Psy approach to cyber security
•Download as PPTX, PDF•
0 likes•55 views
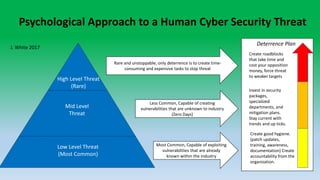
This document outlines three levels of cyber security threats - low, mid, and high level - and proposes strategies to address each. Low level threats are the most common and can exploit known vulnerabilities, requiring good security hygiene. Mid-level threats are less common but can create unknown vulnerabilities, necessitating investment in security packages and specialized teams. High level threats are rare but unstoppable, so the strategy is to deter them through time-consuming and expensive roadblocks that force threats to target weaker organizations instead.
Report
Share
Report
Share
Recommended
More Related Content
What's hot
What's hot (7)
2 ppt final dan shoemaker dd1 stockholm presentation

2 ppt final dan shoemaker dd1 stockholm presentation
Taking a Data-Driven Approach to Business Continuity

Taking a Data-Driven Approach to Business Continuity
Viewers also liked
Viewers also liked (10)
Employee Motivation as a tool to implement internal Marketing.

Employee Motivation as a tool to implement internal Marketing.
Recently uploaded
Sustainability by Design: Assessment Tool for Just Energy Transition Plans

Sustainability by Design: Assessment Tool for Just Energy Transition PlansJust Energy Transition in Coal Regions Knowledge Hub
Lorain Road Business District Revitalization Plan Final Presentation

Lorain Road Business District Revitalization Plan Final PresentationCuyahoga County Planning Commission
Recently uploaded (20)
Call Girl Service in Korba 9332606886 High Profile Call Girls You Can Get ...

Call Girl Service in Korba 9332606886 High Profile Call Girls You Can Get ...
NAP Expo - Delivering effective and adequate adaptation.pptx

NAP Expo - Delivering effective and adequate adaptation.pptx
Genuine Call Girls in Salem 9332606886 HOT & SEXY Models beautiful and charm...

Genuine Call Girls in Salem 9332606886 HOT & SEXY Models beautiful and charm...
Delivery in 20 Mins Call Girls Malappuram { 9332606886 } VVIP NISHA Call Girl...

Delivery in 20 Mins Call Girls Malappuram { 9332606886 } VVIP NISHA Call Girl...
Antisemitism Awareness Act: pénaliser la critique de l'Etat d'Israël

Antisemitism Awareness Act: pénaliser la critique de l'Etat d'Israël
Sustainability by Design: Assessment Tool for Just Energy Transition Plans

Sustainability by Design: Assessment Tool for Just Energy Transition Plans
Lorain Road Business District Revitalization Plan Final Presentation

Lorain Road Business District Revitalization Plan Final Presentation
Top profile Call Girls In Haldia [ 7014168258 ] Call Me For Genuine Models We...![Top profile Call Girls In Haldia [ 7014168258 ] Call Me For Genuine Models We...](data:image/gif;base64,R0lGODlhAQABAIAAAAAAAP///yH5BAEAAAAALAAAAAABAAEAAAIBRAA7)
![Top profile Call Girls In Haldia [ 7014168258 ] Call Me For Genuine Models We...](data:image/gif;base64,R0lGODlhAQABAIAAAAAAAP///yH5BAEAAAAALAAAAAABAAEAAAIBRAA7)
Top profile Call Girls In Haldia [ 7014168258 ] Call Me For Genuine Models We...
Private Call Girls Bidar 9332606886Call Girls Advance Cash On Delivery Service

Private Call Girls Bidar 9332606886Call Girls Advance Cash On Delivery Service
Vivek @ Cheap Call Girls In Kamla Nagar | Book 8448380779 Extreme Call Girls ...

Vivek @ Cheap Call Girls In Kamla Nagar | Book 8448380779 Extreme Call Girls ...
Call Girls Koregaon Park - 8250092165 Our call girls are sure to provide you ...

Call Girls Koregaon Park - 8250092165 Our call girls are sure to provide you ...
2024 UN Civil Society Conference in Support of the Summit of the Future.

2024 UN Civil Society Conference in Support of the Summit of the Future.
Dating Call Girls inBaloda Bazar Bhatapara 9332606886Call Girls Advance Cash...

Dating Call Girls inBaloda Bazar Bhatapara 9332606886Call Girls Advance Cash...
2024: The FAR, Federal Acquisition Regulations, Part 32

2024: The FAR, Federal Acquisition Regulations, Part 32
2024: The FAR, Federal Acquisition Regulations, Part 31

2024: The FAR, Federal Acquisition Regulations, Part 31
Psy approach to cyber security
- 1. Low Level Threat (Most Common) Mid Level Threat High Level Threat (Rare) Rare and unstoppable, only deterrence is to create time- consuming and expensive tasks to stop threat Most Common, Capable of exploiting vulnerabilities that are already known within the industry Less Common, Capable of creating vulnerabilities that are unknown to industry (Zero Days) Psychological Approach to a Human Cyber Security Threat Create roadblocks that take time and cost your opposition money, force threat to weaker targets Create good hygiene. (patch updates, training, awareness, documentation) Create accountability from the organization. Invest in security packages, specialized departments, and mitigation plans. Stay current with trends and up ticks. J. White 2017 Deterrence Plan
