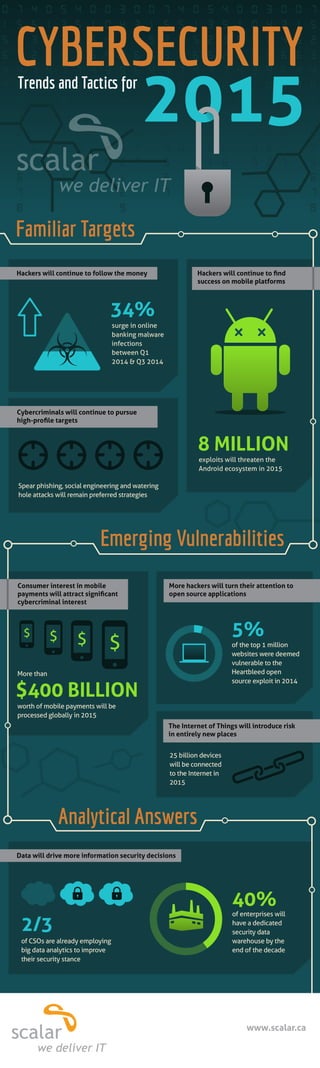
Cyber Security trends and tactics for 2015
•
1 gefällt mir•5,283 views
Our infographic takes a look at cyber security trends and tactics as we head into 2015.
Melden
Teilen
Melden
Teilen
Downloaden Sie, um offline zu lesen
Empfohlen
Empfohlen
Weitere ähnliche Inhalte
Andere mochten auch
Andere mochten auch (16)
Scalar Case Study: Strong Project Management Helps McMaster University Succes...

Scalar Case Study: Strong Project Management Helps McMaster University Succes...
@AtchisonFrazer Enterprise Mobile Security Trends, Challenges 

@AtchisonFrazer Enterprise Mobile Security Trends, Challenges
Executive Summary of the 2016 Scalar Security Study

Executive Summary of the 2016 Scalar Security Study
Key Findings from the 2015 IBM Cyber Security Intelligence Index

Key Findings from the 2015 IBM Cyber Security Intelligence Index
Mehr von Scalar Decisions
Mehr von Scalar Decisions (20)
2016 Scalar Security Study: The Cyber Security Readiness of Canadian Organiza...

2016 Scalar Security Study: The Cyber Security Readiness of Canadian Organiza...
Disrupting the Malware Kill Chain - What's New from Palo Alto Networks.

Disrupting the Malware Kill Chain - What's New from Palo Alto Networks.
Scalar Security Roadshow: Toronto Presentation - April 15, 2015

Scalar Security Roadshow: Toronto Presentation - April 15, 2015
Hyperconverged Infrastructure: The Leading Edge of Virtualization

Hyperconverged Infrastructure: The Leading Edge of Virtualization
The Cyber Security Readiness of Canadian Organizations

The Cyber Security Readiness of Canadian Organizations
Where Technology Meets Medicine: SickKids High Performance Computing Data Centre

Where Technology Meets Medicine: SickKids High Performance Computing Data Centre
Scalar Customer Case Study: Toronto 2015 Pan Am/Parapan Am Games

Scalar Customer Case Study: Toronto 2015 Pan Am/Parapan Am Games
Kürzlich hochgeladen
Enterprise Knowledge’s Urmi Majumder, Principal Data Architecture Consultant, and Fernando Aguilar Islas, Senior Data Science Consultant, presented "Driving Behavioral Change for Information Management through Data-Driven Green Strategy" on March 27, 2024 at Enterprise Data World (EDW) in Orlando, Florida.
In this presentation, Urmi and Fernando discussed a case study describing how the information management division in a large supply chain organization drove user behavior change through awareness of the carbon footprint of their duplicated and near-duplicated content, identified via advanced data analytics. Check out their presentation to gain valuable perspectives on utilizing data-driven strategies to influence positive behavioral shifts and support sustainability initiatives within your organization.
In this session, participants gained answers to the following questions:
- What is a Green Information Management (IM) Strategy, and why should you have one?
- How can Artificial Intelligence (AI) and Machine Learning (ML) support your Green IM Strategy through content deduplication?
- How can an organization use insights into their data to influence employee behavior for IM?
- How can you reap additional benefits from content reduction that go beyond Green IM?
Driving Behavioral Change for Information Management through Data-Driven Gree...

Driving Behavioral Change for Information Management through Data-Driven Gree...Enterprise Knowledge
Kürzlich hochgeladen (20)
Strategies for Unlocking Knowledge Management in Microsoft 365 in the Copilot...

Strategies for Unlocking Knowledge Management in Microsoft 365 in the Copilot...
[2024]Digital Global Overview Report 2024 Meltwater.pdf![[2024]Digital Global Overview Report 2024 Meltwater.pdf](data:image/gif;base64,R0lGODlhAQABAIAAAAAAAP///yH5BAEAAAAALAAAAAABAAEAAAIBRAA7)
![[2024]Digital Global Overview Report 2024 Meltwater.pdf](data:image/gif;base64,R0lGODlhAQABAIAAAAAAAP///yH5BAEAAAAALAAAAAABAAEAAAIBRAA7)
[2024]Digital Global Overview Report 2024 Meltwater.pdf
IAC 2024 - IA Fast Track to Search Focused AI Solutions

IAC 2024 - IA Fast Track to Search Focused AI Solutions
TrustArc Webinar - Stay Ahead of US State Data Privacy Law Developments

TrustArc Webinar - Stay Ahead of US State Data Privacy Law Developments
ProductAnonymous-April2024-WinProductDiscovery-MelissaKlemke

ProductAnonymous-April2024-WinProductDiscovery-MelissaKlemke
08448380779 Call Girls In Civil Lines Women Seeking Men

08448380779 Call Girls In Civil Lines Women Seeking Men
08448380779 Call Girls In Diplomatic Enclave Women Seeking Men

08448380779 Call Girls In Diplomatic Enclave Women Seeking Men
Axa Assurance Maroc - Insurer Innovation Award 2024

Axa Assurance Maroc - Insurer Innovation Award 2024
Workshop - Best of Both Worlds_ Combine KG and Vector search for enhanced R...

Workshop - Best of Both Worlds_ Combine KG and Vector search for enhanced R...
Understanding Discord NSFW Servers A Guide for Responsible Users.pdf

Understanding Discord NSFW Servers A Guide for Responsible Users.pdf
Driving Behavioral Change for Information Management through Data-Driven Gree...

Driving Behavioral Change for Information Management through Data-Driven Gree...
Mastering MySQL Database Architecture: Deep Dive into MySQL Shell and MySQL R...

Mastering MySQL Database Architecture: Deep Dive into MySQL Shell and MySQL R...
How to Troubleshoot Apps for the Modern Connected Worker

How to Troubleshoot Apps for the Modern Connected Worker
Powerful Google developer tools for immediate impact! (2023-24 C)

Powerful Google developer tools for immediate impact! (2023-24 C)
Presentation on how to chat with PDF using ChatGPT code interpreter

Presentation on how to chat with PDF using ChatGPT code interpreter
