Darknets - Introduction & Deanonymization of Tor Users By Hitesh Bhatia
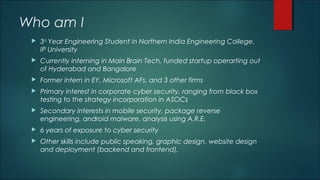
- 1. Who am I 3rd Year Engineering Student in Northern India Engineering College, IP University Currently interning in Main Brain Tech, funded startup operarting out of Hyderabad and Bangalore Former intern in EY, Microsoft AFs, and 3 other firms Primary interest in corporate cyber security, ranging from black box testing to the strategy incorporation in ASOCs Secondary interests in mobile security, package reverse engineering, android malware, analysis using A.R.E. 6 years of exposure to cyber security Other skills include public speaking, graphic design, website design and deployment (backend and frontend),
- 2. Darknet
- 4. Introduction - Darknet Most frequently refers to an area of the Internet only accessible by using an encryption tool called The Onion Router (Tor) Aimed at those desiring privacy online, although frequently attracts those with criminal intentions Ability to host websites anonymously and with a degree of impunity Tor makes it difficult for governments to censor sites or content that may be hosted elsewhere in the world Critical mass of users averaging 2.5 million per day as of June 2016 (Tor Project 2016 statistics) Frequently cited as one of the key tools against government surveillance Is a part of the Deepweb (sites that are not indexed by search engines) https://www.torproject.org/
- 5. Softwares used to access the Deep Web The Onion Router (Tor) is an open- source software program that allows users to protect their privacy and security against a common form of Internet surveillance known as traffic analysis. Tor was originally developed for the U.S. Navy in an effort to protect government communications. The name of the software originated as an acronym for the Onion Router, but Tor is now the official name of the program. It is the most used software, due to the services it hosts, in addition to its reliability over the years.
- 6. Softwares used to access the Deep Web Invisible Internet Project(I2P) is an anonymous network, exposing a simple layer that applications can use to anonymously and securely send messages to each other. The network itself is strictly message based (a la IP), but there is a library available to allow reliable streaming communication on top of it (a la TCP). All communication is end to end encrypted (in total there are four layers of encryption used when sending a message), and even the end points ("destinations") are cryptographic identifiers (essentially a pair of public keys). It is the most used software, due to the services it hosts, in addition to its reliability over the years. It is lesser known than Tor, and therefore less prone to deanonymization attacks.
- 7. Other softwares part of the Deep Web Freenet Subgraph os Freepto iprediaOS JonDo Live-CD (combination of TOR and other commonly used darknet applications) Whonix Tails Tox (encryped IM and video/audio calls, with voice modulation)
- 8. History in Brief 1995 - Development began on “Onion Routing” (ONR) 1997 – Funded by DARPA High Confidence Networks Program as part of the Memex project was to invent better methods for interacting with and sharing information, so users can quickly and thoroughly organize and search subsets of information relevant to their individual interests. The technologies developed in the program would provide the mechanisms for improved content discovery, information extraction, information retrieval, user collaboration and other key search functions. 1998 – 13 nodes created, 1 in Canadian Ministry of Defence 2001 – More DARPA funding 2003 - US Naval Research Lab releases ONR v2 (aka TOR) 2004 - Hidden Services introduced 2014 - Sponsors include SRI, US Department of State. NSF, Radio Free Asia, The Ford Foundation, Google, EFF, 4300 individuals
- 9. Other softwares used to access parts of the Darknet Freenet is a popular darknet (friend-to-friend) by default; since version 0.7 it can run as a "opennet" (peer nodes are discovered automatically). RetroShare can be run as a darknet (friend-to-friend) by default to perform anonymous file transfers if DHT and Discovery features are disabled. GNUnet is a darknet if the "F2F (network) topology" option is enabled. Zeronet is open source software aimed to build an internet-like computer network of peer-to-peer users of Tor. Syndie is software used to publish distributed forums over the anonymous networks of I2P, Tor and Freenet. OneSwarm can be run as a darknet for friend-to-friend file-sharing. Tribler can be run as a darknet for file-sharing.
