Report
Share
Download to read offline
Recommended
Recommended
More Related Content
What's hot
What's hot (20)
How Banking as a Service Will Keep Banks Digitally Relevant and Growing

How Banking as a Service Will Keep Banks Digitally Relevant and Growing
Open Banking - Opening the door to Digital Transformation 

Open Banking - Opening the door to Digital Transformation
An Entry Point to Impactful Open Banking Architecture

An Entry Point to Impactful Open Banking Architecture
apidays LIVE LONDON - How APIs are changing the fintech world by Chirine Ben...

apidays LIVE LONDON - How APIs are changing the fintech world by Chirine Ben...
Open Banking APIs with case studies for senior stakeholders

Open Banking APIs with case studies for senior stakeholders
Open Banking - The Digital Transformation Opportunity in Disguise 

Open Banking - The Digital Transformation Opportunity in Disguise
APIsecure 2023 - Approaching Multicloud API Security USing Metacloud, David L...

APIsecure 2023 - Approaching Multicloud API Security USing Metacloud, David L...
The Power Of Open Banking Coupled With Artificial Intelligence

The Power Of Open Banking Coupled With Artificial Intelligence
Webinar: Practical use-cases to monetize Open Banking APIs

Webinar: Practical use-cases to monetize Open Banking APIs
BIAN Applied to Open Banking - Thoughts on Architecture and Implementation

BIAN Applied to Open Banking - Thoughts on Architecture and Implementation
Similar to open-banking-on-aws.pdf
Similar to open-banking-on-aws.pdf (20)
Nurturing a large GST ecosystem on AWS - Anil Sharma, Chicago

Nurturing a large GST ecosystem on AWS - Anil Sharma, Chicago
50 Extraordinary AWS CloudWatch Interview Questions & Answers.pdf

50 Extraordinary AWS CloudWatch Interview Questions & Answers.pdf
How To Build Credit Card Payment Processing Platform on AWS?

How To Build Credit Card Payment Processing Platform on AWS?
Secured Hosting of PCI DSS Compliant Web Applications on AWS

Secured Hosting of PCI DSS Compliant Web Applications on AWS
building-a-scalable-and-secure-multi-vpc-aws-network-infrastructure.pdf

building-a-scalable-and-secure-multi-vpc-aws-network-infrastructure.pdf
50 Extraordinary AWS CloudWatch Interview Questions & Answers.pdf

50 Extraordinary AWS CloudWatch Interview Questions & Answers.pdf
Microservice architecture-api-gateway-considerations

Microservice architecture-api-gateway-considerations
Cloud computing - Compute,Storage,Networking & Security

Cloud computing - Compute,Storage,Networking & Security
AWS re:Invent 2016: Understanding IoT Data: How to Leverage Amazon Kinesis in...

AWS re:Invent 2016: Understanding IoT Data: How to Leverage Amazon Kinesis in...
Recently uploaded
Booking open Available Pune Call Girls Koregaon Park 6297143586 Call Hot Indian Girls Waiting For You To Fuck
Booking Contact Details
WhatsApp Chat: +91-6297143586
pune Escort Service includes providing maximum physical satisfaction to their clients as well as engaging conversation that keeps your time enjoyable and entertaining. Plus they look fabulously elegant; making an impressionable.
Independent Escorts pune understands the value of confidentiality and discretion - they will go the extra mile to meet your needs. Simply contact them via text messaging or through their online profiles; they'd be more than delighted to accommodate any request or arrange a romantic date or fun-filled night together.
We provide -
01-may-2024(v.n)
Booking open Available Pune Call Girls Koregaon Park 6297143586 Call Hot Ind...

Booking open Available Pune Call Girls Koregaon Park 6297143586 Call Hot Ind...Call Girls in Nagpur High Profile
Booking open Available Pune Call Girls Pargaon 6297143586 Call Hot Indian Girls Waiting For You To Fuck
Booking Contact Details
WhatsApp Chat: +91-6297143586
pune Escort Service includes providing maximum physical satisfaction to their clients as well as engaging conversation that keeps your time enjoyable and entertaining. Plus they look fabulously elegant; making an impressionable.
Independent Escorts pune understands the value of confidentiality and discretion - they will go the extra mile to meet your needs. Simply contact them via text messaging or through their online profiles; they'd be more than delighted to accommodate any request or arrange a romantic date or fun-filled night together.
We provide -
01-may-2024(v.n)
Booking open Available Pune Call Girls Pargaon 6297143586 Call Hot Indian Gi...

