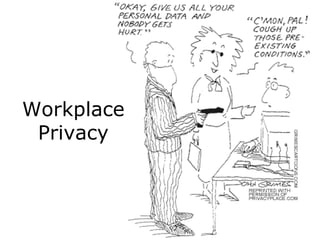
Workplace Privacy Presentation
•
5 likes•4,629 views
Presentation created for a Human Resources Course at the University of Western Ontario.
Report
Share
Report
Share
Recommended
More Related Content
What's hot
What's hot (20)
Data Privacy: What you need to know about privacy, from compliance to ethics

Data Privacy: What you need to know about privacy, from compliance to ethics
Viewers also liked
Data Privacy Rights @ Workplace - Balancing Employer Interests v. Employee Ri...

Data Privacy Rights @ Workplace - Balancing Employer Interests v. Employee Ri...Kavitha Gupta, CIPP-Asia
Viewers also liked (20)
Workplace Privacy and Employee Monitoring: Laws and Methods

Workplace Privacy and Employee Monitoring: Laws and Methods
Is employer monitoring of employee email justified

Is employer monitoring of employee email justified
Employee Privacy Rights: New Developments in the Law

Employee Privacy Rights: New Developments in the Law
Data Privacy Rights @ Workplace - Balancing Employer Interests v. Employee Ri...

Data Privacy Rights @ Workplace - Balancing Employer Interests v. Employee Ri...
A Framework of Purpose and Consent for Data Security and Consumer Privacy

A Framework of Purpose and Consent for Data Security and Consumer Privacy
What a data-centric strategy gives you that others do not

What a data-centric strategy gives you that others do not
Information from Jack Tuckner about Workplace Rights

Information from Jack Tuckner about Workplace Rights
QLD EILS Seminar: Emerging Issues in Workplace Privacy

QLD EILS Seminar: Emerging Issues in Workplace Privacy
Big Data, Security Intelligence, (And Why I Hate This Title) 

Big Data, Security Intelligence, (And Why I Hate This Title)
Similar to Workplace Privacy Presentation
The Information that You Gather: Application of Ethics & Privacy in Fundraising

The Information that You Gather: Application of Ethics & Privacy in FundraisingUniversity of Victoria
Similar to Workplace Privacy Presentation (20)
The Information that You Gather: Application of Ethics & Privacy in Fundraising

The Information that You Gather: Application of Ethics & Privacy in Fundraising
Privacy Practice Fundamentals: Understanding Compliance Regimes and Requirements

Privacy Practice Fundamentals: Understanding Compliance Regimes and Requirements
Privacy Best Practices for Lawyers: What Every Law Practice Needs to Know Abo...

Privacy Best Practices for Lawyers: What Every Law Practice Needs to Know Abo...
Legal Perspective on Information Management “New Social Media – The New Recor...

Legal Perspective on Information Management “New Social Media – The New Recor...
Introduction to US Privacy and Data Security Regulations and Requirements (Se...

Introduction to US Privacy and Data Security Regulations and Requirements (Se...
Protecting ePHI: What Providers and Business Associates Need to Know

Protecting ePHI: What Providers and Business Associates Need to Know
[Title Redacted for Privacy Purposes]: How Internal Audit Can Help Drive Priv...![[Title Redacted for Privacy Purposes]: How Internal Audit Can Help Drive Priv...](data:image/gif;base64,R0lGODlhAQABAIAAAAAAAP///yH5BAEAAAAALAAAAAABAAEAAAIBRAA7)
![[Title Redacted for Privacy Purposes]: How Internal Audit Can Help Drive Priv...](data:image/gif;base64,R0lGODlhAQABAIAAAAAAAP///yH5BAEAAAAALAAAAAABAAEAAAIBRAA7)
[Title Redacted for Privacy Purposes]: How Internal Audit Can Help Drive Priv...
InstructionsPaper A Application of a decision making framework 

InstructionsPaper A Application of a decision making framework
Introduction to US Privacy and Data Security: Regulations and Requirements

Introduction to US Privacy and Data Security: Regulations and Requirements
Recently uploaded
Recently uploaded (20)
DevoxxFR 2024 Reproducible Builds with Apache Maven

DevoxxFR 2024 Reproducible Builds with Apache Maven
What's New in Teams Calling, Meetings and Devices March 2024

What's New in Teams Calling, Meetings and Devices March 2024
Time Series Foundation Models - current state and future directions

Time Series Foundation Models - current state and future directions
Ensuring Technical Readiness For Copilot in Microsoft 365

Ensuring Technical Readiness For Copilot in Microsoft 365
Unraveling Multimodality with Large Language Models.pdf

Unraveling Multimodality with Large Language Models.pdf
Gen AI in Business - Global Trends Report 2024.pdf

Gen AI in Business - Global Trends Report 2024.pdf
Generative AI for Technical Writer or Information Developers

Generative AI for Technical Writer or Information Developers
Use of FIDO in the Payments and Identity Landscape: FIDO Paris Seminar.pptx

Use of FIDO in the Payments and Identity Landscape: FIDO Paris Seminar.pptx
Scale your database traffic with Read & Write split using MySQL Router

Scale your database traffic with Read & Write split using MySQL Router
(How to Program) Paul Deitel, Harvey Deitel-Java How to Program, Early Object...

(How to Program) Paul Deitel, Harvey Deitel-Java How to Program, Early Object...
DevEX - reference for building teams, processes, and platforms

DevEX - reference for building teams, processes, and platforms
Workplace Privacy Presentation
- 10. Privacy Decision Tree Turnbull, I. J. (Ed.) (2004). Privacy in the workplace: The employment perspective. Toronto: CCH Canadian.