- 11. Figures connecting India and Tor
- 12. Figures connecting India and Tor
- 13. How it works Volunteers run thousands of “relays,” a server that any other user can ask to route traffic through Observer can see traffic entering and leaving the relay, but they cannot determine which user is visiting which site because the traffic is encrypted When a user visits any sites through a relay, his traffic appears to come from the relay rather than the user’s computer. Thus, the user remains anonymous to the site itself How it works Relay Site A Site B Site C User A User B User C Observer
- 15. Hidden Services (HSes) in Tor It is the ability to host a website (or Internet service) anonymously. In this case, both the visitor and the site are anonymous to each other. Analogous to websites on the internet Also allows the possibility of criminally oriented material to be hosted with a degree of impunity 2016 study estimated that there were 43,000 HSes at any one time Services use .onion as a domain name instead of .com etc
- 16. Different HSes offered Hidden Wiki (like Wikipedia) Torfind (Like Bing) Grams (Like Google) The Pirate Bay (Famous piracy p2p magnet site) Assassination Market (Hire hitmen to assassinate people of interest) Rent-A-Hacker (Hacking for money) (BlackHat ONLY) TorCarding Forum (Trading of identities, hacking info, requires 50 USD for purchase) Intel Exchange HackBB (Advanced hacking tutorials) SilkRoad 2.0 (Full fledged blackmarket for all kinds of recreational drugs)
- 17. Different HSes offered (Contd.) Agora (Same as Silk Road, online drugs marketplace and other illicit items) Fake US driver licences Fake Passports/Drivers Licences of other countries
- 19. Transaction Methods in Darknet Bitcoin is the only method of transactions on TOR. Transfer BTC to wallet on any marketplace account, then use like any normal E-commerce website Ship to pick-up location, home, anywhere else BTC (or any cryptocurrency) boils down to a global transaction ledger maintained by the computational power of a P2P network.
- 21. Bitcoins Bitcoins are not physical currency; the currency itself depends on transactions and no actual money changes hands Cryptocurrency is extremely hard to track, since Bitcoin accounts are alphanumeric strings, instead of normal names It is therefore viable for anonymous transactions i.e. for the exchange of illegal services for bitcoins ( like hacking ranging from lone wolf to full black box attacks, to assassinations, obtaining federal intelligence, stalking, compromised credit card and email details)
- 22. Considerations for TOR Tor can in some cases reveal your true identity If someone owns both an entry and exit node, they can correlate between the two (this is known as a correlation attack) Browser exploits like JavaScript Engine, XSS and pingbacks over non Tor connections BTC is not fully anonymous, the block chain is made available to the public
- 23. Alternative to TOR – I2P (Invisible Internet Project) The “Invisible Internet Project” Messages encrypted Outbound and Inbound tunnels Data exchange 1st query must be made to I2P network’s “database” Acts like a distributed hash table
- 24. Content on the Darknet Abuse: sites where the title indicates some form of sexual abuse (typically minors) Anonymity: sites aimed at promoting (or teaching) the use of anonymity tools or anonymous culture Bitcoin: currency exchange from a mainstream currency to bitcoin, but more often money-laundering services Blog: personal or topical blog, often covering topics such as hacktivism Books: ebook service typically offering copyrighted material for free Chat: web-based chat service, excluding services such as Jabber and Internet Relay Chat Counterfeit: sites offering counterfeit items; notable fake currency, such as notes, or fake passports/ identity documents Directory: site offering links to other sites within the Dark Net, often used for discovering other sites
- 25. Content on the Darknet (Contd.) Drugs: the sale or purchase of narcotics; typically, marketplaces connecting buyers and sellers Forum: web-based forum whose primary purpose does not fit into another category; for example, generalist forum Fraud: sites attempting to obtain a pecuniary advantage by deception Gambling: any site that promotes/supports gambling. Bitcoin gambling services were most prevalent here, whereby users would first convert their fiat currency to bitcoin Guns: sites exclusively aimed at selling guns Hacking: site providing instructional information on illegal computer hacking Hosting: Dark Net hosting service allowing users to host another Dark Net site Mail: Dark Net web-based email or messaging service; examples include Mail2Tor and the now defunct TorMail
- 26. Content on the Darknet (Contd.) Market: a marketplace selling items other than drugs or services covered in other categories News: news service such as current affairs or news specific to the Dark Net Porn: Pornography sites that carry material that would be legal in most Western jurisdictions Search: site providing a search engine-type service; one example is Ahmia Whistleblower: sites typically operated by journalists for whistleblowers to submit documents. The GlobaLeaks platform (Hermes Center for Transparency and Digital Human Rights 2014) and SecureDrop platform (Freedom of the Press Foundation 2014) were prominently featured in this category.
- 28. Breaking the anonymity of Tor Users and HSes In reality, any suitably resourced entity can launch attacks with high success rates while maintaining a minimal risk of detection A typical user may send millions of bytes and an observer can see the precise time they were sent and received. It is therefore easy to confirm with high probability that two parties are communicating. No cases whereby a deanonymization attack alone has been used to seek a conviction Therefore this process involves guesswork
- 29. Breaking the anonymity of Tor Users and HSes When visitors accessed a website, the FBI deployed a network investigative technique (NIT) – a hacking tool – and used a single warrant to uncover 1,300 IP addresses, tracing these addresses back to actual individuals, in the case of Playpen. When visitors accessed the website, although their traffic might have been encrypted, a Flash application was secretly installed on the user's computer that quietly sent important data about the user straight to the FBI so that it did not pass through the Tor network at all.
- 30. Case Studies – 1(Harvard) Eldo Kim made a bomb threat to Harvard's student newspaper and some other Harvard officials The reasons under the sun to do something like this his was that he wanted to get out of a final exam He used tor to send the threat via email He connected to TOR through his student account Because of this fact and the fact that he was the only one connected to TOR at the time the email was sent it was easy for them to correlate that he may have sent the threat. As if that wasn't enough, Eldo puts the final nail in his own coffin by actually admitting that he was the one who made the bomb threat.
