Emerging Tech: IOT, AI, Cloud, Cyber Security
•Download as PPTX, PDF•
2 likes•97 views
Emerging technologies discussed include Internet of Things (IOT), artificial intelligence, and cloud computing. IOT uses sensors to connect devices while AI uses machine learning and deep learning with sensor input. Cloud computing provides cost, speed, and scale benefits through public, private, and hybrid cloud models and services like infrastructure as a service (IaaS), platform as a service (PaaS), and software as a service (SaaS). Cyber security aims to protect data and programs through network, application, endpoint, and data security given increasing digital data storage and processing.
Report
Share
Report
Share
Recommended
More Related Content
What's hot
What's hot (20)
What is an IoT Gateway Device & Why It's Important?

What is an IoT Gateway Device & Why It's Important?
A 2020 Security strategy for Health Care Providers

A 2020 Security strategy for Health Care Providers
Agile Network India | Demystifying IoT | Himanshu Jain

Agile Network India | Demystifying IoT | Himanshu Jain
Drobics trustworthy io-t-for-industrial-applications

Drobics trustworthy io-t-for-industrial-applications
5th Meetup - Ethereum & IoT: examples, opportunities and IBM initiative

5th Meetup - Ethereum & IoT: examples, opportunities and IBM initiative
The Internet of Things - Solutions to Drive Business Transformation

The Internet of Things - Solutions to Drive Business Transformation
Internet of things architecture perspective - IndicThreads Conference

Internet of things architecture perspective - IndicThreads Conference
Identive | Press Release | Innovative Access Control Technology from Identive...

Identive | Press Release | Innovative Access Control Technology from Identive...
Similar to Emerging Tech: IOT, AI, Cloud, Cyber Security
Similar to Emerging Tech: IOT, AI, Cloud, Cyber Security (20)
IoT Security, Threats and Challenges By V.P.Prabhakaran

IoT Security, Threats and Challenges By V.P.Prabhakaran
School of Computer & Information SciencesITS-532 Cloud C.docx

School of Computer & Information SciencesITS-532 Cloud C.docx
Revealing the Potential and Risks From the Coming Together of IoT, AI, and C...

Revealing the Potential and Risks From the Coming Together of IoT, AI, and C...
DDS - The Proven Data Connectivity Standard for the Industrial IoT (IIoT)

DDS - The Proven Data Connectivity Standard for the Industrial IoT (IIoT)
Roberto Minerva: iot challenges - IoT Tunisia 2016

Roberto Minerva: iot challenges - IoT Tunisia 2016
Cybersecurity In IoT Challenges And Effective Strategies.pdf

Cybersecurity In IoT Challenges And Effective Strategies.pdf
Bhadale group of companies it cloud security catalogue

Bhadale group of companies it cloud security catalogue
More from suryateja swamy
More from suryateja swamy (6)
Recently uploaded
Recently uploaded (20)
DevoxxFR 2024 Reproducible Builds with Apache Maven

DevoxxFR 2024 Reproducible Builds with Apache Maven
Transcript: New from BookNet Canada for 2024: Loan Stars - Tech Forum 2024

Transcript: New from BookNet Canada for 2024: Loan Stars - Tech Forum 2024
Take control of your SAP testing with UiPath Test Suite

Take control of your SAP testing with UiPath Test Suite
Dev Dives: Streamline document processing with UiPath Studio Web

Dev Dives: Streamline document processing with UiPath Studio Web
A Journey Into the Emotions of Software Developers

A Journey Into the Emotions of Software Developers
The Ultimate Guide to Choosing WordPress Pros and Cons

The Ultimate Guide to Choosing WordPress Pros and Cons
Passkey Providers and Enabling Portability: FIDO Paris Seminar.pptx

Passkey Providers and Enabling Portability: FIDO Paris Seminar.pptx
TrustArc Webinar - How to Build Consumer Trust Through Data Privacy

TrustArc Webinar - How to Build Consumer Trust Through Data Privacy
Digital Identity is Under Attack: FIDO Paris Seminar.pptx

Digital Identity is Under Attack: FIDO Paris Seminar.pptx
Use of FIDO in the Payments and Identity Landscape: FIDO Paris Seminar.pptx

Use of FIDO in the Payments and Identity Landscape: FIDO Paris Seminar.pptx
"Subclassing and Composition – A Pythonic Tour of Trade-Offs", Hynek Schlawack

"Subclassing and Composition – A Pythonic Tour of Trade-Offs", Hynek Schlawack
Transcript: New from BookNet Canada for 2024: BNC CataList - Tech Forum 2024

Transcript: New from BookNet Canada for 2024: BNC CataList - Tech Forum 2024
Unraveling Multimodality with Large Language Models.pdf

Unraveling Multimodality with Large Language Models.pdf
Emerging Tech: IOT, AI, Cloud, Cyber Security
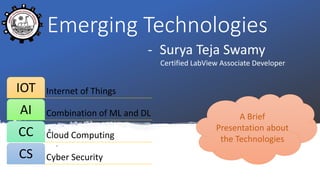
- 1. Emerging Technologies - Surya Teja Swamy Certified LabView Associate Developer Internet of ThingsIOT Combination of ML and DLAI Cloud ComputingCC Cyber SecurityCS A Brief Presentation about the Technologies
- 2. IOT Using all different sensors we can achieve IOT
- 3. AI 1 Artificial Intelligence is machine independent of Human 2 For that the basic tool is Machine Learning(ML), which later joins Deep Learning(DL) 3 With Combination of ML, DL and some input sensors AI can be achieved 4 Need different sort of Algorithms
- 5. Definition •Combination of technologies and process to protect data and programs from unauthorized access Importance •Different bodies such as government, military, corporate, financial…stores, process unprecedented data on computers, for safeguarding such Data Challenges •Network security •Application security •Endpoint security •Data security
Editor's Notes
- ML: Machine Learning; DL: Deep learning
- IOT: Getting environment connected through Internet; simply life connected with internet PIR Motion sensor; Photoelectric sensor; esp8266(internet sensor); HCSR04 (Ultrasonic Sensor)
- Reference: https://azure.microsoft.com/en-in/overview/what-is-cloud-computing/
- Reference: https://digitalguardian.com/blog/what-cyber-security
