IoT Circuit Threats and Vulnerabilities
Mark is regarded as a Cybersecurity thought Leader. In 2002 Mark founded the Atlantic Canada High Technology Crime Investigation Association. In 2015 Mark published the first NIST Cybersecurity Framework Foundation course. Mark was trained by IBM on IBM’s AS400 and worked with IBM Global Services on a Red Team conducting penetration testing against off shore financial institutions.Mark has led the design and implementation of information security programs for many US and Canadian organisations using ISO. Mark led Central 1 Credit Union to become the first Canadian Bank to earn ISO/IEC 27001 Certification. During Mark’s work with BC Government 2008 he also led the Ministry of Finance Division Corporate Account Services to become the first Canadian Government entity to earn ISO 27001 Registration /Certification.
Recommended
Recommended
More Related Content
What's hot
What's hot (20)
Similar to IoT Circuit Threats and Vulnerabilities
Similar to IoT Circuit Threats and Vulnerabilities (20)
More from www.securekm.com; Secure Knowledge Management Inc.
More from www.securekm.com; Secure Knowledge Management Inc. (8)
Recently uploaded
Recently uploaded (20)
IoT Circuit Threats and Vulnerabilities
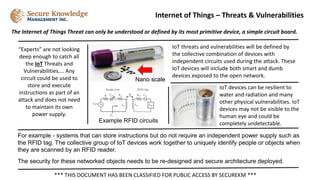
- 1. The Internet of Things Threat can only be understood or defined by its most primitive device, a simple circuit board. Internet of Things – Threats & Vulnerabilities *** THIS DOCUMENT HAS BEEN CLASSIFIED FOR PUBLIC ACCESS BY SECUREKM *** For example - systems that can store instructions but do not require an independent power supply such as the RFID tag. The collective group of IoT devices work together to uniquely identify people or objects when they are scanned by an RFID reader. The security for these networked objects needs to be re-designed and secure architecture deployed. IoT threats and vulnerabilities will be defined by the collective combination of devices with independent circuits used during the attack. These IoT devices will include both smart and dumb devices exposed to the open network. “Experts” are not looking deep enough to catch all the IoT Threats and Vulnerabilities…. Any circuit could be used to store and execute instructions as part of an attack and does not need to maintain its own power supply. Example RFID circuits IoT devices can be resilient to water and radiation and many other physical vulnerabilities. IoT devices may not be visible to the human eye and could be completely undetectable. Nano scale
