Melden
Teilen
Downloaden Sie, um offline zu lesen
Empfohlen
Weitere ähnliche Inhalte
Mehr von Rafel Ivgi
Mehr von Rafel Ivgi (20)
Implementing and auditing security controls part 2

Implementing and auditing security controls part 2
Implementing and auditing security controls part 1

Implementing and auditing security controls part 1
Firmitas Cyber Solutions - Inforgraphic - Mirai Botnet - A few basic facts on...

Firmitas Cyber Solutions - Inforgraphic - Mirai Botnet - A few basic facts on...
Firmitas Cyber Solutions - Inforgraphic - ICS & SCADA Vulnerabilities

Firmitas Cyber Solutions - Inforgraphic - ICS & SCADA Vulnerabilities
Kürzlich hochgeladen
Kürzlich hochgeladen (20)
Nell’iperspazio con Rocket: il Framework Web di Rust!

Nell’iperspazio con Rocket: il Framework Web di Rust!
TrustArc Webinar - How to Build Consumer Trust Through Data Privacy

TrustArc Webinar - How to Build Consumer Trust Through Data Privacy
Transcript: New from BookNet Canada for 2024: BNC CataList - Tech Forum 2024

Transcript: New from BookNet Canada for 2024: BNC CataList - Tech Forum 2024
Time Series Foundation Models - current state and future directions

Time Series Foundation Models - current state and future directions
Gen AI in Business - Global Trends Report 2024.pdf

Gen AI in Business - Global Trends Report 2024.pdf
DSPy a system for AI to Write Prompts and Do Fine Tuning

DSPy a system for AI to Write Prompts and Do Fine Tuning
DevEX - reference for building teams, processes, and platforms

DevEX - reference for building teams, processes, and platforms
Use of FIDO in the Payments and Identity Landscape: FIDO Paris Seminar.pptx

Use of FIDO in the Payments and Identity Landscape: FIDO Paris Seminar.pptx
Dev Dives: Streamline document processing with UiPath Studio Web

Dev Dives: Streamline document processing with UiPath Studio Web
What's New in Teams Calling, Meetings and Devices March 2024

What's New in Teams Calling, Meetings and Devices March 2024
The Ultimate Guide to Choosing WordPress Pros and Cons

The Ultimate Guide to Choosing WordPress Pros and Cons
Passkey Providers and Enabling Portability: FIDO Paris Seminar.pptx

Passkey Providers and Enabling Portability: FIDO Paris Seminar.pptx
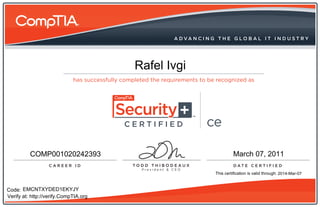
Comptia Security+ CE Certificate
- 1. CERTIFIED ce Rafel Ivgi CERTIFIED ce COMP001020242393 March 07, 2011 This certification is valid through: 2014-Mar-07 Code: EMCNTXYDED1EKYJY Verify at: http://verify.CompTIA.org