- 31. Lessons Learned Don't be the only person using Tor on a monitored network at a given time Use a bridge DON'T ADMIT ANYTHING Correlation attacks are a bitch
- 32. Case Studies – 2 (Citizen of the US) Hector (Sabu) was already being watched by the FBI. However, his mistake was that he became careless Slipping up, he connected to IRC without tor, when he normally would. This allowed the FBI to get his home IP address. Jeremy( sup_g ), when speaking with Hector on IRC spoke carelessly of places he had previously been arrested and other groups that he was involved with. The FBI used this information to narrow their suspect pool and allowed them to obtain a court order to monitor his internet traffic. Once again correlation proves to be a bitch say this because although the FBI did not exploit tor to bust Jeremy, they were, however, able to correlate the times 'sup_g' spoke with 'Sabu' on IRC with when Jeremy was at home using his computer.
- 33. Lessons Learned Use Tor consistently Don't give personal information Correlation attacks are still a b!$%*%!
- 34. Case Studies – 3 (Freedom hosting) Freedom Hosting was known for hosting child pornography. This is enough to make you a mark for all sorts. In fact, Freedom had already been under attack from Anonymous during Op Darknet because of the child porn. The FBI was able to compromise Freedom because they were using an outdated version, 17 ESR, of tor browser. This allowed the FBI to exploit bug CVE-2013-1690. Freedom Hosting did not update their version of the TOR browser. The FBI used a payload called Magneto that gave them Freedom's IP address, MAC address, and Windows host name with the unique serial number that ties a user to a site visit (Cookie malware!!)
- 35. Lessons Learned Don't host Captain Picard or Julian Bashir Patch, patch, patch Follow the money Leave encrypted laptops in a powered down state when not in use!
- 36. Case Studies – 4 (Silk Road) Famous drug acquisition site - Ross Ulbricht (Dread Pirate Roberts) To market his site [The Silk Road] he would post around in clear net forums (reddit, HF.net etc.) The FBI claims the former physics and engineering student even publicly alluded to his alleged criminal enterprise on his LinkedIn profile He put his links on his G+ account and regularly posted that he was using Ubuntu on the actual Hses He would go as far as the neighborhood Starbucks or library, which was just around the corner from his house, to logon to and administrate his Silk Road onion
- 37. Lessons Learned Don’t do drugs, drugs are bad Keep online identities separate Have a consistent story Don't talk about personal interests Don't volunteer information!
- 38. Blocking Of Tor Since the list of relays (known as the consensus) is public, anyone is able to download the list and block access to all of them. The user would then be unable to connect to the first hop and into the network An individual can block a single site by launching several relays and ensuring they occupy the positions in the DHT of the responsible relays for that service. If someone comes to the relay asking for the descriptor, the individual can simply deny it Operators of Tor relays could themselves choose to block the content by patching their relays to deny requests to these sites. This would require the cooperation of a large percentage of relay operators to be effective, but it would be a decentralized blocking mechanism requiring some consensus
- 39. Examples of TOR Relay Lists https://torstatus.blutmagie.de/ - Common list of approximately 7000 routers being used as Onion relays https://atlas.torproject.org/#/top10 - Top 10 relays in order of bandwidth provided ( remember that a TOR network is only as fast as its slowest router, depending upon bandwidth as well as latency) https://www.dan.me.uk/tornodes - List of entry and exit nodes updated every 30 minutes. Commonly used in the EU to ban entry to the TOR network. https://onionview.com/ - Provides a visual map of entry, exit and internal relays around the globe.
- 40. Legalities involved with relevance to Darknet as a whole India has NO laws that deal with accessing the Darknet, using Tor or other softwares, using TAILS or other operating systems that either promise, claim or guarantee anonymity. Torrents are legal in India, depending on what is being downloaded using a P2P connection (keeping in mind the International Intellectual Property Law) Almost all Western countries, China and Russia have implemented defenses against the Darknet, however Tor is a state sponsored resource that is used by the public for concerns of privacy Need is to build cyber laws that can tackle illicit transactions/trade/barter on the internet as well as the Darknet.
- 41. Conclusion Socio-cultural forces are involved in the “generation and sustainability” of criminal entities that use the Darknet. For example, some countries do not have functioning or sufficient markets in legal goods, a context in which the Darknet may actually facilitate increased social welfare and economic efficiency. The Deep Web and the Darknet are attractive to many because of the prosecution, regulation, and national security surveillance efforts of states in the physical world and Surface Web. Illicit activity is being driven below the electronic thermocline of common search engines and usual investigative techniques, and states must be willing to dive beneath it to gather information and take action. The transnationality of these networks frustrates eradication, regulatory, and prosecution efforts of any one state, creating cooperation, collective action, and law harmonization problems for state actors attempting to work together to counter illicit use of the Internet.
