dr. Anton Chuvakin

So You Got That SIEM. NOW What Do You Do? by Dr. Anton Chuvakin
Rothke secure360 building a security operations center (soc)

Rothke secure360 building a security operations center (soc)
Top 10 tips for effective SOC/NOC collaboration or integration

Top 10 tips for effective SOC/NOC collaboration or integration
Introducing New Kaspersky Endpoint Security for Business - ENGLISH

Introducing New Kaspersky Endpoint Security for Business - ENGLISH
AlienVault Partner Update: So Many Security Products to Sell to My Customers…...

AlienVault Partner Update: So Many Security Products to Sell to My Customers…...
Layered Approach - Information Security Recommendations

Layered Approach - Information Security Recommendations
kaspersky presentation for palette business solution June 2016 v1.0.

kaspersky presentation for palette business solution June 2016 v1.0.
Andere mochten auch
Andere mochten auch (16)
Better Backup For All Symantec Appliances NetBackup 5220 Backup Exec 3600 May...

Better Backup For All Symantec Appliances NetBackup 5220 Backup Exec 3600 May...
Symantec Endpoint Protection - Product Positioning

Symantec Endpoint Protection - Product Positioning
Introduction to Symantec Endpoint Management75.pptx

Introduction to Symantec Endpoint Management75.pptx
IT-Centric Disaster Recovery & Business Continuity

IT-Centric Disaster Recovery & Business Continuity
Unlocking the Value of Delivering Services Event – Monday 18th March 2013 – S...

Unlocking the Value of Delivering Services Event – Monday 18th March 2013 – S...
Ähnlich wie Symantec Endpoint Protection
Ähnlich wie Symantec Endpoint Protection (20)
Key Strategies to Address Rising Application Risk in Your Enterprise

Key Strategies to Address Rising Application Risk in Your Enterprise
What We Learned as the First and Best Customer of Symantec ATP

What We Learned as the First and Best Customer of Symantec ATP
What the New OWASP Top 10 2013 and Latest X-Force Report Mean for App Sec

What the New OWASP Top 10 2013 and Latest X-Force Report Mean for App Sec
7 Reasons Your Applications are Attractive to Adversaries

7 Reasons Your Applications are Attractive to Adversaries
Oliver Schuermann - Integrated Software in Networking - the Mystery of SDN

Oliver Schuermann - Integrated Software in Networking - the Mystery of SDN
Application Hackers Have A Handbook. Why Shouldn't You?

Application Hackers Have A Handbook. Why Shouldn't You?
It's Your Move: The Changing Game of Endpoint Security

It's Your Move: The Changing Game of Endpoint Security
комплексная защита от современных интернет угроз с помощью Check point sandblast

комплексная защита от современных интернет угроз с помощью Check point sandblast
Mehr von Symantec
Mehr von Symantec (20)
Symantec Enterprise Security Products are now part of Broadcom

Symantec Enterprise Security Products are now part of Broadcom
Symantec Webinar | National Cyber Security Awareness Month: Fostering a Secur...

Symantec Webinar | National Cyber Security Awareness Month: Fostering a Secur...
Symantec Webinar | National Cyber Security Awareness Month: Protect IT

Symantec Webinar | National Cyber Security Awareness Month: Protect IT
Symantec Webinar | National Cyber Security Awareness Month: Secure IT

Symantec Webinar | National Cyber Security Awareness Month: Secure IT
Symantec Webinar | National Cyber Security Awareness Month - Own IT

Symantec Webinar | National Cyber Security Awareness Month - Own IT
Symantec Webinar: Preparing for the California Consumer Privacy Act (CCPA)

Symantec Webinar: Preparing for the California Consumer Privacy Act (CCPA)
Symantec Webinar | How to Detect Targeted Ransomware with MITRE ATT&CK

Symantec Webinar | How to Detect Targeted Ransomware with MITRE ATT&CK
Symantec Webinar | Security Analytics Breached! Next Generation Network Foren...

Symantec Webinar | Security Analytics Breached! Next Generation Network Foren...
Symantec Webinar | Implementing a Zero Trust Framework to Secure Modern Workf...

Symantec Webinar | Implementing a Zero Trust Framework to Secure Modern Workf...
Symantec Webinar | Tips for Successful CASB Projects

Symantec Webinar | Tips for Successful CASB Projects
Symantec Webinar: What Cyber Threats Are Lurking in Your Network?

Symantec Webinar: What Cyber Threats Are Lurking in Your Network?
Symantec Best Practices for Cloud Security: Insights from the Front Lines

Symantec Best Practices for Cloud Security: Insights from the Front Lines
Symantec - The Importance of Building Your Zero Trust Program on a Solid Plat...

Symantec - The Importance of Building Your Zero Trust Program on a Solid Plat...
Symantec Webinar | Redefining Endpoint Security- How to Better Secure the End...

