Why Does Your Company Need Effective Web Defense?
•
1 like•6,579 views
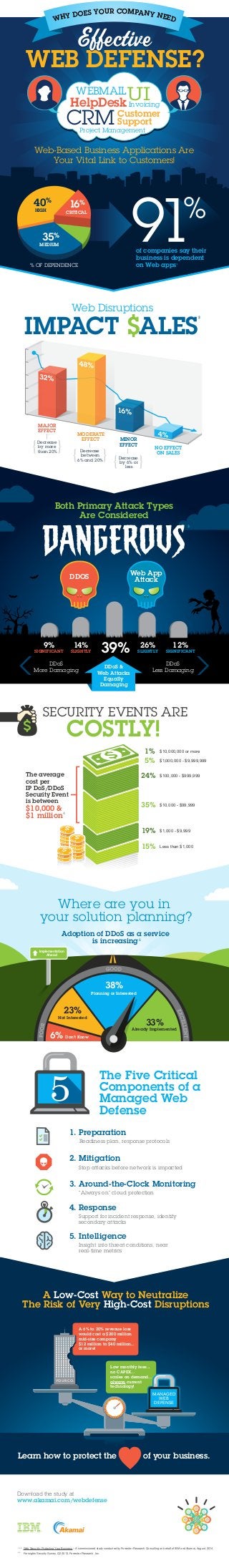
Why does your company need effective web defense? 91% of companies say their business is depended on web application, so effective web defense is critical! Check out this infographic for a compelling overview on why your company needs effective web defense. To learn more, visit: www.akamai.com/webdefense
Report
Share
Report
Share
Download to read offline
Recommended
Recommended
More Related Content
More from Akamai Technologies
More from Akamai Technologies (20)
3 Reasons You Need Proactive Protection Against Malware

3 Reasons You Need Proactive Protection Against Malware
3 razões chegou a hora de um novo modelo de acesso remoto

3 razões chegou a hora de um novo modelo de acesso remoto
3 motivi per cui è necessario un nuovo modello di accesso remoto

3 motivi per cui è necessario un nuovo modello di accesso remoto
3 raisons de changer votre modèle d'accès à distance

3 raisons de changer votre modèle d'accès à distance
3 motivos por los que ahora es el momento perfecto para adoptar un nuevo mode...

3 motivos por los que ahora es el momento perfecto para adoptar un nuevo mode...
Edge 2014: Maintaining the Balance: Getting the Most of Your CDN with IKEA

Edge 2014: Maintaining the Balance: Getting the Most of Your CDN with IKEA
Edge 2014: Increasing Control with Property Manager with eBay

Edge 2014: Increasing Control with Property Manager with eBay
Edge 2014: Bypass Surgery - Akamai's Heartbleed Response Case Study

Edge 2014: Bypass Surgery - Akamai's Heartbleed Response Case Study
Recently uploaded
Recently uploaded (20)
Potential of AI (Generative AI) in Business: Learnings and Insights

Potential of AI (Generative AI) in Business: Learnings and Insights
Modern Roaming for Notes and Nomad – Cheaper Faster Better Stronger

Modern Roaming for Notes and Nomad – Cheaper Faster Better Stronger
Zeshan Sattar- Assessing the skill requirements and industry expectations for...

Zeshan Sattar- Assessing the skill requirements and industry expectations for...
Merck Moving Beyond Passwords: FIDO Paris Seminar.pptx

Merck Moving Beyond Passwords: FIDO Paris Seminar.pptx
The Ultimate Guide to Choosing WordPress Pros and Cons

The Ultimate Guide to Choosing WordPress Pros and Cons
Abdul Kader Baba- Managing Cybersecurity Risks and Compliance Requirements i...

Abdul Kader Baba- Managing Cybersecurity Risks and Compliance Requirements i...
How to Effectively Monitor SD-WAN and SASE Environments with ThousandEyes

How to Effectively Monitor SD-WAN and SASE Environments with ThousandEyes
Emixa Mendix Meetup 11 April 2024 about Mendix Native development

Emixa Mendix Meetup 11 April 2024 about Mendix Native development
Testing tools and AI - ideas what to try with some tool examples

Testing tools and AI - ideas what to try with some tool examples
A Journey Into the Emotions of Software Developers

A Journey Into the Emotions of Software Developers
UiPath Community: Communication Mining from Zero to Hero

UiPath Community: Communication Mining from Zero to Hero
The Future Roadmap for the Composable Data Stack - Wes McKinney - Data Counci...

