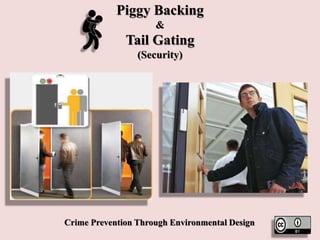
Piggy Backing & Tailgating (Security)
- 1. Piggy Backing & Tail Gating (Security) Crime Prevention Through Environmental Design
- 2. Piggy Backing & Tailgating • In security, piggybacking, similar to tailgating, refers to when a person tags along with another person who is authorized to gain entry into a restricted area, or pass a certain checkpoint. • The act may be legal or illegal, authorized or unauthorized, depending on the circumstances. However, the term more often has the connotation of being an illegal or unauthorized act.
- 3. Tailgating
- 4. Piggybacking
- 5. Piggy Backing & Tailgating • To describe the act of an unauthorized person who follows someone to a restricted area without the consent of the authorized person, the term tailgating is also used. "Tailgating" implies without consent (similar to a car tailgating another vehicle on the freeway), while "piggybacking" usually implies consent of the authorized person.
- 6. Tailgating
- 7. Piggy Backing & Tailgating • Piggybacking came to the public's attention particularly in 1999, when a series of weaknesses were exposed in airport security. • While a study showed that the majority of undercover agents attempting to pass through checkpoints, bring banned items on planes, or board planes without tickets were successful, piggybacking was revealed as one of the methods that was used in order to enter off- limits areas
- 8. Piggy Backing & Tailgating
- 9. Piggy Backing & Tailgating • Piggy-backers have various methods of breaching security. These may include: • Surreptitiously following an individual authorized to enter a location, giving the appearance of being legitimately escorted. • Joining a large crowd authorized to enter, and pretending to be a member of the crowd that is largely unchecked • Finding an authorized person who either disregards the law or the rules of the facility, or is tricked into believing the piggy backer is authorized, and agreeably allows the piggybacker to tag along. • Piggybacking can be regarded as one of the simpler forms of social engineering.
- 10. Surreptitiously following an individual authorized to enter a location
- 11. Joining a large crowd authorized to enter, and pretending to be a member of the crowd
- 12. Finding an authorized person who either disregards the law or the rules of the facility
- 13. Piggy Backing & Tailgating Common Courtesy • Piggy Backing occurs when an authorized individual permits others to follow behind without showing or registering proper authorization and gain access to a secure area.
- 14. Piggy Backing occurs when an authorized individual permits others to follow behind
- 15. Piggy Backing & Tailgating • Tailgating is a function of both the attitude of the individual and the corporate culture to wards adherence to security measures. • The impacts and costs of tailgating affect both the business and personnel including • ; Theft equipment and intellectual property • ; Workplace violence • ; Loss of business because of perception of lax security • ; Lax compliance with other security measures • ; Safety • ; Increased costs due to lack of knowledge of true real estate utilization
- 16. Piggy Backing & Tailgating
- 17. Piggy Backing & Tailgating
- 18. Introduction • Access control is the single most important component of the physical security and man guarding role in corporate security. • Access control is the management of the flow of people to areas for which they are authorized . • Access control must accommodate not only those familiar with the security culture , employees , but also others measures not familiar with the security culture; such as , contractors, visitors, the public , and occasionally the simply lost.
- 19. Access control
- 20. Introduction • Access control is a primary responsibility of company security. • The concept behind access control is that if we specifically determine in advance who is permitted access to certain areas and then control that access, we will have deterred improper activity from occurring, or in the case that improper activity does occur, we will be able to respond effectively. • Good access control speeds resolution of an incident by allowing security personnel to rapidly focus on those who had access to the area, or anomalies in access to an area.
- 21. Access Control
- 22. Introduction • Unfortunately , good access controls are very hard to achieve in an environment intended to be inviting to employees and customers, and also collaborative and productive . • A corruption of access controls can take the form of tailgating, in which the second person takes advantage of the first person’s entry without necessarily the complicit involvement of the first person
- 23. Good Access Controls Are Very Hard To Achieve
- 24. Tailgating
- 25. Introduction • Another form is piggybacking, in which the first person intentionally allows the second person to enter.
- 26. Piggybacking
- 27. The Problem • Common courtesy dictates holding doors open for one another. • In an access controlled environment, however, this behaviour is called tailgating and allows entrants to circumvent ‘badging’ by not presenting authentication for entry. • As soon as this occurs, access control measures such as badge systems have been circumvented. • Tailgating is surprisingly common in cooperative workplaces and has been observed at rates of 40 - 60% of all entrants to a building.
- 28. Holding Doors Open For One Another
- 29. Tailgating
- 30. Badging Systems • One might argue that many of those who “piggybacked in” (or “tailgated in”) have the appropriate credentials to allow them entry in to the space. • However, once badging systems have been circumvented, it is impossible to ascertain who is authorized and who is not. • This is a very big problem for an organization and does not come without costs.