Booking open Available Pune Call Girls Pargaon 6297143586 Call Hot Indian Gi...Call Girls in Nagpur High Profile
Call Girls Service Nashik Vaishnavi 7001305949 Independent Escort Service Nashik
Booking Contact Details
WhatsApp Chat: +91-7001035870
Nashik Escort Service includes providing maximum physical satisfaction to their clients as well as engaging conversation that keeps your time enjoyable and entertaining. Plus they look fabulously elegant; making an impressionable.
Independent Escorts Nashik understands the value of confidentiality and discretion - they will go the extra mile to meet your needs. Simply contact them via text messaging or through their online profiles; they'd be more than delighted to accommodate any request or arrange a romantic date or fun-filled night together.
We provide -
27-april-2024(v.n)
Call Girls Service Nashik Vaishnavi 7001305949 Independent Escort Service Nashik

Call Girls Service Nashik Vaishnavi 7001305949 Independent Escort Service NashikCall Girls in Nagpur High Profile
Welcome to the April edition of WIPAC Monthly, the magazine brought to you by Water Industry Process Automation & Control.
In this month's edition, along with the latest news from the industry we have articles on:
The use of artificial intelligence and self-service platforms to improve water sustainability
A feature article on measuring wastewater spills
An article on the National Underground Asset Register
Have a good month,
OliverWater Industry Process Automation & Control Monthly - April 2024

Water Industry Process Automation & Control Monthly - April 2024Water Industry Process Automation & Control
Call Girls Service Nagpur Tanvi Call 7001035870 Meet With Nagpur Escorts
Booking Contact Details
WhatsApp Chat: +91-7001035870
Nagpur Escort Service includes providing maximum physical satisfaction to their clients as well as engaging conversation that keeps your time enjoyable and entertaining. Plus they look fabulously elegant; making an impressionable.
Independent Escorts Nagpur understands the value of confidentiality and discretion - they will go the extra mile to meet your needs. Simply contact them via text messaging or through their online profiles; they'd be more than delighted to accommodate any request or arrange a romantic date or fun-filled night together.
We provide -
27-april-2024(v.n)
Call Girls Service Nagpur Tanvi Call 7001035870 Meet With Nagpur Escorts

Call Girls Service Nagpur Tanvi Call 7001035870 Meet With Nagpur EscortsCall Girls in Nagpur High Profile
Recently uploaded (20)
result management system report for college project

result management system report for college project
(ANVI) Koregaon Park Call Girls Just Call 7001035870 [ Cash on Delivery ] Pun...![(ANVI) Koregaon Park Call Girls Just Call 7001035870 [ Cash on Delivery ] Pun...](data:image/gif;base64,R0lGODlhAQABAIAAAAAAAP///yH5BAEAAAAALAAAAAABAAEAAAIBRAA7)
![(ANVI) Koregaon Park Call Girls Just Call 7001035870 [ Cash on Delivery ] Pun...](data:image/gif;base64,R0lGODlhAQABAIAAAAAAAP///yH5BAEAAAAALAAAAAABAAEAAAIBRAA7)
(ANVI) Koregaon Park Call Girls Just Call 7001035870 [ Cash on Delivery ] Pun...
Booking open Available Pune Call Girls Koregaon Park 6297143586 Call Hot Ind...

Booking open Available Pune Call Girls Koregaon Park 6297143586 Call Hot Ind...
Sheet Pile Wall Design and Construction: A Practical Guide for Civil Engineer...

Sheet Pile Wall Design and Construction: A Practical Guide for Civil Engineer...
The Most Attractive Pune Call Girls Manchar 8250192130 Will You Miss This Cha...

The Most Attractive Pune Call Girls Manchar 8250192130 Will You Miss This Cha...
Processing & Properties of Floor and Wall Tiles.pptx

Processing & Properties of Floor and Wall Tiles.pptx
BSides Seattle 2024 - Stopping Ethan Hunt From Taking Your Data.pptx

BSides Seattle 2024 - Stopping Ethan Hunt From Taking Your Data.pptx
VIP Call Girls Ankleshwar 7001035870 Whatsapp Number, 24/07 Booking

VIP Call Girls Ankleshwar 7001035870 Whatsapp Number, 24/07 Booking
MANUFACTURING PROCESS-II UNIT-1 THEORY OF METAL CUTTING

MANUFACTURING PROCESS-II UNIT-1 THEORY OF METAL CUTTING
Booking open Available Pune Call Girls Pargaon 6297143586 Call Hot Indian Gi...

Booking open Available Pune Call Girls Pargaon 6297143586 Call Hot Indian Gi...
Call Girls Service Nashik Vaishnavi 7001305949 Independent Escort Service Nashik

Call Girls Service Nashik Vaishnavi 7001305949 Independent Escort Service Nashik
Water Industry Process Automation & Control Monthly - April 2024

Water Industry Process Automation & Control Monthly - April 2024
Call Girls Service Nagpur Tanvi Call 7001035870 Meet With Nagpur Escorts