The Future Roadmap for the Composable Data Stack - Wes McKinney - Data Counci...
The Fit for Passkeys for Employee and Consumer Sign-ins: FIDO Paris Seminar.pptx

The Fit for Passkeys for Employee and Consumer Sign-ins: FIDO Paris Seminar.pptx
TrustArc Webinar - How to Build Consumer Trust Through Data Privacy

TrustArc Webinar - How to Build Consumer Trust Through Data Privacy
Transcript: New from BookNet Canada for 2024: Loan Stars - Tech Forum 2024

Transcript: New from BookNet Canada for 2024: Loan Stars - Tech Forum 2024
Varsha Sewlal- Cyber Attacks on Critical Critical Infrastructure

Varsha Sewlal- Cyber Attacks on Critical Critical Infrastructure
Passkey Providers and Enabling Portability: FIDO Paris Seminar.pptx

Passkey Providers and Enabling Portability: FIDO Paris Seminar.pptx
So einfach geht modernes Roaming fuer Notes und Nomad.pdf

So einfach geht modernes Roaming fuer Notes und Nomad.pdf
Generative Artificial Intelligence: How generative AI works.pdf

Generative Artificial Intelligence: How generative AI works.pdf
Unleashing Real-time Insights with ClickHouse_ Navigating the Landscape in 20...

Unleashing Real-time Insights with ClickHouse_ Navigating the Landscape in 20...
Why Does Your Company Need Effective Web Defense?
- 1. WHY DOES YOUR COMPANY NEED WEB DEFENSE? Invoicing UI WEBMAIL HelpDesk Customer Support CRM Project Management Web-Based Business Applications Are Your Vital Link to Customers! 40% 16% HIGH CRITICAL 35% % OF DEPENDENCE of companies say their business is dependent on Web apps1 Web Disruptions MEDIUM IMPACT $ALES2 MAJOR EFFECT Decrease by more than 20% Decrease MINOR EFFECT between 6% and 20% Decrease by 6% or less NO EFFECT ON SALES MODERATE EFFECT Both Primary Attack Types Are Considered DDOS Web App 14% 39% 3 SLIGHTLY Attack 26% SLIGHTLY 9% DDoS Less Damaging SECURITY EVENTS ARE COSTLY! 5% $1,000,000 - $9,999,999 24% $100,000 - $999,999 35% $10,000 - $99,999 19% $1,000 - $9,999 15% SIGNIFICANT 12% SIGNIFICANT DDoS & Web Attacks Equally Damaging DDoS More Damaging Less than $1,000 1% The average cost per IP DoS/DDoS Security Event is between $10,000 & $1 million $10,000,000 or more 4 Where are you in your solution planning? Adoption of DDoS as a service is increasing 5 33% 38% Planning or Interested Already Implemented The Five Critical Components of a Managed Web Defense 23% Not Interested 6% Don’t Know 1. Preparation Readiness plan, response protocols 2. Mitigation Stop attacks before network is impacted 3. Around-the-Clock Monitoring “Always on” cloud protection 4. Response Support for incident response, identify secondary attacks 5. Intelligence Insight into threat conditions, near real-time metrics A Low-Cost Way to Neutralize The Risk of Very High-Cost Disruptions A 6% to 20% revenue loss would cost a $200 million mid-size company $12 million to $40 million... or more! Low monthly fees... no CAPEX... scales on demand... always current technology! Implementation Ahead MANAGED WEB DEFENSE YOUR CO. Learn how to protect the of your business. Download the study at www.akamai.com/webdefense 1, 2, 3 Web Security: Protecting Your Business – A commissioned study conducted by Forrester Research Consulting on behalf of IBM and Akamai, August, 2014 4, 5 Forrsights Security Survey, Q2 2013, Forrester Research, Inc.