- 31. Badging Systems
- 32. Costs of Tailgating • There are tangible and intangible costs to tailgating. • here is value in knowing who is in sensitive areas at all times. • The tangible costs of tailgating include: theft of equipment (e.g., laptops); • theft of sensitive hardware (e.g., proprietary hardware, roto-types ) • ; loss of intellectual property (e.g., software code) • ;workplace violence (e.g., entry of person committing violence at work) • ; physical attacks to network equipment
- 33. Tangible Costs Of Tailgating Include: Theft Of Equipment
- 34. lack of access control is an obvious security problem • While lack of access control is an obvious security problem with resulting tangible damages that are easily attributable, there are also intangible aspects of tailgating . • The intangible aspect of such breaches. Sites experiencing problems with non – compliance with basic security measures such as tailgating also tend to have other issues (e.g., management issues, bad behaviour, harassment, and others).
- 35. Lack Of Access Control Is An Obvious Security Problem
- 36. Lack Of Access Control Is An Obvious Security Problem • An environment can be created slowly over time in which there is a greater level of acceptance for poor management behaviour, harassment, ethical short - cuts, etc. • Tailgating may be a symptom of a larger problem that there is an attitude that security is not important and creates obstacles and slows employees in doing their jobs. • If employees adopt this attitude and don’t comply with security measures, there is greater potential for a security breach. • This tailgating behaviour can even affect customer relations and the loss of business.
- 37. Lack Of Access Control Is An Obvious Security Problem
- 38. Lack Of Access Control Is An Obvious Security Problem • Another intangible cost is the loss of productivity due to an incident occurring. • Loss of productivity in the event of a significant breach ,such as workplace violence or sabotage, is obvious. • Small incidents such as a single laptop theft can result in significant privacy issues, proprietary information loss, and marketplace confidence issues. • The resulting damage control diverts valuable resources to dealing with a problem that may have been avoided. • Even smaller incidents such as the theft of a wallet or purse results in a feeling of personal insecurity and violation that becomes the subject of extensive discussion and mistrust
- 39. Lack Of Access Control Is An Obvious Security Problem
- 40. Lack Of Access Control Is An Obvious Security Problem • In addition to the direct costs of theft, loss of productivity and market credibility, there are opportunity costs to the organization with respect to real -estate space savings and optimization.
- 41. Lack Of Access Control Is An Obvious Security Problem • The costs of tailgating definitely depend on the business model and product. For some organizations , the primary risk is entry of non - employees. • For other organizations, there is also the potential loss of proprietary hardware, personal or intellectual property and/or risk to personal safety. • While these risks are real, it is difficult to assess the potential costs of tailgating and the standard assessment tools either don’t exist or require such extensive customization that they are not useful.
- 42. Lack Of Access Control Is An Obvious Security Problem
- 43. Best Practices • A range of solutions to tailgating are presented in Table 1, which focuses on hardware, and Table 2, which focuses on social engineering.
- 46. Revolving Door
- 48. People Eater
- 49. Card Reader
- 51. Iris Scan
- 52. Mantraps
- 53. Scissor Gates
- 54. Best Practices Social Engineering • Tailgating is primarily a behavioural problem, and physical security hardware is not the only method to influence or stop the behaviour. • There are also ‘soft - power’ options such as social engineering, where non - physical security incentives can successfully alter behaviour and increase compliance.
- 55. Best Practices Social Engineering
- 56. Badging Compliance • In order to influence greater badge compliance it is necessary to understand the reasons that influence an individual’s reason not to wear a badge , such as the following • Cultural backlash to badging can occur; for example, the security measures may generate the perception that big brother is watching. • The badge as fashion statement can also create a problem in getting people to wear badges above the waist.
- 58. Badging Compliance • A company must ensure compliance by clearly documenting its policies and procedures on badge wearing policy . Employees will then be aware of what is expected and management is supported when they are required to take action against non - compliance. • A documented policy should include that all employees must wear badges at all times, report stolen badges, and have temporary badges issued in the event of missing or stolen badges.
- 60. Badging Compliance • To influence badge wearing behaviour, success has been had by requiring multiple uses of the badges; hourly workers need the badges to clock in and out, to attend a class, to obtain a meal or work gloves in a factor y, and to gain printer access in a corporate setting. • In some organizations the use of the badge may need to be negotiated with a union; due to union concerns about using badges to clock in on assembly lines because of concern the data will be used to monitor individual performance.
- 62. Badging Compliance • Another important consideration in changing behaviour is the physical placement of badge reading equipment. • Many times the readers are placed on the wall on the hinge side of the door. • While that works fine for the first person that reads their badge, while the door is open, it becomes very difficult for subsequent people to read their badge even if they don’t want to piggyback. • Placing the reader in a location where it is easily accessible no matter the position of the door can make it easier to change social behaviour.
