Recommended
Recommended
More Related Content
What's hot
What's hot (20)
Similar to Rapid malware defenses
Similar to Rapid malware defenses (20)
Recently uploaded
💉💊+971581248768>> SAFE AND ORIGINAL ABORTION PILLS FOR SALE IN DUBAI AND ABUDHABI}}+971581248768
+971581248768 Mtp-Kit (500MG) Prices » Dubai [(+971581248768**)] Abortion Pills For Sale In Dubai, UAE, Mifepristone and Misoprostol Tablets Available In Dubai, UAE CONTACT DR.Maya Whatsapp +971581248768 We Have Abortion Pills / Cytotec Tablets /Mifegest Kit Available in Dubai, Sharjah, Abudhabi, Ajman, Alain, Fujairah, Ras Al Khaimah, Umm Al Quwain, UAE, Buy cytotec in Dubai +971581248768''''Abortion Pills near me DUBAI | ABU DHABI|UAE. Price of Misoprostol, Cytotec” +971581248768' Dr.DEEM ''BUY ABORTION PILLS MIFEGEST KIT, MISOPROTONE, CYTOTEC PILLS IN DUBAI, ABU DHABI,UAE'' Contact me now via What's App…… abortion Pills Cytotec also available Oman Qatar Doha Saudi Arabia Bahrain Above all, Cytotec Abortion Pills are Available In Dubai / UAE, you will be very happy to do abortion in Dubai we are providing cytotec 200mg abortion pill in Dubai, UAE. Medication abortion offers an alternative to Surgical Abortion for women in the early weeks of pregnancy. We only offer abortion pills from 1 week-6 Months. We then advise you to use surgery if its beyond 6 months. Our Abu Dhabi, Ajman, Al Ain, Dubai, Fujairah, Ras Al Khaimah (RAK), Sharjah, Umm Al Quwain (UAQ) United Arab Emirates Abortion Clinic provides the safest and most advanced techniques for providing non-surgical, medical and surgical abortion methods for early through late second trimester, including the Abortion By Pill Procedure (RU 486, Mifeprex, Mifepristone, early options French Abortion Pill), Tamoxifen, Methotrexate and Cytotec (Misoprostol). The Abu Dhabi, United Arab Emirates Abortion Clinic performs Same Day Abortion Procedure using medications that are taken on the first day of the office visit and will cause the abortion to occur generally within 4 to 6 hours (as early as 30 minutes) for patients who are 3 to 12 weeks pregnant. When Mifepristone and Misoprostol are used, 50% of patients complete in 4 to 6 hours; 75% to 80% in 12 hours; and 90% in 24 hours. We use a regimen that allows for completion without the need for surgery 99% of the time. All advanced second trimester and late term pregnancies at our Tampa clinic (17 to 24 weeks or greater) can be completed within 24 hours or less 99% of the time without the need surgery. The procedure is completed with minimal to no complications. Our Women's Health Center located in Abu Dhabi, United Arab Emirates, uses the latest medications for medical abortions (RU-486, Mifeprex, Mifegyne, Mifepristone, early options French abortion pill), Methotrexate and Cytotec (Misoprostol). The safety standards of our Abu Dhabi, United Arab Emirates Abortion Doctors remain unparalleled. They consistently maintain the lowest complication rates throughout the nation. Our Physicians and staff are always available to answer questions and care for women in one of the most difficult times in their lives. The decision to have an abortion at the Abortion Cl+971581248768>> SAFE AND ORIGINAL ABORTION PILLS FOR SALE IN DUBAI AND ABUDHA...

+971581248768>> SAFE AND ORIGINAL ABORTION PILLS FOR SALE IN DUBAI AND ABUDHA...?#DUbAI#??##{{(☎️+971_581248768%)**%*]'#abortion pills for sale in dubai@
Recently uploaded (20)
Spring Boot vs Quarkus the ultimate battle - DevoxxUK

Spring Boot vs Quarkus the ultimate battle - DevoxxUK
EMPOWERMENT TECHNOLOGY GRADE 11 QUARTER 2 REVIEWER

EMPOWERMENT TECHNOLOGY GRADE 11 QUARTER 2 REVIEWER
Exploring the Future Potential of AI-Enabled Smartphone Processors

Exploring the Future Potential of AI-Enabled Smartphone Processors
Connector Corner: Accelerate revenue generation using UiPath API-centric busi...

