[EMPOWERMENT TECHNOLOGIES] - INTERNET THREATS
•Download as PPTX, PDF•
3 likes•5,834 views
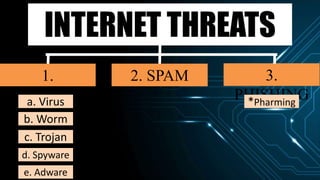
This document discusses various internet threats such as malware, spam, and phishing. It defines different types of malware like viruses, worms, trojans, spyware and adware. Viruses and worms are malicious programs that replicate and spread from one computer to another. Trojans pose as useful programs but leave computers unprotected. Spyware and keyloggers monitor users' activities without their knowledge. Spam refers to unwanted emails, while phishing tricks users into sharing private information on fake websites. It also provides tips to avoid copyright infringement and conduct safe online research.
Report
Share
Report
Share
Recommended
Recommended
More Related Content
What's hot
What's hot (20)
Advanced Presentation Skills - Empowerment Technologies

Advanced Presentation Skills - Empowerment Technologies
Similar to [EMPOWERMENT TECHNOLOGIES] - INTERNET THREATS
Similar to [EMPOWERMENT TECHNOLOGIES] - INTERNET THREATS (20)
Empowerment Technologies Lecture 3 (Philippines SHS)

Empowerment Technologies Lecture 3 (Philippines SHS)
More from JazzyNF
More from JazzyNF (15)
[EMPOWERMENT TECHNOLOGIES]-IMAGING AND DESIGN FOR ONLINE ENVIRONMENT![[EMPOWERMENT TECHNOLOGIES]-IMAGING AND DESIGN FOR ONLINE ENVIRONMENT](data:image/gif;base64,R0lGODlhAQABAIAAAAAAAP///yH5BAEAAAAALAAAAAABAAEAAAIBRAA7)
![[EMPOWERMENT TECHNOLOGIES]-IMAGING AND DESIGN FOR ONLINE ENVIRONMENT](data:image/gif;base64,R0lGODlhAQABAIAAAAAAAP///yH5BAEAAAAALAAAAAABAAEAAAIBRAA7)
[EMPOWERMENT TECHNOLOGIES]-IMAGING AND DESIGN FOR ONLINE ENVIRONMENT
[EMPOWERMENT TECHNOLOGIES]-ADVANCED PRESENTATION SKILLS![[EMPOWERMENT TECHNOLOGIES]-ADVANCED PRESENTATION SKILLS](data:image/gif;base64,R0lGODlhAQABAIAAAAAAAP///yH5BAEAAAAALAAAAAABAAEAAAIBRAA7)
![[EMPOWERMENT TECHNOLOGIES]-ADVANCED PRESENTATION SKILLS](data:image/gif;base64,R0lGODlhAQABAIAAAAAAAP///yH5BAEAAAAALAAAAAABAAEAAAIBRAA7)
[EMPOWERMENT TECHNOLOGIES]-ADVANCED PRESENTATION SKILLS
[EMPOWERMENT TECHNOLOGIES] - ADVANCED WORD PROCESSING SKILLS![[EMPOWERMENT TECHNOLOGIES] - ADVANCED WORD PROCESSING SKILLS](data:image/gif;base64,R0lGODlhAQABAIAAAAAAAP///yH5BAEAAAAALAAAAAABAAEAAAIBRAA7)
![[EMPOWERMENT TECHNOLOGIES] - ADVANCED WORD PROCESSING SKILLS](data:image/gif;base64,R0lGODlhAQABAIAAAAAAAP///yH5BAEAAAAALAAAAAABAAEAAAIBRAA7)
[EMPOWERMENT TECHNOLOGIES] - ADVANCED WORD PROCESSING SKILLS
TLE 6-Common cattle breeds in asia, america and europe

TLE 6-Common cattle breeds in asia, america and europe
Recently uploaded
https://app.box.com/s/7hlvjxjalkrik7fb082xx3jk7xd7liz3TỔNG ÔN TẬP THI VÀO LỚP 10 MÔN TIẾNG ANH NĂM HỌC 2023 - 2024 CÓ ĐÁP ÁN (NGỮ Â...

TỔNG ÔN TẬP THI VÀO LỚP 10 MÔN TIẾNG ANH NĂM HỌC 2023 - 2024 CÓ ĐÁP ÁN (NGỮ Â...Nguyen Thanh Tu Collection
Making communications land - Are they received and understood as intended? webinar
Thursday 2 May 2024
A joint webinar created by the APM Enabling Change and APM People Interest Networks, this is the third of our three part series on Making Communications Land.
presented by
Ian Cribbes, Director, IMC&T Ltd
@cribbesheet
The link to the write up page and resources of this webinar:
https://www.apm.org.uk/news/making-communications-land-are-they-received-and-understood-as-intended-webinar/
Content description:
How do we ensure that what we have communicated was received and understood as we intended and how do we course correct if it has not.Making communications land - Are they received and understood as intended? we...

