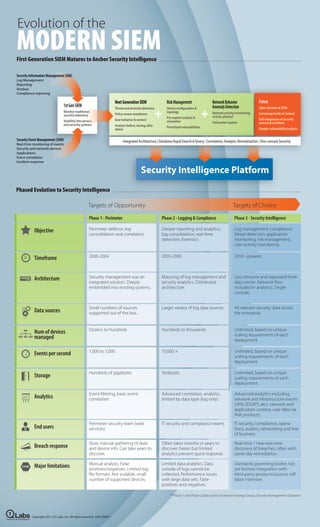
Evolution of the Modern SIEM
- 1. Evolution of the MODERN SIEM First Generation SIEM Matures to Anchor Security Intelligence Security Information Management (SIM) Log Management Reporting Analysis Compliance reporting Next Generation SIEM Risk Management Network Behavior Future 1st Gen SIEM Anomaly Detection + + Threat and anomaly detection Device con guration & Open Systems & SDKs Monitor traditional topology Network activity monitoring; security telemetry Policy-aware compliance Increasing levels of context Pre-exploit analysis & virtual, physical Visibility into servers User behavior & context Full integration of security simulation Full packet capture process & work ow and security systems Analysis before, during, after Prioritized vulnerabilities Greater predictive ability attack Security Event Management (SEM) Integrated Architecture | Database Rapid Search & Query | Correlation, Analysis, Normalization | One-console Security Real-time monitoring of events Security and network devices Applications Event correlation Incident response Security Intelligence Platform Phased Evolution to Security Intelligence Targets of Opportunity Targets of Choice Phase 1 - Perimeter Phase 2 - Logging & Compliance Phase 3 - Security Intelligence Objective Perimeter defense, log Deeper reporting and analytics, Log management, compliance, consolidation and correlation log consolidation, real-time threat detection, application detection, forensics monitoring, risk management, user activity monitoring Timeframe 2000-2004 2005-2009 2010 - present Architecture Security management was an Maturing of log management and Less intrusive and separated from integrated solution. Deeply security analytics. Distributed data center. Network ow embedded into existing systems. architecture. included in analytics. Single console. Small numbers of sources Larger variety of log data sources. All relevant security data across Data sources supported out of the box. the enterprise. Dozens to hundreds Hundreds to thousands Unlimited, based on unique Num of devices scaling requirements of each managed deployment 1,000 to 5,000 10,000 + Unlimited, based on unique Events per second scaling requirements of each deployment Hundreds of gigabytes Terabytes Unlimited, based on unique Storage scaling requirements of each deployment Event ltering, basic event Advanced correlation, analytics Advanced analytics including Analytics correlation limited by data type (log only) network and infrastructure events (VPN, IDS/IPS, etc), network and application context, user data via IAM products. Perimeter security team (web IT security and compliance teams IT security, compliance, opera- End users services) tions, auditor, networking and line of business Slow, manual gathering of data Often takes months or years to Real-time / near-real-time Breach response and device info. Can take years to discover. Faster, but limited discovery of breaches, often with discover. analytics prevent quick response. same-day remediation. Manual analysis. False Limited data analytics. Data Standards governing bodies not Major limitations positives/negatives. Limited log outside of logs cannot be yet formed. Integration with le formats. Not scalable, small collected. Performance issues third-party products/sources still number of supported devices. with large data sets. False labor intensive. positives and negatives. ** Phase 1 and Phase 2 data source: Enterprise Strategy Group, Security Management Evolution Copyright 2011 Q1 Labs, Inc. All rights reserved. EMS-IG0911 Total Security Intelligence
