Connected Car Hacking: OBD2 Port & Mobile Apps Top Vulnerabilities
•
65 gefällt mir•10,570 views
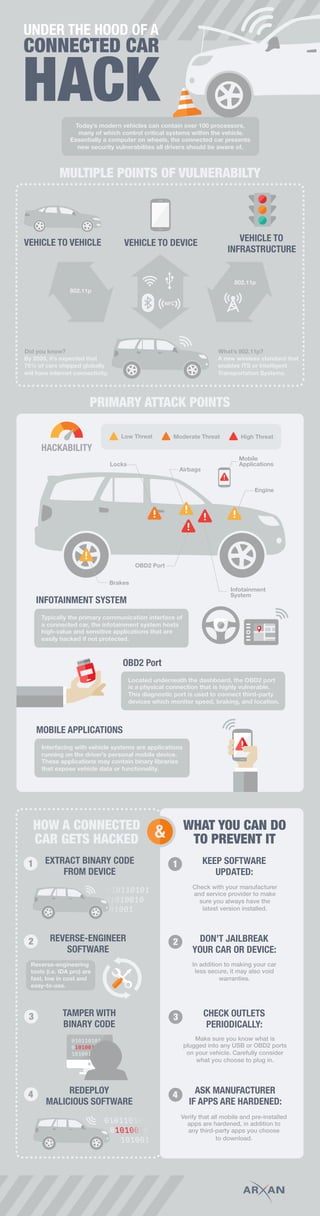
The document discusses security vulnerabilities in connected cars. Modern vehicles contain over 100 processors controlling critical systems, essentially making them computers on wheels. This presents multiple points of vulnerability, with primary attack points being the OBD2 port located under the dashboard and mobile applications interfacing with vehicle systems. Hackers can extract binary code from these systems, reverse engineer the software, and tamper with code to deploy malicious software affecting systems like the engine, brakes, or airbags. The infotainment system is also vulnerable due to hosting sensitive apps.
Melden
Teilen
Melden
Teilen
Downloaden Sie, um offline zu lesen
Empfohlen
Weitere ähnliche Inhalte
Was ist angesagt?
Was ist angesagt? (20)
DWS15 - Connected things forum - conclusive keynote - Raj Talluri

DWS15 - Connected things forum - conclusive keynote - Raj Talluri
Autonomous Driving: Philosophical Changes in Insurance and Public Readiness

Autonomous Driving: Philosophical Changes in Insurance and Public Readiness
Ericsson ConsumerLab – Wearable technology and the internet of things 

Ericsson ConsumerLab – Wearable technology and the internet of things
The Challenge of Managing & Securing Data in the Mobile World. By Stuart Chev...

The Challenge of Managing & Securing Data in the Mobile World. By Stuart Chev...
Realizing the Promise of the Mobile Workforce through a Mobile Device Platfor...

Realizing the Promise of the Mobile Workforce through a Mobile Device Platfor...
Connected Cars - Poster Child for the IoT Reality Check

Connected Cars - Poster Child for the IoT Reality Check
Oies_IoT_week_lisbon_201506_wearablesfieldservice_final

Oies_IoT_week_lisbon_201506_wearablesfieldservice_final
New Technology - our opportunities in the meeting industry

New Technology - our opportunities in the meeting industry
AI/Artificial Intelligent in Aviation Beyond Covid 19

AI/Artificial Intelligent in Aviation Beyond Covid 19
Rio Info 2015 - Projetos de Big Data no Setor Público - Karin Breitman

Rio Info 2015 - Projetos de Big Data no Setor Público - Karin Breitman
Ähnlich wie Connected Car Hacking: OBD2 Port & Mobile Apps Top Vulnerabilities
Ähnlich wie Connected Car Hacking: OBD2 Port & Mobile Apps Top Vulnerabilities (20)
Countering Cybersecurity Risk in Today's IoT World

Countering Cybersecurity Risk in Today's IoT World
Seminar topic -ROLE OF CYBER SECURITY IN CON CAR.pptx

Seminar topic -ROLE OF CYBER SECURITY IN CON CAR.pptx
WHITE PAPER▶ Building Comprehensive Security Into Cars

WHITE PAPER▶ Building Comprehensive Security Into Cars
Advancements and Hurdles in the Evolution of Automotive Wireless Interfaces: ...

