Dp3
•
0 gefällt mir•253 views
Why care about data protection?
Melden
Teilen
Melden
Teilen
Empfohlen
Paul Louis Arslanian, Former Director Bureau d´Enteques et d´Analyses until 2...

Paul Louis Arslanian, Former Director Bureau d´Enteques et d´Analyses until 2...Colegio Oficial de Pilotos de la Aviación Comercial
Weitere ähnliche Inhalte
Ähnlich wie Dp3
Paul Louis Arslanian, Former Director Bureau d´Enteques et d´Analyses until 2...

Paul Louis Arslanian, Former Director Bureau d´Enteques et d´Analyses until 2...Colegio Oficial de Pilotos de la Aviación Comercial
Ähnlich wie Dp3 (20)
Lasa European NFP Technology Conference 2010 - Data protection and the cloud

Lasa European NFP Technology Conference 2010 - Data protection and the cloud
Business Intelligence (BI) Tools For Computer Forensic

Business Intelligence (BI) Tools For Computer Forensic
VTU - MIS Module 8 - Security and Ethical Challenges

VTU - MIS Module 8 - Security and Ethical Challenges
Paul Louis Arslanian, Former Director Bureau d´Enteques et d´Analyses until 2...

Paul Louis Arslanian, Former Director Bureau d´Enteques et d´Analyses until 2...
Gdpr compliance univ'air carslon wagon lit 5 oktober 2017

Gdpr compliance univ'air carslon wagon lit 5 oktober 2017
Mehr von Tommy Vandepitte
Mehr von Tommy Vandepitte (20)
Gegevensbescherming-clausule in (overheids)opdracht

Gegevensbescherming-clausule in (overheids)opdracht
20190131 - Presentation Q&A on legislation's influence (on travel management)

20190131 - Presentation Q&A on legislation's influence (on travel management)
Kürzlich hochgeladen
Kürzlich hochgeladen (20)
Bridging Between CAD & GIS: 6 Ways to Automate Your Data Integration

Bridging Between CAD & GIS: 6 Ways to Automate Your Data Integration
Passkey Providers and Enabling Portability: FIDO Paris Seminar.pptx

Passkey Providers and Enabling Portability: FIDO Paris Seminar.pptx
All These Sophisticated Attacks, Can We Really Detect Them - PDF

All These Sophisticated Attacks, Can We Really Detect Them - PDF
Generative AI - Gitex v1Generative AI - Gitex v1.pptx

Generative AI - Gitex v1Generative AI - Gitex v1.pptx
The Fit for Passkeys for Employee and Consumer Sign-ins: FIDO Paris Seminar.pptx

The Fit for Passkeys for Employee and Consumer Sign-ins: FIDO Paris Seminar.pptx
Infrared simulation and processing on Nvidia platforms

Infrared simulation and processing on Nvidia platforms
A Journey Into the Emotions of Software Developers

A Journey Into the Emotions of Software Developers
Glenn Lazarus- Why Your Observability Strategy Needs Security Observability

Glenn Lazarus- Why Your Observability Strategy Needs Security Observability
Testing tools and AI - ideas what to try with some tool examples

Testing tools and AI - ideas what to try with some tool examples
Scale your database traffic with Read & Write split using MySQL Router

Scale your database traffic with Read & Write split using MySQL Router
UiPath Community: Communication Mining from Zero to Hero

UiPath Community: Communication Mining from Zero to Hero
Digital Identity is Under Attack: FIDO Paris Seminar.pptx

Digital Identity is Under Attack: FIDO Paris Seminar.pptx
Arizona Broadband Policy Past, Present, and Future Presentation 3/25/24

Arizona Broadband Policy Past, Present, and Future Presentation 3/25/24
Abdul Kader Baba- Managing Cybersecurity Risks and Compliance Requirements i...

Abdul Kader Baba- Managing Cybersecurity Risks and Compliance Requirements i...
Long journey of Ruby standard library at RubyConf AU 2024

Long journey of Ruby standard library at RubyConf AU 2024
Zeshan Sattar- Assessing the skill requirements and industry expectations for...

Zeshan Sattar- Assessing the skill requirements and industry expectations for...
QCon London: Mastering long-running processes in modern architectures

QCon London: Mastering long-running processes in modern architectures
Dp3
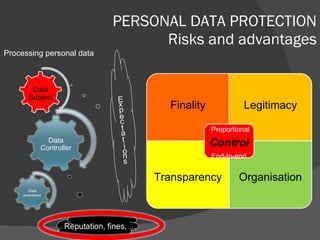
- 1. PERSONAL DATA PROTECTION Risks and advantages Processing personal data Finality Legitimacy Transparency Organisation Proportional End-to-end
Hinweis der Redaktion
- 05/12/10