Call Girls Service Nagpur Tanvi Call 7001035870 Meet With Nagpur Escorts
open-banking-on-aws.pdf
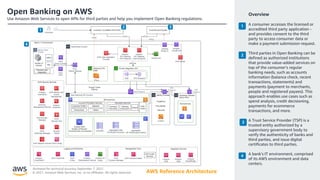
- 1. Reviewed for technical accuracy September 7, 2021 © 2021, Amazon Web Services, Inc. or its affiliates. All rights reserved. AWS Reference Architecture 2 Open Banking on AWS Use Amazon Web Services to open APIs for third parties and help you implement Open Banking regulations. 1 Overview A consumer accesses the licensed or accredited third party application - and provides consent to the third party to access consumer data or make a payment submission request. Third parties in Open Banking can be defined as authorized institutions that provide value-added services on top of the consumer’s regular banking needs, such as accounts information (balance check, recent transactions, statements) and payments (payment to merchants, people and registered payees). This approach enables use cases such as spend analysis, credit decisioning, payments for ecommerce transactions, and more. A Trust Service Provider (TSP) is a trusted entity authorized by a supervisory government body to verify the authenticity of banks and third parties, and issue digital certificates to third parties. A bank's IT environment, comprised of its AWS environment and data centers. 4 3 1 2 4 3
- 2. Reviewed for technical accuracy September 7, 2021 © 2021, Amazon Web Services, Inc. or its affiliates. All rights reserved. AWS Reference Architecture Open Banking on AWS Use Amazon Web Services to open APIs for third parties and help you implement Open Banking regulations. 2 1 Streaming technologies such as Apache Kafka and queueing mechanisms like message queue (MQ) send and receive all new and updated transactions between the core banking systems and AWS. The bank’s data center is connected to AWS using a combination of AWS Direct Connect and AWS Site-to- Site VPN. Two diverse AWS Direct Connect connections are recommended for maximum resiliency. AWS Transit Gateway serves as the central hub on AWS to manage interconnectivity between workloads running in different AWS accounts. It shares the AWS Direct Connect and VPN connection with other workloads in the bank. An outbound VPC provides secure outbound access via a proxy, such as Squid. Mutual TLS (mTLS) provides transport layer security; banks authenticate accredited third parties and provide access tokens to them for calling Open Banking APIs. Amazon API Gateway provides the API management layer that exposes open banking APIs and Authorization APIs. AWS WAF (Web Application Firewall) integrates with the API Gateway for web protection. Amazon Simple Storage Service (Amazon S3) serves as a trust store, where public certificates of clients are stored for validating requests by API Gateway. Additionally, banks perform checks against a TSP to validate the authenticity and status of third parties. API Gateway uses a private integration VPC and AWS PrivateLink to connect to the private subnets hosting microservices in other AWS accounts. Amazon Route 53 provides traffic management and domain name resolution. Amazon CloudFront provides a content delivery network (CDN) that banks can use for exposing static data. AWS Shield (automatically available with CloudFront) protects against L3/L4 DDoS. AWS Shield Advanced (requires sign up) gives additional protection. 4 3 5 6 7 8 Description (Part 1 of 2) 1 2 3 4 8 5 6 7
- 3. Reviewed for technical accuracy September 7, 2021 © 2021, Amazon Web Services, Inc. or its affiliates. All rights reserved. AWS Reference Architecture Open Banking on AWS Use Amazon Web Services to open APIs for Third-parties and help you implement Open Banking regulations. 9 AWS PrivateLink provides secure private connectivity on the Amazon network between VPCs and services hosted on AWS or on-premises. Open Banking API specifications for Account Information and Payments services are implemented using multiple container-based microservices hosted using Amazon Elastic Container Service (Amazon ECS) with AWS Fargate. Caching of customer account information is done using Amazon ElastiCache. Webhooks for payment status are hosted in this layer. Amazon DynamoDB stores consumer consents, aggregated data, and API performance metrics. Amazon Relational Database Service (Amazon RDS) holds a copy of the system of record which is synchronized in near real-time from the bank’s core system. Identity provider (IdP) for OAuth 2.0 implementation resides in separate AWS account so that other workloads in the bank can consume it securely. Customers can choose from AWS partners that provide IdP functionality or build a custom IdP. A separate developer sandbox is required for the third party to integrate with the bank’s AWS environment and build their products. AWS security services help enhance security posture. For example, Amazon GuardDuty monitors for malicious activity and unauthorized behavior; AWS Security Hub provides a comprehensive view of security alerts and security posture across AWS accounts. For more guidance, see Best Practices for Security, Identity & Compliance. Logs from all services are collected in Amazon S3 then analyzed and monitored by Amazon Elasticsearch Service. Management tools like AWS Systems Manager provide configuration management; AWS CloudFormation deploys environment; AWS code services enable CI/CD. Amazon EventBridge, Amazon Simple Queue Service (Amazon SQS), and Amazon Simple Notification Service (Amazon SNS) provide notification capability between services. 12 11 13 14 15 16 Description (Part 2 of 2) 17 18 9 10 13 14 11 12 15 16 17 18 10