Hardware Vs Software Encryption - Comparison
•
0 gefällt mir•1,266 views
Melden
Teilen
Melden
Teilen
Downloaden Sie, um offline zu lesen
Empfohlen
Weitere ähnliche Inhalte
Kürzlich hochgeladen
Kürzlich hochgeladen (20)
"Subclassing and Composition – A Pythonic Tour of Trade-Offs", Hynek Schlawack

"Subclassing and Composition – A Pythonic Tour of Trade-Offs", Hynek Schlawack
Vector Databases 101 - An introduction to the world of Vector Databases

Vector Databases 101 - An introduction to the world of Vector Databases
"LLMs for Python Engineers: Advanced Data Analysis and Semantic Kernel",Oleks...

"LLMs for Python Engineers: Advanced Data Analysis and Semantic Kernel",Oleks...
Beyond Boundaries: Leveraging No-Code Solutions for Industry Innovation

Beyond Boundaries: Leveraging No-Code Solutions for Industry Innovation
Integration and Automation in Practice: CI/CD in Mule Integration and Automat...

Integration and Automation in Practice: CI/CD in Mule Integration and Automat...
My INSURER PTE LTD - Insurtech Innovation Award 2024

My INSURER PTE LTD - Insurtech Innovation Award 2024
Dev Dives: Streamline document processing with UiPath Studio Web

Dev Dives: Streamline document processing with UiPath Studio Web
New from BookNet Canada for 2024: BNC CataList - Tech Forum 2024

New from BookNet Canada for 2024: BNC CataList - Tech Forum 2024
Gen AI in Business - Global Trends Report 2024.pdf

Gen AI in Business - Global Trends Report 2024.pdf
Powerpoint exploring the locations used in television show Time Clash

Powerpoint exploring the locations used in television show Time Clash
Unraveling Multimodality with Large Language Models.pdf

Unraveling Multimodality with Large Language Models.pdf
Leverage Zilliz Serverless - Up to 50X Saving for Your Vector Storage Cost

Leverage Zilliz Serverless - Up to 50X Saving for Your Vector Storage Cost
Empfohlen
More than Just Lines on a Map: Best Practices for U.S Bike Routes

More than Just Lines on a Map: Best Practices for U.S Bike RoutesProject for Public Spaces & National Center for Biking and Walking
Empfohlen (20)
Content Methodology: A Best Practices Report (Webinar)

Content Methodology: A Best Practices Report (Webinar)
How to Prepare For a Successful Job Search for 2024

How to Prepare For a Successful Job Search for 2024
Social Media Marketing Trends 2024 // The Global Indie Insights

Social Media Marketing Trends 2024 // The Global Indie Insights
Trends In Paid Search: Navigating The Digital Landscape In 2024

Trends In Paid Search: Navigating The Digital Landscape In 2024
5 Public speaking tips from TED - Visualized summary

5 Public speaking tips from TED - Visualized summary
Google's Just Not That Into You: Understanding Core Updates & Search Intent

Google's Just Not That Into You: Understanding Core Updates & Search Intent
The six step guide to practical project management

The six step guide to practical project management
Beginners Guide to TikTok for Search - Rachel Pearson - We are Tilt __ Bright...

Beginners Guide to TikTok for Search - Rachel Pearson - We are Tilt __ Bright...
Unlocking the Power of ChatGPT and AI in Testing - A Real-World Look, present...

Unlocking the Power of ChatGPT and AI in Testing - A Real-World Look, present...
More than Just Lines on a Map: Best Practices for U.S Bike Routes

More than Just Lines on a Map: Best Practices for U.S Bike Routes
Ride the Storm: Navigating Through Unstable Periods / Katerina Rudko (Belka G...

Ride the Storm: Navigating Through Unstable Periods / Katerina Rudko (Belka G...
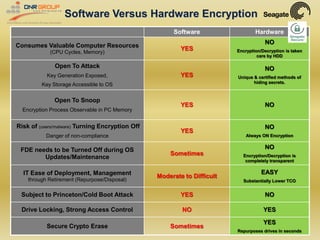
Hardware Vs Software Encryption - Comparison
- 1. Software Versus Hardware Encryption Software Hardware NO Consumes Valuable Computer Resources YES Encryption/Decryption is taken (CPU Cycles, Memory) care by HDD Open To Attack NO YES Key Generation Exposed, Unique & certified methods of hiding secrets. Key Storage Accessible to OS Open To Snoop YES NO Encryption Process Observable in PC Memory Risk of (users/malware) Turning Encryption Off NO YES Danger of non-compliance Always ON Encryption NO FDE needs to be Turned Off during OS Sometimes Encryption/Decryption is Updates/Maintenance completely transparent EASY IT Ease of Deployment, Management Moderate to Difficult through Retirement (Repurpose/Disposal) Substantially Lower TCO Subject to Princeton/Cold Boot Attack YES NO Drive Locking, Strong Access Control NO YES YES Secure Crypto Erase Sometimes Repurposes drives in seconds