Revision Viruses ( Gerardo E)
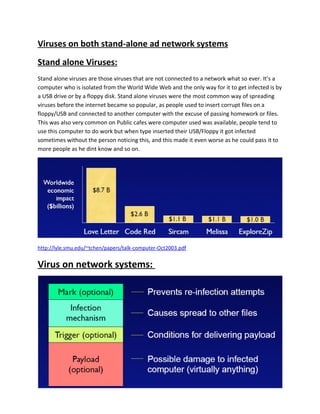
- 1. Viruses on both stand-alone ad network systems Stand alone Viruses: Stand alone viruses are those viruses that are not connected to a network what so ever. It’s a computer who is isolated from the World Wide Web and the only way for it to get infected is by a USB drive or by a floppy disk. Stand alone viruses were the most common way of spreading viruses before the internet became so popular, as people used to insert corrupt files on a floppy/USB and connected to another computer with the excuse of passing homework or files. This was also very common on Public cafes were computer used was available, people tend to use this computer to do work but when type inserted their USB/Floppy it got infected sometimes without the person noticing this, and this made it even worse as he could pass it to more people as he dint know and so on. http://lyle.smu.edu/~tchen/papers/talk-computer-Oct2003.pdf Virus on network systems:
- 2. Viruses on the Network system are now the most common way for spreading viruses. Usually, it propagates through shared resources, such as shared drives and folders. Once it infects a new system, it searches for potential targets by searching the network for other vulnerable systems. (http://library.thinkquest.org/06aug/02257/virus_types.html). Macro Viruses are types of viruses consists on the distribution of files such as excel or word via email that are corrupt meaning that they could have the information needed or a message but the file itself is corrupt and there are two ways of it spreading the unwilling way which you didn’t notice that the file was corrupt or that you have just been infected so consequently depending on the type of virus your documents become corrupt and in the time of sending someone an email containing your document you spread the virus as well. Another way is that you have receive an email and you forward it without knowing that it’s a virus, on the other hand some people who are not thinking ethically or don’t care know that what they have received a virus and instead of deleting it and making society a favor they send the email knowing that a person who is not protected will be compromised. Types of Viruses on the network: • “Worm is a stand alone program that exploits security holes to compromise other computers and spread copies of itself through the network.”( http://lyle.smu.edu/~tchen/papers/talk-computer-Oct2003.pdf) o Unlike viruses worms don’t necessarily attach to other programs, and they are not detectable by a file scanner, and the worst part is that they spread without any human action. The most common example of a Worm virus is “Love letter” which was sent via email that pretended to be a love letter, the attachment appeared to be text but once opened it infected Windows and the systems (figure 1).
- 3. • Sentinels: This is a type of virus that allows the virus controller or programmer to control the computer already infected. • Boot sector viruses: This is a type of virus that hides on the boot sectors such as a bootable disk or hardrive. A boot virus doesn’t affect the files inside this but affects the disk containing them. • Multipartite Viruses are a combination of a file virus and a boot sector virus as they work together to infected the files and the boot sector of the hard drive they are saved on and later on to the system. • Trojan horse Virus: This is a type of virus the which appears to be processing a command but instead its downloading malicious function into the system which allows he virus controller to save the files on his computer, to watch what you are doing and even be able to control the computer. Bibliography: 1. http://library.thinkquest.org/06aug/02257/virus_types.html 2. http://lyle.smu.edu/~tchen/papers/talk-computer-Oct2003.pdf 3. http://en.wikipedia.org/wiki/Trojan_horse_(computing)