Business Impact Analysis 【My Continuous Learning】
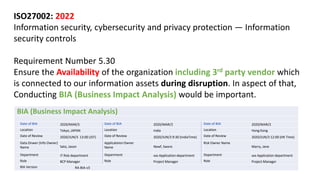
- 1. ISO27002: 2022 Information security, cybersecurity and privacy protection — Information security controls Requirement Number 5.30 Ensure the Availability of the organization including 3rd party vendor which is connected to our information assets during disruption. In aspect of that, Conducting BIA (Business Impact Analysis) would be important. BIA (Business Impact Analysis) Date of BIA 2020/MAR/3 Date of BIA 2020/MAR/2 Date of BIA 2020/MAR/2 Location Tokyo, JAPAN Location India Location Hong Kong Date of Review 2020/JUN/3 13:00 (JST) Date of Review 2020/JUN/3 9:30 (IndiaTime) Date of Review 2020/JUN/3 12:00 (HK Time) Data Onwer (Info Owner) Name Sato, Jason Applicateion Owner Name Newf, Swere Risk Owner Name Marry, Jane Department IT Risk department Department xxx Application department Department xxx Application department Role BCP Manager Role Project Manager Role Project Manager BIA Version RA-BIA-v3
- 2. Activities and scenarios reviewed Risk Reviewed Function responsible Activity importance Max time to restart Time to normal service Comment Critical service App team Vital 1 24 Failier of system necessary Critical service desired Failier of system necessary Critical service Critial BIA per scenario Impact over time #1 Critical service High Medium Low 1hour 2hour 12hour 24 hour Comment Impact of disruption x H H H H Sales Staff × M H H H Operation Staff × L H H H Procurement staff × L H H H Support team × L H H H Infosec team × L H H H Financial × L H H H Service level × L H H H Customers × H H H H
- 3. BIA Summary Activity reviewed #1 Function owned by Activity importance Risk treatment Recovery Sequence Max time to restart (hours) Time to normal service level Comment Shift deployeing planning Critical Acceptance 1 72 7 review of service in schedule Critical Acceptance 2 Critical Business Continuity 3 Critical Business Continuity 4 Activity reviewed #2 Function owned by Activity importance Risk treatment Recovery Sequence Max time to restart (hours) Time to normal service level Comment Shift deployeing planning Critical Acceptance 1 72 7 review of service in schedule 2 Business Continuity 3 Business Continuity 4
- 4. Activity name #1 Activity frequency more than hourly activity owner title Date of operation every day Number of FTEs involved hours of operation 8 hours Daily peak details weekly peak details Monthly peak details Annual peak details Activity name #2 Activity frequency more than hourly activity owner title Date of operation every day Number of FTEs involved hours of operation 8 hours Daily peak details weekly peak details Monthly peak details Annual peak details
- 5. Dependencies a) Internal Independencies of Activity b) External Interdependencies of Activity Internal Independencies External Independencies Owner Owner Internal Independencies External Independencies Owner Owner Internal Independencies External Independencies Owner Owner Internal Independencies External Independencies Owner Owner People Impact Day1 Day2 Day3 Day4 Day8 Day15 1 month Comments Customer Staff Security Operation Customer service IT Business Impact Day1 Day2 Day3 Day4 Day8 Day15 1 month Comments Financial Service Levels Contractual agreements Reputation Helth and Safety
- 6. Resources required to restart activity and reach normal service level Headcount Restart Normal Skill as restart knowledge IT Importance of activity Agreed level of importance of activity of key business services and objectives. Critical Completed by Positions Date Signature Senior Management agreement that the fundings detailed above are a true reflection of the organization Completed by Positions Date Signature Sooma, Jerimi Senor VP 2021/JUL/3 CEO 2021/JUL/3 Mwema, Adsf Impact - Business Function Information How long can the activity operate in manual mode? Are there any written processes/ procedures for operation in manual mode? When were the processes / procedures for operating in manual mode last updated? What additioanl respurces are required for operating in manual mode? In the event of a disruption there will be lost data / transactions. Can they be recovered? How will lost data be recovered? Are there any written processes / procefures for recovering lost data? When were the processes / procedures for recovering list data last updated? What would be the impact if the data cannot be recovered? Does the activity reply on information that is not electronic? (Specify data and media) How will lost (non electronic) information be recovered? What specialised equipment is required to perform the activity? CIO