- 64. The following table (Table 2) lists some methods to promote the badge wearing behaviour within an organization. Table 2 . Social Engineering Solutions
- 67. Ask for Badges
- 70. Implementation Considerations • The most effective tailgating deterrent is single person revolving doors, which physically restrict access to a single user at a time upon presentation of a valid credential. • However, the deployment of single-person revolving doors at all corporate access points is untenable; issues of culture, aesthetics, accountability, and climate affect the solution that can be implemented.
- 71. Single-person Trap Doors At All Corporate Access
- 72. Single-person Revolving Doors At All Corporate Access • Single-person revolving doors are highly restrictive in throughput and would not be appropriate in almost all main lobby environments. • They are expensive to install and maintain at exterior peripheral doors. • They are also not conducive to creating an inviting culture of a collaborative work environment, and certainly not an aesthetically pleasing one
- 73. Single-person Revolving Doors At All Corporate Access
- 74. Implementation Considerations • The hardest and most difficult two problems to solve is a corporate environment that places high value on an aesthetic welcoming environment and has high throughput, and one in which the culture resists physical security measures.
- 75. Implementation Considerations • There are solutions available that are more open, have greater throughput, and are more aesthetically pleasing. • Such solutions include several layers of access controls prior to reaching a restricted space (concentric circles approach), high-speed electronic turnstiles (with and without physical barriers), photo-beam detectors, intelligent video, biometrics, guard presence / identity validation during high traffic hours, or a combination of such measures.
- 77. Buildings and Building Function • Businesses with periods of high flow through, such as factories, require solutions that don’t delay traffic flow; like a mantrap would. • The implementation of physical security measures are further complicated with the repurposing of real estate, and leased buildings; owner approval is required and changes will need to be negotiated. • Many commercial buildings are like a sieve, and many thefts occur in commercial buildings. Many companies also have large campuses with many different buildings, some with better compliance than others. There are also campuses which house multiple companies that act independently but report to the same parent company.
- 79. Implementation Considerations • Laws - Privacy issues, and different data retention laws by country (e.g., Italian privacy law prohibits the use of cameras on warehouse doors). • Many try to have a standard, but one which is open to country laws. Social political issues can be different depending on country of origin; the US thinks the Middle East is high risk, but locals use a different risk filter. This difference of perspective also applies to the regulatory environment (e.g., working with animals).
- 81. Implementation Considerations • Accountability - A general security plan is relatively easy to implement when there is a single site with a single site executive. Difficulties arise with a campus where there is no single site director responsible, or there is a campus housing different companies with boards of directors that all report to a single parent company.
- 83. Implementation Considerations • Climate- It is also necessary to work within your climate. A very windy environment can require revolving doors to keep them shut because it is windy and others don’t stay closed. This allows them culturally to retrofit buildings with more secure revolving doors.
- 85. Implementation Considerations • Aesthetics – See the case study for a layered solution in an aesthetically pleasing lobby of a major firm using audible alarms with secondary full stop barriers. • Emergency Evacuation - A well-executed access control system can provide useful information in accounting for employees in an emergency evacuation (muster situation).
- 86. Aesthetics
- 88. Conclusion • You can install the most advanced security system on the market, but your security measures will fail if your occupants aren’t on board. • You need to create a secure building culture. Think about the difference between a casual office setting and going through airport security. Clear expectations and constant communication shape behaviour.
- 89. Conclusion
- 90. Conclusions • Tailgating is a common corporate security problem with high potential tangible and intangible costs. • Solutions for deterring/eliminating tailgating include hardware and social engineering approaches, which differ in cost, throughput, aesthetics, and other factors. • Badge-wearing compliance is a particularly challenging issue, and many lessons are provided for increasing compliance. • Implementation of solutions must be tailored to the aesthetic and cultural needs of a given scenario; the most challenging being providing access control in a welcoming, high-throughput, aesthetically pleasing lobby. The case study illustrates a real-world solution to this challenging scenario, which ultimately uses a combination of solutions
- 91. Tailgating
- 92. Tailgating
- 93. Tailgating: A Common Courtesy and a Common Risk
- 94. References • Tail-gating (Piggybacking) https://whatis.techtarget.com/definition/tailgating-piggybacking • Tailgating: A Common Courtesy and a Common Risk https://www.securitymagazine.com/articles/86026-tailgating-a-common-courtesy- and-a-common-risk • Piggybacking (security) https://en.wikipedia.org/wiki/Piggybacking_(security) • Security Tailgating (aka Piggybacking) http://www.alliedbarton.com/Portals/0/SRC/WhitePapers/Security%20Tailgating %20-%20Best%20Practices%20in%20Access%20Control.pdf • 10 Strategies to Prevent Tailgating https://www.buildings.com/article-details/articleid/13274/title/10-strategies-to- prevent-tailgating
- 95. Thanks…