Advancements and Hurdles in the Evolution of Automotive Wireless Interfaces: ...
Hacking your Connected Car: What you need to know NOW

Hacking your Connected Car: What you need to know NOW
Is cybersecurity protection of commercial vehicles harder?

Is cybersecurity protection of commercial vehicles harder?
Alexander Olenyev & Andrey Voloshin - Car Hacking: Yes, You can do that!

Alexander Olenyev & Andrey Voloshin - Car Hacking: Yes, You can do that!
Mehr von IBM Security
Mehr von IBM Security (20)
Leaders & Laggards: The Latest Findings from the Ponemon Institute’s Study on...

Leaders & Laggards: The Latest Findings from the Ponemon Institute’s Study on...
Bridging the Gap between Privacy and Security: Using Technology to Manage Com...

Bridging the Gap between Privacy and Security: Using Technology to Manage Com...
The Resilient End-of-Year Review: The Top Cyber Security Trends in 2018 and P...

The Resilient End-of-Year Review: The Top Cyber Security Trends in 2018 and P...
Leveraging Validated and Community Apps to Build a Versatile and Orchestrated...

Leveraging Validated and Community Apps to Build a Versatile and Orchestrated...
Accelerating SOC Transformation with IBM Resilient and Carbon Black

Accelerating SOC Transformation with IBM Resilient and Carbon Black
How to Build a Faster, Laser-Sharp SOC with Intelligent Orchestration

How to Build a Faster, Laser-Sharp SOC with Intelligent Orchestration
Orchestrate Your Security Defenses to Optimize the Impact of Threat Intelligence

Orchestrate Your Security Defenses to Optimize the Impact of Threat Intelligence
Your Mainframe Environment is a Treasure Trove: Is Your Sensitive Data Protec...

Your Mainframe Environment is a Treasure Trove: Is Your Sensitive Data Protec...
Meet the New IBM i2 QRadar Offense Investigator App and Start Threat Hunting ...

Meet the New IBM i2 QRadar Offense Investigator App and Start Threat Hunting ...
Understanding the Impact of Today's Security Breaches: The 2017 Ponemon Cost ...

Understanding the Impact of Today's Security Breaches: The 2017 Ponemon Cost ...
How to Improve Threat Detection & Simplify Security Operations

How to Improve Threat Detection & Simplify Security Operations
Orchestrate Your Security Defenses; Protect Against Insider Threats 

Orchestrate Your Security Defenses; Protect Against Insider Threats
Kürzlich hochgeladen
(COD) ̄Young Call Girls In Dwarka , New Delhi꧁❤ 7042364481❤꧂ Escorts Service i...

(COD) ̄Young Call Girls In Dwarka , New Delhi꧁❤ 7042364481❤꧂ Escorts Service i...Hot Call Girls In Sector 58 (Noida)
Hauz Khas Call Girls ☎ 7042364481 independent Escorts Service in delhi

Hauz Khas Call Girls ☎ 7042364481 independent Escorts Service in delhiHot Call Girls In Sector 58 (Noida)
Kürzlich hochgeladen (20)
Alia +91-9537192988-Experience the Unmatchable Pleasure with Model Ahmedabad ...

Alia +91-9537192988-Experience the Unmatchable Pleasure with Model Ahmedabad ...
Delhi Call Girls Mayur Vihar 9711199171 ☎✔👌✔ Whatsapp Hard And Sexy Vip Call

Delhi Call Girls Mayur Vihar 9711199171 ☎✔👌✔ Whatsapp Hard And Sexy Vip Call
How To Troubleshoot Mercedes Blind Spot Assist Inoperative Error

How To Troubleshoot Mercedes Blind Spot Assist Inoperative Error
Delhi Call Girls East Of Kailash 9711199171 ☎✔👌✔ Whatsapp Hard And Sexy Vip Call

Delhi Call Girls East Of Kailash 9711199171 ☎✔👌✔ Whatsapp Hard And Sexy Vip Call
FULL ENJOY - 9953040155 Call Girls in Sector 61 | Noida

FULL ENJOY - 9953040155 Call Girls in Sector 61 | Noida
Hot And Sexy 🥵 Call Girls Delhi Daryaganj {9711199171} Ira Malik High class G...

Hot And Sexy 🥵 Call Girls Delhi Daryaganj {9711199171} Ira Malik High class G...
VIP Russian Call Girls in Jamshedpur Deepika 8250192130 Independent Escort Se...