Connector Corner: Accelerate revenue generation using UiPath API-centric busi...
DEV meet-up UiPath Document Understanding May 7 2024 Amsterdam

DEV meet-up UiPath Document Understanding May 7 2024 Amsterdam
Strategize a Smooth Tenant-to-tenant Migration and Copilot Takeoff

Strategize a Smooth Tenant-to-tenant Migration and Copilot Takeoff
Navigating the Deluge_ Dubai Floods and the Resilience of Dubai International...

Navigating the Deluge_ Dubai Floods and the Resilience of Dubai International...
Finding Java's Hidden Performance Traps @ DevoxxUK 2024

Finding Java's Hidden Performance Traps @ DevoxxUK 2024
2024: Domino Containers - The Next Step. News from the Domino Container commu...

2024: Domino Containers - The Next Step. News from the Domino Container commu...
Repurposing LNG terminals for Hydrogen Ammonia: Feasibility and Cost Saving

Repurposing LNG terminals for Hydrogen Ammonia: Feasibility and Cost Saving
AWS Community Day CPH - Three problems of Terraform

AWS Community Day CPH - Three problems of Terraform
Apidays New York 2024 - Scaling API-first by Ian Reasor and Radu Cotescu, Adobe

Apidays New York 2024 - Scaling API-first by Ian Reasor and Radu Cotescu, Adobe
Axa Assurance Maroc - Insurer Innovation Award 2024

Axa Assurance Maroc - Insurer Innovation Award 2024
How to Troubleshoot Apps for the Modern Connected Worker

How to Troubleshoot Apps for the Modern Connected Worker
+971581248768>> SAFE AND ORIGINAL ABORTION PILLS FOR SALE IN DUBAI AND ABUDHA...

+971581248768>> SAFE AND ORIGINAL ABORTION PILLS FOR SALE IN DUBAI AND ABUDHA...
Rapid malware defenses
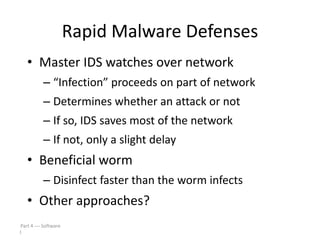
- 1. Rapid Malware Defenses • Master IDS watches over network – “Infection” proceeds on part of network – Determines whether an attack or not – If so, IDS saves most of the network – If not, only a slight delay • Beneficial worm – Disinfect faster than the worm infects • Other approaches? Part 4 Software 1
- 2. Push vs Pull Malware • Viruses/worms examples of “push” • Recently, a lot of “pull” malware • Scenario – A compromised web server – Visit a website at compromised server – Malware loaded on you machine • Good paper: Ghost in the Browser Part 4 Software 2
- 3. Botnet • Botnet: a “network” of infected machines • Infected machines are “bots” – Victim is unaware of infection (stealthy) • Botmaster controls botnet – Generally, using IRC – P2P botnet architectures exist • Botnets used for… – Spam, DoS attacks, key logging, ID theft, etc. Part 4 Software 3
- 4. Botnet Examples • XtremBot – Similar bots: Agobot, Forbot, Phatbot – Highly modular, easily modified – Source code readily available (GPL license) • UrXbot – Similar bots: SDBot, UrBot, Rbot – Less sophisticated than XtremBot type • GT-Bots and mIRC-based bots – mIRC is common IRC client for Windows Part 4 Software 4
- 5. More Botnet Examples • Mariposa – Used to steal credit card info – Creator arrested in July 2010 • Conficker – Estimated 10M infected hosts (2009) • Kraken – Largest as of 2008 (400,000 infections) • Srizbi – For spam, one of largest as of 2008 Part 4 Software 5
- 6. Computer Infections • Analogies are made between computer viruses/worms and biological diseases • There are differences – Computer infections are much quicker – Ability to intervene in computer outbreak is more limited (vaccination?) – Bio disease models often not applicable – “Distance” almost meaningless on Internet • But there are some similarities… Part 4 Software 6
- 7. Computer Infections • Cyber “diseases” vs biological diseases • One similarity – In nature, too few susceptible individuals and disease will die out – In the Internet, too few susceptible systems and worm might fail to take hold • One difference – In nature, diseases attack more-or-less at random – Cyber attackers select most “desirable” targets – Cyber attacks are more focused and damaging Part 4 Software 7
- 8. Future Malware Detection? • Likely that malware outnumbers “good ware” – Metamorphic copies of existing malware – Many virus toolkits available – Trudy: recycle old viruses, different signature • So, may be better to “detect” good code – If code not on “good” list, assume it’s bad – That is, use white list instead of blacklist Part 4 Software 8