Making communications land - Are they received and understood as intended? we...Association for Project Management
Recently uploaded (20)
UGC NET Paper 1 Mathematical Reasoning & Aptitude.pdf

UGC NET Paper 1 Mathematical Reasoning & Aptitude.pdf
Mixin Classes in Odoo 17 How to Extend Models Using Mixin Classes

Mixin Classes in Odoo 17 How to Extend Models Using Mixin Classes
ICT Role in 21st Century Education & its Challenges.pptx

ICT Role in 21st Century Education & its Challenges.pptx
On National Teacher Day, meet the 2024-25 Kenan Fellows

On National Teacher Day, meet the 2024-25 Kenan Fellows
Basic Civil Engineering first year Notes- Chapter 4 Building.pptx

Basic Civil Engineering first year Notes- Chapter 4 Building.pptx
Food safety_Challenges food safety laboratories_.pdf

Food safety_Challenges food safety laboratories_.pdf
TỔNG ÔN TẬP THI VÀO LỚP 10 MÔN TIẾNG ANH NĂM HỌC 2023 - 2024 CÓ ĐÁP ÁN (NGỮ Â...

TỔNG ÔN TẬP THI VÀO LỚP 10 MÔN TIẾNG ANH NĂM HỌC 2023 - 2024 CÓ ĐÁP ÁN (NGỮ Â...
General Principles of Intellectual Property: Concepts of Intellectual Proper...

General Principles of Intellectual Property: Concepts of Intellectual Proper...
Python Notes for mca i year students osmania university.docx

Python Notes for mca i year students osmania university.docx
Making communications land - Are they received and understood as intended? we...

Making communications land - Are they received and understood as intended? we...
This PowerPoint helps students to consider the concept of infinity.

This PowerPoint helps students to consider the concept of infinity.
Salient Features of India constitution especially power and functions

Salient Features of India constitution especially power and functions
[EMPOWERMENT TECHNOLOGIES] - INTERNET THREATS
- 1. INTERNET THREATS 1. MALWARE 3. PHISHING 2. SPAM a. Virus b. Worm c. Trojan d. Spyware e. Adware *Pharming
- 4. a. Virus Malicious program designed to replicate itself & transfer from one computer to another either through the internet & local networks or data storage like flash drives and CD’s.
- 6. b. Worm A malicious program designed that transfers from one computer to another by any type of means, Often, it uses a computer network to spread itself.
- 7. b. Worm Onel de Guzman The creator of one of the most popular worm: ILOVEYOU worm. (“Love bug worm”)
- 8. c. Trojan A malicious program disguised as a useful program but once downloaded or installed, leaves your PC unprotected & allows hackers to get information.
- 10. c. Trojan ROGUE SECURITY SOFTWARE tricks the user into posing that it is a security software. But in reality they are not protected at all.
- 11. d. Spyware Program that runs in the background without you knowing it ( thus called “spy”) Has the ability to monitor what you are currently doing through keylogging.
- 12. d. Spyware Keyloggers - used to record the keystroke done by the user. -done to steal password or any other sensitive information -can record email, messages, any info.
- 13. e. Adware Program designed to send you advertisements, mostly as pop ups.
- 14. 2. SPAM Unwanted email mostly from bots or advertisers.
- 15. 3. PHISHING It’s goal is to acquire sensitive personal information like password & credit card details.
- 16. 3. PHISHING Done by sending you email that will direct the user to visit a website & be asked to update his/her username, password, credit card details or personal information.
- 17. *Pharming A more complicated way of phishing where it exploits DNS (Domain Name Service)
- 20. - As a responsible user of the internet, you have to consider that not everything out there is free for you to use.
- 21. TIPS TO AVOID COPYRIGHT INFRINGEMENT 1. Understand 2. Be responsible 3. Be Creative 4. Know the Law
- 22. Fair use logo
- 24. TIPS IN CONDUCTING RESEARCH ONLINE 1. Have a question in mind 2. Narrow it down 3. Advanced Search 4. Look for credible sources 5. Give Credit
- 26. Name of the Person or organization (the author of the information). Title of the home page in italics (title is shown in the title bar but is sometimes missing or unrelated). URL. Date last seen. Lapiz, Adrian Harold L. “Oleander’s Fun Facts about Bananas.” http://oleander.penz.com/random/bananalove.htm. Viewed on September 7, 2015 Proper Citation
