Melden
Teilen
Downloaden Sie, um offline zu lesen
Empfohlen
Bringing Safety Climate Theory to Life in the Electrical Industry

Bringing Safety Climate Theory to Life in the Electrical IndustryOccupational Health and Safety Industry Group
Ethical AI at VDAB, presented by Vincent Buekenhout (Ethical AI Lead, VDAB) a...

Ethical AI at VDAB, presented by Vincent Buekenhout (Ethical AI Lead, VDAB) a...Patrick Van Renterghem
Weitere ähnliche Inhalte
Andere mochten auch
Andere mochten auch (9)
Programa para integração da Cultura e Turismo - resumo 

Programa para integração da Cultura e Turismo - resumo
Caracterização e Dimensionamento do Turismo Receptivo na Bahia 2014

Caracterização e Dimensionamento do Turismo Receptivo na Bahia 2014
Plano Estratégico do Turismo Náutico da Baía de Todos os-Santos

Plano Estratégico do Turismo Náutico da Baía de Todos os-Santos
2010 03-02 shared savings model - marillac and st. mary's hospital

2010 03-02 shared savings model - marillac and st. mary's hospital
Ähnlich wie IS Undergrads Class 8
Bringing Safety Climate Theory to Life in the Electrical Industry

Bringing Safety Climate Theory to Life in the Electrical IndustryOccupational Health and Safety Industry Group
Ethical AI at VDAB, presented by Vincent Buekenhout (Ethical AI Lead, VDAB) a...

Ethical AI at VDAB, presented by Vincent Buekenhout (Ethical AI Lead, VDAB) a...Patrick Van Renterghem
Ähnlich wie IS Undergrads Class 8 (20)
Anastasia Bilous: Machine Learning & AI Involvement in IT businesses

Anastasia Bilous: Machine Learning & AI Involvement in IT businesses
Information architecture for men in kilts slideshare

Information architecture for men in kilts slideshare
AI Restart 2023: Guillermo Alda - How AI is transforming companies, inside out

AI Restart 2023: Guillermo Alda - How AI is transforming companies, inside out
StatsCraft 2015: The problem (Keynote) - Nir Cohen

StatsCraft 2015: The problem (Keynote) - Nir Cohen
The elements of product success for business leaders

The elements of product success for business leaders
Evolutionary Approach for EIS Strategy Decision Making Framework and Efficien...

Evolutionary Approach for EIS Strategy Decision Making Framework and Efficien...
Bringing Safety Climate Theory to Life in the Electrical Industry

Bringing Safety Climate Theory to Life in the Electrical Industry
Ethical AI at VDAB, presented by Vincent Buekenhout (Ethical AI Lead, VDAB) a...

Ethical AI at VDAB, presented by Vincent Buekenhout (Ethical AI Lead, VDAB) a...
Innovation in Cybersecurity [Montreal 2018 CRIAQ RDV Forum]![Innovation in Cybersecurity [Montreal 2018 CRIAQ RDV Forum]](data:image/gif;base64,R0lGODlhAQABAIAAAAAAAP///yH5BAEAAAAALAAAAAABAAEAAAIBRAA7)
![Innovation in Cybersecurity [Montreal 2018 CRIAQ RDV Forum]](data:image/gif;base64,R0lGODlhAQABAIAAAAAAAP///yH5BAEAAAAALAAAAAABAAEAAAIBRAA7)
Innovation in Cybersecurity [Montreal 2018 CRIAQ RDV Forum]
Convergence Of Technology And Core Business Strategy

Convergence Of Technology And Core Business Strategy
From Data Science to Business Value - Analytics Applied

From Data Science to Business Value - Analytics Applied
Mehr von Joao Cunha
Mehr von Joao Cunha (20)
Kürzlich hochgeladen
Kürzlich hochgeladen (20)
Ensure the security of your HCL environment by applying the Zero Trust princi...

Ensure the security of your HCL environment by applying the Zero Trust princi...
VIP Call Girl Jamshedpur Aashi 8250192130 Independent Escort Service Jamshedpur

VIP Call Girl Jamshedpur Aashi 8250192130 Independent Escort Service Jamshedpur
Insurers' journeys to build a mastery in the IoT usage

Insurers' journeys to build a mastery in the IoT usage
Mysore Call Girls 8617370543 WhatsApp Number 24x7 Best Services

Mysore Call Girls 8617370543 WhatsApp Number 24x7 Best Services
VIP Kolkata Call Girl Howrah 👉 8250192130 Available With Room

VIP Kolkata Call Girl Howrah 👉 8250192130 Available With Room
Yaroslav Rozhankivskyy: Три складові і три передумови максимальної продуктивн...

Yaroslav Rozhankivskyy: Три складові і три передумови максимальної продуктивн...
Call Girls Pune Just Call 9907093804 Top Class Call Girl Service Available

Call Girls Pune Just Call 9907093804 Top Class Call Girl Service Available
0183760ssssssssssssssssssssssssssss00101011 (27).pdf

0183760ssssssssssssssssssssssssssss00101011 (27).pdf
Cash Payment 9602870969 Escort Service in Udaipur Call Girls

Cash Payment 9602870969 Escort Service in Udaipur Call Girls
Sales & Marketing Alignment: How to Synergize for Success

Sales & Marketing Alignment: How to Synergize for Success
Call Girls in Gomti Nagar - 7388211116 - With room Service

Call Girls in Gomti Nagar - 7388211116 - With room Service
IS Undergrads Class 8
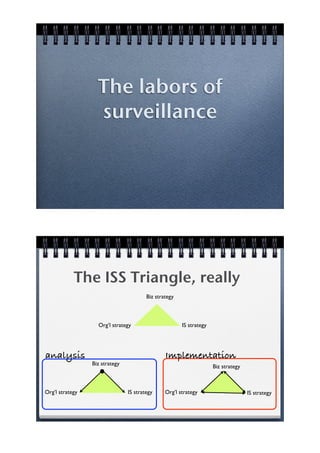
- 1. The labors of surveillance The ISS Triangle, really Biz strategy Org’l strategy IS strategy analysis Implementation Biz strategy Biz strategy Org’l strategy IS strategy Org’l strategy IS strategy
- 2. IS strategy --> Biz strategy Implementation Biz strategy Systems thinking Outliars simple measurements Surfacing ? secrets Org’l strategy IS strategy IT and leadership: Metaphor.
- 3. The two axes of panopticism Visible Unverifiable The panoptic process People control and police themselves • Unverifiable control places the locus of control within the subject ! mind, not guard • In a perfect panopticon, people are unaware of their domination ! they ascribe their behavior to motivation
- 4. The bases of panopticism People behave according to theory X A corporation’s tools belong to it, not to employees Surveillance is included into the employment contract Examples of surveillance technologies Packet sniffers Log files Desktop monitoring programs Phone recording Closed-circuit cameras
- 5. Uses of surveillance technologies 78% of all companies use surveillance IT Reviewing computer files: 1 in 3 Video recording: 1 in 8 Reviewing calls: 1 in 9 Reviewing voice mail: 1 in 11 What is identity? Consistent story That we tell ourselves and others About what happened to us and about what he did in the past
- 6. Why do we need identity? Our brain works with models and needs ontological security Measurement and face Ooooops!
- 7. Identity and face Face is the sign (+/-) of our ID Human beings need a positive ID We all work very hard at it We breed to remain physically alive, we do facework to remain socially alive
- 8. Measuring work Vertical Surveillance Peer surveillance The problems of panopticsm Theory X is Compliance, not self-fulfilling commitment
- 9. Conclusion