VIP Russian Call Girls in Jamshedpur Deepika 8250192130 Independent Escort Se...
ENJOY Call Girls In Okhla Vihar Delhi Call 9654467111

ENJOY Call Girls In Okhla Vihar Delhi Call 9654467111
Call Girls in Malviya Nagar Delhi 💯 Call Us 🔝9205541914 🔝( Delhi) Escorts Ser...

Call Girls in Malviya Nagar Delhi 💯 Call Us 🔝9205541914 🔝( Delhi) Escorts Ser...
83778-77756 ( HER.SELF ) Brings Call Girls In Laxmi Nagar

83778-77756 ( HER.SELF ) Brings Call Girls In Laxmi Nagar
Russian Call Girls Delhi Indirapuram {9711199171} Aarvi Gupta ✌️Independent ...

Russian Call Girls Delhi Indirapuram {9711199171} Aarvi Gupta ✌️Independent ...
(COD) ̄Young Call Girls In Dwarka , New Delhi꧁❤ 7042364481❤꧂ Escorts Service i...

(COD) ̄Young Call Girls In Dwarka , New Delhi꧁❤ 7042364481❤꧂ Escorts Service i...
Delhi Call Girls Vikaspuri 9711199171 ☎✔👌✔ Whatsapp Hard And Sexy Vip Call

Delhi Call Girls Vikaspuri 9711199171 ☎✔👌✔ Whatsapp Hard And Sexy Vip Call
VIP Kolkata Call Girl Kasba 👉 8250192130 Available With Room

VIP Kolkata Call Girl Kasba 👉 8250192130 Available With Room
Vip Hot🥵 Call Girls Delhi Delhi {9711199012} Avni Thakur 🧡😘 High Profile Girls

Vip Hot🥵 Call Girls Delhi Delhi {9711199012} Avni Thakur 🧡😘 High Profile Girls
Hauz Khas Call Girls ☎ 7042364481 independent Escorts Service in delhi

Hauz Khas Call Girls ☎ 7042364481 independent Escorts Service in delhi
Connected Car Hacking: OBD2 Port & Mobile Apps Top Vulnerabilities
- 1. CONNECTED CAR HACK UNDER THE HOOD OF A new security vulnerabilites all drivers should be aware of. Today’s modern vehicles can contain over 100 processors, many of which control critical systems within the vehicle. Essentially a computer on wheels, the connected car presents MULTIPLE POINTS OF VULNERABILTY PRIMARY ATTACK POINTS CAR GETS HACKED devices which monitor speed, braking, and location. Located underneath the dashboard, the OBD2 port is a physical connection that is highly vulnerable. This diagnostic port is used to connect third-party OBD2 Port that expose vehicle data or functionality. Interfacing with vehicle systems are applications running on the driver’s personal mobile device. These applications may contain binary libraries MOBILE APPLICATIONS Infotainment Engine Locks Brakes System Airbags OBD2 Port EXTRACT BINARY CODE FROM DEVICE REVERSE-ENGINEER SOFTWARE TAMPER WITH BINARY CODE REDEPLOY MALICIOUS SOFTWARE High ThreatModerate ThreatLow Threat Mobile Applications 1 2 3 4 easily hacked if not protected. Typically the primary communication interface of a connected car, the infotainment system hosts high-value and sensitive applications that are INFOTAINMENT SYSTEM 1 & 2 3 4 KEEP SOFTWARE UPDATED: DON’T JAILBREAK YOUR CAR OR DEVICE: CHECK OUTLETS PERIODICALLY: ASK MANUFACTURER IF APPS ARE HARDENED: TO PREVENT IT WHAT YOU CAN DOHOW A CONNECTED HACKABILITY Check with your manufacturer and service provider to make sure you always have the In addition to making your car less secure, it may also void warranties. what you choose to plug in. Make sure you know what is plugged into any USB or OBD2 ports on your vehicle. Carefully consider latest version installed. to download. Verify that all mobile and pre-installed apps are hardened, in addition to any third-party apps you choose VEHICLE TO VEHICLE VEHICLE TOVEHICLE TO DEVICE NFC 802.11p 802.11p INFRASTRUCTURE What’s 802.11p? A new wireless standard that enables ITS or Intelligent Transportation Systems. Did you know? By 2020, it’s expected that 75% of cars shipped globally will have internet connectivity. Reverse-engineering tools (i.e. IDA pro) are fast, low in cost and easy-to-use.
