CRPT Secure Messaging Introduction The Anti-Email by Augustine Fou 2013
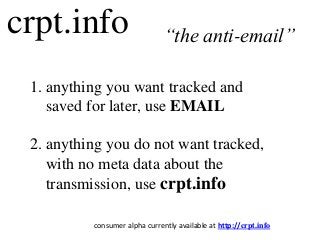
- 1. crpt.info 1. anything you want tracked and saved for later, use EMAIL 2. anything you do not want tracked, with no meta data about the transmission, use crpt.info “the anti-email” consumer alpha currently available at http://crpt.info
- 2. Why We Built It 1. private citizens have a right to private communications 2. security experts agree that email is “not securable” 3. standard encryption technology is too expensive or too hard to use 4. other encrypted email systems are not anonymous
- 3. Offline Analogies personal mail lockbox only you have private key for decrypting messages dropped into your lock box public phone senders use a public phone to anonymously create and send messages to your lock box
- 4. Top Features 1. Endpoints are anonymous, not associatable 2. Message encrypted with recipient’s public key 3. Sender can “unsend” after hitting “send” 4. Every part of transmission is “transient” ? ?njbf8nw8cw9casssddnasda3131wcwyfkj01 Public key encryption Private key decryption
- 5. How to Use 1. Get a SendToIt code • You can get as many as you need • Use your own name for something easy-to-remember; get an alphanumeric code for more anonymity • Create a passphrase that you will later use to get messages 2. Send Message • Type in the recipients’ SendToIt codes (comma separated) • Type your message or attach picture, file, voice memo, etc. 3. Get Message • Type in YOUR OWN SendToIt code • Type your passphrase • Click download, and then view to see each message
- 6. Android Devices On Android devices, using Chrome or Firefox, you can click the “Choose Files” button and directly: - take picture - take video - record voice memo - select music track - attach file NOTE: iPhone restrictions do not allow this
- 7. Tested Devices/Browsers Desktop Mobile Recommended Available Recommended Recommended (very slow)
- 8. Comparison to SnapChat SnapChat: 1. cannot send text, files, audio 2. is not anonymous (requires login, phone #) 3. sender cannot “unsend” messages 4. does not actually encrypt files (or even delete them irrecoverably)
- 9. Key Points of Differentiation Crpt.info: 1. does not rely on strength of encryption alone 2. does not rely on industry standard forms of encryption (due to NSA involvement) 3. does not use email or SMS infrastructure 4. does not require large processing power on “endpoints” like cell phones 5. scales inifintely using principles of parallelism
- 10. Dr. Augustine Fou – Digital Consigliere “I study trends in cyber security in payments and communications. In light of recent revelations I developed the CRPT platform to enable secure communications for individuals and enterprises. It was designed with the principle that given enough time and/or computing power ANY form of encryption can be broken. So the system does not rely on the strength of the ecryption alone but, rather, a series of steps which is straighforward in one direction but very difficult in reverse.” FORMER CHIEF DIGITAL OFFICER, HCG (OMNICOM) MCKINSEY CONSULTANT CLIENT SIDE / AGENCY SIDE EXPERIENCE PROFESSOR AND COLUMNIST ENTREPRENEUR / SMALL BUSINESS OWNER PHD MATERIALS SCIENCE (MIT '95) AT AGE 23 ClickZ Articles: http://bit.ly/augustine-fou-clickz Slideshares: http://bit.ly/augustine-fou-slideshares LinkedIn: http://linkd.in/augustinefou