Symantec Webinar | Redefining Endpoint Security- How to Better Secure the End...
Symantec Webinar Using Advanced Detection and MITRE ATT&CK to Cage Fancy Bear

Symantec Webinar Using Advanced Detection and MITRE ATT&CK to Cage Fancy Bear
Kürzlich hochgeladen
Kürzlich hochgeladen (20)
Ensuring Technical Readiness For Copilot in Microsoft 365

Ensuring Technical Readiness For Copilot in Microsoft 365
DSPy a system for AI to Write Prompts and Do Fine Tuning

DSPy a system for AI to Write Prompts and Do Fine Tuning
TeamStation AI System Report LATAM IT Salaries 2024

TeamStation AI System Report LATAM IT Salaries 2024
"Debugging python applications inside k8s environment", Andrii Soldatenko

"Debugging python applications inside k8s environment", Andrii Soldatenko
How AI, OpenAI, and ChatGPT impact business and software.

How AI, OpenAI, and ChatGPT impact business and software.
Dev Dives: Streamline document processing with UiPath Studio Web

Dev Dives: Streamline document processing with UiPath Studio Web
New from BookNet Canada for 2024: BNC CataList - Tech Forum 2024

New from BookNet Canada for 2024: BNC CataList - Tech Forum 2024
Nell’iperspazio con Rocket: il Framework Web di Rust!

Nell’iperspazio con Rocket: il Framework Web di Rust!
Unraveling Multimodality with Large Language Models.pdf

Unraveling Multimodality with Large Language Models.pdf
The Fit for Passkeys for Employee and Consumer Sign-ins: FIDO Paris Seminar.pptx

The Fit for Passkeys for Employee and Consumer Sign-ins: FIDO Paris Seminar.pptx
(How to Program) Paul Deitel, Harvey Deitel-Java How to Program, Early Object...

(How to Program) Paul Deitel, Harvey Deitel-Java How to Program, Early Object...
Take control of your SAP testing with UiPath Test Suite

Take control of your SAP testing with UiPath Test Suite
Time Series Foundation Models - current state and future directions

Time Series Foundation Models - current state and future directions
WordPress Websites for Engineers: Elevate Your Brand

WordPress Websites for Engineers: Elevate Your Brand
Symantec Endpoint Protection
- 1. Symantec has seen 1 million new malware variants created a day in 2015. To deal with mutating malware, targeted attacks, and advanced threats, you need to arm yourself with reputation analysis and behavior monitoring technologies. Powered by one of the world’s largest threat intelligence networks, Symantec Endpoint Protection utilizes both reputation- based analysis (Symantec™ Insight) and real-time behavioral monitoring technology (SONAR™) that applies machine-learning heuristics to detect and block unknown malware while it executes in real-time. INNOVATION SYMANTEC LETS YOU WORK FASTER Use of advanced protection technologies THE POWER OF PROTECT ION PERF ORMANCE INNOVATION Below shows the points rating based on the solution’s ability to stop threats successfully and to allow users to install and run legitimate software. Symantec is the only vendor to receive a AAA rating over a four year period. Thinking of choosing McAfee? Think about this first. Symantec Endpoint Protection Only has Defending your business against targeted attacks, advanced threats, and zero-day vulnerabilities is extremely important. You need to have complete protection. But that shouldn’t get in the way of everyday work. Symantec’s solution not only provides the best protection and innovation against online threats, it’s also number one for performance, allowing your staff to work unimpeded. 1 PROTECTION McAfee VSE Sophos EndUser Protection Trend Micro OfficeScan Kaspersky Endpoint Security Symantec Endpoint Protection Source: Dennis Technology Labs, Anti-Virus Protection Reports, 2012-2015 2 PERFORMANCE AAA AA B C A N/A Q3 Q4 Q1 Q2 Q3 Q4 Q1 Q2 Q3 Q4 Q1 Q2 Q3 2012 2013 2014 2015 Symantec Trend McAfee Sophos Kaspersky Overall Performance Consistency and Stability 3 Source: 2014 Performance Benchmark Testing - Symantec Endpoint Protection vs. Six Competitors, PassMark Software 77 63 56 42 41 Performance was assessed using 16 different tests to see how each solution impacted everyday tasks such as starting up, launching a program and using a network connection. The higher the points, the better. Source: 2014 Performance Benchmark Testing - Symantec Endpoint Protection vs. Six Competitors, PassMark Software The clear choice is Symantec Endpoint Protection Average of all solutions tested Sophos Endpoint Protection 206 MB Kaspersky Endpoint Security for Business 210 MB 131.9 MB LEARN MORE 102.3 MB CPU usage was assessed during a scan of a set of media files. The lower the score the better. 175MILLION MILLION TRILLION ENDPOINTS 3.7 ROWS OF TELEMETRY 57 ATTACK SENSORS IN 157 COUNTRIES Awarded AAA every time for the last 13 quarters 1010100 0010001 0011001 0010000 1010100 0010001 0011001 0010000 Symantec 8.6% 19.4% 22.6% 52.8% Kaspersky 49.4% McAfee Sophos Trend Enterprise Endpoint Security Performance Benchmarks, PassMark Software, Aug 2014 © Copyright 2016 Symantec Corporation. All rights reserved. Symantec, the Symantec Logo, the Checkmark Logo are trademarks or registered trademarks of Symantec Corporation or its affiliates in the U.S. and other countries. Other names may be trademarks of their respective owners. 21363026 01/16 ...AND BROWSE THE WEB FASTER Amount of memory (RAM) used by each solution during a web browsing session. The less used the better: Symantec Endpoint Protection
